talk: A multi-scale approach to analyze large clinical datasets, Noon Thr 4/10
A multi-scale approach to analyze large clinical datasets:
Towards the understanding of the complex effects of concussions
Dr. Jesus Caban
National Intrepid Center of Excellence
Walter Reed, Bethesda, MD
Noon Thursday, 10 April 2014, ITE325b
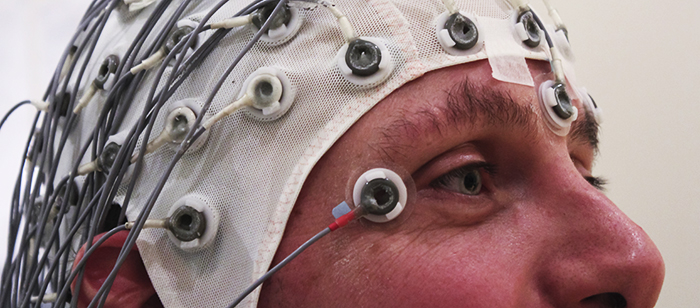
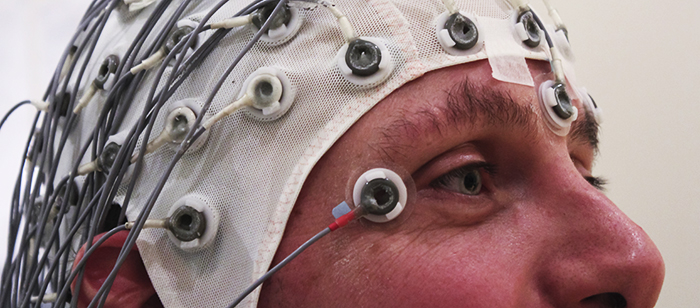
Mild traumatic brain injuries (mTBIs) or concussions are invisible injuries that are poorly understood and their sequelae can be difficult to diagnose. Individuals who have had concussions are at an increased risk of depression, post-traumatic stress disorder (PTSD), headaches, concentration difficulties, and other problems. During the last decade, a significant amount of attention has been given to the acquisition of clinical data from patients suffering from mTBI. Unfortunately, most of the data collection and analysis have focused on individual aspects of the injury, not necessarily on comprehensive and multi-modal analytical techniques to capture the complex biological state of mTBI patients.
This talk will discuss a large-scale informatics database that has been developed to enable interdisciplinary research on mTBI and will introduce a multi-scale approach to mine complex clinical datasets. The millions of multi-modal elements originated from different clinical disciplines are treated as weak features and modeled independently to generate stronger features. Three cases of going from weak to stronger features will be discussed including (a) an inductive/transductive model to extract stable image features from multi-modal MRI scans, (b) a rule-based model used to infer knowledge from blood measurements, and (c) a sentiment analysis-based model to extract behavioral signals from writing samples. Once stronger features are obtained, a relational model is used to integrate the data and extract new knowledge from such a complex dataset.
Dr. Caban is the Acting Chief of Clinical & Research Informatics at the National Intrepid Center of Excellence (NICoE) at Walter Reed Bethesda. He received a Ph.D. in Computer Science from UMBC (2009), his M.S. degree in Computer Science from the University of Kentucky (2005), and his B.S. in Computer Science from the University of Puerto Rico (2002). Over the last eight years Dr. Caban’s research has focused on the design and development of techniques to analyze clinical and imaging data. His research and experience has given him the opportunity to work at top research and healthcare organizations including the National Institutes of Health (NIH), John Hopkins University, the University of Maryland Medical Center, and IBM Research. Dr. Caban is presently an adjunct faculty member at John Hopkins University Applied Physics Lab and a part-time instructor at the Department of Computer Science at UMBC. Recently, he received the 2013-14 JHU/APL Junior faculty award for his commitment to teaching. Currently, he is serving as the Associate Editor of the JAMIA special issue on Visual Analytics in Healthcare and as the contracting officer representative (COR) for the DoD program on “Watson-Like Technologies for TBI/PTSD Clinical Decision Support and Predictive Analytics”.
]]>
A multi-scale approach to analyze large clinical datasets: Towards the understanding of the complex effects of concussions Dr. Jesus Caban National Intrepid Center of Excellence Walter Reed,...
http://www.csee.umbc.edu/2014/04/talk-a-multi-scale-approach-to-analyze-large-clinical-datasets-1pm-fri-411/
https://dev.my.umbc.edu/api/v0/pixel/news/43873/guest@my.umbc.edu/3ba36b966a6a56d3e76234f0946f1452/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 07 Apr 2014 11:47:03 -0400
talk: Talking to Robots, 1pm Mon 4/7 ITE325b
Talking to Robots: Learning to Ground Human
Language in Robotic Perception
1:00pm Monday, 7 April 2014, ITE325b, UMBC
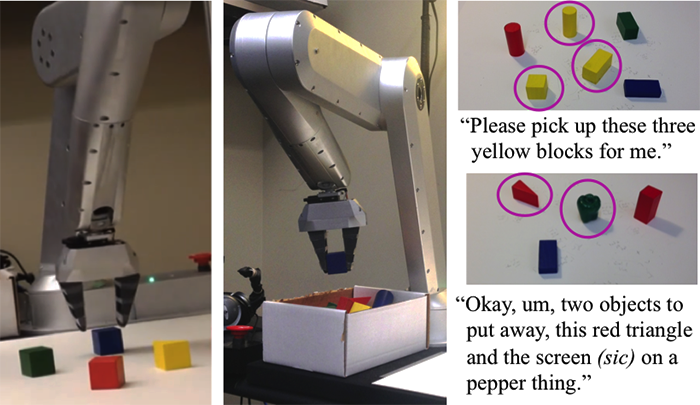
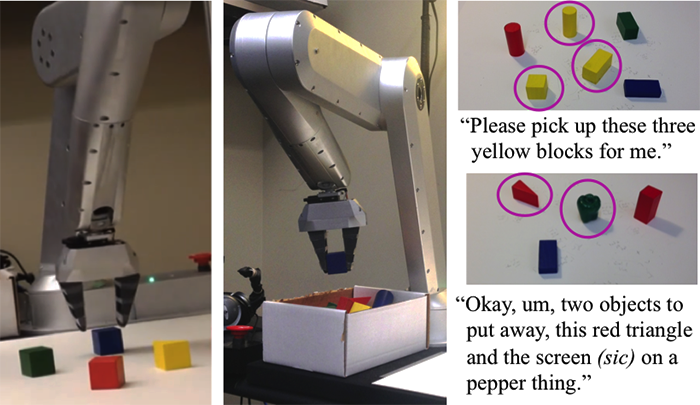
Advances in computation, sensing, and hardware are enabling robots to perform an increasing variety of tasks in ever less constrained settings. It is now possible to imagine robots that can operate in traditionally human-centric settings. However, such robots need the flexibility to take instructions and learn about tasks from nonspecialists using language and other natural modalities. At the same time, learning to process natural language about the physical world is difficult without a robot’s sensors and actuators. Combining these areas to create useful robotic systems is a fundamentally multidisciplinary problem, requiring advances in natural language processing, machine learning, robotics, and human-robot interaction. In this talk, I describe my work on learning natural language from end users in a physical context; such language allows a person to communicate their needs in a natural, unscripted way. I demonstrate that this approach can enable a robot to follow directions, learn about novel objects in the world, and perform simple tasks such as navigating an unfamiliar map or putting away objects.
Cynthia Matuszek is a Ph.D. candidate in the University of Washington Computer Science and Engineering department, where she is a member of both the Robotics and State Estimation lab and the Language, Interaction, and Learning group. She earned a B.S. in Computer Science from the University of Texas at Austin, and M.Sc. from the University of Washington. She is published in the areas of artificial intelligence, robotics, ubiquitous computing, and human-robot interaction.
]]>
Talking to Robots: Learning to Ground Human Language in Robotic Perception Cynthia Matuszek University of Washington 1:00pm Monday, 7 April 2014, ITE325b, UMBC Advances in computation,...
http://www.csee.umbc.edu/2014/04/talk-talking-to-robots-1pm-mon-47-ite325b/?utm_source=rss&utm_medium=rss&utm_campaign=talk-talking-to-robots-1pm-mon-47-ite325b
https://dev.my.umbc.edu/api/v0/pixel/news/43257/guest@my.umbc.edu/c77a9469f84afdd20a15a105c48039d2/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 05 Apr 2014 15:23:54 -0400
talk: Talking to Robots, 1pm Mon 4/7 ITE325b
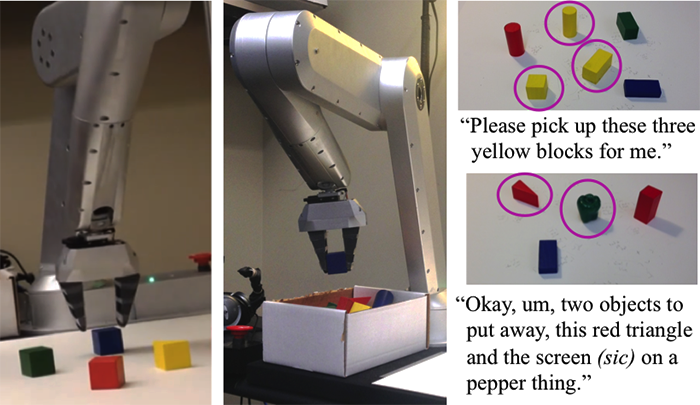
Talking to Robots: Learning to Ground Human
Language in Robotic Perception
1:00pm Monday, 7 April 2014, ITE325b, UMBC
Advances in computation, sensing, and hardware are enabling robots to perform an increasing variety of tasks in ever less constrained settings. It is now possible to imagine robots that can operate in traditionally human-centric settings. However, such robots need the flexibility to take instructions and learn about tasks from nonspecialists using language and other natural modalities. At the same time, learning to process natural language about the physical world is difficult without a robot’s sensors and actuators. Combining these areas to create useful robotic systems is a fundamentally multidisciplinary problem, requiring advances in natural language processing, machine learning, robotics, and human-robot interaction. In this talk, I describe my work on learning natural language from end users in a physical context; such language allows a person to communicate their needs in a natural, unscripted way. I demonstrate that this approach can enable a robot to follow directions, learn about novel objects in the world, and perform simple tasks such as navigating an unfamiliar map or putting away objects.
Cynthia Matuszek is a Ph.D. candidate in the University of Washington Computer Science and Engineering department, where she is a member of both the Robotics and State Estimation lab and the Language, Interaction, and Learning group. She earned a B.S. in Computer Science from the University of Texas at Austin, and M.Sc. from the University of Washington. She is published in the areas of artificial intelligence, robotics, ubiquitous computing, and human-robot interaction.
]]>
Talking to Robots: Learning to Ground Human Language in Robotic Perception Cynthia Matuszek University of Washington 1:00pm Monday, 7 April 2014, ITE325b, UMBC Advances in computation,...
http://www.csee.umbc.edu/2014/04/talk-talking-to-robots-1pm-mon-47-ite325b/
https://dev.my.umbc.edu/api/v0/pixel/news/43874/guest@my.umbc.edu/0b8b8da68f72648d5aabaf446d3db1a6/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 05 Apr 2014 15:23:54 -0400
talk: Making Physical Inferences to Enhance Wireless Security, 1pm Tue 4/8
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Making Physical Inferences to Enhance Wireless Security
Prof. Jie Yang, Oakland University
1:00pm Tuesday, 8 April 2014, ITE 325b
The ubiquity of wireless is redefining security challenges as the increasingly pervasive wireless networks make it easier to conduct attacks for new and rapidly evolving adversaries. There is an urgent need to seek security solutions that can be built into any wireless network stack to defend against attacks across the current heterogeneous mix of wireless technologies, which do not require extensive customization on wireless devices and cannot be undermined easily even when nodes are compromised. In particular, security solutions that are generic across all wireless technologies and can complement conventional security methods must be devised. My research efforts are centered around exploiting physical properties correlated with pervasive wireless environments to enhance wireless security and make inferences for context-aware applications. In this talk, I will present my research work in exploiting spatial correlation as a unique physical property inherited from any wireless device to address identity-based attacks including both spoofing and Sybil. These attacks are especially harmful as the claimed identity of a wireless device is often considered as an important first step in an adversary’s attempt to launch a variety of attacks in different network layers.
Our proposed techniques address several challenges include (1) detecting identity-based attacks in challenging mobile environments, (2) determining the number of attackers, and (3) localizing multiple adversaries. I will also present our work in secret key generation for facilitating secure data communication in the increasing dynamic wireless environments. Our work addressed the problem of collaborative secret key extraction for a group of wireless devices without relying on a key distribution infrastructure. Moreover, in order to provide efficient secret key generation, we exploit fine-grained physical layer information, such as the channel state information made available from OFDM system, to improve the secret key generation rate and make the secret key extraction approach more practical.
Jie Yang received his Ph.D. degree in Computer Engineering from Stevens Institute of Technology in 2011. He is currently an assistant professor in the Department of Computer Science and Engineering at Oakland University. His research interests include cyber security and privacy, and mobile and pervasive computing, with an emphasis on network security, smartphone security and applications, security in cognitive radio and smart grid, location systems and vehicular applications. His research is supported by National Science Foundation and Army Research Office. He is the recipient of the Best Paper Runner-up Award from IEEE Conference on Communications and Network Security 2013 and the Best Paper Award from ACM MobiCom 2011. His research has received wide press coverage including MIT Technology Review, The Wall Street Journal, NPR, CNET News, and Yahoo News.
Hosts: Nilanjan Banerjee and Tim Finin
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Making Physical Inferences to Enhance Wireless Security Prof. Jie Yang, Oakland University 1:00pm...
http://www.csee.umbc.edu/2014/04/talk-making-physical-inferences-to-enhance-wireless-security-1pm-tue-48/?utm_source=rss&utm_medium=rss&utm_campaign=talk-making-physical-inferences-to-enhance-wireless-security-1pm-tue-48
https://dev.my.umbc.edu/api/v0/pixel/news/43239/guest@my.umbc.edu/87f87f90205f40096757d5c3a1bd2d69/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 04 Apr 2014 16:10:46 -0400
talk: Making Physical Inferences to Enhance Wireless Security, 1pm Tue 4/8
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Making Physical Inferences to Enhance Wireless Security
Prof. Jie Yang, Oakland University
1:00pm Tuesday, 8 April 2014, ITE 325b
The ubiquity of wireless is redefining security challenges as the increasingly pervasive wireless networks make it easier to conduct attacks for new and rapidly evolving adversaries. There is an urgent need to seek security solutions that can be built into any wireless network stack to defend against attacks across the current heterogeneous mix of wireless technologies, which do not require extensive customization on wireless devices and cannot be undermined easily even when nodes are compromised. In particular, security solutions that are generic across all wireless technologies and can complement conventional security methods must be devised. My research efforts are centered around exploiting physical properties correlated with pervasive wireless environments to enhance wireless security and make inferences for context-aware applications. In this talk, I will present my research work in exploiting spatial correlation as a unique physical property inherited from any wireless device to address identity-based attacks including both spoofing and Sybil. These attacks are especially harmful as the claimed identity of a wireless device is often considered as an important first step in an adversary’s attempt to launch a variety of attacks in different network layers.
Our proposed techniques address several challenges include (1) detecting identity-based attacks in challenging mobile environments, (2) determining the number of attackers, and (3) localizing multiple adversaries. I will also present our work in secret key generation for facilitating secure data communication in the increasing dynamic wireless environments. Our work addressed the problem of collaborative secret key extraction for a group of wireless devices without relying on a key distribution infrastructure. Moreover, in order to provide efficient secret key generation, we exploit fine-grained physical layer information, such as the channel state information made available from OFDM system, to improve the secret key generation rate and make the secret key extraction approach more practical.
Jie Yang received his Ph.D. degree in Computer Engineering from Stevens Institute of Technology in 2011. He is currently an assistant professor in the Department of Computer Science and Engineering at Oakland University. His research interests include cyber security and privacy, and mobile and pervasive computing, with an emphasis on network security, smartphone security and applications, security in cognitive radio and smart grid, location systems and vehicular applications. His research is supported by National Science Foundation and Army Research Office. He is the recipient of the Best Paper Runner-up Award from IEEE Conference on Communications and Network Security 2013 and the Best Paper Award from ACM MobiCom 2011. His research has received wide press coverage including MIT Technology Review, The Wall Street Journal, NPR, CNET News, and Yahoo News.
Hosts: Nilanjan Banerjee and Tim Finin
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Making Physical Inferences to Enhance Wireless Security Prof. Jie Yang, Oakland University 1:00pm...
http://www.csee.umbc.edu/2014/04/talk-making-physical-inferences-to-enhance-wireless-security-1pm-tue-48/
https://dev.my.umbc.edu/api/v0/pixel/news/43875/guest@my.umbc.edu/6b45c2ce5bc2edd26083db829e539294/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 04 Apr 2014 16:10:46 -0400
2014 Cybersecurity Summer Courses

The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session.
Each class will meet one or two days a week in the late afternoon or evening, depending on the length of the session where the course is offered.
-
CYBR 620: Introduction to Cybersecurity (Parr)
T/TH 6-8:45PM
Summer I (6 weeks) May 27th-July 3rd, 2014
-
CYBR 691: Special Topics in Cybersecurity: “Software Security” (Coman)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
Pre-Req: CYBR 620 or equivalent
Offered to students enrolled at the Universities at Shady Grove campus ONLY
-
CYBR 691: Special Topics in Cybersecurity: “Cybersecurity Risk Management” (Shariati)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
PreReq: CYBR 620 and enrollment at the Universities at Shady Grove
The deadline to apply for Fall 2014 admission to the UMBC Graduate Cybersecurity Program is August 1, 2014.
]]>
The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session. Each class will meet one or two days a week in the late afternoon or evening, depending on...
http://www.csee.umbc.edu/2014/04/2014-cybersecurity-summer-courses/?utm_source=rss&utm_medium=rss&utm_campaign=2014-cybersecurity-summer-courses
https://dev.my.umbc.edu/api/v0/pixel/news/43189/guest@my.umbc.edu/e67499260bb6dace33b03af98994995a/api/pixel
computer-science
csee
cybersecurity
fyi
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Apr 2014 14:39:22 -0400
Thu, 03 Apr 2014 14:39:22 -0400
2014 Cybersecurity Summer Courses

The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session.
Each class will meet one or two days a week in the late afternoon or evening, depending on the length of the session where the course is offered.
-
CYBR 620: Introduction to Cybersecurity (Parr)
T/TH 6-8:45PM
Summer I (6 weeks) May 27th-July 3rd, 2014
-
CYBR 691: Special Topics in Cybersecurity: “Software Security” (Coman)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
Pre-Req: CYBR 620 or equivalent
Offered to students enrolled at the Universities at Shady Grove campus ONLY
-
CYBR 691: Special Topics in Cybersecurity: “Cybersecurity Risk Management” (Shariati)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
PreReq: CYBR 620 and enrollment at the Universities at Shady Grove
The deadline to apply for Fall 2014 admission to the UMBC Graduate Cybersecurity Program is August 1, 2014.
]]>
The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session. Each class will meet one or two days a week in the late afternoon or evening, depending on...
http://www.csee.umbc.edu/2014/04/2014-cybersecurity-summer-courses/?utm_source=rss&utm_medium=rss&utm_campaign=2014-cybersecurity-summer-courses
https://dev.my.umbc.edu/api/v0/pixel/news/43190/guest@my.umbc.edu/21d7ca3e416e25617fba05e5c436ec87/api/pixel
computer-science
csee
cybersecurity
fyi
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Apr 2014 14:39:22 -0400
Thu, 03 Apr 2014 14:39:22 -0400
2014 Cybersecurity Summer Courses

The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session.
Each class will meet one or two days a week in the late afternoon or evening, depending on the length of the session where the course is offered.
-
CYBR 620: Introduction to Cybersecurity (Parr)
T/TH 6-8:45PM
Summer I (6 weeks) May 27th-July 3rd, 2014
-
CYBR 691: Special Topics in Cybersecurity: “Software Security” (Coman)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
Pre-Req: CYBR 620 or equivalent
Offered to students enrolled at the Universities at Shady Grove campus ONLY
-
CYBR 691: Special Topics in Cybersecurity: “Cybersecurity Risk Management” (Shariati)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
PreReq: CYBR 620 and enrollment at the Universities at Shady Grove
The deadline to apply for Fall 2014 admission to the UMBC Graduate Cybersecurity Program is August 1, 2014.
]]>
The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session. Each class will meet one or two days a week in the late afternoon or evening, depending on...
http://www.csee.umbc.edu/2014/04/2014-cybersecurity-summer-courses/
https://dev.my.umbc.edu/api/v0/pixel/news/43863/guest@my.umbc.edu/3feff382e9f5d1f02922fd1e22ebce44/api/pixel
computer-science
csee
cybersecurity
fyi
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Apr 2014 14:39:22 -0400
2014 Cybersecurity Summer Courses

The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session.
Each class will meet one or two days a week in the late afternoon or evening, depending on the length of the session where the course is offered.
-
CYBR 620: Introduction to Cybersecurity (Parr)
T/TH 6-8:45PM
Summer I (6 weeks) May 27th-July 3rd, 2014
-
CYBR 691: Special Topics in Cybersecurity: “Software Security” (Coman)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
Pre-Req: CYBR 620 or equivalent
Offered to students enrolled at the Universities at Shady Grove campus ONLY
-
CYBR 691: Special Topics in Cybersecurity: “Cybersecurity Risk Management” (Shariati)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
PreReq: CYBR 620 and enrollment at the Universities at Shady Grove
The deadline to apply for Fall 2014 admission to the UMBC Graduate Cybersecurity Program is August 1, 2014.
]]>
The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session. Each class will meet one or two days a week in the late afternoon or evening, depending on...
http://www.csee.umbc.edu/2014/04/2014-cybersecurity-summer-courses/
https://dev.my.umbc.edu/api/v0/pixel/news/43876/guest@my.umbc.edu/fdce6bd5a6da83d68f72a13ddd590e7b/api/pixel
computer-science
csee
cybersecurity
fyi
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Apr 2014 14:39:22 -0400
2014 Cybersecurity Summer Courses

The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session.
Each class will meet one or two days a week in the late afternoon or evening, depending on the length of the session where the course is offered.
-
CYBR 620: Introduction to Cybersecurity (Parr)
T/TH 6-8:45PM
Summer I (6 weeks) May 27th-July 3rd, 2014
-
CYBR 691: Special Topics in Cybersecurity: “Software Security” (Coman)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
Pre-Req: CYBR 620 or equivalent
Offered to students enrolled at the Universities at Shady Grove campus ONLY
-
CYBR 691: Special Topics in Cybersecurity: “Cybersecurity Risk Management” (Shariati)
M/W 7:10-9:40PM
Summer I (6 weeks) May 27th-July 3rd, 2014
PreReq: CYBR 620 and enrollment at the Universities at Shady Grove
The deadline to apply for Fall 2014 admission to the UMBC Graduate Cybersecurity Program is August 1, 2014.
]]>
The UMBC Graduate Cybersecurity Program is offering the following courses over the Summer 2014 session. Each class will meet one or two days a week in the late afternoon or evening, depending on...
https://www.csee.umbc.edu/2014/04/2014-cybersecurity-summer-courses/
https://dev.my.umbc.edu/api/v0/pixel/news/57836/guest@my.umbc.edu/62860cb72e73420344b7502faa3440d4/api/pixel
computer-science
csee
cybersecurity
fyi
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Apr 2014 14:39:22 -0400