Professors Adali and Westlake receive grant to improve treatment for stroke victims
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed Grant Program for a project that ultimately will improve the recovery of stroke victims. The new joint UMBC-UMB Seed Grant Program pairs primary investigators from UMBC and the University of Maryland, Baltimore to conduct research as a team. Successful partners are offered research funding of up to $75,000 over twelve months to pursue their collaboration.
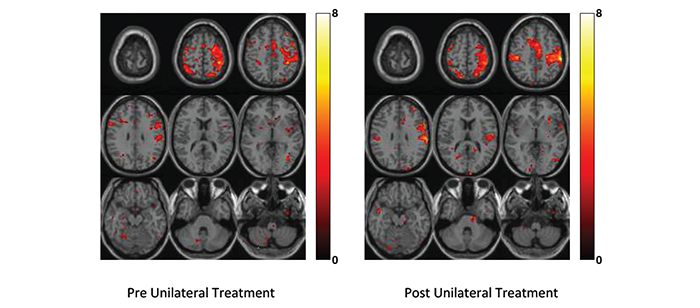
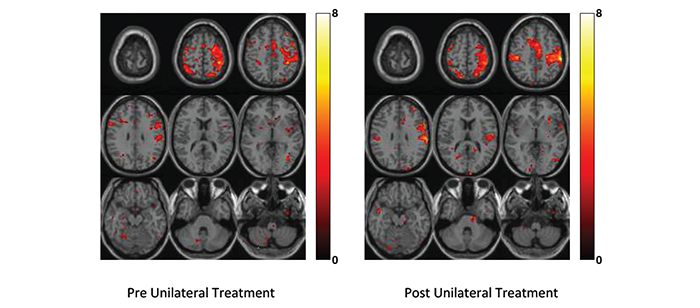
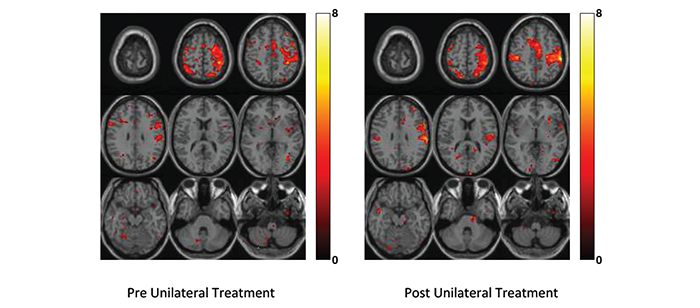
Nearly 800,000 U.S. citizens have a stroke each year, making it the leading cause of long-term disability. Treatment for stroke victims is mainly targeted towards residual functional deficits, especially regaining hand functions. Their project (“Independent Vector Analysis to Investigate Cognitive Neural Networks after Stroke: A Comparison between Two Rehabilitation Interventions”) will have a direct impact on stroke rehabilitation through objective evaluation of the two main treatment paradigms currently in use: unimanual (involving one hand) and bimanual (involving both hands) training. The evaluation will use the new class of medical image analysis techniques, independent vector analysis (IVA) algorithms, developed by Dr. Adali and her research group. The new class of IVA algorithms successfully captures subject variability and perform significantly better than the approaches traditionally used for the problem.
The initial results of the project demonstrate the advantages using IVA for the problem and will be presented this month at the 48th Annual Conference on Information Sciences and Systems in Princeton, NJ. The PIs are preparing two journal submissions, one based on the methods developed for the task and a second one emphasizing clinical significance of the results. These results will also provide the preliminary data for the proposal that Professors Adali and Westlake plan to submit to the NIH later this year.
]]>
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed...
http://www.csee.umbc.edu/2014/03/professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims/
https://dev.my.umbc.edu/api/v0/pixel/news/41982/guest@my.umbc.edu/d7a850947a7fbd58dd2708b3734ccfad/api/pixel
faculty-and-staff
news
research
research-awards
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 12:56:02 -0500
Mon, 03 Mar 2014 12:56:02 -0500
Professors Adali and Westlake receive grant to improve treatment for stroke victims
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed Grant Program for a project that ultimately will improve the recovery of stroke victims. The new joint UMBC-UMB Seed Grant Program pairs primary investigators from UMBC and the University of Maryland, Baltimore to conduct research as a team. Successful partners are offered research funding of up to $75,000 over twelve months to pursue their collaboration.
Nearly 800,000 U.S. citizens have a stroke each year, making it the leading cause of long-term disability. Treatment for stroke victims is mainly targeted towards residual functional deficits, especially regaining hand functions. Their project (“Independent Vector Analysis to Investigate Cognitive Neural Networks after Stroke: A Comparison between Two Rehabilitation Interventions”) will have a direct impact on stroke rehabilitation through objective evaluation of the two main treatment paradigms currently in use: unimanual (involving one hand) and bimanual (involving both hands) training. The evaluation will use the new class of medical image analysis techniques, independent vector analysis (IVA) algorithms, developed by Dr. Adali and her research group. The new class of IVA algorithms successfully captures subject variability and perform significantly better than the approaches traditionally used for the problem.
The initial results of the project demonstrate the advantages using IVA for the problem and will be presented this month at the 48th Annual Conference on Information Sciences and Systems in Princeton, NJ. The PIs are preparing two journal submissions, one based on the methods developed for the task and a second one emphasizing clinical significance of the results. These results will also provide the preliminary data for the proposal that Professors Adali and Westlake plan to submit to the NIH later this year.
]]>
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed...
http://www.csee.umbc.edu/2014/03/professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims/?utm_source=rss&utm_medium=rss&utm_campaign=professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims
https://dev.my.umbc.edu/api/v0/pixel/news/42619/guest@my.umbc.edu/14c837573ac6d2cec7960704cd65db6d/api/pixel
faculty-and-staff
news
research
research-awards
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 12:56:02 -0500
talk: Predictive Analytics for Insider Threats, 4pm Wed 3/5
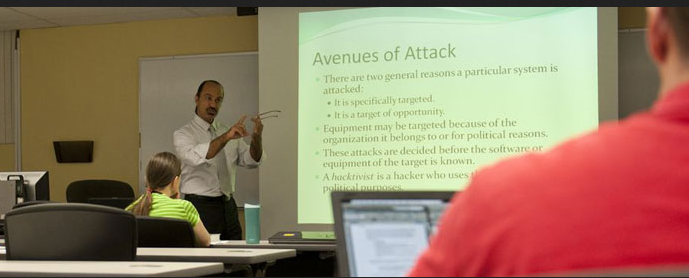
Predictive Analytics for Insider Threats
Ben Shariati
Visiting Lecturer & Interim Assistant CYBR GPD
4:00pm Wednesday, 5 March 2014, ITE325b
This talk will discuss how using operational cyber analytics for predictive security intelligence support a powerful defensive cybersecurity capability. Specifically, I will share elements of my commercial research on how organizations can predict malicious behavior (both user and digital) on their networks by incorporating tailored algorithms and artificial intelligence capabilities as part of an overall cybersecurity sensor architecture. Additionally, this talk will briefly discuss the impact that mobile devices have on the insider threat vulnerability within the government and private sector.
Ben Shariati is a Ph.D. candidate in Information Assurance/Cybersecurity at the George Washington University, where his dissertation work examines the analysis and management of cybersecurity concerns of critical infrastructures. His research and professional interests include mobile device security, emerging technology evaluation, risk analysis, audit, and compliance. For AY13-14, Mr. Shariati is a visiting lecturer and Interim Assistant Director of the Graduate Cybersecurity Program overseeing program activities at The Universities at Shady Grove. In addition to teaching several courses at UMBC, Mr. Shariati has taught graduate cybersecurity courses at George Washington University and undergraduate technical certification classes Hagerstown Community College.
Mr. Shariati is a technology and business executive with over 20 years of experience specializing in strategic and operational cybersecurity program activities and development for international organizations. His career highlights include serving as a lead enterprise security architect at the Federal Reserve Bank in Richmond, VA, a cybersecurity advisor at Cell Trust Corporation, and Technology Advisor/Cybersecurity Architect for the United Nations Pan American Health Organization.
]]>
Predictive Analytics for Insider Threats Ben Shariati Visiting Lecturer & Interim Assistant CYBR GPD 4:00pm Wednesday, 5 March 2014, ITE325b This talk will discuss how using operational...
http://www.csee.umbc.edu/2014/03/talk-predictive-analytics-for-insider-threats/
https://dev.my.umbc.edu/api/v0/pixel/news/41960/guest@my.umbc.edu/bbd49e0ac74987523077d3af39379525/api/pixel
csee
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 02 Mar 2014 19:46:31 -0500
Sun, 02 Mar 2014 19:46:31 -0500
talk: Predictive Analytics for Insider Threats, 4pm Wed 3/5
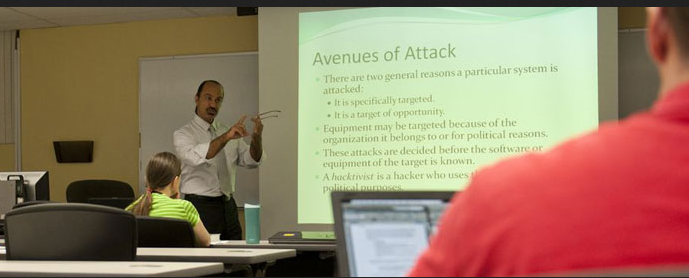
Predictive Analytics for Insider Threats
Ben Shariati
Visiting Lecturer & Interim Assistant CYBR GPD
4:00pm Wednesday, 5 March 2014, ITE325b
This talk will discuss how using operational cyber analytics for predictive security intelligence support a powerful defensive cybersecurity capability. Specifically, I will share elements of my commercial research on how organizations can predict malicious behavior (both user and digital) on their networks by incorporating tailored algorithms and artificial intelligence capabilities as part of an overall cybersecurity sensor architecture. Additionally, this talk will briefly discuss the impact that mobile devices have on the insider threat vulnerability within the government and private sector.
Ben Shariati is a Ph.D. candidate in Information Assurance/Cybersecurity at the George Washington University, where his dissertation work examines the analysis and management of cybersecurity concerns of critical infrastructures. His research and professional interests include mobile device security, emerging technology evaluation, risk analysis, audit, and compliance. For AY13-14, Mr. Shariati is a visiting lecturer and Interim Assistant Director of the Graduate Cybersecurity Program overseeing program activities at The Universities at Shady Grove. In addition to teaching several courses at UMBC, Mr. Shariati has taught graduate cybersecurity courses at George Washington University and undergraduate technical certification classes Hagerstown Community College.
Mr. Shariati is a technology and business executive with over 20 years of experience specializing in strategic and operational cybersecurity program activities and development for international organizations. His career highlights include serving as a lead enterprise security architect at the Federal Reserve Bank in Richmond, VA, a cybersecurity advisor at Cell Trust Corporation, and Technology Advisor/Cybersecurity Architect for the United Nations Pan American Health Organization.
]]>
Predictive Analytics for Insider Threats Ben Shariati Visiting Lecturer & Interim Assistant CYBR GPD 4:00pm Wednesday, 5 March 2014, ITE325b This talk will discuss how using operational...
http://www.csee.umbc.edu/2014/03/talk-predictive-analytics-for-insider-threats/?utm_source=rss&utm_medium=rss&utm_campaign=talk-predictive-analytics-for-insider-threats
https://dev.my.umbc.edu/api/v0/pixel/news/42620/guest@my.umbc.edu/04b3dcbde13cb738b1decfe32bc76ab4/api/pixel
csee
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 02 Mar 2014 19:46:31 -0500
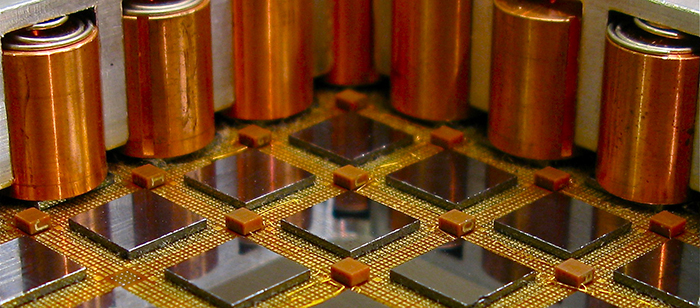
Samuel Lomonaco: Strange World of Quantum Computing, NASA Mon. 3/10
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the Building 3 Auditorium.
Abstract: Quantum computers have the potential to greatly increase computational power beyond the capabilities of conventional computers by exploiting the bizarre quantum properties of the subatomic world. This talk will give an introductory overview of quantum computing in an intuitive and conceptual fashion. No prior knowledge of quantum mechanics will be assumed.
]]>
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the...
http://www.csee.umbc.edu/2014/03/samuel-lomonaco-strange-world-of-quantum-computing-nasa-mon-310/
https://dev.my.umbc.edu/api/v0/pixel/news/41956/guest@my.umbc.edu/f07bef95672ee9cc8bad65bd43a229db/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 02 Mar 2014 14:11:12 -0500
Samuel Lomonaco: Strange World of Quantum Computing, NASA Mon. 3/10
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the Building 3 Auditorium.
Abstract: Quantum computers have the potential to greatly increase computational power beyond the capabilities of conventional computers by exploiting the bizarre quantum properties of the subatomic world. This talk will give an introductory overview of quantum computing in an intuitive and conceptual fashion. No prior knowledge of quantum mechanics will be assumed.
]]>
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the...
http://www.csee.umbc.edu/2014/03/samuel-lomonaco-strange-world-of-quantum-computing-nasa-mon-310/?utm_source=rss&utm_medium=rss&utm_campaign=samuel-lomonaco-strange-world-of-quantum-computing-nasa-mon-310
https://dev.my.umbc.edu/api/v0/pixel/news/42621/guest@my.umbc.edu/6d22b810d556da44e5834b9e1209c580/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 02 Mar 2014 14:11:12 -0500
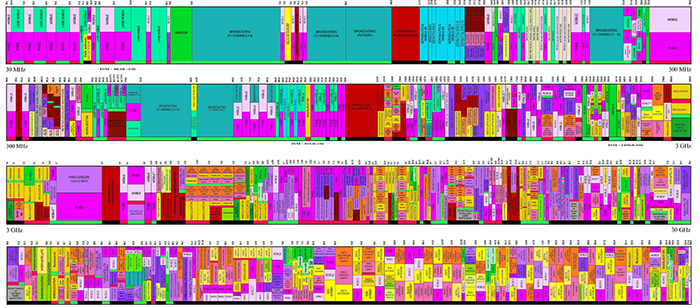
talk: Probabilistic Information for Spectrum Sensing and Utilization, 11:45 3/7, UMBC
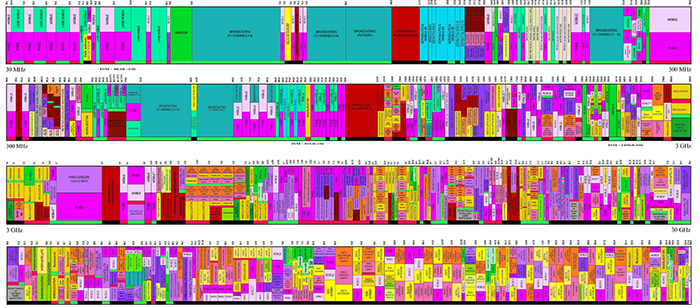
Exploiting Probabilistic Information for Spectrum Sensing
and Utilization: towards Efficient Wireless Coexistence
Prof. Xiangwei Zhou
University of Illinois, Carbondale
11:45am Friday, 7 March 2014, ITE 325b, UMBC
With the rapid growth of wireless devices and applications, the electromagnetic radio spectrum is considered to be in short supply. To overcome spectrum scarcity and satisfy emerging user demands, cognitive radio, which can sense and adapt to the surrounding spectral environment, has been introduced to enhance the utilization of the spectrum. However, it is a challenging task to design a robust and cost-effective system involving identification and reuse of spectrum opportunities changing over time, frequency, and space. In this talk, I will focus on efficient spectrum sensing and utilization techniques for dynamic spectrum access. In particular, I will emphasize the importance of exploiting probabilistic information unique to such a system. I will present novel techniques from the perspectives of both a single user and a multi-user network. In the end, I will discuss further extension of the work to enable the coexistence of heterogeneous wireless networks.
Xiangwei Zhou received his Ph.D. degree in Electrical and Computer Engineering from Georgia Institute of Technology, Atlanta, Georgia, in 2011. He received his M.S. degree in Information and Communication Engineering from Zhejiang University, Hangzhou, China and his B.S. degree in Communication Engineering from Nanjing University of Science and Technology, Nanjing, China, in 2007 and 2005, respectively. Since 2013, Dr. Zhou has been with the Department of Electrical and Computer Engineering at Southern Illinois University Carbondale as an Assistant Professor. Prior to that, he was a Senior Systems Engineer with Marvell Semiconductor, Santa Clara, California, from 2011 to 2013. Dr. Zhou’s general research interests include wireless communications and statistical signal processing, with current emphasis on cognitive radio and heterogeneous coexistence, cyber-physical systems, and cross-layer optimization. He is now serving as an Editor for IEEE Transactions on Wireless Communications.
Host: Mohamed Younis, Sorry, you need javascript to view this email address.
]]>
Exploiting Probabilistic Information for Spectrum Sensing and Utilization: towards Efficient Wireless Coexistence Prof. Xiangwei Zhou University of Illinois, Carbondale 11:45am Friday, 7...
http://www.csee.umbc.edu/2014/02/talk-probabilistic-information-for-spectrum-sensing-and-utilization-1145-37-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/42110/guest@my.umbc.edu/daf7c43a442c49da2458c178029c9dfa/api/pixel
computer-engineering
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 28 Feb 2014 23:39:44 -0500
Fri, 28 Feb 2014 23:39:44 -0500
talk: Probabilistic Information for Spectrum Sensing and Utilization, 11:45 3/7, UMBC
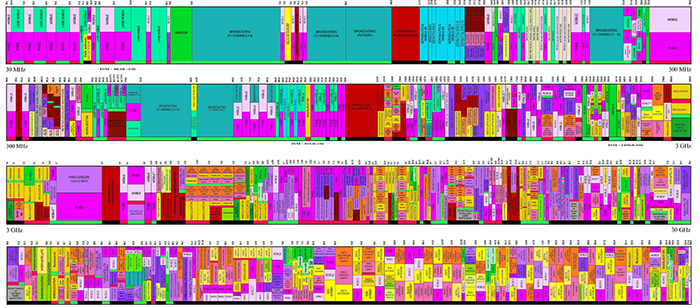
Exploiting Probabilistic Information for Spectrum Sensing
and Utilization: towards Efficient Wireless Coexistence
Prof. Xiangwei Zhou
University of Illinois, Carbondale
11:45am Friday, 7 March 2014, ITE 325b, UMBC
With the rapid growth of wireless devices and applications, the electromagnetic radio spectrum is considered to be in short supply. To overcome spectrum scarcity and satisfy emerging user demands, cognitive radio, which can sense and adapt to the surrounding spectral environment, has been introduced to enhance the utilization of the spectrum. However, it is a challenging task to design a robust and cost-effective system involving identification and reuse of spectrum opportunities changing over time, frequency, and space. In this talk, I will focus on efficient spectrum sensing and utilization techniques for dynamic spectrum access. In particular, I will emphasize the importance of exploiting probabilistic information unique to such a system. I will present novel techniques from the perspectives of both a single user and a multi-user network. In the end, I will discuss further extension of the work to enable the coexistence of heterogeneous wireless networks.
Xiangwei Zhou received his Ph.D. degree in Electrical and Computer Engineering from Georgia Institute of Technology, Atlanta, Georgia, in 2011. He received his M.S. degree in Information and Communication Engineering from Zhejiang University, Hangzhou, China and his B.S. degree in Communication Engineering from Nanjing University of Science and Technology, Nanjing, China, in 2007 and 2005, respectively. Since 2013, Dr. Zhou has been with the Department of Electrical and Computer Engineering at Southern Illinois University Carbondale as an Assistant Professor. Prior to that, he was a Senior Systems Engineer with Marvell Semiconductor, Santa Clara, California, from 2011 to 2013. Dr. Zhou’s general research interests include wireless communications and statistical signal processing, with current emphasis on cognitive radio and heterogeneous coexistence, cyber-physical systems, and cross-layer optimization. He is now serving as an Editor for IEEE Transactions on Wireless Communications.
Host: Mohamed Younis, Sorry, you need javascript to view this email address.
]]>
Exploiting Probabilistic Information for Spectrum Sensing and Utilization: towards Efficient Wireless Coexistence Prof. Xiangwei Zhou University of Illinois, Carbondale 11:45am Friday, 7...
http://www.csee.umbc.edu/2014/02/talk-probabilistic-information-for-spectrum-sensing-and-utilization-1145-37-umbc/?utm_source=rss&utm_medium=rss&utm_campaign=talk-probabilistic-information-for-spectrum-sensing-and-utilization-1145-37-umbc
https://dev.my.umbc.edu/api/v0/pixel/news/42622/guest@my.umbc.edu/e83b8f01c5b7aaffbaf5b611d7878c62/api/pixel
computer-engineering
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 28 Feb 2014 23:39:44 -0500
Fri, 28 Feb 2014 23:39:44 -0500
talk: Strong, usable access control for personal data, 1pm Thr 3/6, UMBC

Toward strong, usable access control for personal data
Michelle Mazurek
Carnegie Mellon University
1:00pm Thursday, 6 March 2014, ITE 325b, UMBC
Users create, store and access a lot of personal data, both on their devices and in the cloud. Although this provides tremendous benefits, it also creates risks to security and privacy, ranging from the inconvenient (private photos posted around the office) to the serious (loss of a job; withdrawal of college admission). Simply refusing to share personal data is not feasible or desirable, but sharing indiscriminately is equally problematic. Instead, users should be able to efficiently accomplish their primary goals without unnecessarily compromising their privacy. In this talk, I describe my work toward developing usable access-control mechanisms for personal data. I review the results of three user studies that provided insight into users’ policy needs and preferences. I then discuss the design and implementation of Penumbra, a distributed file system with built-in access control designed to support those needs. Penumbra has two key building blocks: semantic-tag-based policy specification and logic-based policy enforcement. Our results show that Penumbra can enforce users’ preferred policies securely with low overhead.
Michelle Mazurek is a Ph.D. candidate in Electrical and Computer Engineering at Carnegie Mellon University, co-advised by Lujo Bauer and Greg Ganger. Her research interests span security, systems, and HCI, with particular emphasis on designing systems from the ground up for usable security. She has worked on projects related to usable access control, distributed systems, and passwords.
Host: Penny Rheingans, Sorry, you need javascript to view this email address.
]]>
Toward strong, usable access control for personal data Michelle Mazurek Carnegie Mellon University 1:00pm Thursday, 6 March 2014, ITE 325b, UMBC Users create, store and access a lot of...
http://www.csee.umbc.edu/2014/02/talk-strong-usable-access-control-for-personal-data-1pm-thr-36-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/41912/guest@my.umbc.edu/e111db9b4680253b1ffeefdea34b02c7/api/pixel
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 28 Feb 2014 09:41:22 -0500
Fri, 28 Feb 2014 09:41:22 -0500
talk: Strong, usable access control for personal data, 1pm Thr 3/6, UMBC

Toward strong, usable access control for personal data
Michelle Mazurek
Carnegie Mellon University
1:00pm Thursday, 6 March 2014, ITE 325b, UMBC
Users create, store and access a lot of personal data, both on their devices and in the cloud. Although this provides tremendous benefits, it also creates risks to security and privacy, ranging from the inconvenient (private photos posted around the office) to the serious (loss of a job; withdrawal of college admission). Simply refusing to share personal data is not feasible or desirable, but sharing indiscriminately is equally problematic. Instead, users should be able to efficiently accomplish their primary goals without unnecessarily compromising their privacy. In this talk, I describe my work toward developing usable access-control mechanisms for personal data. I review the results of three user studies that provided insight into users’ policy needs and preferences. I then discuss the design and implementation of Penumbra, a distributed file system with built-in access control designed to support those needs. Penumbra has two key building blocks: semantic-tag-based policy specification and logic-based policy enforcement. Our results show that Penumbra can enforce users’ preferred policies securely with low overhead.
Michelle Mazurek is a Ph.D. candidate in Electrical and Computer Engineering at Carnegie Mellon University, co-advised by Lujo Bauer and Greg Ganger. Her research interests span security, systems, and HCI, with particular emphasis on designing systems from the ground up for usable security. She has worked on projects related to usable access control, distributed systems, and passwords.
Host: Penny Rheingans, Sorry, you need javascript to view this email address.
]]>
Toward strong, usable access control for personal data Michelle Mazurek Carnegie Mellon University 1:00pm Thursday, 6 March 2014, ITE 325b, UMBC Users create, store and access a lot of...
http://www.csee.umbc.edu/2014/02/talk-strong-usable-access-control-for-personal-data-1pm-thr-36-umbc/?utm_source=rss&utm_medium=rss&utm_campaign=talk-strong-usable-access-control-for-personal-data-1pm-thr-36-umbc
https://dev.my.umbc.edu/api/v0/pixel/news/42623/guest@my.umbc.edu/84dd29259e2a0fa081962e30129027ae/api/pixel
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 28 Feb 2014 09:41:22 -0500
Fri, 28 Feb 2014 09:41:22 -0500