Hacker School: spend 12 weeks in NYC developing as a programmer
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as programmers. Three sessions are run each year, with one in the summer.
Hacker School is largely unstructured, self-directed, and project-based with optional activities and structure: reading groups, mini workshops and seminars, weekly dinners and talks, group presentations, and more.
The program is tuition-free, but participants are responsible for their own living expenses. Some aid is available, including more than $150,000 from Google for need-based grants for female programmers to come to Hacker School. For more information and to apply, see the Hacker School site.
]]>
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as...
http://www.csee.umbc.edu/2013/12/hacker-school-spend-12-weeks-in-nyc-developing-as-a-programmer/
https://dev.my.umbc.edu/api/v0/pixel/news/39311/guest@my.umbc.edu/48bd239b0ce1f9bbaa221a512bd67a42/api/pixel
fyi
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 10 Dec 2013 16:43:42 -0500
Hacker School: spend 12 weeks in NYC developing as a programmer
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as programmers. Three sessions are run each year, with one in the summer.
Hacker School is largely unstructured, self-directed, and project-based with optional activities and structure: reading groups, mini workshops and seminars, weekly dinners and talks, group presentations, and more.
The program is tuition-free, but participants are responsible for their own living expenses. Some aid is available, including more than $150,000 from Google for need-based grants for female programmers to come to Hacker School. For more information and to apply, see the Hacker School site.
]]>
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as...
http://www.csee.umbc.edu/2013/12/hacker-school-spend-12-weeks-in-nyc-developing-as-a-programmer/?utm_source=rss&utm_medium=rss&utm_campaign=hacker-school-spend-12-weeks-in-nyc-developing-as-a-programmer
https://dev.my.umbc.edu/api/v0/pixel/news/42628/guest@my.umbc.edu/8afff6eba1e891a0948fd6c2b1b5f2fc/api/pixel
fyi
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 10 Dec 2013 16:43:42 -0500
Hacker School: spend 12 weeks in NYC developing as a programmer
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as programmers. Three sessions are run each year, with one in the summer.
Hacker School is largely unstructured, self-directed, and project-based with optional activities and structure: reading groups, mini workshops and seminars, weekly dinners and talks, group presentations, and more.
The program is tuition-free, but participants are responsible for their own living expenses. Some aid is available, including more than $150,000 from Google for need-based grants for female programmers to come to Hacker School. For more information and to apply, see the Hacker School site.
]]>
Hacker School is a free, full-time, immersive school in New York for becoming a better programmer. Participants come from around the world to spend 12 weeks writing code and growing as...
https://www.csee.umbc.edu/2013/12/hacker-school-spend-12-weeks-in-nyc-developing-as-a-programmer/
https://dev.my.umbc.edu/api/v0/pixel/news/57839/guest@my.umbc.edu/3f2c5187e02e757feb009501745a75fd/api/pixel
fyi
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 10 Dec 2013 16:43:42 -0500
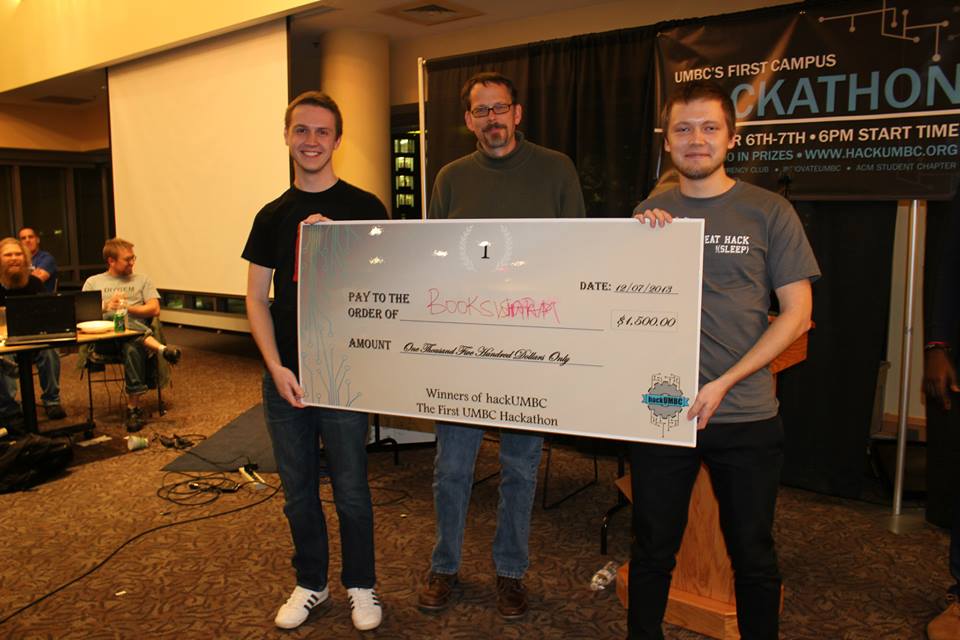
First hackUMBC concludes successfully

The inaugural hackUMBC hackathon was a smashing success!
Held in the UMBC Skylight Room from 7:00pm Friday to 7:00pm Saturday this past weekend, UMBC’s first-ever hackathon was open to all UMBC students of any skill level, from innovators and explorers to designers and hardcore coders. Its purpose was to allow students to mingle and collaborate for 24 continuous hours of community exploration to grow technology projects from scratch while expanding their connections to other students, industry leaders, and faculty. Admission was free and attracted students from across the UMBC campus community, including CS, CE, EE, IS, Biology, Biotechnology, Math, Physics, and Media Studies.
The term ‘hackathon’ hearkens back to the original meaning of “hacker” and “hacking” in early Internet history — namely, to “hack together (create) something quickly” instead of their current interpretations typically referring to illegal cybersecurity activities.
The theme for hackUMBC 2013 was “Hacking to Improve Campus Life” with the goal of ‘hacking together’ any sort of hardware or software project that helps students, teachers, or schools. Accordingly, projects developed during the event included a textbook resale service, realtime intelligent parking space sensors, Peoplesoft interface refinements, and mobile apps to help UMBC students network, socialize, and monitor class schedules, among many others.
Throughout the event, volunteer mentors from UMBC and local industry circulated amongst the teams to offer advice and guidance on their efforts, including how to successfully ‘pitch’ their products to the judges.
UMBC President Freeman Hrabowski joined the festivities early Friday evening to offer words of encouragement and motivation for the nearly 100 UMBC students competing in this innovative and highly charged event.
hackUMBC was conceived by CSEE students Perry Ogwuche and Randi Williams following their summer experience as fellows at CODE2040. Assisting in the effort was Prajit Kumar Das, CS PhD student and president of UMBC’s ACM chapter, and Alexander Morrow, a senior CS student and president of UMBC’s Cryptocurrency Club. CSEE’s Dr. Rick Forno served as faculty advisor to the event.
Projects were evaluated by several faculty and staff judges based on creativity, technical difficulty, polish, relevance, and usefulness. More than $2500 in prizes were awarded!
First Place: BookSwap (Rostislav Tsiomenko, Ilya Dynin)
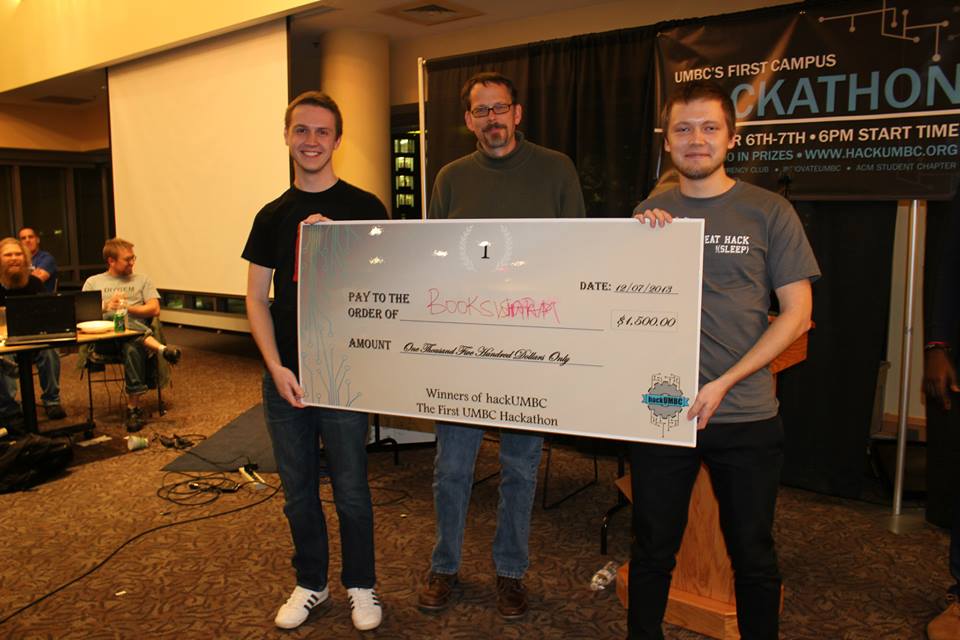
Second Place: Erill Labs (Robert Forder, Talmo Pereira, Patrick O’Neill, Sefa Kilic)

Third Place: Clever Source Solutions (Edward Mukasey, Ian Shefferman, Chinonso Ugwu)

hackUMBC Judges: Tim Oates, Rick Forno, Wesley Griffin, Dan Hood, Shawn Lupoli, Valerie Thomas, Geoffrey Weiss, and Ashwinkumar Ganesan.
hackUMBC was sponsored by Northrop Grumman, the UMBC Department of Computer Science and Electrical Engineering, ClearEdge IT Solutions, Independent Security Evaluators, Next Century Corporation, TriTech Systems, Github, CODE2040, the UMBC BWTech Cync Program, and the UMBC Alex Brown Center.
More information can be found at the hackUMBC page.

]]>
The inaugural hackUMBC hackathon was a smashing success! Held in the UMBC Skylight Room from 7:00pm Friday to 7:00pm Saturday this past weekend, UMBC’s first-ever hackathon was open to all UMBC...
http://www.csee.umbc.edu/2013/12/first-hackumbc-concludes-successfully/
https://dev.my.umbc.edu/api/v0/pixel/news/39298/guest@my.umbc.edu/ccda83873ec78b746e51f5ad4c59a0c7/api/pixel
computer-engineering
computer-science
csee
electrical-engineering
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
49
7
true
Tue, 10 Dec 2013 13:17:53 -0500
Tue, 10 Dec 2013 13:17:53 -0500
UMBC ACM student chapter

UMBC’s ACM student chapter has a new website that will be used to announce its activities and events as well as news about computing related opportunities and resources. The chapter is open to both undergraduate and graduate students interested in computing from all majors. Joining is free and is a great way to meet other students interested in computing and to participate in activities that will help you grow as a professional.
ACM, the Association for Computing Machinery, is the the world’s largest educational and scientific computing society. It provides members with resources that advance computing both as a science and a profession. UMBC’s chapter meetings are open to all undergraduate and graduate students of any major. While you do not need to join ACM to be a part of the local chapter, the annual membership dues for students is only $19, heavily discounted from the non-student rate. See the ACM site for more information on student membership and its benefits.
For more information contact us at acmofficers AT lists.umbc.edu.
]]>
UMBC’s ACM student chapter has a new website that will be used to announce its activities and events as well as news about computing related opportunities and resources. The chapter is open to...
http://www.csee.umbc.edu/2013/12/umbc-acm-student-chapter/
https://dev.my.umbc.edu/api/v0/pixel/news/39073/guest@my.umbc.edu/26c493a5e87608262bceb54d8639afe8/api/pixel
computer-engineering
computer-science
electrical-engineering
game-track
graduate
news
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 04 Dec 2013 10:48:24 -0500
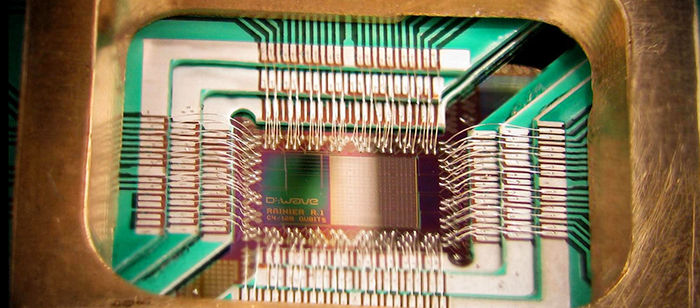
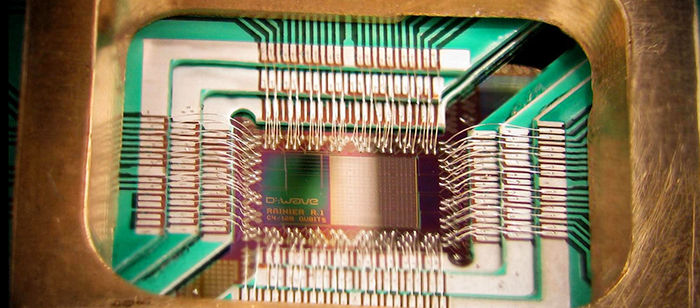
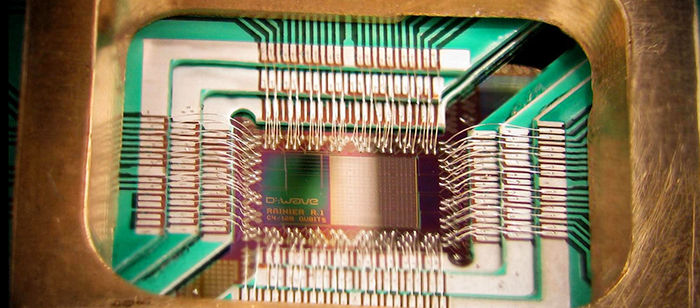
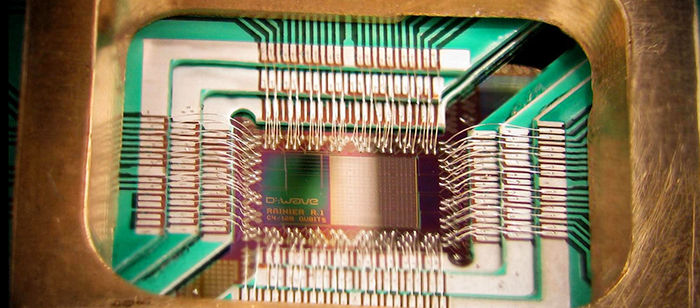
talk: Lomonaco on Shor’s Algorithm (part 2), 2:30-3:00 Tue 12/3
Computer Science and Electrical Engineering
Quantum Computing Seminar
Shor’s Algorithm Part 2
Samuel Lomonaco, CSEE, UMBC
2:30-3:00 Tuesday, 3 December 2013, ITE 325b
As requested in the last seminar, we will devote this seminar to stepping through the complete Shor algorithm (from beginning to end) to factor the “enormous” integer 21. This talk will based on the example found at the beginning of the following paper.
Quantum hidden subgroup algorithms: A mathematical perspective, AMS CONM, vol. 305, (2002), 139 – 202.
Samuel J. Lomonaco is a professor at the Department of Computer Science and Electrical Engineering of the University of Maryland Baltimore County. He is internationally known for his many contributions in mathematics and in computer science. His research interests span a wide range of subjects from knot theory, algebraic and differential topology to algebraic coding theory, quantum computation, and symbolic computation. In quantum cryptography, he has shown how quantum information theory can be used to gain a better understanding of eavesdropping with quantum entanglement. In quantum computation, he has shown how Lie groups can be used to solve problems arising in the study of quantum entanglement. In 2000 Professor Lomonoco organized the first American Mathematical Society short course on quantum computation.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
Computer Science and Electrical Engineering Quantum Computing Seminar Shor’s Algorithm Part 2 Samuel Lomonaco, CSEE, UMBC 2:30-3:00 Tuesday, 3 December 2013, ITE 325b As requested in the...
http://www.csee.umbc.edu/2013/12/talk-lomonaco-on-shors-algorithm-part-2-230-300-tue-123/
https://dev.my.umbc.edu/api/v0/pixel/news/38963/guest@my.umbc.edu/ecef53535e2eba99307c6a76f07b1b03/api/pixel
fyi
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 01 Dec 2013 22:55:53 -0500
Sun, 01 Dec 2013 22:55:53 -0500
talk: Lomonaco on Shor’s Algorithm (part 2), 2:30-3:00 Tue 12/3
Computer Science and Electrical Engineering
Quantum Computing Seminar
Shor’s Algorithm Part 2
Samuel Lomonaco, CSEE, UMBC
2:30-3:00 Tuesday, 3 December 2013, ITE 325b
As requested in the last seminar, we will devote this seminar to stepping through the complete Shor algorithm (from beginning to end) to factor the “enormous” integer 21. This talk will based on the example found at the beginning of the following paper.
Quantum hidden subgroup algorithms: A mathematical perspective, AMS CONM, vol. 305, (2002), 139 – 202.
Samuel J. Lomonaco is a professor at the Department of Computer Science and Electrical Engineering of the University of Maryland Baltimore County. He is internationally known for his many contributions in mathematics and in computer science. His research interests span a wide range of subjects from knot theory, algebraic and differential topology to algebraic coding theory, quantum computation, and symbolic computation. In quantum cryptography, he has shown how quantum information theory can be used to gain a better understanding of eavesdropping with quantum entanglement. In quantum computation, he has shown how Lie groups can be used to solve problems arising in the study of quantum entanglement. In 2000 Professor Lomonoco organized the first American Mathematical Society short course on quantum computation.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
Computer Science and Electrical Engineering Quantum Computing Seminar Shor’s Algorithm Part 2 Samuel Lomonaco, CSEE, UMBC 2:30-3:00 Tuesday, 3 December 2013, ITE 325b As requested in the...
http://www.csee.umbc.edu/2013/12/talk-lomonaco-on-shors-algorithm-part-2-230-300-tue-123/?utm_source=rss&utm_medium=rss&utm_campaign=talk-lomonaco-on-shors-algorithm-part-2-230-300-tue-123
https://dev.my.umbc.edu/api/v0/pixel/news/42629/guest@my.umbc.edu/13ba9e01ce47dd52b7da2ace198e0120/api/pixel
fyi
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 01 Dec 2013 22:55:53 -0500
Sun, 01 Dec 2013 22:55:53 -0500
talk: Lomonaco on Shor’s Algorithm (part 2), 2:30-3:00 Tue 12/3
Computer Science and Electrical Engineering
Quantum Computing Seminar
Shor’s Algorithm Part 2
Samuel Lomonaco, CSEE, UMBC
2:30-3:00 Tuesday, 3 December 2013, ITE 325b
As requested in the last seminar, we will devote this seminar to stepping through the complete Shor algorithm (from beginning to end) to factor the “enormous” integer 21. This talk will based on the example found at the beginning of the following paper.
Quantum hidden subgroup algorithms: A mathematical perspective, AMS CONM, vol. 305, (2002), 139 – 202.
Samuel J. Lomonaco is a professor at the Department of Computer Science and Electrical Engineering of the University of Maryland Baltimore County. He is internationally known for his many contributions in mathematics and in computer science. His research interests span a wide range of subjects from knot theory, algebraic and differential topology to algebraic coding theory, quantum computation, and symbolic computation. In quantum cryptography, he has shown how quantum information theory can be used to gain a better understanding of eavesdropping with quantum entanglement. In quantum computation, he has shown how Lie groups can be used to solve problems arising in the study of quantum entanglement. In 2000 Professor Lomonoco organized the first American Mathematical Society short course on quantum computation.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
Computer Science and Electrical Engineering Quantum Computing Seminar Shor’s Algorithm Part 2 Samuel Lomonaco, CSEE, UMBC 2:30-3:00 Tuesday, 3 December 2013, ITE 325b As requested in the...
https://www.csee.umbc.edu/2013/12/talk-lomonaco-on-shors-algorithm-part-2-230-300-tue-123/
https://dev.my.umbc.edu/api/v0/pixel/news/57840/guest@my.umbc.edu/045e74a296960cf8939d6843f0c9b5f7/api/pixel
fyi
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 01 Dec 2013 22:55:53 -0500
talk: Simson Garfinkel on Finding privacy leaks and stolen data with bulk data analysis

Center for Information Security and Assurance
University of Maryland, Baltimore County
Finding privacy leaks and stolen data with
bulk data analysis and optimistic decoding
Dr. Simson Garfinkel
Naval Postgraduate School
12:00-1:00 Friday, 6 December 2013, ITE 229
Modern digital forensics tools are largely based on the recovery and analysis of files. This talk explores how identity information such as email addresses, credit card numbers, and other of information can be more efficiently found using bulk data analysis, and how results are significantly improved through the use of optimistic decompression. Together, these techniques can find important information on computer media that are ignored by the majority of today’s digital forensics tools.
This talk presents the results of a study of roughly 5000 hard drives purchased on the secondary market and shows how different kinds of data formats can be traced to different kinds of privacy leaks and coding errors. It shows how the results were generated using bulk_extractor, an easy-to-use open source digital forensics tool. Finally, it shows how bulk_extractor was extended to detect data obscured with a simple steganographic technique (XOR 255), and how a subsequence re-analysis of the research corpus found significant use of the technique in commercial software, malware, and by at least one computer criminal.
Dr. Simson L. Garfinkel is an Associate Professor at the Naval Postgraduate School. Based in Arlington VA, Garfinkel’s research interests include digital forensics, usable security, data fusion, information policy and terrorism. He holds six US patents for his computer-related research and has published dozens of research articles on security and digital forensics.
Garfinkel is the author or co-author of fourteen books on computing. He is perhaps best known for his book Database Nation: The Death of Privacy in the 21st Century. Garfinkel’s most successful book, Practical UNIX and Internet Security (co-authored with Gene Spafford), has sold more than 250,000 copies and been translated into more than a dozen languages since the first edition was published in 1991.
Garfinkel received three Bachelor of Science degrees from MIT in 1987, a Master’s of Science in Journalism from Columbia University in 1988, and a Ph.D. in Computer Science from MIT in 2005.
Host: Dr. Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
Center for Information Security and Assurance University of Maryland, Baltimore County Finding privacy leaks and stolen data with bulk data analysis and optimistic decoding Dr. Simson...
http://www.csee.umbc.edu/2013/12/talk-simson-garfinkel-on-finding-privacy-leaks-and-stolen-data-with-bulk-data-analysis/
https://dev.my.umbc.edu/api/v0/pixel/news/38960/guest@my.umbc.edu/1d32579ecb9dd714b7776df281ef94df/api/pixel
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 01 Dec 2013 21:45:11 -0500
Sun, 01 Dec 2013 21:45:11 -0500
2014 CRA-Women Graduate Cohort Workshop Applications due Dec 4

CRA-Women is accepting applications for the 2014 Graduate Cohort for Women. Cohort activities will kick off with a workshop 11-12 April 2014 in Santa Clara, CA. This workshop is the cornerstone of CRA-W’s efforts to increase the ranks of senior women in computing by building and mentoring nationwide communities of women during their graduate studies.
Women students in their first, second, and third year of graduate school in computer science and engineering or a closely related field, who are studying at a U.S. or Canadian institution. Travel expenses, meals and lodging will be provided for students chosen to participate in this program.
At the Grad Cohort Workshop, women graduate students in their first year of graduate school will be welcomed into the community of computing researchers and professionals by providing them with a broad range of strategies and role models. Strategies and mentoring for students in their second and third years of graduate school will also be provided.
All of the students will meet for two days with ~20 senior computing researchers and professionals who will share pertinent information on graduate school survival skills, as well as more personal information and insights into their experiences. The rewards of a research career will be emphasized. This workshop will include a mix of formal presentations and informal discussions and social events. Through the workshop, students will be able to build mentoring relationships and develop peer networks that will form the basis for ongoing activities during their graduate careers. Also, participants will be able to network with our generous sponsors to learn about career and internship opportunities they have available.
See http://bit.ly/crawgcw for more information about the Grad Cohort program. Apply by December 4, 2013.
]]>
CRA-Women is accepting applications for the 2014 Graduate Cohort for Women. Cohort activities will kick off with a workshop 11-12 April 2014 in Santa Clara, CA. This workshop is the cornerstone of...
http://www.csee.umbc.edu/2013/11/2014-cra-women-graduate-cohort-workshop-applications-due-dec-4/
https://dev.my.umbc.edu/api/v0/pixel/news/38785/guest@my.umbc.edu/aa81b3026909d14944b222b51718a917/api/pixel
fyi
graduate
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sun, 24 Nov 2013 11:09:29 -0500
Sun, 24 Nov 2013 11:09:29 -0500