talk: Building Incorruptible Systems in Cloud Environments

Building “Incorruptible” Systems in Cloud Environments
Dr. Haibin Zhang
University of Connecticut
12:00pm Friday, 17 February 2017, ITE 325b, UMBC
In this talk, I will discuss how to design and implement efficient distributed systems in untrusted cloud environments that simultaneously achieve the three most important security goals — integrity, availability, and confidentiality.
Haibin Zhang is a postdoctoral fellow at University of Connecticut advised by Prof. Marten van Dijk. He is working on the MACS project, a cross-institutional collaboration among BU, MIT, Northeastern, and UConn. Previously, he was a postdoctoral research associate at the University of North Carolina at Chapel Hill, advised by Prof. Michael Reiter, working on Project Silver. He received his Ph.D. from University of California at Davis (with Prof. Matthew Franklin), his M.S. from Chinese Academy of Sciences, and his B.S. from Shandong University. He is interested in cloud computing, cryptography, security, privacy, and distributed systems. He received the best paper candidate award at 33rd IEEE International Symposium on Reliable Distributed Systems, proved the security of a NIST standard on ciphertext stealing, and was one of the main inventors of Norton Zone, Symantec’s scalable cloud storage.
The post talk: Building Incorruptible Systems in Cloud Environments appeared first on Department of Computer Science and Electrical Engineering.
]]>
Building “Incorruptible” Systems in Cloud Environments Dr. Haibin Zhang University of Connecticut 12:00pm Friday, 17 February 2017, ITE 325b, UMBC In this talk, I will discuss how to design...
https://www.csee.umbc.edu/2017/02/building-incorruptible-systems-cloud-environments/
https://dev.my.umbc.edu/api/v0/pixel/news/65731/guest@my.umbc.edu/88596a7266730cb9e046a46d35ce6ee1/api/pixel
csee
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 15 Feb 2017 09:55:46 -0500
talk: Cybersecurity and Cellular Technology, 6pm 2/23 Shady Grove

UMBC Cybersecurity Program Cyber Talk
Cybersecurity and Cellular Technology
Joshua Franklin
6:00-8:00pm Thursday, 23 February 2017
The Universities at Shady Grove
Building III (Camille Kendall Academic Center) Room 3241
9636 Gudelsky Drive, Rockville, MD 20850
The UMBC Cybersecurity Program is proud to bring you Cyber Talk, a new speaker series that highlights special topics in Cybersecurity. Join us at The Universities at Shady Grove (USG) for an informative and engaging discussion on the operation of cellular networks and the threats posed to mobile technology. Participants will have the opportunity to ask questions and hear about the latest trends in industry.
Cellular technology plays an increasingly large role in society as it has become the primary portal to the internet for a large segment of the population. One of the main drivers making this change possible is the deployment of modern 4G LTE cellular technologies. This talk serves as a guide to the fundamentals of how cellular networks operate and explores the evolution of 2G GSM, 3G UMTS and 4G cellular security architectures. This is followed by an analysis of the threats posed to cellular networks and supporting mitigations. Although the talk discusses older GSM and UMTS technologies – it is heavily focused on LTE.
Joshua Franklin is a Security Engineer at the National Institute of Standards and Technology (NIST) focusing on cellular security, electronic voting, and public safety. Prior to NIST, Joshua worked at the U.S. Election Assistance Commission gathering extensive experience with voting technologies. After graduating from Kennesaw State University with a Bachelors of Science in Information Systems, he received a Masters of Science in Information Security and Assurance from George Mason University.
The post talk: Cybersecurity and Cellular Technology, 6pm 2/23 Shady Grove appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC Cybersecurity Program Cyber Talk Cybersecurity and Cellular Technology Joshua Franklin 6:00-8:00pm Thursday, 23 February 2017 The Universities at Shady Grove Building III (Camille...
https://www.csee.umbc.edu/2017/02/cybersecurity-cellular-technology-talk-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/65898/guest@my.umbc.edu/c5241a88efd36ef3ae4e21922ffa14ce/api/pixel
cybersecurity
events
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 14 Feb 2017 10:36:32 -0500
talk: Accountability and Data Privacy in the Life Cycle of Big Data

Towards End-to-End Security and Privacy: Accountability
and Data Privacy in the Life Cycle of Big Data
Taeho Jung
Department of Computer Science
Illinois Institute of Technology
11:00am Tuesday, 14 February 2017, ITE 325b, UMBC
The advent of big data has given birth to numerous innovative life-enhancing applications, but the big data is often called as a double-edged sword due to the increased privacy and security threats. Such threats, if unaddressed, will become deadly barriers to the achievement of big opportunities and success anticipated in the big data industry because they may arise at any part of the life cycle of the big data.
In this talk, I will describe my research which addressed various privacy and security issues in the big data life cycle: acquisition, storage, provisioning, and consumption. More specifically, I will briefly present how various types of data can be protected in their acquisition and consumption phases of the life cycle, and subsequently, I will introduce the theoretic foundations of the presented research. Finally, I will present how to make large-scale data trading accountable against dishonest users for the provisioning phase of big data, and this talk will be concluded with my future research agenda briefing.
Taeho Jung is a Ph.D. candidate in Computer Science at Illinois Institute of Technology. His research area, in general, includes privacy and security issues in data mining and provisioning in the big data life cycle. His paper has won a best paper award (IEEE IPCCC 2014), and two of his papers were selected as best paper candidate (ACM MobiHoc 2014) and best paper award runner up (BigCom 2015) respectively. He has served many international conferences as a TPC member, including IEEE DCOSS 2016, IEEE MSN 2016, IEEE IPCCC 2016, and BigCom 2016. He received his B.E. in Computer Software in Tsinghua University in 2011, and he will receive his Ph.D. in May 2017.
The post talk: Accountability and Data Privacy in the Life Cycle of Big Data appeared first on Department of Computer Science and Electrical Engineering.
]]>
Towards End-to-End Security and Privacy: Accountability and Data Privacy in the Life Cycle of Big Data Taeho Jung Department of Computer Science Illinois Institute of Technology 11:00am...
https://www.csee.umbc.edu/2017/02/talk-privacy-security-big-data/
https://dev.my.umbc.edu/api/v0/pixel/news/65689/guest@my.umbc.edu/50b5107abe349d41c30ebea2d20d7f46/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 13 Feb 2017 14:48:41 -0500
IBM’s Arvind Krishna, Accelerating Technology Disruption: the Cognitive Revolution, 1pm Fri 2/24, UMBC

CSEE Department Distinguished Seminar
Accelerating Technology Disruption: The Cognitive Revolution
Dr. Arvind Krishna
Senior Vice President, Hybrid Cloud and Director, IBM Research
1:00-2:00pm, Friday, 24 February 2017, PAHB 132
Digital disruption is changing the world around us, breaking down traditional barriers to market entry, creating new business models, and leading to new solutions to global challenges. Dr. Arvind Krishna will examine some of the core emerging technologies driving this phenomenon today, with an emphasis on artificial intelligence/cognitive computing. He will also share his perspectives on what it takes to build a successful, high-impact technical career in an era of disruptive innovation.
Arvind Krishna is senior vice president, Hybrid Cloud, and director of IBM Research. In this role, he leads the company’s hybrid cloud business, including strategy, product design, offering development, marketing, sales and service. He also helps guide IBM’s overall technical strategy in core and emerging technologies including cognitive computing, quantum computing, cloud platform services, data-driven solutions and blockchain. Previously, Arvind was general manager of IBM Systems and Technology Group’s development and manufacturing organization, responsible for developing and engineering everything from advanced semiconductor materials to leading-edge microprocessors, servers and storage systems.
Earlier in his career, he was general manager of IBM Information Management, which included database, information integration and big data software solutions. Prior to that, he was vice president of strategy for IBM Software. He has held several key technical roles in IBM Software and IBM Research, where he pioneered IBM’s security software business. Arvind has an undergraduate degree from the Indian Institute of Technology, Kanpur and a Ph.D. from the University of Illinois at Urbana-Champaign. He is the recipient of a distinguished alumni award from the University of Illinois, is the co-author of 15 patents, has been the editor of IEEE and ACM journals, and has published extensively in technical conferences and journals.
The post IBM’s Arvind Krishna, Accelerating Technology Disruption: the Cognitive Revolution, 1pm Fri 2/24, UMBC appeared first on Department of Computer Science and Electrical Engineering.
]]>
CSEE Department Distinguished Seminar Accelerating Technology Disruption: The Cognitive Revolution Dr. Arvind Krishna Senior Vice President, Hybrid Cloud and Director, IBM Research...
https://www.csee.umbc.edu/2017/02/talk-dr-arvind-krishna-accelerating-technology-disruption-the-cognitive-revolution/
https://dev.my.umbc.edu/api/v0/pixel/news/65616/guest@my.umbc.edu/8938aaf0921be2741de2dad917f5f97f/api/pixel
ai
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
1
true
Thu, 09 Feb 2017 21:23:36 -0500
Tue, 21 Feb 2017 20:52:36 -0500
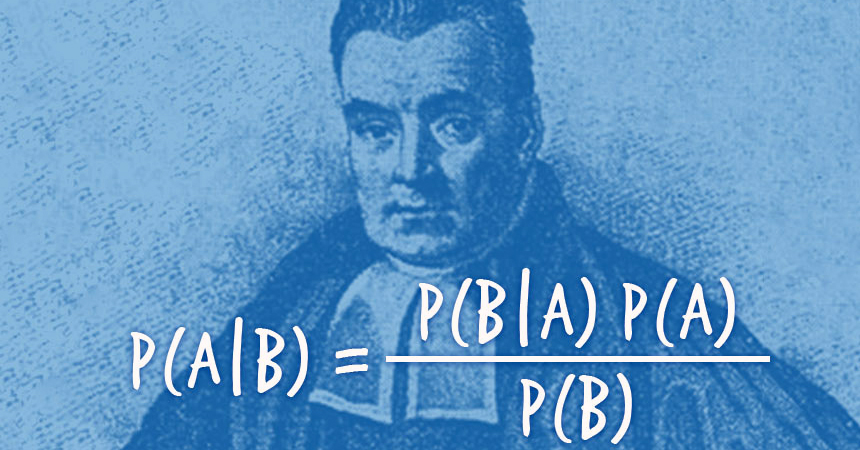
talk: Bayesianism and the Evidence Problem, 4pm 2/15
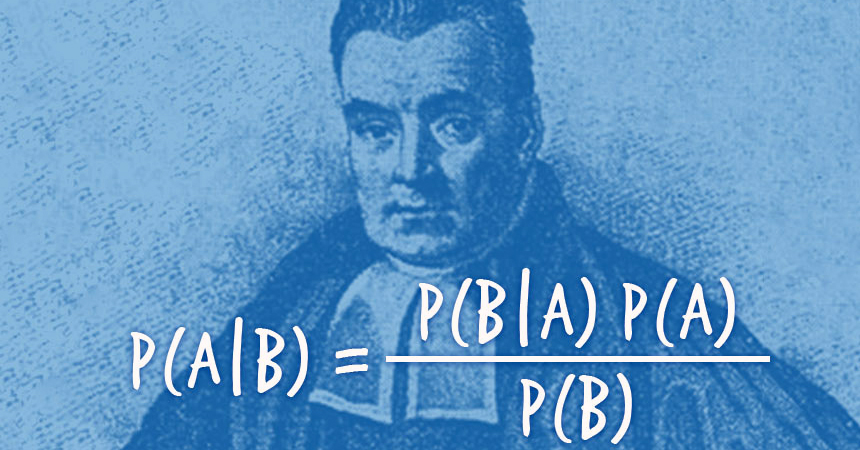
Philosophy Department Colloquium
Bayesianism and the Evidence Problem
Lisa Cassell
University of Massachusetts/Amherst
4-6:00pm Wednesday, 15 February 2017, 456 Performing Arts & Humanities
Bayesianism is a theory that gives us norms for how the degrees of belief we have in certain propositions — our “credences” — ought to hang together. For instance, it tells me that if my credence that I will play baseball tomorrow is .3 and my credence that I will play basketball tomorrow is .4, then, if I believe that I will only play one or the other, my credence that I will either play baseball tomorrow or basketball tomorrow is .7. One of Bayesianism’s most attractive features is its updating norm, which gives us a simple and powerful way of revising our beliefs in the light of new evidence. However, Bayesians have an “Evidence Problem”: while their updating norm tells us what to do once we get evidence, it doesn’t tell us what it means to actually have evidence. In this talk, I consider two arguments — one in support of Bayesian’s updating norm and one against it — and show that both of these arguments fail. I go on to consider what these failures teach us about the Evidence Problem. I conclude by considering some different ways of resolving this problem.
The post talk: Bayesianism and the Evidence Problem, 4pm 2/15 appeared first on Department of Computer Science and Electrical Engineering.
]]>
Philosophy Department Colloquium Bayesianism and the Evidence Problem Lisa Cassell University of Massachusetts/Amherst 4-6:00pm Wednesday, 15 February 2017, 456 Performing Arts &...
https://www.csee.umbc.edu/2017/02/talk-bayesianism-evidence-problem-4pm-215/
https://dev.my.umbc.edu/api/v0/pixel/news/65600/guest@my.umbc.edu/3c234fcb5953c82846436244d7dea79d/api/pixel
data-science
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 09 Feb 2017 11:23:12 -0500
UMBC’s Cyber Scholars program stands out as a national model in “Diverse”

At a time when just 12 percent of information security analysts are black, Hispanic or Asian, and only 20 percent of information security analysts are women, successful student support programs like UMBC’s Cyber Scholars are poised to make a major impact on the field, suggests a new article in Diverse: Issues in Higher Education. The article focuses on this UMBC program as a model for increasing diversity in cyber-related fields through supporting the success of women and underrepresented minority students in cybersecurity, including providing them with opportunities to expand their professional networks.
The UMBC Cyber Scholars program currently includes 40 scholars and 10 associates, and over 97 percent of the scholars and associates in the program have graduated in their intended major, or are pursuing degrees in computer science, computer engineering or information systems, said Cindy Greenwood, assistant director of the program. Of those participating students, 53 percent are women and 40 percent are underrepresented minorities, in stark contrast to national averages for information security professions.
The Cyber Scholars program stands out in higher education because of the variety of elements offered to students, explained Anupam Joshi, professor and chair of computer science and electrical engineering, and director of the Center for Cybersecurity at UMBC. “Many other programs only focus on imparting technology training in cybersecurity,” he said. “Our program is part of formal degree requirements in computer science, computer engineering and information systems” and students can take a broad range of elective courses, which, Joshi noted, “mix instruction in the theory with hands-on projects.”
Each week, Joshi explained, the students in the Cyber Scholars program hear from industry leaders and government officials on topics such as professional development and technical aspects of the field. “They also conduct peer-led workshops in cybersecurity and work with faculty in research labs,” he added. “They are encouraged to do internships in the industry multiple times and get security clearances in the process.”
Alejandra Diaz ‘17, computer science, has been involved with the Cyber Scholars program since she was a freshman at UMBC, and described how the program has helped her grow and access new opportunities. After she met with UMBC President Freeman Hrabowski and Wes Bush, CEO of Northrop Grumman, Diaz interviewed for an internship with Northrop Grumman. Diaz has now interned twice with Northrop Grumman and plans to return to the company before pursuing her master’s degree.
 Alejandra Diaz, left, with fellow Cyber Scholars. Photo by Marlayna Demond ’11 for UMBC.
Alejandra Diaz, left, with fellow Cyber Scholars. Photo by Marlayna Demond ’11 for UMBC.
Read “Programs Aim to Open Doors to Diversity in Cybersecurity” in Diverse: Issues in Higher Education.
Adapted from UMBC News; Header Image: The ITE building at UMBC. Photo by Marlayna Demond ’11 for UMBC.
The post UMBC’s Cyber Scholars program stands out as a national model in “Diverse” appeared first on Department of Computer Science and Electrical Engineering.
]]>
At a time when just 12 percent of information security analysts are black, Hispanic or Asian, and only 20 percent of information security analysts are women, successful student support...
https://www.csee.umbc.edu/2017/02/umbc-cyber-scholars-program-national-model-diversity/
https://dev.my.umbc.edu/api/v0/pixel/news/65473/guest@my.umbc.edu/f13b788ddfe83bd94f9018c560fe8f3c/api/pixel
cwit
cybersecurity
news
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Fri, 03 Feb 2017 18:44:19 -0500
Recruiting UMBC Students for the Grand Challenge Scholars Program , Fri. 2/17

UMBC undergraduates interested in the Grand Challenge Scholars Program are encouraged to attend a symposium and recruiting event at 1:00pm on Friday, February 17.
The Grand Challenge Scholars Program is a program for undergraduates in all majors who are interested in thinking about big problems facing society, and how to solve them from broad, multidisciplinary perspectives. Students select one of 14 Grand Challenges identified by the National Academy Engineering, and work within the cohort of Grand Challenge Scholars to identify and pursue experiences related to their Grand Challenge in five program areas: research, interdisciplinary, entrepreneurship, global, and service.
To launch the upcoming spring application period for UMBC students entering the program, there will be a Grand Challenge Symposium on February 17, 2017, from 1-2:30 pm on the 7th floor of the Library. The symposium will feature 14 UMBC faculty members who will give two minute “mini-talks” on their research as it relates to the 14 Grand Challenges. The event will also showcase some of the work of the current Grand Challenge Scholars, and we will offer light refreshments.
Students who are interested in applying to the Grand Challenge Scholars Program are especially encouraged to attend, as are faculty and staff who have an interest in any of the Grand Challenges or would simply like to learn more about the program. More information about the program is available on the UMBC Grand Challenge Scholars Program Web site and applications are due on April 1.
Course instructors or TAs can arrange for a program representative come to their class to share information about the program by contacting Prof. *protected email* or *protected email*.
Please RSVP for the event, follow the Grad Challenges MyUMBC group and contact *protected email* if you have any questions or comments about the program.
The post Recruiting UMBC Students for the Grand Challenge Scholars Program , Fri. 2/17 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC undergraduates interested in the Grand Challenge Scholars Program are encouraged to attend a symposium and recruiting event at 1:00pm on Friday, February 17. The Grand Challenge...
https://www.csee.umbc.edu/2017/02/26094/
https://dev.my.umbc.edu/api/v0/pixel/news/65413/guest@my.umbc.edu/768c46ccd2112cfc7b58ab1dc2e3fa77/api/pixel
news
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Thu, 02 Feb 2017 09:44:59 -0500
Recruiting UMBC Students for the Grand Challenge Scholars Program , Fri. 2/17

UMBC undergraduates interested in the Grand Challenge Scholars Program are encouraged to attend a symposium and recruiting event at 1:00pm on Friday, February 17.
The Grand Challenge Scholars Program is a program for undergraduates in all majors who are interested in thinking about big problems facing society, and how to solve them from broad, multidisciplinary perspectives. Students select one of 14 Grand Challenges identified by the National Academy Engineering, and work within the cohort of Grand Challenge Scholars to identify and pursue experiences related to their Grand Challenge in five program areas: research, interdisciplinary, entrepreneurship, global, and service.
To launch the upcoming spring application period for UMBC students entering the program, there will be a Grand Challenge Symposium on February 17, 2017, from 1-2:30 pm on the 7th floor of the Library. The symposium will feature 14 UMBC faculty members who will give two minute “mini-talks” on their research as it relates to the 14 Grand Challenges. The event will also showcase some of the work of the current Grand Challenge Scholars, and we will offer light refreshments.
Students who are interested in applying to the Grand Challenge Scholars Program are especially encouraged to attend, as are faculty and staff who have an interest in any of the Grand Challenges or would simply like to learn more about the program. More information about the program is available on the UMBC Grand Challenge Scholars Program Web site and applications are due on April 1.
Course instructors or TAs can arrange for a program representative come to their class to share information about the program by contacting Prof. *protected email* or *protected email*.
Please RSVP for the event, follow the Grad Challenges MyUMBC group and contact *protected email* if you have any questions or comments about the program.
The post Recruiting UMBC Students for the Grand Challenge Scholars Program , Fri. 2/17 appeared first on Department of Computer Science and Electrical Engineering.
]]>
UMBC undergraduates interested in the Grand Challenge Scholars Program are encouraged to attend a symposium and recruiting event at 1:00pm on Friday, February 17. The Grand Challenge...
https://www.csee.umbc.edu/2017/02/recruiting-umbc-students-grand-challenge-scholars-program/
https://dev.my.umbc.edu/api/v0/pixel/news/65414/guest@my.umbc.edu/75d59b24d2fc606194728be636eb9e1c/api/pixel
news
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Thu, 02 Feb 2017 09:44:59 -0500
CSEE faculty on securing the president’s smartphone and avoiding “cyber-fatigue”
 Professor Anupam Joshi, chair of the CSEE Department and director of the UMBC Center for Cybersecurity
Professor Anupam Joshi, chair of the CSEE Department and director of the UMBC Center for Cybersecurity
With a new administration in the White House, securing the president’s smartphone is a national security priority, but exactly what steps are taken to secure the phone are not made public. In a new article in The Conversation, Anupam Joshi, professor and chair of computer science and electrical engineering, and director of the Center for Cybersecurity at UMBC, discusses several likely ways President Trump’s security team is building protections into his phone, through everything from hardware to settings to app restrictions.
Limiting the number of people who have the president’s new phone number and keeping the unique International Mobile Equipment Identity number guarded can prevent potential attackers from accessing confidential information stored on the phone. This method is called “security by obscurity,” says Joshi.
Joshi also says the device Trump will use was likely made by a trusted manufacturer with carefully created and checked parts, explaining that this minimizes the “risk that the hardware would have any vulnerabilities that an attacker could exploit.”
Customizing the operating system, and allowing the phone to connect only with predetermined networks that are regularly monitored can also help protect against attacks, says Joshi. “Limiting its contact with the internet would, of course, by key,” he notes, “though that would also significantly limit the phone’s usefulness to a president whose routine involves constant connection.” Joshi says that limiting the number of apps on the phone, reducing the ability for additional apps to be downloaded and installed, and disabling automatic updates to the phone could keep the device even more secure.
While it is not certain which methods have been employed to secure the presidential smartphone, Joshi says that Trump trading in his commercial-grade phone for a government-secured device is an important first step in protecting the U.S. from hacks and attacks.
In another article in The Conversation, Rick Forno, assistant director of the UMBC Center for Cybersecurity and director of the Cybersecurity Graduate Program at UMBC, addresses the importance of addressing both short-term and long-term cybersecurity issues. He explains that ignoring underlying problems and only addressing small, attention-grabbing issues does not lead to lasting progress. “Cyber-fatigue,” explains Forno, is an “inability to think critically about what needs to happen for meaningful, lasting cybersecurity improvements while focusing only on near-term problems.”
He says that while it is important to evaluate the benefits, conveniences and savings that new products and services may offer, the potential risks and problems should be considered, too. “So instead of repeating the same guidelines and recommendations of the past, it’s time to take a new and unconventional look at our approach to technology and how we secure it,” Forno explains. “Unless we’re willing to go beyond our traditional cybersecurity ‘comfort zone’ and explore new solutions, our cyber-fatigue will worsen.”
Read “How to secure a smartphone for the tweeter-in-chief” and “Overcoming ‘cyber-fatigue’ requires users to step up for security” in The Conversation. Joshi’s piece also appeared in Mashable and Channel Newsasia, and together the articles have already been read over 36,000 times.
Adapted from UMBC News, photo by Marlayna Demond ’11 for UMBC.
The post CSEE faculty on securing the president’s smartphone and avoiding “cyber-fatigue” appeared first on Department of Computer Science and Electrical Engineering.
]]>
Professor Anupam Joshi, chair of the CSEE Department and director of the UMBC Center for Cybersecurity With a new administration in the White House, securing the president’s smartphone is a...
https://www.csee.umbc.edu/2017/01/csee-faculty-securing-presidents-smartphone-avoiding-cyber-fatigue/
https://dev.my.umbc.edu/api/v0/pixel/news/65344/guest@my.umbc.edu/76e0f72417b7ebfef3fd599e48085977/api/pixel
cybersecurity
faculty-and-staff
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 31 Jan 2017 10:17:04 -0500
Tue, 31 Jan 2017 10:17:04 -0500
Capital Area Women in Computing Celebration, 2/24-25
The Capital Area Women in Computing Celebration, sponsored by ACM-W, will be held at Georgetown University on Friday, February 24th and Saturday, February 25.
The celebration will bring together women at the high school, undergraduate, graduate, and professional levels to promote the recruitment, retention, and progression of women in computing fields.
The cost of student attendance is modest: $50 with shared hotel room, or $25 without hotel. Scholarships are available as well.
To get more infomration and to register, visit the CAPWIC 2017 Web site.
Reasons to Attend
- Share your work and ideas with your peers and experts during the poster session, flash talk, or technical short.
- Be inspired. Meet technical women like you and celebrate your accomplishments together.
- Hear success stories of technical women who made it this far!
- Broaden your skills by attending a workshop.
- Meet recruiters from business, industry, and academia for internships, jobs, or graduate programs.
- Find a new job or internship. Bring your resume to our career fair to apply for job and internship opportunities.
- Did we mention that it is FUN!
The post Capital Area Women in Computing Celebration, 2/24-25 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The Capital Area Women in Computing Celebration, sponsored by ACM-W, will be held at Georgetown University on Friday, February 24th and Saturday, February 25. The celebration will bring...
https://www.csee.umbc.edu/2017/01/26080/
https://dev.my.umbc.edu/api/v0/pixel/news/65302/guest@my.umbc.edu/2437b14ddca025743a9a5a0af6b35d63/api/pixel
cwit
graduate
news
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 28 Jan 2017 21:45:14 -0500





 Alejandra Diaz, left, with fellow Cyber Scholars. Photo by Marlayna Demond ’11 for UMBC.
Alejandra Diaz, left, with fellow Cyber Scholars. Photo by Marlayna Demond ’11 for UMBC.
 Professor Anupam Joshi, chair of the CSEE Department and director of the UMBC Center for Cybersecurity
Professor Anupam Joshi, chair of the CSEE Department and director of the UMBC Center for Cybersecurity