talk: Topic Modeling for Analyzing Document Collection, 11am Mon 3/16

CHMPR Lecture Series
-
Topic Modeling for Analyzing Document Collection
Mitsunori Ogihara
Department of Computer Science, University of Miami
11:00am Monday, 16 May 2016, ITE 325b, UMBC
Topic modeling (in particular, Latent Dirichlet Analysis) is a technique for analyzing a large collection of documents. In topic modeling we view each document as a frequency vector over a vocabulary and each topic as a static distribution over the vocabulary. Given a desired number, K, of document classes, a topic modeling algorithm attempts to estimate concurrently K static distributions and for each document how much each K class contributes. Mathematically, this is the problem of approximating the matrix generated by stacking the frequency vectors into the product of two non-negative matrices, where both the column dimension of the first matrix and the row dimension of the second matrix are equal to K. Topic modeling is gaining popularity recently, for analyzing large collections of documents.
In this talk I will present some examples of applying topic modeling: (1) a small sentiment analysis of a small collection of short patient surveys, (2) exploratory content analysis of a large collection of letters, (3) document classification based upon topics and other linguistic features, and (4) exploratory analysis of a large collection of literally works. I will speak not only the exact topic modeling steps but also all the preprocessing steps for preparing the documents for topic modeling.
Mitsunori Ogihara is a Professor of Computer Science at the University of Miami, Coral Gables, Florida. There he directs the Data Mining Group in the Center for Computational Science, a university-wide organization for providing resources and consultation for large-scale computation. He has published three books and approximately 190 papers in conferences and journals. He is on the editorial board for Theory of Computing Systems and International Journal of Foundations of Computer Science. Ogihara received a Ph.D. in Information Sciences from Tokyo Institute of Technology in 1993 and was a tenure-track/tenured faculty member in the Department of Computer Science at the University of Rochester from 1994 to 2007.
]]>
CHMPR Lecture Series Topic Modeling for Analyzing Document Collection Mitsunori Ogihara Department of Computer Science, University of Miami 11:00am Monday, 16 May 2016, ITE 325b,...
http://www.csee.umbc.edu/2016/05/talk-topic-modeling-for-analyzing-document-collection-11am-mon-316/
https://dev.my.umbc.edu/api/v0/pixel/news/60131/guest@my.umbc.edu/91fb0afc30b52a265bc7d9a766de7bd8/api/pixel
computer-science
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 12 May 2016 17:26:43 -0400
talk: Human mental models and robots: Grasping and tele-presence, 11am 5/9

Human mental models and robots:
Grasping and tele-presence
Dr. Cindy Grimm, Oregon State University
11:00-12:00 Monday 9 May 2016, ITE 325b
In this talk I will cover two separate research efforts in robotics, both of which use human mental models to improve robotic functionality. Robots struggle to pick up and manipulate physical objects, yet humans do this with ease – but can’t tell you how they do it. In this research we focus on how to capture human data in such a way as to gain insight into how people structure the grasping task. Specifically, we look at the role of perceptual cues in evaluating grasps and mental classification models of grasps (i.e., all these grasps are the “same”). In the second half of the talk I will switch to discussing how human mental models of privacy, trust, and presence come in to play in remote tele-presence applications (“Skype-on-a-movable-stick”).
Dr. Cindy Grimm is currently an associate professor at Oregon State University (since 2013) in the School of Mechanical, Industrial, and Manufacturing Engineering (application area robotics). Prior to that she was tenured faculty at Washington University in St. Louis in Computer Science (12 years). Her research areas range from 3D sketching to biological modeling to human-robot interaction. She approaches these problems with a combination of mathematical models and empirically-verified human-centered design (HCD). Mathematical models provide a sound, quantitative, rigorous, elegant basis for representing shape and function, and are a core part of the “language” of computation. Including a human in the loop is a key component of the application areas she works in; HCD provides the mechanism for addressing the fundamental problem of how to make mathematical computation “useful” for humans. She has worked with collaborators in fields ranging from psychology, mechanical and biological engineering, statistics, to art.
]]>
Human mental models and robots: Grasping and tele-presence Dr. Cindy Grimm, Oregon State University 11:00-12:00 Monday 9 May 2016, ITE 325b In this talk I will cover two separate research...
http://www.csee.umbc.edu/2016/05/talk-human-mental-models-and-robots-grasping-and-tele-presence-11am-59/
https://dev.my.umbc.edu/api/v0/pixel/news/59974/guest@my.umbc.edu/458296f1894f82516822f9488eb130aa/api/pixel
computer-engineering
computer-science
news
research
robotics
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Fri, 06 May 2016 12:51:56 -0400
Innovations in Cybersecurity Education Workshop, Friday June 3, UMBC

The third Innovations in Cybersecurity Education Workshop (ICEW) will be held from 9:00am to 5:00pm on Friday, June 3, 2016 on the UMBC campus.
ICEW is a free regional workshop on cybersecurity education from high school through post-graduate. It is intended primarily for educators who are teaching cybersecurity at high schools, colleges, and community colleges. Anyone is welcome to attend, including teachers, students, administrators, researchers, and government officials. It will highlight master teachers and ongoing educational projects, including an effort at the US Naval Academy to teach cybersecurity to all midshipmen. The workshop will feature hands-on learning activities, including secure programming, cyber competition, and an educational game.
Sessions will include:
-
Secure coding through hands-on exercise: Blair Taylor and Siddharth Kaza (Towson University) will show how to carry out self-contained, lab-based modules designed to be injected into CS0-CS2 introductory computer science courses.
-
Using a message board as a hands-on learning tool for Cyber Security II: LCDR Chris W. Hoffmeister (US Naval Academy) will discuss how to solve security challenges involving a simple, configurable HTML message board.
-
Hands-on vulnerability testing: Marcelle Lee (Anne Arundel Community College) and Steve Morrill (Loyola Blakefield) will demonstrate how to engage in a hands-on challenge and learning experience to help highlight the vulnerabilities in systems, with you in the driver’s seat. Participants of any skill level will learn strategies and techniques for determining if a system is vulnerable.
-
Hands-on group threat brainstorming with Security Cards: Tamara Denning (University of Utah) will demonstrate teaching students how to think broadly and creatively about computer security threats using 42 Security Cards along four dimensions (suits): human impact, adversary’s motivation, adversary’s resources, and adversary’s methods.
ICEW is free and open to the public — all are welcome to attend. This workshop will to be of interest to educators, school administrators, undergraduate and graduate students, and government officials. Lunch will be provided. There is ample parking.
For more information and to register, see the 2016 ICEW Web site.
]]>
The third Innovations in Cybersecurity Education Workshop (ICEW) will be held from 9:00am to 5:00pm on Friday, June 3, 2016 on the UMBC campus. ICEW is a free regional workshop on cybersecurity...
http://www.csee.umbc.edu/2016/05/innovations-in-cybersecurity-education-workshop-friday-june-3-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/59970/guest@my.umbc.edu/ae265d84bb1ddf2a09c7fbc751036649/api/pixel
computer-science
cybersecurity
events
icew
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Fri, 06 May 2016 10:21:34 -0400
Sun, 29 May 2016 09:21:34 -0400
talk: Statistical Testing of Hash Bit Sequences, 11:15am Fri May 6, UMBC

The UMBC Cyber Defense Lab presents
Statistical Testing of Hash Bit Sequences
Enis Golaszewski
CSEE, UMBC
11:15am-12:30pm Friday, 6 May 2016, ITE 237
We tested bit sequences generated from the MD5 hash function using multinomial distribution and close-point spatial statistical tests for randomness. We found that bit sequences generated from truncated-round MD5 hash fail these tests for high- and low-density input choices.
In 2000, the National Institute of Standards and Technology concluded a competition to select the Advanced Encryption Standard. One of the requirements for candidates was randomness of output bits. The techniques used to evaluate symmetric block cipher randomness have not been extensively applied to hash functions.
In this study, we adapt a subset of the techniques used to analyze the randomness of AES candidate algorithms to study the randomness of the well-known MD5 hash function. Our approach uses high-density, lo- density, and chained-input methods to generate MD5 hashes. We concatenate these hash outputs and subjected them to multinomial distribution and close-point spatial tests. We iterated this approach over reduced-round versions of MD5. Our presentation includes specifications for the input methods, details on the statistical tests, and analysis of the statistical results.
Through statistical testing of concatenated MD5 hashes, we derive results that demonstrate a link between the performance of the concatenated hash bit sequences in our statistical testing and the number of hash rounds applied to the high-density and low-density input methods. Randomness is a desirable property for cryptographic hash functions. We present a new approach that facilitates the analysis and interpretation of hash functions for statistical randomness.
About the Speaker. Enis Golaszewski is a prospective PhD student in CS at UMBC, working with Dr. Alan T. Sherman. His research interests include the security of software-defined networks. He graduated from UMBC in CS in December 2015 and was a student in the fall 2015 INSuRE class. Email: <Sorry, you need javascript to view this email address. >
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Statistical Testing of Hash Bit Sequences Enis Golaszewski CSEE, UMBC 11:15am-12:30pm Friday, 6 May 2016, ITE 237 We tested bit sequences generated...
http://www.csee.umbc.edu/2016/05/20573/
https://dev.my.umbc.edu/api/v0/pixel/news/59963/guest@my.umbc.edu/fe105755ae51867d909cc45707e8ac6a/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 05 May 2016 22:12:30 -0400
Thu, 05 May 2016 22:12:30 -0400
UMBC students demonstrate smartphone applications, 12:30-2:30 Tue 5/10

Student groups drawn from two UMBC classes will demonstrate twelve mobile applications they developed as projects from 12:30 to 2:30 on Tuesday, 10 May 2016 in the UC Ballroom. Pizza will be provided.
The projects are a result of an innovative collaboration between a computer science class lead by Professor Nilanjan Banerjee (CMSC 678 Mobile Computing) and a visual arts class lead by Professor Viviana Chacon (ART 434 Advanced Interface Design).
The two faculty were awarded a grant from the fall 2015 round of the Hrabowski Fund for Innovation competition to develop and evaluate the collaboration between the two courses. The classes held regular joint sessions and each project group comprised students from both Engineering and Visual Arts.
In ART 434 Prof. Cordova concentrated on the visual experience of the interface in mobile and desktop applications, while in CMSC 628 Prof. Banerjee provided the tools necessary to design and implement mobile applications. Specific mobile development topics such as user interface design and implementation, accessing and displaying sensor and location data, and mobile visual design were co-‐taught by both instructors. Teams comprising Engineering and Visual Arts students designed and built mobile applications for local clients in Baltimore and Washington DC area.
A poster describing the event has brief descriptions of the twelve class projects.
]]>
Student groups drawn from two UMBC classes will demonstrate twelve mobile applications they developed as projects from 12:30 to 2:30 on Tuesday, 10 May 2016 in the UC Ballroom. Pizza will be...
http://www.csee.umbc.edu/2016/05/umbc-students-demonstrate-smartphone-applications-1230-230-tue-510/
https://dev.my.umbc.edu/api/v0/pixel/news/59887/guest@my.umbc.edu/60403a18ab2b56f9de53f5602411740f/api/pixel
computer-engineering
computer-science
events
graduate
news
teaching-innovation
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Tue, 03 May 2016 12:37:27 -0400
NSF CyberCorps: Scholarship For Service, May 15 deadline

UMBC undergraduate and graduate students interested in cybersecurity can apply for an Federal CyberCorps: Scholarship For Service scholarship by 15 May 2016. This application deadline will be the last one under the current NSF grant, which ends August 2017.
The Federal CyberCorps: Scholarship For Service program is designed to increase and strengthen the cadre of federal information assurance professionals that protect the government’s critical information infrastructure. This program provides scholarships that may fully fund the typical costs incurred by full-time students while attending a participating institution, including tuition and education and related fees. Participants also receive stipends of $22,500 for undergraduate students and $34,000 for graduate students.
Applicants must be be full-time UMBC students within two years of graduation with a BS or MS degree; a student within three years of graduation with both the BS/MS degree; a student participating in a combined BS/MS degree program; or a research-based doctoral student within three years of graduation in an academic program focused on cybersecurity or information assurance. Recipients must also be US citizens or permanent residents; meet criteria for Federal employment; and be able to obtain a security clearance, if required.
For more information and instructions on how to apply see the UMBC CISA site (use old application form, and be sure to include the cover sheet).
]]>
UMBC undergraduate and graduate students interested in cybersecurity can apply for an Federal CyberCorps: Scholarship For Service scholarship by 15 May 2016. This application deadline will be the...
http://www.csee.umbc.edu/2016/04/nsf-cybercorps-scholarship-for-service-may-15-deadline/
https://dev.my.umbc.edu/api/v0/pixel/news/59888/guest@my.umbc.edu/ce66f650f9ee28ba90fc01b8e05b7f37/api/pixel
cybersecurity
graduate
news
sfs
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 29 Apr 2016 08:54:57 -0400
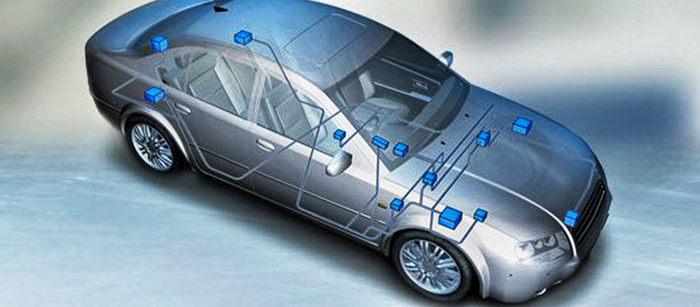
tutorial: Design, Analysis and Security of Automotive Networks, 2pm 4/29
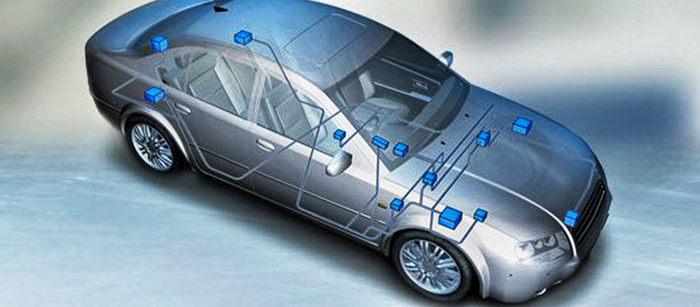
Design, Analysis and Security of Automotive Networks
Sekar Kulandaivel
University of Maryland, Baltimore County
2:00-3:30pm Friday, 29 April 2016, ITE 325b
As more electronic and wireless technologies permeate modern vehicles, understanding the design of an embedded automotive network becomes necessary to protect drivers from external agents with a malicious intent to disrupt onboard electronics. By analyzing the different types of automotive networks and current security issues that the industry faces, we will learn how intruders are able to access an automotive network, read data that streams from the connected nodes and inject potentially malicious messages. This presentation will cover the electrical design of automotive networks, the communication protocols between electronic control units, methods for analyzing network messages and a detailed overview of previous automotive attacks and current security issues.
Sekar Kulandaivel is a Meyerhoff Scholar and Computer Engineering undergraduate student at UMBC. He currently works on designing an intrusion detection system for automotive networks with Dr. Nilanjan Banerjee of the UMBC Eclipse Cluster. Sekar has had previous internships at MIT Lincoln Laboratory, Northrop Grumman Corporation and Johns Hopkins University. He will attend Carnegie Mellon University in Fall 2016 to pursue a PhD in Electrical and Computer Engineering with a focus in electric vehicle security.
]]>
Design, Analysis and Security of Automotive Networks Sekar Kulandaivel University of Maryland, Baltimore County 2:00-3:30pm Friday, 29 April 2016, ITE 325b As more electronic and wireless...
http://www.csee.umbc.edu/2016/04/tutorial-design-analysis-and-security-of-automotive-networks-2pm-429/
https://dev.my.umbc.edu/api/v0/pixel/news/59723/guest@my.umbc.edu/3ebfa9715706199e10a97506bbec1fd5/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 27 Apr 2016 14:42:55 -0400
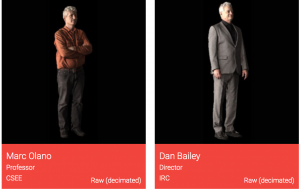
3D Capturing the Future at UMBC

Nestled in the back of room 109 of the Information Technology and Engineering building, Dan Bailey, head of the Image Researching Center (IRC) is being captured. He sits in the center of the room, in a open metal rig with cameras that are surrounding him. IRC staff walk around him, fine tuning each of the camera settings as they make their final preparations.
The lights turn off, and within a second a bright flash illuminates the room. The lights turn back on, and a staff member exclaims “got it” as another successful 3D capture has been performed at the IRC. In the next few hours a powerful computer will start to build a 3D scan of Dan Bailey.
“Being able to capture a 3D model is just a priceless ability,”
Outside of the room sits Dr. Marc Olano, a professor of Computer Science & Electrical Engineering, who helps run the studio. Olano and Bailey worked with Direct Dimensions Inc, a company based in Owings Mills, Maryland, and funded the space through a $180,000 grant from the National Science Foundation.
Olano told Stephen Babcock, a reporter at Technical.ly Baltimore that “Being able to capture a 3D model is just a priceless ability,” and “That flash is the first step.”

Dr. Marc Olano outside the capture room. Here, he can view the 3D models and manipulate them.
The system is smart enough to ignore all the cameras around the person or object and instead finds unique points of features to focus on. In addition, there are projectors that help capture something that doesn’t have enough detail to focus on by projecting more detail onto a person or object so the person can find it.
Between captures, there are a couple of tools that are used to help calibrate the space. One tool is a pole that is used to help position the cameras using tape on the pole that gives reference points for the center and edge of the frame for the cameras.
For capturing, there is a calibration dummy made out of cardboard construction tubes with a lot of different clothing patterns. This is essential in making it easier to build a 3D model of the dummy, as the reconstruction process can find the shape of the object and camera positions simultaneously, but if the part of the object or person you are scanning is too featureless, it can have trouble solving for both of those at once
After the image is captured, the computer starts building a 3D model out of 90 images. Zooming in on the image, you can actually see each individual polygon that makes up the image.
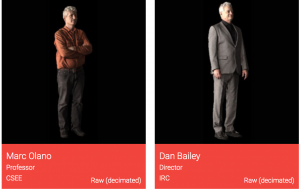
3D scans of Marc Olano and Dan Bailey done in the capture studio.
“This [studio] serves as not only the intersection of art and computer science, but other disciplines as well.”
Olano believes that this 3D capture studio can go beyond computer science. “This [studio] serves as not only the intersection of art and computer science, but other disciplines as well.” When scanning in a person, it is possible to make that person into an animation model for use in video games.
Museums could ask to scan in historical objects so that one could rotate and inspect the object at any angle they want. People who have had amputations could get scanned and have something custom built for them. The possibilities for this space are immense and will continue to grow over time.
The 3D capture studio is still limited to only a few projects at a time but Olano hopes to open it up to more departments soon. You can view some of the scans the studio has done online here.
]]>
Nestled in the back of room 109 of the Information Technology and Engineering building, Dan Bailey, head of the Image Researching Center (IRC) is being captured. He sits in the center of the room,...
http://www.csee.umbc.edu/2016/04/3d-capturing-the-future-at-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/59697/guest@my.umbc.edu/99ea18721c868dc772a346e9c122057b/api/pixel
computer-engineering
news
other
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 26 Apr 2016 14:30:52 -0400
Tue, 26 Apr 2016 14:30:52 -0400
talk: Medical Epistemology: A Gerontologist’s Perspective, 3pm Wed 4/27

CHMPR Seminar
Medical Epistemology: A Gerontologist’s Perspective
Dr. John D. Sorkin, M.D., Ph.D.
University of Maryland School of Medicine
3:00pm Wednesday, 27 April 2016, ITE 325b
The randomized clinical trial is the gold standard method by which we test a hypothesis positing an association between an exposure and outcome. Unfortunately many hypotheses are not grist for a clinical trial. It would, for example not be ethically permissible to randomize people to smoking vs. non-smoking if we wanted to study the hypothesis that smoking is associated with increased incidence of lung cancer. Similarly it would not be ethical to randomize pregnant women to being infected or not infected with Zika virus to determine if maternal Zika infection is associated with microcephaly. Clinical trials are also not helpful in determining the relation between a putative exposure and a rare disease such as Pick’s disease (a rare type of frontotemporal dementia) as the number of subjects who would need to be studied is prohibitively large.
The movement over the last decade away from paper-based charts to the electronic medical record (EMR) and advances in the speed of computers allow us to process large volumes of data in near real-time, and herald the advent of clinical studies based on “big data”. The availability of big data requires us to rethink how we can establish an association between cause and effect because the big data we obtain from the EMR are not collected from randomized clinical trials, and as noted above a clinical trial cannot be used to study many diseases. Further making inferences based on the EMR can be difficult because data gleamed from the electronic medical record can be confounded by changes brought about by the aging process which include primary aging (i.e., the aging process itself), secondary aging (i.e., changes brought about by changes in lifestyle as we get older) and tertiary aging (i.e., disease). Fortunately epidemiologists have designed and used study designs other than the clinical trials for years to gain insight into the relation between exposure and disease. The aim of my talk is to review five study designs, cross-sectional, time-series and longitudinal, case-control and cohort study designs, that can be used to identify change, quantify the rate at which changes occurs with aging, and to separate biological aging from the effects of life style and disease. In addition to presenting the five study designs, I will review the strengths and weaknesses of the five study designs. It is my hope that thinking about five study designs will help you design analyses that make use of big data to examine questions relevant to public health and treatment of disease.
Dr. John Sorkin is a professor at the University of Maryland School of Medicine. His research examines the changes that occur with aging in carbohydrate and lipid metabolism, obesity, and body fat distribution. He is interested in measuring the changes and determining the relation of the changes to the development of diabetes, cardiovascular disease, death, morbidity, and mortality. These interests have lead him to try to identify the phenotypes associated with longevity and the genetics of longevity in collaboration with Drs. Shuldiner and Mitchell. Dr. Sorkin is Chief of Biostatistics and Informatics for the Division of Gerontology and is PI of the Statistics Core for the University of Maryland Claude D. Pepper Older Americans Independence Center and Baltimore VA Geriatrics Research, Education and Clinical Center.
]]>
CHMPR Seminar Medical Epistemology: A Gerontologist’s Perspective Dr. John D. Sorkin, M.D., Ph.D. University of Maryland School of Medicine 3:00pm Wednesday, 27 April 2016, ITE 325b The...
http://www.csee.umbc.edu/2016/04/big_data_medicine_sorkin/
https://dev.my.umbc.edu/api/v0/pixel/news/59660/guest@my.umbc.edu/4ce4f24cac9eb1b562252d915b758e89/api/pixel
computer-science
data-science
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 25 Apr 2016 14:59:37 -0400
Blindfold Chess Spectacular at UMBC, 9-6 Sun 4/24

This Sunday as part of Quadmania, the UMBC Chess Program will present a Blindfold Chess Spectacular. UMBC alum International Grandmaster Timur Gareyev will:
- 9am – simultaneously play ten challengers while blindfolded
- 1pm – explain how he does it
- 2-6pm – play a knockout match against UMBC’s top three players where
everyone will be blindfolded.
The event is free and open to the public.
Gareyev is preparing to break the world record this fall in Prague by playing and defeating 50 challengers while he is blindfolded (the world record is 46).
UMBC students AbhilashPuranik (CSEE) and Nathanial Wong will play and help with the chess technology. Using four DGT boards, we will display four games and broadcast them live to the Internet (via the website chess24). In the DGT technology, each piece has an RFID chip broadcasting its identify. Antennas under each row and column receive the signals. Software interpolates the positions, generates a graphical display, and expresses the move in standard PGN notation.
Pieter Heesters, a 6th grader who won a scholarship to UMBC by winning the 2016 Maryland Scholastic Chess Championship, will also play.
]]>
This Sunday as part of Quadmania, the UMBC Chess Program will present a Blindfold Chess Spectacular. UMBC alum International Grandmaster Timur Gareyev will: 9am – simultaneously play ten...
http://www.csee.umbc.edu/2016/04/blindfold-chess-spectacular-at-umbc-9-6-sun-424/
https://dev.my.umbc.edu/api/v0/pixel/news/59616/guest@my.umbc.edu/2fddda280891f4c99a8e5dba13a1d748/api/pixel
events
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 23 Apr 2016 23:03:14 -0400