talk: Engineering Notes on Homomorphic Private Information Retrieval, 11:15 Fri 12/4

The UMBC Cyber Defense Lab presents
Engineering Notes on Homomorphic
Private Information Retrieval
Russ Fink
Johns Hopkins University Applied Physics Lab
11:15am-12:30pm, Friday, 4 December 4 2015, ITE 231
For two years, we have been investigating applications of private information retrieval (PIR) using the additive homomorphic scheme designed by Paillier that forms the basis of a space efficient PIR system by Ostrovsky, Skeith, and Bethencourt. We have implemented a working prototype and gained some insights about the technique, and identified improvements to make it practical to real-world privacy problems. I will present an overview of the technique, present a real world use case, and discuss our technical contributions and ongoing challenges.
Dr. Russ Fink is Chief Engineer of the Enterprise Security Group at APL. He earned the PhD from UMBC with a dissertation on applying trustworthy computing to voting.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Engineering Notes on Homomorphic Private Information Retrieval Russ Fink Johns Hopkins University Applied Physics Lab 11:15am-12:30pm, Friday, 4...
https://www.csee.umbc.edu/2015/12/talk-engineering-notes-on-homomorphic-private-information-retrieval-1115-fri-124/
https://dev.my.umbc.edu/api/v0/pixel/news/57865/guest@my.umbc.edu/eee901c0dc911b198ec2ca6c27a15416/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 21:11:00 -0500
talk: Addressing Energy & Big Data Challenges in Microgrids, 1pm 12/4
The UMBC CSEE Seminar Series Presents
Addressing Energy and Big Data
Challenges in Microgrids
Prof. Ting Zhu, UMBC
1-2pm Friday, Dec 4, 2015, ITE 325B
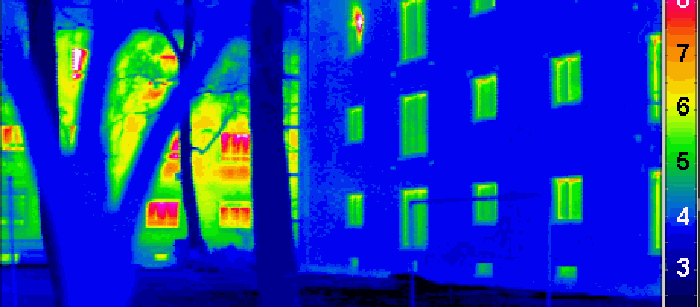
Buildings account for over 75% of the electricity consumption in the United States. To reduce electricity usage and peak demand, many utility companies are introducing market-based time-of-use (TOU) pricing models. In parallel, government programs that increase the fraction of renewable energy are incentivizing residential consumers to adopt on-site renewables and energy storage. Connecting on-site renewables and energy storage between homes forms a sustainable microgrid that is capable of generating, storing, and sharing electricity to balance local generation and consumption in residential areas. In this talk, I will present two pieces of our work in this area. The first work targets at minimizing the electricity cost from a utility company for a microgrid under different market-based TOU pricing models. This work is selected as the best paper runners up at BuildSys 2014. The goals of the second work are real-time energy data gathering, compression, and recovery based on unique features in the energy consumption patterns. In the end of the talk, I will also briefly introduce some of my latest work in indoor localization, networking, and smart health.
Ting Zhu is an assistant professor in the CSEE at UMBC. He received the Computing Innovation Fellowship in 2010. His papers have been selected in the best paper award finalist in multiple conferences (i.e., SenSys ’10, e-Energy ’13, and BuildSys ’14). He has a broad research interest in areas such as internet of things, energy, networking, systems, big data, and security. He is looking for undergraduate, Master and PhD students to work in the above areas.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
]]>
The UMBC CSEE Seminar Series Presents Addressing Energy and Big Data Challenges in Microgrids Prof. Ting Zhu, UMBC 1-2pm Friday, Dec 4, 2015, ITE 325B Buildings account for over 75% of...
http://www.csee.umbc.edu/2015/12/talk-addressing-energy-big-data-challenges-in-microgrids-1pm-124/
https://dev.my.umbc.edu/api/v0/pixel/news/56443/guest@my.umbc.edu/e822f43f6b038094d3d23344fea8b08d/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 17:39:02 -0500
Thu, 03 Dec 2015 17:39:02 -0500
talk: Addressing Energy & Big Data Challenges in Microgrids, 1pm 12/4
The UMBC CSEE Seminar Series Presents
Addressing Energy and Big Data
Challenges in Microgrids
Prof. Ting Zhu, UMBC
1-2pm Friday, Dec 4, 2015, ITE 325B
Buildings account for over 75% of the electricity consumption in the United States. To reduce electricity usage and peak demand, many utility companies are introducing market-based time-of-use (TOU) pricing models. In parallel, government programs that increase the fraction of renewable energy are incentivizing residential consumers to adopt on-site renewables and energy storage. Connecting on-site renewables and energy storage between homes forms a sustainable microgrid that is capable of generating, storing, and sharing electricity to balance local generation and consumption in residential areas. In this talk, I will present two pieces of our work in this area. The first work targets at minimizing the electricity cost from a utility company for a microgrid under different market-based TOU pricing models. This work is selected as the best paper runners up at BuildSys 2014. The goals of the second work are real-time energy data gathering, compression, and recovery based on unique features in the energy consumption patterns. In the end of the talk, I will also briefly introduce some of my latest work in indoor localization, networking, and smart health.
Ting Zhu is an assistant professor in the CSEE at UMBC. He received the Computing Innovation Fellowship in 2010. His papers have been selected in the best paper award finalist in multiple conferences (i.e., SenSys ’10, e-Energy ’13, and BuildSys ’14). He has a broad research interest in areas such as internet of things, energy, networking, systems, big data, and security. He is looking for undergraduate, Master and PhD students to work in the above areas.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
]]>
The UMBC CSEE Seminar Series Presents Addressing Energy and Big Data Challenges in Microgrids Prof. Ting Zhu, UMBC 1-2pm Friday, Dec 4, 2015, ITE 325B Buildings account for over 75% of...
https://www.csee.umbc.edu/2015/12/talk-addressing-energy-big-data-challenges-in-microgrids-1pm-124/
https://dev.my.umbc.edu/api/v0/pixel/news/57866/guest@my.umbc.edu/801e60281c11ae1ebc007917ab033570/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 17:39:02 -0500
Rick Forno, “Ask the Experts” regarding ID theft

WalletHub.Com has released its annual survey regarding the states most vulnerable to identity theft.
As a cyber-oriented culture, it’s natural to wonder whether and how a person’s daily habits assist hackers in stealing personal information. Accordingly, the site consulted a panel of cybersecurity professors for answers to such questions and offer advice on how to safeguard data against cybercriminals. Items asked include:
- How should consumers choose among third-party providers offering services to protect their identity and personal data?
- What can individuals do to guard against identity theft?
- Is the recent expansion of social media facilitating identity thefts?
- Should the federal government intervene to establish a clear process for victims of identity theft looking to clear their name?
Dr. Rick Forno, CSEE’s Cybersecurity Graduate Program Director and Assistant Director of UMBC’s Center for Cybersecurity, was one of those invited to offer comments on this ongoing problem facing Internet users.
]]>
WalletHub.Com has released its annual survey regarding the states most vulnerable to identity theft. As a cyber-oriented culture, it’s natural to wonder whether and how a person’s daily habits...
http://www.csee.umbc.edu/2015/12/rick-forno-ask-the-experts-regarding-id-theft/
https://dev.my.umbc.edu/api/v0/pixel/news/56430/guest@my.umbc.edu/7b3fbcc415cac2bc38ac84ae8c180190/api/pixel
computer-science
cybersecurity
news
other
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 03 Dec 2015 12:48:21 -0500
Rick Forno, “Ask the Experts” regarding ID theft

WalletHub.Com has released its annual survey regarding the states most vulnerable to identity theft.
As a cyber-oriented culture, it’s natural to wonder whether and how a person’s daily habits assist hackers in stealing personal information. Accordingly, the site consulted a panel of cybersecurity professors for answers to such questions and offer advice on how to safeguard data against cybercriminals. Items asked include:
- How should consumers choose among third-party providers offering services to protect their identity and personal data?
- What can individuals do to guard against identity theft?
- Is the recent expansion of social media facilitating identity thefts?
- Should the federal government intervene to establish a clear process for victims of identity theft looking to clear their name?
Dr. Rick Forno, CSEE’s Cybersecurity Graduate Program Director and Assistant Director of UMBC’s Center for Cybersecurity, was one of those invited to offer comments on this ongoing problem facing Internet users.
]]>
WalletHub.Com has released its annual survey regarding the states most vulnerable to identity theft. As a cyber-oriented culture, it’s natural to wonder whether and how a person’s daily habits...
https://www.csee.umbc.edu/2015/12/rick-forno-ask-the-experts-regarding-id-theft/
https://dev.my.umbc.edu/api/v0/pixel/news/57867/guest@my.umbc.edu/7e8595e044122aeb9a02018f60f69e4c/api/pixel
computer-science
cybersecurity
news
other
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 12:48:21 -0500
PhD defense: Infrastructure-less Group Data Sharing using Smart Devices

Ph.D. Dissertation Defense
Infrastructure-less Group Data
Sharing using Smart Devices
Ahmed Shahin
2:30 Tuesday, 8 December 2015, ITE-346
Advances in pervasive communication technology have enabled many unconventional applications that facilitate and improve the safety and quality of life in modern society. Among emerging applications is situational awareness where individuals and first-responders receive timely alerts about serious events that could have caused the interruption of the services provided by the communication infrastructure such as cellular networks, Wi-Fi hotspots, etc. Another example is when exchanging road conditions between peer-to-peer networked vehicles without the involvement of roadside units. The popularity of smart portable devices such as iPhone and Android powered phones and tablets has made them an attractive choice that can play a role in the realization of these emerging applications. These devices support multiple communication standards and thus enable Device-to-Device (D2D) data exchange at an increased level of convenience. By using technologies such as Bluetooth, Wi-Fi ad-hoc mode and Wi-Fi Direct, these devices are able to communicate without the need for any communication infrastructures. In addition, many of these devices are equipped with sensors that can provide a wealth of information about the surroundings once their readings are aggregated.
However, most existing protocols for data sharing among devices either require an internet connection, which may not be available and may incur extra costs in some cases, or suffer from the device’s operating system limitations. Actually there is no existing solution that allows a set of devices to start sharing data dynamically without forcing the users to apply an elaborate procedure for setting up a group. These shortcomings render existing solutions unsuitable for emergency cases. In this dissertation proposal, we tackle such a problem by developing a framework for enabling data exchange in a cost-effective and timely manner through the establishment of peer-to-peer links among smart devices. In addition, our framework opts to minimize the user required interaction for setting up a connection and overcome the limitations of the operating system.
Our framework consists of a set of protocols for group data exchange using Wi-Fi Direct on Android devices. First we present an Efficient and Lightweight protocol for peer-to-peer Networking of Android smart devices over Wi-Fi Direct (ELN). ELN main goal is to overcome the Wi-Fi Direct support limitations in Android, thus allowing the devices in one Wi-Fi Direct group to communicate together. The ELN protocol is validated by implementing a group chatting application. In addition, we present a protocol for Alert Dissemination using Service discovery (ADS) in Wi-Fi Direct. ADS uses the service discovery feature of Wi-Fi Direct for distributing alerts to nearby devices without requiring any prior connections and thus avoids the setup delay in creating Wi-Fi Direct groups and the limitations of multi-group connectivity in Android. ADS is validated by implementing a hazard propagation application for Android. Finally, we present an Efficient Multi-group formation and Communication (EMC) protocol for Wi-Fi Direct. EMC exploits the battery specifications of the devices to qualify potential group owners and enable dynamic formation of efficient groups. Moreover, EMC allows data exchange between different Wi-Fi direct groups. Part of our implementation of EMC in Android involves the modification of the Android source code to allow multi-group support. A chat application is developed to validate EMC.
To complete the dissertation, we plan to extend EMC by replacing the static assignment of devices’ addresses in our current implementation with an IP address negotiation protocol that runs before creating groups. Such an extension would give greater flexibility in adapting EMC. In addition, we plan to define some criteria for selecting proxy members in order to allow maximum coverage and allow the D2D communication to span a larger geographical area. In addition, we will develop a simulator to do large scale testing for the proposed framework. Finally, we would like to explore the use of dual transceivers in order to increase the robustness of D2D connections when the wireless channels are subject to varying level of interference; particularly we like to investigate the integration of Bluetooth Low Energy within our framework to enable group membership of nodes that do not have Wi-Fi Direct or suffer interference that makes the Wi-Fi Direct links unstable.
Committee: Drs. Mohamed Younis (Chair), Charles Nicholas, Chintan Patel, Tinoosh Mohsenin
]]>
Ph.D. Dissertation Defense Infrastructure-less Group Data Sharing using Smart Devices Ahmed Shahin 2:30 Tuesday, 8 December 2015, ITE-346 Advances in pervasive communication technology...
http://www.csee.umbc.edu/2015/12/phd-defense-infrastructure-less-group-data-sharing-using-smart-devices/
https://dev.my.umbc.edu/api/v0/pixel/news/56419/guest@my.umbc.edu/1defac66c310ae1b6a0776a1f95583a8/api/pixel
computer-engineering
computer-science
defense
graduate
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 09:07:09 -0500
Thu, 03 Dec 2015 09:07:09 -0500
PhD defense: Infrastructure-less Group Data Sharing using Smart Devices

Ph.D. Dissertation Defense
Infrastructure-less Group Data
Sharing using Smart Devices
Ahmed Shahin
2:30 Tuesday, 8 December 2015, ITE-346
Advances in pervasive communication technology have enabled many unconventional applications that facilitate and improve the safety and quality of life in modern society. Among emerging applications is situational awareness where individuals and first-responders receive timely alerts about serious events that could have caused the interruption of the services provided by the communication infrastructure such as cellular networks, Wi-Fi hotspots, etc. Another example is when exchanging road conditions between peer-to-peer networked vehicles without the involvement of roadside units. The popularity of smart portable devices such as iPhone and Android powered phones and tablets has made them an attractive choice that can play a role in the realization of these emerging applications. These devices support multiple communication standards and thus enable Device-to-Device (D2D) data exchange at an increased level of convenience. By using technologies such as Bluetooth, Wi-Fi ad-hoc mode and Wi-Fi Direct, these devices are able to communicate without the need for any communication infrastructures. In addition, many of these devices are equipped with sensors that can provide a wealth of information about the surroundings once their readings are aggregated.
However, most existing protocols for data sharing among devices either require an internet connection, which may not be available and may incur extra costs in some cases, or suffer from the device’s operating system limitations. Actually there is no existing solution that allows a set of devices to start sharing data dynamically without forcing the users to apply an elaborate procedure for setting up a group. These shortcomings render existing solutions unsuitable for emergency cases. In this dissertation proposal, we tackle such a problem by developing a framework for enabling data exchange in a cost-effective and timely manner through the establishment of peer-to-peer links among smart devices. In addition, our framework opts to minimize the user required interaction for setting up a connection and overcome the limitations of the operating system.
Our framework consists of a set of protocols for group data exchange using Wi-Fi Direct on Android devices. First we present an Efficient and Lightweight protocol for peer-to-peer Networking of Android smart devices over Wi-Fi Direct (ELN). ELN main goal is to overcome the Wi-Fi Direct support limitations in Android, thus allowing the devices in one Wi-Fi Direct group to communicate together. The ELN protocol is validated by implementing a group chatting application. In addition, we present a protocol for Alert Dissemination using Service discovery (ADS) in Wi-Fi Direct. ADS uses the service discovery feature of Wi-Fi Direct for distributing alerts to nearby devices without requiring any prior connections and thus avoids the setup delay in creating Wi-Fi Direct groups and the limitations of multi-group connectivity in Android. ADS is validated by implementing a hazard propagation application for Android. Finally, we present an Efficient Multi-group formation and Communication (EMC) protocol for Wi-Fi Direct. EMC exploits the battery specifications of the devices to qualify potential group owners and enable dynamic formation of efficient groups. Moreover, EMC allows data exchange between different Wi-Fi direct groups. Part of our implementation of EMC in Android involves the modification of the Android source code to allow multi-group support. A chat application is developed to validate EMC.
To complete the dissertation, we plan to extend EMC by replacing the static assignment of devices’ addresses in our current implementation with an IP address negotiation protocol that runs before creating groups. Such an extension would give greater flexibility in adapting EMC. In addition, we plan to define some criteria for selecting proxy members in order to allow maximum coverage and allow the D2D communication to span a larger geographical area. In addition, we will develop a simulator to do large scale testing for the proposed framework. Finally, we would like to explore the use of dual transceivers in order to increase the robustness of D2D connections when the wireless channels are subject to varying level of interference; particularly we like to investigate the integration of Bluetooth Low Energy within our framework to enable group membership of nodes that do not have Wi-Fi Direct or suffer interference that makes the Wi-Fi Direct links unstable.
Committee: Drs. Mohamed Younis (Chair), Charles Nicholas, Chintan Patel, Tinoosh Mohsenin
]]>
Ph.D. Dissertation Defense Infrastructure-less Group Data Sharing using Smart Devices Ahmed Shahin 2:30 Tuesday, 8 December 2015, ITE-346 Advances in pervasive communication technology...
https://www.csee.umbc.edu/2015/12/phd-defense-infrastructure-less-group-data-sharing-using-smart-devices/
https://dev.my.umbc.edu/api/v0/pixel/news/57868/guest@my.umbc.edu/d3e316b253b8390de7af4c058b8c428d/api/pixel
computer-engineering
computer-science
defense
graduate
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Dec 2015 09:07:09 -0500
MS defense, Budhraja: Neuroevolution-Based Inverse Reinforcement Learning
M.S. Thesis Defense
Neuroevolution-Based Inverse Reinforcement Learning
Karan K. Budhraja
9:00am Wednesday, 2 December 2015, ITE 346
Motivated by such learning in nature, the problem of Learning from Demonstration is targeted at learning to perform tasks based on observed examples. One of the approaches to Learning from Demonstration is Inverse Reinforcement Learning, in which actions are observed to infer rewards. This work combines a feature based state evaluation approach to Inverse Reinforcement Learning with neuroevolution, a paradigm for modifying neural networks based on their performance on a given task. Neural networks are used to learn from a demonstrated expert policy and are evolved to generate a policy similar to the demonstration. The algorithm is discussed and evaluated against competitive feature-based Inverse Reinforcement Learning approaches. At the cost of execution time, neural networks allow for non-linear combinations of features in state evaluations. These valuations may correspond to state value or state reward. This results in better correspondence to observed examples as opposed to using linear combinations.
This work also extends existing work on Bayesian Non-Parametric Feature construction for Inverse Reinforcement Learning by using non-linear combinations of intermediate data to improve performance. The algorithm is observed to be specifically suitable for a linearly solvable non-deterministic Markov Decision Processes in which multiple rewards are sparsely scattered in state space. Performance of the algorithm is shown to be limited by parameters used, implying adjustable capability. A conclusive performance hierarchy between evaluated algorithms is constructed.
Committee: Drs. Tim Oates, Cynthia Matuszek and Tim Finin
]]>
M.S. Thesis Defense Neuroevolution-Based Inverse Reinforcement Learning Karan K. Budhraja 9:00am Wednesday, 2 December 2015, ITE 346 Motivated by such learning in nature, the problem of...
http://www.csee.umbc.edu/2015/12/ms-defense-budhraja-neuroevolution-based-inverse-reinforcement-learning/
https://dev.my.umbc.edu/api/v0/pixel/news/56383/guest@my.umbc.edu/a3baac40117364cc0e0836a7d8a741c6/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Tue, 01 Dec 2015 23:06:25 -0500
Tue, 01 Dec 2015 23:06:25 -0500
MS defense, Budhraja: Neuroevolution-Based Inverse Reinforcement Learning
M.S. Thesis Defense
Neuroevolution-Based Inverse Reinforcement Learning
Karan K. Budhraja
9:00am Wednesday, 2 December 2015, ITE 346
Motivated by such learning in nature, the problem of Learning from Demonstration is targeted at learning to perform tasks based on observed examples. One of the approaches to Learning from Demonstration is Inverse Reinforcement Learning, in which actions are observed to infer rewards. This work combines a feature based state evaluation approach to Inverse Reinforcement Learning with neuroevolution, a paradigm for modifying neural networks based on their performance on a given task. Neural networks are used to learn from a demonstrated expert policy and are evolved to generate a policy similar to the demonstration. The algorithm is discussed and evaluated against competitive feature-based Inverse Reinforcement Learning approaches. At the cost of execution time, neural networks allow for non-linear combinations of features in state evaluations. These valuations may correspond to state value or state reward. This results in better correspondence to observed examples as opposed to using linear combinations.
This work also extends existing work on Bayesian Non-Parametric Feature construction for Inverse Reinforcement Learning by using non-linear combinations of intermediate data to improve performance. The algorithm is observed to be specifically suitable for a linearly solvable non-deterministic Markov Decision Processes in which multiple rewards are sparsely scattered in state space. Performance of the algorithm is shown to be limited by parameters used, implying adjustable capability. A conclusive performance hierarchy between evaluated algorithms is constructed.
Committee: Drs. Tim Oates, Cynthia Matuszek and Tim Finin
]]>
M.S. Thesis Defense Neuroevolution-Based Inverse Reinforcement Learning Karan K. Budhraja 9:00am Wednesday, 2 December 2015, ITE 346 Motivated by such learning in nature, the problem of...
https://www.csee.umbc.edu/2015/12/ms-defense-budhraja-neuroevolution-based-inverse-reinforcement-learning/
https://dev.my.umbc.edu/api/v0/pixel/news/57869/guest@my.umbc.edu/269e31dee805d8a289f6c3baf616c114/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 01 Dec 2015 23:06:25 -0500
PhD defense: R. Holder, Plan Adaptation Through Offline Analysis of Potential Plan Disruptors

Ph.D. Dissertation Defense
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Rapid Plan Adaptation Through Offline
Analysis of Potential Plan Disruptors
Robert H. Holder, III
9:00am Wednesday, 9 December 2015, ITE 325b
Computing solutions to intractable planning problems is particularly problematic in dynamic, real-time domains. For example, visitation planning problems, such as a delivery truck that must deliver packages to various locations, can be mapped to a Traveling Salesman Problem (TSP). The TSP is an NP-complete problem, requiring planners to use heuristics to find solutions to any significantly large problem instance, and can require a lengthy amount of time. Planners that solve the dynamic variant, the Dynamic Traveling Salesman Problem (DTSP), calculate an efficient route to visit a set of potentially changing locations. When a new location becomes known, DTSP planners typically use heuristics to add the new locations to the previously computed route. Depending on the placement and quantity of these new locations, the efficiency of this adapted, approximated solution can vary significantly. Solving a DTSP in real time thus requires choosing between a TSP planner, which produces a relatively good but slowly generated solution, and a DTSP planner, which produces a less optimal solution relatively quickly.
Instead of quickly generating approximate solutions or slowly generating better solutions at runtime, this dissertation introduces an alternate approach of precomputing a library of high-quality solutions prior to runtime. One could imagine a library containing a high-quality solution for every potential problem instance consisting of potential new locations, but this approach obviously does not scale with increasing problem complexity. Because complex domains preclude creating a comprehensive library, I instead choose a subset of all possible plans to include. Strategic plan selection will ensure that the library contains appropriate plans for future scenarios.
Committee: Drs. Marie desJardins (co-chair), Tim Finin (co-chair), Tim Oates, Donald Miner, R. Scott Cost
]]>
Ph.D. Dissertation Defense Computer Science and Electrical Engineering University of Maryland, Baltimore County Rapid Plan Adaptation Through Offline Analysis of Potential Plan Disruptors...
http://www.csee.umbc.edu/2015/11/plan-adaptation-offline-analysis-potential-disruptors/
https://dev.my.umbc.edu/api/v0/pixel/news/56277/guest@my.umbc.edu/4fd4717b172771ae8e0d04aa620dc0d9/api/pixel
computer-science
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sat, 28 Nov 2015 18:52:10 -0500
Sat, 28 Nov 2015 18:52:10 -0500