Internships at Oracle Labs for IR/NLP/ML

The Information Retrieval and Machine Learning group at Oracle Labs is looking for highly motivated interns for both Spring and Summer 2015. The candidate should be proficient in Machine Learning and/or Statistical NLP.
Their current focus is in the areas of search, information extraction, including entity extraction and linking, relationship extraction, sentiment analysis as well as topic models. Other focus areas include parallel and distributed inference algorithms, deep learning and word embeddings, graphical models and transfer learning.
Research experience in any of these areas is strongly preferred. The candidate should also have good implementation skills in Java, Scala or other common language of choice.
They are located in Burlington, MA, and the candidate would need to relocate to this area. They are open to both Masters and PhD candidates, but PhD candidates are preferred. Send your CV to Sorry, you need javascript to view this email address. <mailto:Sorry, you need javascript to view this email address. > for applications or questions about the position. Oracle is an equal opportunity employer.
]]>
The Information Retrieval and Machine Learning group at Oracle Labs is looking for highly motivated interns for both Spring and Summer 2015. The candidate should be proficient in Machine...
http://www.csee.umbc.edu/2014/12/internships-at-oracle-labs-for-irnlpml/
https://dev.my.umbc.edu/api/v0/pixel/news/48676/guest@my.umbc.edu/0cf8b3b5abfb7eca1020aa97af4ca57a/api/pixel
jobs
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 15 Dec 2014 01:16:57 -0500
Mon, 15 Dec 2014 01:16:57 -0500
PhD defense: Huguens Jean, Paper Form Classification for Information Systems Strengthening in Developing Countries

Ph.D. thesis defense
Paper Form Classification for Information
Systems Strengthening in Developing Countries
Huguens Jean
1:00pm Friday, 19 December 2015, ITE 325b
In developing countries, people are now more likely to have access to a mobile phone than clean water, making cellular based technology the only viable medium for collecting, aggregating, and communicating local data so that it can be turned into useful information. While mobile phones have found broad application in reporting health, financial and environmental data, many data collection methods still suffer from delays, inefficiency and difficulties maintaining quality. In environments with insufficient IT support and infrastructure, and among populations with limited education and experience with technology, paper forms rather than electronic methods remain the predominant means for data collection.
To meet the digitization needs of paper driven data collection practices in developing countries, SHREDDR proposes an end-to-end architecture that transforms paper form images into structured digital information on-demand. To facilitate the automatic extraction of input regions in form images, this thesis extends the SHREDDR architecture with the necessary capabilities to efficiently classify form images according to their template document. Specifically, it introduces a novel framework for visually identifying form templates by decomposing the template identification problem into three distinct tasks: retrieval, learning and matching (RLM).
Given a query form instance, the retrieval component finds and ranks the topmost h similar templates. If h>1, the matching component uses full image registration to conduct a more rigorous assessment of the visual similarity between the query form instance and the candidate templates. After matching, the retrieval’s preliminary ranking is adjusted, if necessary. The topmost candidate template with the highest registration score satisfying a global alignment threshold denotes the input form’s template. Based on the answer obtained from matching, the learning component updates the retrieval so that it can provide a better ranking in future searches. If h=1, the RLM bypasses matching and uses the retrieved template as the final classification.
Based on the proposed framework, the present thesis investigates form classification under the conditions of known and unknown template classes. A pilot study integrating the RLM into the SHREDDR system demonstrates its classification accuracy and its impact on digitization efficiency.
Committee: Drs. Timothy Oates (Chair), Fow-Sen Choa, Janet Rutledge, Jesus Caban, Nilanjan Banerjee
]]>
Ph.D. thesis defense Paper Form Classification for Information Systems Strengthening in Developing Countries Huguens Jean 1:00pm Friday, 19 December 2015, ITE 325b In developing...
http://www.csee.umbc.edu/2014/12/phd-defense-huguens-jean-paper-form-digitization-for-information-systems-strengthening-and-socio-economic-development-in-developing-countries/
https://dev.my.umbc.edu/api/v0/pixel/news/48672/guest@my.umbc.edu/736c88aad90ee793439d9df49947d778/api/pixel
defense
graduate
news
research
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 13 Dec 2014 09:01:29 -0500
Sat, 13 Dec 2014 09:01:29 -0500
Anupam Joshi named an IEEE Fellow

CSEE Professor Anupam Joshi has been named an IEEE Fellow, recognized for his for contributions to security, privacy and data management in mobile and pervasive systems. This designation is conferred by the IEEE Board of Directors on individuals with an outstanding record of accomplishments in any of the IEEE fields of interest and is recognized by the technical community as a prestigious honor and an important career achievement. No more than 0.1% of the total IEEE voting membership can be selected in a year.

Dr. Joshi joined UMBC’s faculty in 1998 and currently is the Oros Family Professor of Technology and Director of the UMBC Center for Cybersecurity. He previously held faculty appointments at the University of Missouri, Columbia and Purdue University. He received a Ph.D. in Computer Science from Purdue University and a B. Tech in Electrical Engineering from the Indian Institute of Technology, Delhi. While at UMBC he has taught both undergraduate and graduate courses in operating systems, mobile computing and security. He developed and teaches an Honors College seminar on “Privacy and Security in a Mobile Social World”. He has mentored nine Ph.D. graduates and a large number of M.S. students.
Joshi has made many contributions to the design, analysis and development of intelligent systems for mobile, social and secure computing. Twenty years ago he was one of a handful of researchers who recognized that mobility introduced new challenges for data management, security and privacy over and above those brought about by wireless connectivity. His key insight was to model mobile and pervasive systems as distributed systems that are both open, in that they do not pre-identify a set of known participants, and dynamic, in that the participants change regularly.
He observe that applications on mobile devices require greater degrees of decision making and autonomy as they become increasingly sophisticated and intelligent and can’t always assume connectivity to central servers. Entities in these pervasive computing systems must exchange information about the data and services offered and sought and their associated security and privacy policies, negotiate for information and resource sharing, be aware of their context, and monitor for and report on suspicious or anomalous behavior. Dr. Joshi has addressed these challenges across the stack, from network protocols to data management to policy controlled interactions between autonomous entities.
Much of his research has been done in collaboration with colleagues in industry such as IBM, Microsoft, Northrop Grumman and Qualcomm. It has been funded by not just them, but also NSF, DARPA, AFOSR, ARL, NIST and other federal agencies. Joshi has published prolifically with more than 200 publications in refereed journals and conferences, many of which are highly cited. He has served as the General or Program Chair of many key conferences including the IEEE International Conference on Intelligence and Security Informatics which will be held in Baltimore in May 2015.
The IEEE is the world’s leading professional association for advancing technology for humanity. Through its 400,000 members in 160 countries, it is a leading authority on a wide variety of areas ranging from aerospace systems, computers and telecommunications to biomedical engineering, electric power and consumer electronics. Dedicated to the advancement of technology, the IEEE publishes 30 percent of the world’s literature in the electrical and electronics engineering and computer science fields, and has developed more than 900 active industry standards.
]]>
CSEE Professor Anupam Joshi has been named an IEEE Fellow, recognized for his for contributions to security, privacy and data management in mobile and pervasive systems. This designation is...
http://www.csee.umbc.edu/2014/12/anupam-joshi-named-an-ieee-fellow/
https://dev.my.umbc.edu/api/v0/pixel/news/48702/guest@my.umbc.edu/25401eae81588bdf57f90e140539e1c9/api/pixel
cybersecurity
faculty-and-staff
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 13 Dec 2014 00:40:25 -0500
MS defense: Epileptic Seizure Detection using Symbolic Aggregate Approximation and Bag of Patterns

MS Thesis Defense
SAX-BOP: Epileptic Seizure Detection using
Symbolic Aggregate Approximation and Bag of Patterns
Sidharth Allani
1:00pm Friday, 12 December 2014, ITE 325b
Epilepsy is a chronic neurological disorder that makes patients susceptible to experiencing recurrent seizures. A seizure occurs when abnormal activity in the brain leads to involuntary body moment, lack of awareness or behavior, short-term loss of memory or attention, short-term unconsciousness, or body convulsions. Epilepsy affects three million people in the United States and accounts for $15.5 billion in direct and indirect costs.
Epilepsy has many different causes, and often no definite cause can be found. Patients who suffer from intractable seizures experience unpredictable and frequent seizures that cannot be controlled using anti-seizure drugs. Such seizures leave the patient traumatized and, due to their uncertainty, the patient’s mobility and independence are restricted, resulting in social isolation and economic hardship.
The research in this thesis aims to detect epileptic seizures and to analyze the performance of Symbolic Aggregate approXimation and the Bag of Patterns representation for seizure event detection. We use Electroencephalogram (EEG) recordings as the data source for seizure detection, which is the recording of electrical activity along the scalp that measures ionic current flows within the neurons of the brain. These signals are a good source of information about abnormal activity in the brain and are helpful in the process of epileptic seizure detection. This problem becomes challenging because of the enormous size of the EEG data, making it difficult to effectively and efficiently analyze these signals and detect a seizure. We use Symbolic Aggregate approXimation (SAX) and the Bag of Patterns Representation (BOP) and analyze their performance with EEG time series data to detect seizures.
Committee: Drs. Tim Oates (chair), Tim Finin and Tinoosh Mohsenin
]]>
MS Thesis Defense SAX-BOP: Epileptic Seizure Detection using Symbolic Aggregate Approximation and Bag of Patterns Sidharth Allani 1:00pm Friday, 12 December 2014, ITE 325b Epilepsy is a...
http://www.csee.umbc.edu/2014/12/ms-defense-epileptic-seizure-detection-using-symbolic-aggregate-approximation-and-bag-of-patterns/
https://dev.my.umbc.edu/api/v0/pixel/news/48647/guest@my.umbc.edu/e3575a4d9ee7bc9a24f6ba4c61b59675/api/pixel
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Fri, 12 Dec 2014 08:38:01 -0500
Dr. Rick Forno discusses infrastructure security with SIGNAL magazine

In the December 2014 issue of AFCEA’s SIGNAL Magazine, CSEE’s Dr. Rick Forno comments on the likelihood of a destructive cyberattack on critical American infrastructure. He was one of several experts discussing US Cyber Command’s worry about such potential incidents and how it might respond.
He believes a major cyber attack against critical infrastructure is more likely from a rogue terrorist or criminal group than a nation-state. However, he says that although the possibility for a nation-state to launch attacks remains a valid concern, the probability of such an event remains fairly low. Moreover, Forno points out that a destructive attack could hinder an adversary’s own operations. “You can’t collect intelligence on an enemy or communicate if the Internet is down,” he says. “That may play into a nation-state’s calculus about what type of attack they might employ in a given situation.”
]]>
In the December 2014 issue of AFCEA’s SIGNAL Magazine, CSEE’s Dr. Rick Forno comments on the likelihood of a destructive cyberattack on critical American infrastructure. He was one of several...
http://www.csee.umbc.edu/2014/12/dr-rick-forno-discusses-infrastructure-security-with-signal-magazine/
https://dev.my.umbc.edu/api/v0/pixel/news/48634/guest@my.umbc.edu/eca877a0283982ce99a8d37ffca4f083/api/pixel
computer-science
csee
cybersecurity
in-the-news
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 11 Dec 2014 15:22:01 -0500
Thu, 11 Dec 2014 15:22:01 -0500
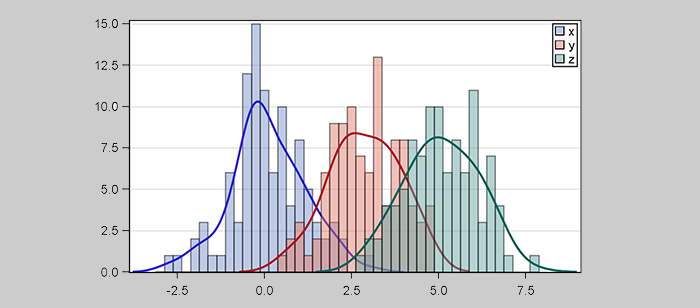
PhD Proposal: Learning Representation and Modeling Time Series
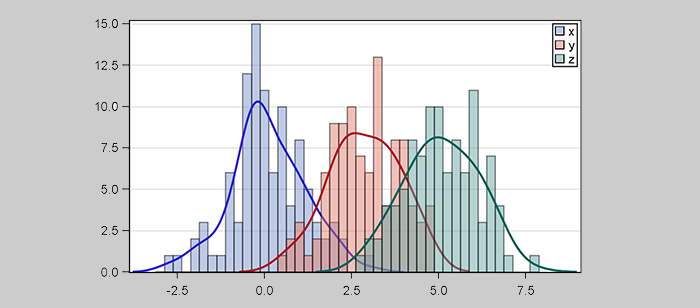
Ph.D. Dissertation Proposal
Learning Representation and Modeling Time Series
Zhiguang Wang
10:00-12:00 Friday, 12 December 2015, ITE 325B
Most real-world data has a temporal component, whether it is measurements of natural (weather, sound) or man-made (stock market, robotics) phenomena. Analysis of time-series data has been the subject of active research for decades and is still considered to be a challenge in machine learning and data mining due to the properties of temporal data.
Traditional approaches for modeling and representing time-series data fall into three categories. Non-data adaptive models, such as Discrete Fourier Transformation (DFT), Discrete Wavelet Transformation (DWT), and Discrete Cosine Transformation (DCT), compute the transformation with an algorithm that is invariant with respect to the data. Data adaptive approaches such as Symbolic Aggregation approXimation (SAX), Piecewise Linear Aggregation (PLA), and shapelets compute transforms that are highly dependent on the data. In model-based approaches such as AutoRegressive Moving Average models (ARMA), Linear Dynamical Systems (LDS), and Hidden Markov Models (HMMs), the underlying data is assumed to fit a specific type of model. The estimated parameters can then be used as features in, for example, a classifier.
However, more complex, high-dimensional, and noisy real-world time-series data are often difficult to model because the dynamics are either too complex or unknown. Traditional shallow methods, which contain a small number of non-linear operations, might not have the capacity to accurately model such complex systems.
We develop and verify three different approaches to represent and model time-series. Time-Warping SAX and Pooling SAX are two extensions of the vanilla SAX approach that is used as a symbolic representation of time series. Time-Warping SAX extracts linear temporal dependencies by building a time-delay embedding vector to construct more informative SAX words. Pooling SAX applies a non-parametric weighting scheme to extract significant variables. These are data adaptive models that achieve state-of-the-art accuacy on time-series classification problems.
We also propose the Gramian Angular Field (GAF) and Markov Transition Field (MTF) as two novel approaches to encode a time-series as an image. These representations not only demonstrate potential for visual inspection by humans, but when they are combined with deep learning approaches (Convolutional Network and Denoised Auto-encoders) they achieve excellent performance compared to other modern algorithms on classification and regression/imputation problems. GAF and MTF are non-data adaptive approaches that allow us to learn models and extract the abstract representations supported by model-based approaches.
Finally, we propose to model time-series by learning the representation directly from the raw data with model-based approaches. We will develop recurrent auto-encoders, in which the global optimum is ensured by a new Adaptive Risk-Averting/Seeking Criterion, to model the real/complex time series (dynamical systems) by learning the implicit data generating distribution over time. This model will be applied to tasks such as classification, regression/imputation, and anomaly detection.
Committee: Drs. Timothy Oates (Chair), James Lo (Math), Yun Peng and Matt Schmill
]]>
Ph.D. Dissertation Proposal Learning Representation and Modeling Time Series Zhiguang Wang 10:00-12:00 Friday, 12 December 2015, ITE 325B Most real-world data has a temporal component,...
http://www.csee.umbc.edu/2014/12/phd-proposal-learning-representation-and-modeling-time-series/
https://dev.my.umbc.edu/api/v0/pixel/news/48614/guest@my.umbc.edu/13427f5e0ab2c6dddc442e4d139346ff/api/pixel
computer-science
graduate
news
research
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 10 Dec 2014 23:00:19 -0500
Daily Record profiles UMBC’s cybersecurity education & training

UMBC’s Cybersecurity Graduate Program Director Dr. Rick Forno and Homer Minnick, Director of UMBC Training Centers’ Cyber Academy, were featured in a recent Daily Record article examining how local universities support the cybersecurity education and training needs of corporate, military, and intelligence employers.
More information:
UMBC’s Graduate Cybersecurity Program
UMBC Training Centers Cyber Academy
]]>
UMBC’s Cybersecurity Graduate Program Director Dr. Rick Forno and Homer Minnick, Director of UMBC Training Centers’ Cyber Academy, were featured in a recent Daily Record article examining...
http://www.csee.umbc.edu/2014/12/daily-record-profiles-umbcs-cybersecurity-education-training/
https://dev.my.umbc.edu/api/v0/pixel/news/48565/guest@my.umbc.edu/5d44518168a9c4fb93755da6361fe8cd/api/pixel
computer-science
csee
cybersecurity
in-the-news
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 09 Dec 2014 11:02:28 -0500
Tue, 09 Dec 2014 11:02:28 -0500
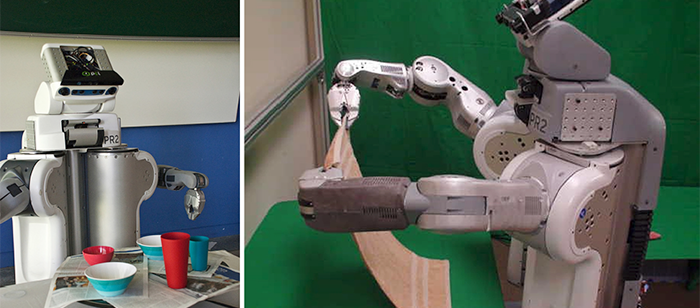
PhD Proposal: Increased Autonomy with Robotics for Daily Living
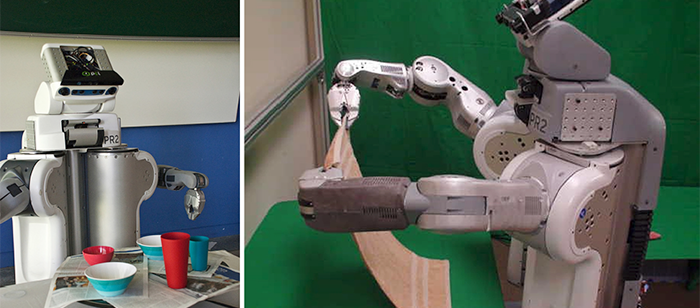
Ph.D. Proposal
Increased Autonomy with Robotics for Daily Living
Kavita Preethi Krishnaswamy
5:30pm-7:30pm, Tuesday, 9 December 2014, ITE 325B
Robotic technologies can provide people with disabilities invaluable tools to perform activities of daily living (ADLs). Few studies have investigated how effective and accessible the control of robotic aids is for people with severe physical disabilities with respect to their needs and current facility with technology. Though present-day robotic aids can help people with disabilities with important daily living tasks, there is still room for improvement.
What has been needed, and heretofore unavailable, is a self-directed transferring, repositioning, and personal care robotic device that is capable of increasing independence for people with physical disabilities without the assistance of caregivers. This thesis proposal will serve as the base of the research study to design and develop self-directed transferring, repositioning, and personal care robotic systems with a focus on accessible user interfaces for control that are feasible for persons with severe physical disabilities. The interface should allow local and remote control, and thus must be aware of network constraints to ensure safe and accurate control.
Committee Members: Dr. Tim Oates (Chair), Dr. Dan Ding, Dr. Tim Finin, Dr. Charles Nicholas, Dr. Yelena Yesha
]]>
Ph.D. Proposal Increased Autonomy with Robotics for Daily Living Kavita Preethi Krishnaswamy 5:30pm-7:30pm, Tuesday, 9 December 2014, ITE 325B Live Webcast: http://goo.gl/5JmjlR or...
http://www.csee.umbc.edu/2014/12/phd-proposal-increased-autonomy-with-robotics-for-daily-living/
https://dev.my.umbc.edu/api/v0/pixel/news/48520/guest@my.umbc.edu/0f45e763f88b9e3bf5a46bcda557985a/api/pixel
graduate
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
25
2
true
Sun, 07 Dec 2014 13:36:18 -0500
New computing faculty positions at UMBC

UMBC has a total of nine open full-time positions for computing faculty including five tenure track professors, a professor of the practice and three lecturers.
UMBC’s Computer Science and Electrical Engineering department is seeking to fill five positions for the coming year. They include two tenure track positions in Computer Science, up to three full-time lecturers. See the CSEE jobs page for more information.
The College of Engineering and Information Technology has a position for a full-time lecturer or Professor of Practice to focus on the needs of incoming computing majors through teaching, advising, and helping develop programs in computing. This person will work closely with faculty in the Computer Science and Electrical Engineering Department and Information Systems Department.
UMBC’s Information Systems department is accepting applications for three tenure track faculty positions in data science, software engineering and human-centered computing.
]]>
UMBC has a total of nine open full-time positions for computing faculty including five tenure track professors, a professor of the practice and three lecturers. UMBC’s Computer Science and...
http://www.csee.umbc.edu/2014/12/open-computing-faculty-positions-at-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/48515/guest@my.umbc.edu/27121dbdf8f8192649d3793decef5da4/api/pixel
jobs
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 06 Dec 2014 10:47:51 -0500
Sat, 20 Dec 2014 12:14:51 -0500
New computing faculty positions at UMBC

UMBC has a total of nine open full-time positions for computing faculty including five tenure track professors, a professor of the practice and three lecturers.
UMBC’s Computer Science and Electrical Engineering department is seeking to fill five positions for the coming year. They include two tenure track positions in Computer Science, up to three full-time lecturers. See the CSEE jobs page for more information.
The College of Engineering and Information Technology has a position for a full-time lecturer or Professor of Practice to focus on the needs of incoming computing majors through teaching, advising, and helping develop programs in computing. This person will work closely with faculty in the Computer Science and Electrical Engineering Department and Information Systems Department.
UMBC’s Information Systems department is accepting applications for three tenure track faculty positions in data science, software engineering and human-centered computing.
]]>
UMBC has a total of nine open full-time positions for computing faculty including five tenure track professors, a professor of the practice and three lecturers. UMBC’s Computer Science and...
http://www.csee.umbc.edu/2014/12/open-computing-faculty-positions-at-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/48516/guest@my.umbc.edu/5bb1205059418536a79ff240033b3cd5/api/pixel
jobs
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 06 Dec 2014 10:47:51 -0500
Sat, 20 Dec 2014 12:14:51 -0500