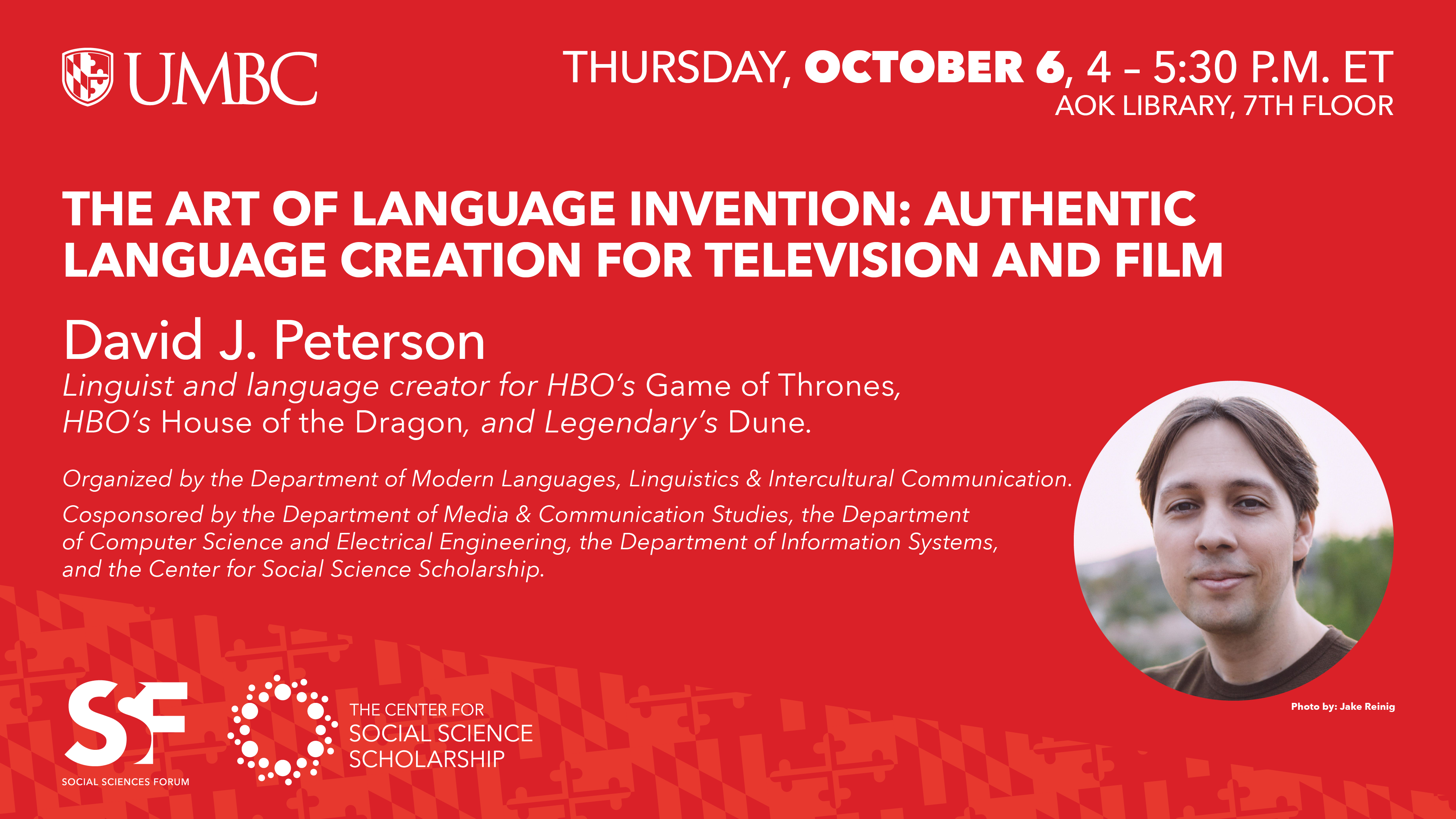
Talk: The Art of Language Invention; 4-5:30pm Thur. 10/6
Authentic Language Creation for Television and Film
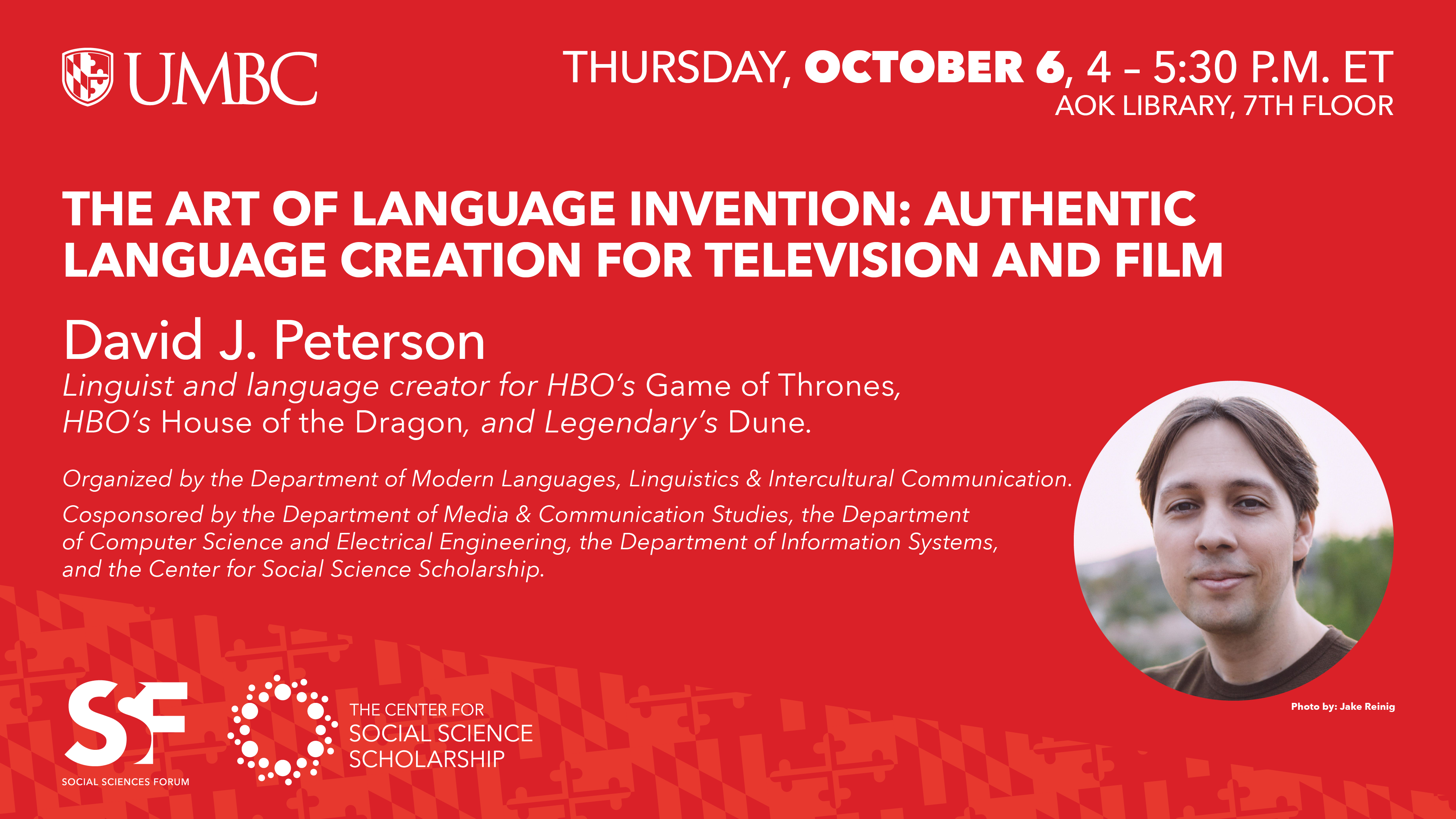
The Art of Language Invention: Authentic Language Creation for Television and Film
David J. Peterson
MLLI SSF Lecture
4-5:30 pm, Thursday, 6 October 2022
AOK Library 7th floor, UMBC
The
UMBC Social Sciences Forum presents
David J. Peterson, linguist and language creator for HBO's Game of Thrones, HBO's House of the Dragon, and Legendary's Dune, who will speak on The Art of Language Invention: Authentic Language Creation for Television and Film.
Peterson will detail his process for authentic language creation. Drawing from linguistics and language study, and utilizing both traditional and digital tools, Peterson will go through the creation of a language's sound system, grammar, lexicon, and writing system, and will discuss how his work interfaces with film, television and video game production.
In the fall of 2015, Peterson published his nonfiction work The Art of Language Invention with Penguin Books. He has a background in academic linguistics, having earned a bachelor's degree in English and Linguistics from UC Berkeley in 2003, and a master's degree in Linguistics from UC San Diego in 2005 (recipient of the 2016 Emerging Leader Award). He's also been creating languages since 2000. He served as a cofounder and original board member of the Language Creation Society, and served as its president from 2011 to 2014.
]]>
The Art of Language Invention: Authentic Language Creation for Television and Film David J. Peterson MLLI SSF Lecture 4-5:30 pm, Thursday, 6 October 2022 AOK Library 7th floor, UMBC...
https://dev.my.umbc.edu/api/v0/pixel/news/127870/guest@my.umbc.edu/0831160e2bfac9ab25de6fb6c3c006d5/api/pixel
linguistics
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Modern Languages, Linguistics & Intercultural Communication
0
0
true
Thu, 22 Sep 2022 22:43:16 -0400
Thu, 22 Sep 2022 22:45:25 -0400
Interweave Cognitive Radio for 4G Long Term Evolution and 5G
PhD Defense: Brian Stevens, Computer Engineering
Ph.D. Dissertation Defense
Interweave Cognitive Radio for 4G Long Term Evolution and 5G New Radio Self-Reliant Networks
Brian Stevens, Computer Engineering
1-3 pm ET Tuesday, 20 September 2022, Zoom
Committee: Drs. Mohamed Younis (Chair), Tulay Adali, Sunita Bhatia
(JHUAPL), Seung-Jun Kim, Dmitri Perkins, Ting Zhu
Existing cellular networks have untapped radio frequency resources, also known as white space, available for cognitive radio applications. A secondary network can opportunistically interweave communication within the white space of an existing cellular signal by leveraging cognitive radio. This thesis presents a novel methodology for forming a cognitive interwoven self-reliant secondary network with no additional physical infrastructure, collaboration from the existing primary network, and software or hardware changes in the primary network. The methodology is tested first with 4G and later with 5G cellular technological standards. For the physical layer, this thesis optimizes synchronization as the initial step in aligning to a cellular signal in time, frequency, and sector identity. We improve synchronization through sensitivity, execution time, and applies a threshold to form a "cell detector" instead of the traditional "cell search," which only considers the most detectable signal.
After synchronization, resource detectors monitor the available spectral resources of the entire cellular infrastructure. Modern cellular networks have grown in complexity and become an ecosystem that includes the host technologies, such as 4G Long Term Evolution (LTE) and 5G New Radio (NR), along with subsystems such as narrowband internet of things (NB-IoT), category M1 (Cat-M1/LTE-M), observed time difference of arrival (OTDOA), and support for 4G/5G coexistence using dynamic spectrum sharing (DSS). Such an increased complexity has driven the need for network monitoring to enable load tracking, congestion control, spectral efficiency analysis, intrusion detection, and cognitive radio communications.
This thesis develops resource monitoring that can passively monitor the entire cellular ecosystem, including reservations configured with high-layer messages that are only accessible to in-network, active, and sometimes user-specific equipment. Resource monitoring provides white-space reservations for cognitive communications. We define interference control to prevent interference with the primary network through physical layer access schemes and power control cluster protocols to access resources safely. With the added complexity of 5G as a host technology, our research leverages geospatial beamforming of known signals as spatially dependent white space. In this case, the known synchronization signal burst must be detected with a "beam detector" instead of a "beam search" to properly use beam resources that are not close to cognitive radio nodes. The thesis applies the self-reliant methodology, which defines opportunistic access and power control protocols that limit interference between cellular networks in both the time and frequency domains with additional support in the geospatial domain for 5G NR. Our research determines that an adapted version of Slotted ALOHA for medium access control (MAC) with a no-back-off contention fits the self-reliant approach of our work and timing constraints found in 4G LTE and 5G NR networks.
]]>
Ph.D. Dissertation Defense Interweave Cognitive Radio for 4G Long Term Evolution and 5G New Radio Self-Reliant Networks Brian Stevens, Computer Engineering 1-3 pm ET Tuesday, 20...
https://dev.my.umbc.edu/api/v0/pixel/news/127760/guest@my.umbc.edu/e64a5f0ad7f42f9b06c9171ad1fbc11c/api/pixel
cognitive
defense
phd
radio
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 19 Sep 2022 16:52:50 -0400
Talk: Critical Infrastructure Risk Assessment and Reduction
Online, 12:00-1pm ET, Friday, 23 September 2022
The UMBC Cyber Defense Lab presents
On A Risk Assessment and
Reduction Approach for
National Critical Infrastructure
Cyrus Jian Bonyadi
Security Systems Analyst and PhD Student
Sandia National Labs and UMBC
12:00-1pm ET, Friday, 23 Sept. 2022, via WebEx
Work by Jason Reinhardt, Merideth Secor, Lindsey Miles, Ron Lafond, Derek Koolman II, Lauren Wind, Ray Ludwig, Jeff Munns
The
Cybersecurity and Infrastructure Security Agency (CISA) leads the national effort to understand, manage, and reduce risk to our cyber and physical infrastructure. CISA must assess risks that cover a broad range of scenarios over a complex set of interdependent critical infrastructure (CI) systems. While many threat and hazard impact models and data sets exist, there is no overarching analytic structure that organizes and integrates these disparate sources into a unified risk assessment. CISA is building capabilities that will address these challenges to support stakeholders across all levels of government and the private sector.
First, CISA has developed a
National Critical Functions (NCFs) data structure to organize and describe critical infrastructure. This data set provides a set of decompositions structured as directed graphs that break down each identified function into enabling sub-functions that detail the operation and interdependencies across disparate CI systems.
The functional description of NCFs serves as a complementary lens to the sector-based organization of CI and better facilitates systemic and cross-sector risk analysis.
Additionally, CISA has begun developing the Risk Architecture, a technology-enabled analytic tool that contains a set of standards, scenarios, visualizations, and workflows that leverage the NCF and other integrated CI data sets. This talk describes the need for an integrated approach to CI risk assessment, the NCF decomposition structure, the principles and concepts behind the Risk Architecture, and the approaches to functional interdependency analysis while also providing initial use examples.
Cyrus Jian Bonyadi is a PhD student working on developing a set of corollaries for consensus theory in distributed system security. Cyrus is a former member of the UMBC
Cyberdawgs cyberdefense team and maintains a relationship with UMBC as a full time researcher at Sandia National Labs.
Host: Alan T. Sherman,
sherman@umbc.edu.
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL meetings: Oct 7, Geoffrey Herman (Illinois), Validation of the Cybersecurity Curriculum Assessment (CCA); Oct 21, Peter Peterson (UMN Duluth), Misconceptions in cybersecurity; Nov 4, Josiah Dykstra (DoD), Myths in cybersecurity; Nov 18, Russ Fink (APL), ARMR: Autonomous resilience / machine recovery; Dec 2 Peter Peterson (UMN Duluth), Adversarial Thinking; SFS/CySP Research Study: January 2-6, 2023 (tentative).
]]>
The UMBC Cyber Defense Lab presents On A Risk Assessment and Reduction Approach for National Critical Infrastructure Cyrus Jian Bonyadi Security Systems Analyst and PhD Student Sandia...
https://cisa.umbc.edu/
https://dev.my.umbc.edu/api/v0/pixel/news/127703/guest@my.umbc.edu/2b1521e170974ba41a6ccf6e64f0f355/api/pixel
cisa
cybersecurity
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
UMBC Cyber Defense Lab
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/xxlarge.jpg?1663610286
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/xlarge.jpg?1663610286
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/large.jpg?1663610286
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/medium.jpg?1663610286
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/small.jpg?1663610286
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/xsmall.jpg?1663610286
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/703/bd8be10767478fbe30cf9ba484b8eefe/xxsmall.jpg?1663610286
0
0
true
Mon, 19 Sep 2022 09:13:48 -0400
Mon, 19 Sep 2022 14:01:23 -0400
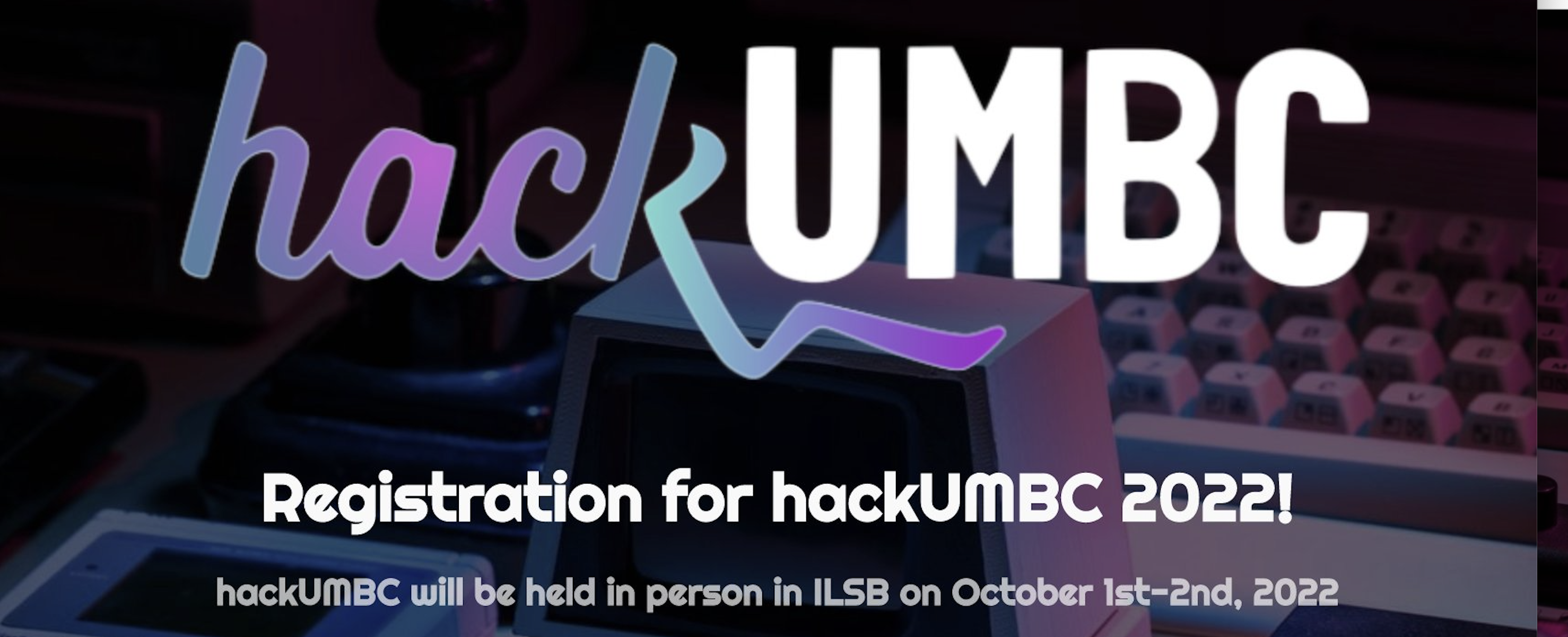
Registration open for the 2022 hackUMBC hackathon
Saturday and Sunday, 1-2 October 2022 in the ILSB building
Join hackUMBC for our 24-hour hackathon event where we challenge our ideas to come to life! Collaborate with other students and pick up some new skills in our workshop sessions!
With lots of fun activities, over $5,000 in prizes, and swag for all participants, you will be in for an exciting weekend.
There will be four tracks focused on different areas: data analysis and visualization, hardware systems, AI/machine learning, and general ideas that don't fit the other three.
For more information, see the
hackUMBC site.
]]>
Registration is now open for the 2022 hackUMBC hackathon, which takes place on campus on Saturday and Sunday, 1-2 October 2022 in the ILSB building. Join hackUMBC for our 24-hour hackathon...
https://www.hackumbc.org/
https://dev.my.umbc.edu/api/v0/pixel/news/127693/guest@my.umbc.edu/048eb2b965c45b4d05aea250b8ae1223/api/pixel
hackathon
hackumbc
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 17 Sep 2022 21:02:11 -0400
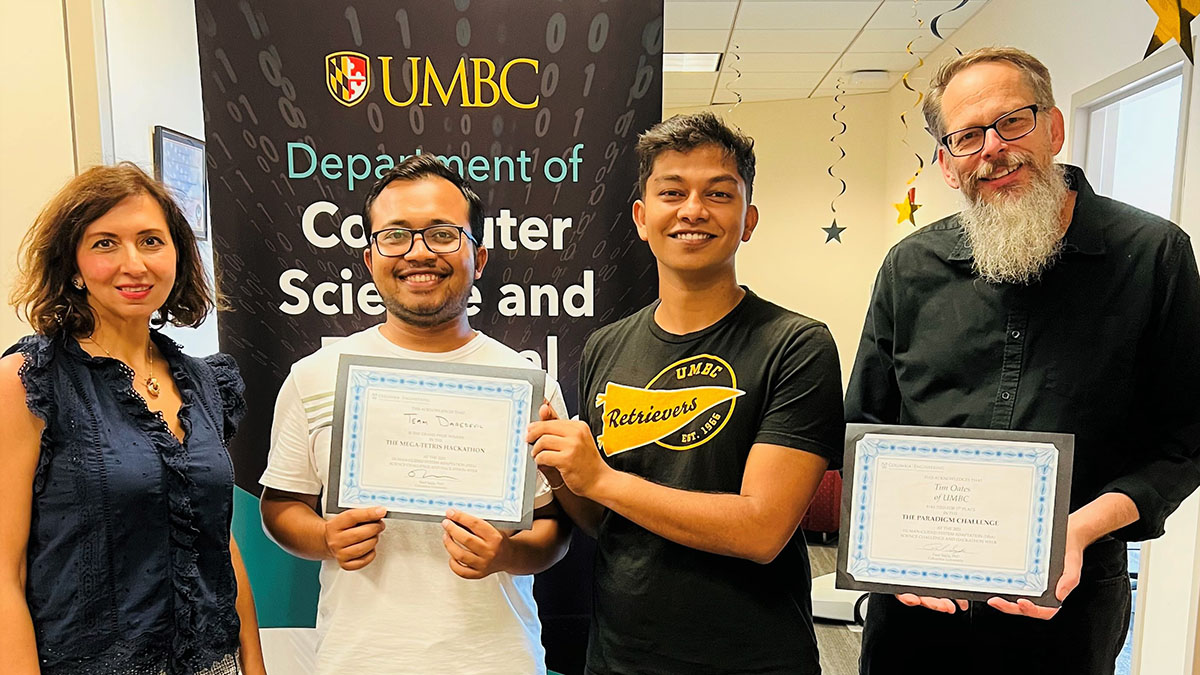
CSEE faculty & students win human-machine teaming events
Hackathon sponsored by the Army Research Lab and Columbia U.
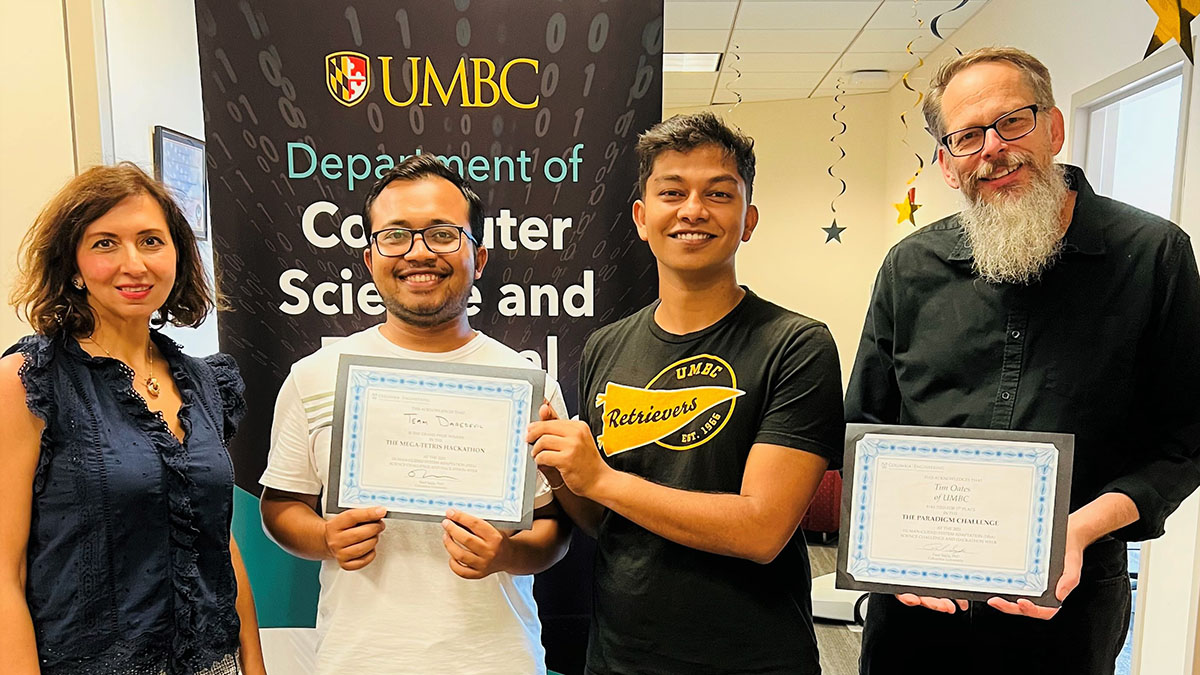
Professor Tinoosh Mohsenin, Khondoker Hossain, Prakhar Dixit, and Professor Tim Oates
CSEE faculty and grad students show expertise in human-guided system adaptation at Columbia University event
A team led by CSEE Professors Tinoosh Mohsenin and Tim Oates recently competed in three events at the Human-Guided System Adaptation (HSA) Science Challenge and Hackathon Week. The event, sponsored by the Columbia University Program for Human-Guided Machine Adaptation and the Army Research Lab, was held at Columbia the week of August 8-12 with the goal of extending the state-of-the-art in human-machine teaming. UMBC either won or was on the team that won all three events.
The first competition required the participants to prepare a five-minute video proposing a testbed for human-machine teaming that included specific drivers in the 2040+ Vision of the US Army: advanced intelligence, superhuman capabilities, and rapid technological change. Dr. Oates proposed using Nomic--a game in which a move corresponds to proposing and voting on changes to the rules--as the testbed. His video tied for first place with Duke University.
The second competition required the team to propose a sequence of five or more experiments in a single testbed to answer critical scientific questions in one of the following areas: Human-Guided Machine Learning, Tech Savvy, Hybrid Thinking, Rapid Adaptable Small Teams, and Distributed Teams. Dr. Mohsenin's team, led by ARL collaborator Dr. Nick Waytowich, won first place.
Finally, Ph.D. student Khondoker Murad Hossain and master's student Prakhar Dixit competed in a classic hackathon where the goal was to build a human-agent team to play Hybrid Team Mega-Tetris--a tetris variant in with multiple ongoing game screens and novel rules that can arise at any time, making it impossible for humans to play well without machine help. Khondoker and Prakhar won the tournament with a final score that was more than twice that of the second place team.
]]>
Professor Tinoosh Mohsenin, Khondoker Hossain, Prakhar Dixit, and Professor Tim Oates CSEE faculty and grad students show expertise in human-guided system adaptation at Columbia University...
https://liinc.bme.columbia.edu/human-guided-system-adaptation-hsa-science-challenge-and-hackathon-week/
https://dev.my.umbc.edu/api/v0/pixel/news/127509/guest@my.umbc.edu/74c87d0636b9bd0a17309b6ded4b8671/api/pixel
ai
hackathon
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 14 Sep 2022 14:24:59 -0400
PhD Defense: Md Shafiqul Islam, Computer Eng., 9-11am 9/14
Communication Across the Air-Water Interface

PhD Defense, Computer Engineering
Analysis and Protocols to Establish Downlink for
Communication Across the Air-Water Interface
Md Shafiqul Islam
9-11 am Wed. 14 Sept. 2022 via WebEx
In underwater wireless networks (UWNs), conventionally there is no direct communication between an underwater node and a remote command center, because there is no known physical signal that propagates well in both the water and air mediums. Radio signals are the popular choice in the air while acoustics are the prime means for communication underwater. Hence, the typical architecture of an UWN includes surface nodes or gateways which have dual modems, an acoustic modem to communicate with underwater nodes and a radio modem to interact with terrestrial command centers. However, such an architecture is logistically complicated and could expose the network to security threat. Therefore, it is desirable to establish a direct communication from air to underwater without having any intermediate surface node.
This dissertation opts to fulfill such a need by pursuing two viable solutions, namely, using visual light communications (VLC) and exploiting the optoacoustic (photoacoustic) effect. Through extensive analysis and experiments we show that VLC is an effective means for scenarios where the distance between the airborne and underwater nodes is relatively short. We first analyze the coverage area and intensity inside the water for a light transmitter placed in the air. We then provide guidelines for using single and multiple light sources to establish robust VLC links under rough environmental conditions like high water current and turbidity. Furthermore, we investigate effective modulation techniques that suit VLC. For long distance communication, VLC is not a viable option since light gets absorbed at an exponentially growing rate with the increase of water depth. Photoacoustic (PA) energy transfer mechanism is the promising method for long distance communication.
Although the use of the photoacoustic mechanism is quite common in medical imaging, little progress has been made on building the communication protocol stack for air-to-underwater communication. In our research work, at first, we have studied the channel characteristics of the PA based air-to-underwater communication. We show that by carefully choosing the relative position of the airborne unit and underwater node, we can generate a narrowband acoustic signal which is very crucial for long distance communication. Moreover, we develop suitable modulation and demodulation schemes for PA communication.
Committee: Drs. Mohamed Younis, Fow-Sen Choa, Gary Carter, Lloyd Emokpae, Akram Fadhl N. Ahmed
]]>
PhD Defense, Computer Engineering Analysis and Protocols to Establish Downlink for Communication Across the Air-Water Interface Md Shafiqul Islam 9-11 am Wed. 14 Sept. 2022 via WebEx ...
https://dev.my.umbc.edu/api/v0/pixel/news/127467/guest@my.umbc.edu/7195032010c7ec3a0266f38c0b84b179/api/pixel
computer-engineering
defense
phd
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 11 Sep 2022 22:08:42 -0400
Sun, 11 Sep 2022 22:10:58 -0400
Free 10-week Discover AI program, apply by Tuesday, Sept. 20
Application deadline extended to 9/20
UMBC and nonprofit AI4ALL will offer UMBC first-year, sophomore, and junior undergraduates the opportunity to apply to the freeCollege Pathways Discover AIprogram. It's designed to be accessible to students with and without programming experience.
The ten-week project-oriented program starts on September 30 and will have weekly online synchronous sessions on Fridays from 3:30 to 5:00 pm. Additional asynchronous material will also be available. It is not graded and students who finish it will get a certificate of completion.
]]>
UMBC and nonprofit AI4ALL will offer UMBC first-year, sophomore, and junior undergraduates the opportunity to apply to the freeCollege Pathways Discover AIprogram. It's designed to be accessible...
https://dev.my.umbc.edu/api/v0/pixel/news/127465/guest@my.umbc.edu/62159d14e29e03938f7785ba6a909697/api/pixel
ai
machine-learning
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 11 Sep 2022 19:55:53 -0400
Sat, 17 Sep 2022 12:59:57 -0400
Physical Security and How We Break It (Legally)
talk on physical penetration testing by alum Adam Sachsel
The UMBC Cyber Defense Lab presents
Physical Security and
How We Break It (Legally)
Adam J. Sachsel
Cyber Testing Associate
RSM Consulting
12-1pm Fri. 9 Sept. 2022, via WebEx
This talk explores many aspects of physical security, including why it is important, how physical security is assessed professionally, and some professional opinions on what comprises "good" physical security. Then, I will briefly touch on physical penetration testing and what usually comprises a physical penetration test. I will also relate a few fun war stories from some personal experiences while performing these kinds of tests.
Adam Sachsel graduated from UMBC in 2021 with a BS in computer science. Initially his goal was to become a software developer, until the UMBC Cyberdawgs recruited him and completely changed his career path to focus on security. After graduation Adam secured a job as a "Cyber Testing Associate" with RSM Consulting in Des Moines, Iowa. He was quickly assigned to the Social Engineering Team and now spends his days performing internal and external penetration tests, drafting phishing campaigns, and lying his way into secure areas around the U.S. He is currently on the path to achieve his Practical Network Penetration Tester (PNPT) certification and eventually join the RSM Red Team in more complex engagements. Email:
adamsachsel@gmail.com.
Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681.
The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL meetings: Sept 23, TBA; Oct 7, TBA; Oct 21, Peter Peterson, Misconceptions in cybersecurity; Nov 4, Josiah Dykstra (DoD), Myths in cybersecurity; Nov 18, Russ Fink (APL), ARMR: autonomous resilience / machine recovery; Dec 2, Peter Peterson, Adversarial Thinking; January 2-6, 2023 (tentative): SFS/CySP Research Study.
]]>
The UMBC Cyber Defense Lab presents Physical Security and How We Break It (Legally) Adam J. Sachsel Cyber Testing Associate RSM Consulting 12-1pm Fri. 9 Sept. 2022, via WebEx This...
https://dev.my.umbc.edu/api/v0/pixel/news/127380/guest@my.umbc.edu/6367e185ad3bfb3f04a4b0e6c1bad159/api/pixel
cybersecurity
talk
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
UMBC Cyber Defense Lab
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/xxlarge.jpg?1662644407
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/xlarge.jpg?1662644407
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/large.jpg?1662644407
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/medium.jpg?1662644407
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/small.jpg?1662644407
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/xsmall.jpg?1662644407
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/127/380/5f5cc0e1d193db626faad9a0db0766d4/xxsmall.jpg?1662644407
0
0
true
Thu, 08 Sep 2022 09:49:10 -0400
Professional Development Opportunity: AI & Careers in Tech
Free College Pathways Discover AI program, apply by Sept. 14

Professional Development Opportunity:
Artificial Intelligence & Careers in Tech
WHEN
- The Discover AI program runs from September 30 to December 9 and include weekly synchronous and asynchronous Instruction. Review the program's application page for more details.
WHAT
- Discover AI is a virtual program in partnership with select schools that provides students with a project-based introduction to computer science, machine learning, data, artificial intelligence and tech careers through the lens of societal and ethics impact. In addition, students get access to AI industry leaders and are guided through a roadmap with the goal of cultivating a future career in the AI industry.
- What are both the positive and negative implications of AI technology on society? How can (and does) AI affect communities in today's world? Through research, discussions, and reflection, you will explore the intersectionality of AI with other fields and articulate your own mindful perspective of AI. The program is facilitated at no cost to students.
- Students that complete the program will emerge with actionable next steps in pursuing an academic or career path in AI - and the opportunity to continue in the following semester to our second program, Apply AI and direct mentorship from industry leaders in the AI and tech industry from companies like Google, Capital One, Facebook, Slalom Consulting, Accenture, Pearson, and more.
- At the end of the Discover AI program, participants receive an AI4ALL Discover AI certificate of completion.
WHO
- The program is designed for Freshman, Sophomores, and Juniors with any level of coding and/or Computing/AI experience, including everything from none to advanced.
- For computing majors, the program is a great supplement to your existing course work.
- Other majors are welcome as well! If accepted, you will have the opportunity to learn more about AI in a safe and thoughtful environment that offers you the opportunity to consider AI as a future career option and as a presence in your major industry/discipline
- AI4ALL programs are designed to bring together and highlight voices that have been historically excluded, and that will lead and shape the future of AI.
]]>
Professional Development Opportunity: Artificial Intelligence & Careers in Tech UMBC and nonprofit AI4ALL have partnered to offer UMBC undergraduate students the opportunity to apply to...
https://ai-4-all.org/
https://dev.my.umbc.edu/api/v0/pixel/news/127191/guest@my.umbc.edu/c6462d97fb92b768460bfdc8f98d46e4/api/pixel
ai
ai4all
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 31 Aug 2022 18:46:24 -0400
NSA Codebreaker Challenge Technical Talk
6 pm ET Thursday, September 1, online
NSA will hold a 2022 Codebreaker Challenge Technical Talk online at 6:00pm ET on Thursday, September 1. You'll meet the team and get an overview of the challenge this year. Join the talk using this MS Teams link.
The annual NSA
Codebreaker Challenge consists of a series of tasks for students that are worth a varying amount of points based on their difficulty. Schools are ranked according to the total number of points accumulated by their students. Solutions may be submitted at any time during the challenge, which ends early in January, 2023.
Each task in this year's challenge will require a range of skills. It starts with easy tasks but advances to harder ones, so it's a great learning experience even if you are know little about cybersecurity. To solve all of the tasks, you will need to call upon your technical expertise, your intuition, and your common sense.
Getting started is easy. Go to the challenge
webpage, create an account and identify yourself as a student, instructor, or alumnus of UMBC. After you've verified your email address, you will get an invitation to join the
Codebreaker Discord server. Joining will earn you (and UMBC) your first point!
As you work on the problems, you can
track how UMBC is doing on the leaderboard. Of the more than 340 schools currently registered, UMBC is #2 in terms of the number of its participants, but only #45 in based on its score.