talk: Human mental models and robots: Grasping and tele-presence, 11am 5/9

Human mental models and robots:
Grasping and tele-presence
Dr. Cindy Grimm, Oregon State University
11:00-12:00 Monday 9 May 2016, ITE 325b
In this talk I will cover two separate research efforts in robotics, both of which use human mental models to improve robotic functionality. Robots struggle to pick up and manipulate physical objects, yet humans do this with ease – but can’t tell you how they do it. In this research we focus on how to capture human data in such a way as to gain insight into how people structure the grasping task. Specifically, we look at the role of perceptual cues in evaluating grasps and mental classification models of grasps (i.e., all these grasps are the “same”). In the second half of the talk I will switch to discussing how human mental models of privacy, trust, and presence come in to play in remote tele-presence applications (“Skype-on-a-movable-stick”).
Dr. Cindy Grimm is currently an associate professor at Oregon State University (since 2013) in the School of Mechanical, Industrial, and Manufacturing Engineering (application area robotics). Prior to that she was tenured faculty at Washington University in St. Louis in Computer Science (12 years). Her research areas range from 3D sketching to biological modeling to human-robot interaction. She approaches these problems with a combination of mathematical models and empirically-verified human-centered design (HCD). Mathematical models provide a sound, quantitative, rigorous, elegant basis for representing shape and function, and are a core part of the “language” of computation. Including a human in the loop is a key component of the application areas she works in; HCD provides the mechanism for addressing the fundamental problem of how to make mathematical computation “useful” for humans. She has worked with collaborators in fields ranging from psychology, mechanical and biological engineering, statistics, to art.
]]>
Human mental models and robots: Grasping and tele-presence Dr. Cindy Grimm, Oregon State University 11:00-12:00 Monday 9 May 2016, ITE 325b In this talk I will cover two separate research...
http://www.csee.umbc.edu/2016/05/talk-human-mental-models-and-robots-grasping-and-tele-presence-11am-59/
https://dev.my.umbc.edu/api/v0/pixel/news/59974/guest@my.umbc.edu/458296f1894f82516822f9488eb130aa/api/pixel
computer-engineering
computer-science
news
research
robotics
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Fri, 06 May 2016 12:51:56 -0400
talk: Statistical Testing of Hash Bit Sequences, 11:15am Fri May 6, UMBC

The UMBC Cyber Defense Lab presents
Statistical Testing of Hash Bit Sequences
Enis Golaszewski
CSEE, UMBC
11:15am-12:30pm Friday, 6 May 2016, ITE 237
We tested bit sequences generated from the MD5 hash function using multinomial distribution and close-point spatial statistical tests for randomness. We found that bit sequences generated from truncated-round MD5 hash fail these tests for high- and low-density input choices.
In 2000, the National Institute of Standards and Technology concluded a competition to select the Advanced Encryption Standard. One of the requirements for candidates was randomness of output bits. The techniques used to evaluate symmetric block cipher randomness have not been extensively applied to hash functions.
In this study, we adapt a subset of the techniques used to analyze the randomness of AES candidate algorithms to study the randomness of the well-known MD5 hash function. Our approach uses high-density, lo- density, and chained-input methods to generate MD5 hashes. We concatenate these hash outputs and subjected them to multinomial distribution and close-point spatial tests. We iterated this approach over reduced-round versions of MD5. Our presentation includes specifications for the input methods, details on the statistical tests, and analysis of the statistical results.
Through statistical testing of concatenated MD5 hashes, we derive results that demonstrate a link between the performance of the concatenated hash bit sequences in our statistical testing and the number of hash rounds applied to the high-density and low-density input methods. Randomness is a desirable property for cryptographic hash functions. We present a new approach that facilitates the analysis and interpretation of hash functions for statistical randomness.
About the Speaker. Enis Golaszewski is a prospective PhD student in CS at UMBC, working with Dr. Alan T. Sherman. His research interests include the security of software-defined networks. He graduated from UMBC in CS in December 2015 and was a student in the fall 2015 INSuRE class. Email: <Sorry, you need javascript to view this email address. >
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Statistical Testing of Hash Bit Sequences Enis Golaszewski CSEE, UMBC 11:15am-12:30pm Friday, 6 May 2016, ITE 237 We tested bit sequences generated...
http://www.csee.umbc.edu/2016/05/20573/
https://dev.my.umbc.edu/api/v0/pixel/news/59963/guest@my.umbc.edu/fe105755ae51867d909cc45707e8ac6a/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 05 May 2016 22:12:30 -0400
Thu, 05 May 2016 22:12:30 -0400
tutorial: Design, Analysis and Security of Automotive Networks, 2pm 4/29
Design, Analysis and Security of Automotive Networks
Sekar Kulandaivel
University of Maryland, Baltimore County
2:00-3:30pm Friday, 29 April 2016, ITE 325b
As more electronic and wireless technologies permeate modern vehicles, understanding the design of an embedded automotive network becomes necessary to protect drivers from external agents with a malicious intent to disrupt onboard electronics. By analyzing the different types of automotive networks and current security issues that the industry faces, we will learn how intruders are able to access an automotive network, read data that streams from the connected nodes and inject potentially malicious messages. This presentation will cover the electrical design of automotive networks, the communication protocols between electronic control units, methods for analyzing network messages and a detailed overview of previous automotive attacks and current security issues.
Sekar Kulandaivel is a Meyerhoff Scholar and Computer Engineering undergraduate student at UMBC. He currently works on designing an intrusion detection system for automotive networks with Dr. Nilanjan Banerjee of the UMBC Eclipse Cluster. Sekar has had previous internships at MIT Lincoln Laboratory, Northrop Grumman Corporation and Johns Hopkins University. He will attend Carnegie Mellon University in Fall 2016 to pursue a PhD in Electrical and Computer Engineering with a focus in electric vehicle security.
]]>
Design, Analysis and Security of Automotive Networks Sekar Kulandaivel University of Maryland, Baltimore County 2:00-3:30pm Friday, 29 April 2016, ITE 325b As more electronic and wireless...
http://www.csee.umbc.edu/2016/04/tutorial-design-analysis-and-security-of-automotive-networks-2pm-429/
https://dev.my.umbc.edu/api/v0/pixel/news/59723/guest@my.umbc.edu/3ebfa9715706199e10a97506bbec1fd5/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 27 Apr 2016 14:42:55 -0400
talk: Medical Epistemology: A Gerontologist’s Perspective, 3pm Wed 4/27

CHMPR Seminar
Medical Epistemology: A Gerontologist’s Perspective
Dr. John D. Sorkin, M.D., Ph.D.
University of Maryland School of Medicine
3:00pm Wednesday, 27 April 2016, ITE 325b
The randomized clinical trial is the gold standard method by which we test a hypothesis positing an association between an exposure and outcome. Unfortunately many hypotheses are not grist for a clinical trial. It would, for example not be ethically permissible to randomize people to smoking vs. non-smoking if we wanted to study the hypothesis that smoking is associated with increased incidence of lung cancer. Similarly it would not be ethical to randomize pregnant women to being infected or not infected with Zika virus to determine if maternal Zika infection is associated with microcephaly. Clinical trials are also not helpful in determining the relation between a putative exposure and a rare disease such as Pick’s disease (a rare type of frontotemporal dementia) as the number of subjects who would need to be studied is prohibitively large.
The movement over the last decade away from paper-based charts to the electronic medical record (EMR) and advances in the speed of computers allow us to process large volumes of data in near real-time, and herald the advent of clinical studies based on “big data”. The availability of big data requires us to rethink how we can establish an association between cause and effect because the big data we obtain from the EMR are not collected from randomized clinical trials, and as noted above a clinical trial cannot be used to study many diseases. Further making inferences based on the EMR can be difficult because data gleamed from the electronic medical record can be confounded by changes brought about by the aging process which include primary aging (i.e., the aging process itself), secondary aging (i.e., changes brought about by changes in lifestyle as we get older) and tertiary aging (i.e., disease). Fortunately epidemiologists have designed and used study designs other than the clinical trials for years to gain insight into the relation between exposure and disease. The aim of my talk is to review five study designs, cross-sectional, time-series and longitudinal, case-control and cohort study designs, that can be used to identify change, quantify the rate at which changes occurs with aging, and to separate biological aging from the effects of life style and disease. In addition to presenting the five study designs, I will review the strengths and weaknesses of the five study designs. It is my hope that thinking about five study designs will help you design analyses that make use of big data to examine questions relevant to public health and treatment of disease.
Dr. John Sorkin is a professor at the University of Maryland School of Medicine. His research examines the changes that occur with aging in carbohydrate and lipid metabolism, obesity, and body fat distribution. He is interested in measuring the changes and determining the relation of the changes to the development of diabetes, cardiovascular disease, death, morbidity, and mortality. These interests have lead him to try to identify the phenotypes associated with longevity and the genetics of longevity in collaboration with Drs. Shuldiner and Mitchell. Dr. Sorkin is Chief of Biostatistics and Informatics for the Division of Gerontology and is PI of the Statistics Core for the University of Maryland Claude D. Pepper Older Americans Independence Center and Baltimore VA Geriatrics Research, Education and Clinical Center.
]]>
CHMPR Seminar Medical Epistemology: A Gerontologist’s Perspective Dr. John D. Sorkin, M.D., Ph.D. University of Maryland School of Medicine 3:00pm Wednesday, 27 April 2016, ITE 325b The...
http://www.csee.umbc.edu/2016/04/big_data_medicine_sorkin/
https://dev.my.umbc.edu/api/v0/pixel/news/59660/guest@my.umbc.edu/4ce4f24cac9eb1b562252d915b758e89/api/pixel
computer-science
data-science
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 25 Apr 2016 14:59:37 -0400
talk: Securing the Cloud: The Need for Quantum Network Security, 11:15am 4/22 UMBC

UMBC Cyber Defense Lab
Securing the Cloud: The Need for Quantum Network Security
Brian Kelley, Senior Member IEEE
Associate Professor of ECE
The University of Texas at San Antonio
11:15am-12:30pm Friday, 22 April 2016, UMBC, ITE 227
A significant trend in cloud data centers virtualization has been the migration away from virtual machines (VMs) with multiple guest operating systems (OS) to containers with a single Host OS. Whereas VMs incorporate a hypervisor manager layer enabling the Host OS to spawn multiple guest OSs, containers support all the code, run-time tools, and system libraries to run workload applications from a single Host OS.
While all cloud-based platforms posses security vulnerabilities, the additional security challenges with container systems stem from the sharing of the Host OS among independent container applications.
In this presentation we pose the question, “Can we use quantum information concepts to protect the cloud?” We introduce Quantum Key Distribution (QKD) protocols. We present schemes for cloud container security based upon concepts drawn from QKD and related concepts in quantum teleportation. We also propose a new framework for Quantum Container Security drawing upon concepts of quantum entanglement. We will also present information the Cloud Academic Research Center at the University of Texas at San Antonio.
Dr. Brian Kelley is Associate Professor of ECE at the University of Texas at San Antonio. He is a leading researcher on communication systems, 4G and 5G cellular, cloud communications, and smart grid communications. He is also a member of the Cloud Academic Center at the University of Texas. Dr. Kelley is currently on sabbatical leave as a consultant with the DoD in Washington D.C. His current research focus is on the intersection of software-defined networks, 5G communications, and cloud systems. He is Senior Member of the IEEE, was an Oak Ridge National Laboratory Summer Faculty Fellow in Quantum Information Science during the summer of 2015, was Globecom 2014 Chair for the High-Level Technical Program Committee, Associate Editor and Editorial Board of IEEE System Journal, 2011-2012, and Associate Editor of Computers & Electrical Engineering, Elsevier, 2008-2011; he founded the San Antonio IEEE Communications and Signal Processing Chapter, in 2008. From 2000-2006, he was Distinguished Member of the Technical Staff at Motorola and a senior lecturer at the University of Texas at Austin. Since 2007, he has been Associate Professor of ECE and Director of the Wireless Next Generation Systems (WiNGS) Lab at the University of Texas at San Antonio. Dr. Kelley received his BSEE from Cornell University and his MS/PhD in EE from the Georgia Institute of Technology in 1992, where he was an ONR Fellow. He is a member of Tau Beta Pi and Eta Kappa Nu. Contact: Dr. Brian Kelley, (210) 706-0854 Sorry, you need javascript to view this email address.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
The UMBC Cyber Defense Lab meets biweekly Fridays (May 6: Enis Golaszewski, Hash bit sequences)
]]>
UMBC Cyber Defense Lab Securing the Cloud: The Need for Quantum Network Security Brian Kelley, Senior Member IEEE Associate Professor of ECE The University of Texas at San Antonio...
http://www.csee.umbc.edu/2016/04/talk-securing-the-cloud-the-need-for-quantum-network-security-1115am-422-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/59483/guest@my.umbc.edu/0ed8b20a9cfb1308eea87ec550ddd1f6/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 18 Apr 2016 23:21:23 -0400
Mon, 18 Apr 2016 23:21:23 -0400
talk: IoT Device Security Research at Morgan State University, 12pm Fri 4/15

UMBC CSEE Seminar
IoT Device Security Research at Morgan State University
Dr. Kevin T. Kornegay
Professor and IoT Security Endowed Chair,
School of Electrical and Computer Engineering, Morgan State University
12:00-1:00pm Friday, 15 April 2016, ITE 239, UMBC
The Internet of Things (IoT) and its myriad of components are proliferating as they increasingly permeate all areas of life and work, with unprecedented economic effect. The IoT is the network of dedicated physical objects (things) whose embedded system technology senses or interacts with their internal state or external environment. Embedded systems use a combination of computer hardware and software to perform dedicated functions within a larger mechanical or electrical system. Examples of embedded systems include cell phones, personal digital assistants, gaming consoles, global positioning systems, etc. Over 98 percent of all microprocessors being manufactured are used in embedded system applications. In private industry and the public sector, IoT growth and possible uses are evolving rapidly. Critical infrastructures in transportation, smart grid, manufacturing and health care are highly dependent on embedded systems for distributed control, tracking, and electronic data collection. While it is paramount to protect these systems from hacking, intrusion or physical tampering, our current solutions are often based on a patchwork of legacy systems, and this is unsustainable as a long-term solution. Transformative solutions are required to protect these systems by engineering secure embedded systems. Secure embedded systems use cryptography and countermeasures to protect electronic data and commands to systematically achieve resiliency, stability, safety, integrity, and privacy. Engineering secure embedded implementations that are resistant to attacks is vital. Essential to achieving this goal is obtaining fundamental knowledge and understanding of the various types of vulnerabilities embedded systems present. Hence, in this talk, we will present our embedded systems security research activities including the IoT testbed, side-channel and fault injection analysis, and associated research projects.
Kevin T. Kornegay received the B.S. degree in electrical engineering from Pratt Institute, Brooklyn, NY, in 1985 and the M.S. and Ph.D. degrees in electrical engineering from the University of California at Berkeley in 1990 and 1992, respectively. He is presently Professor and IoT Security Endowed Chair in the School of Electrical and Computer Engineering at Morgan State University in Baltimore, MD. His research interests include hardware assurance, reverse engineering, secure embedded system design, side-channel analysis, differential fault analysis, radio frequency and millimeter wave integrated circuit design, high-speed circuits, and broadband wired and wireless system design. Dr. Kornegay serves or has served on the technical program committees of several international conferences including the IEEE Symposium on Hardware Oriented Security and Trust (HOST), EEE International Solid State Circuits Conference, the IEEE Custom Integrated Circuits Conference, and the Radio Frequency Integrated Circuits Symposium. He has also served a two-year term on the IEEE Solid-State Circuits AdCom committee, as well as, on the editorial board of the IEEE Transactions on Circuits and Systems II and as Editor of IEEE Electron Device Letters and Guest Editor of the IEEE Journal of Solid-State Circuits Special Issue on the 2004 Compound Semiconductor IC Symposium. He is the recipient of numerous awards, including the National Society of Black Engineers’ Dr. Janice A. Lumpkin Educator of the Year in 2005, the 2002 Black Engineer of the Year Award in Higher Education from U.S. Black Engineer and Information Technology magazine, the NSF CAREER Award, an IBM Faculty Partnership Award, the National Semiconductor Faculty Development Award, and the General Motors Faculty Fellowship Award. He was also selected as a participant in the National Academy of Engineering Frontiers of Engineering Symposium, and the German–American Frontiers of Engineering, where he later served on the organizing committee. He is a Distinguished Lecturer of the IEEE Electron Devices Society and a senior member of the IEEE, as well as a member of Eta Kappa Nu and Tau Beta Pi.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks.
]]>
UMBC CSEE Seminar IoT Device Security Research at Morgan State University Dr. Kevin T. Kornegay Professor and IoT Security Endowed Chair, School of Electrical and Computer Engineering,...
http://www.csee.umbc.edu/2016/04/talk-iot-device-security-research-at-morgan-state-university-12pm-fri-415/
https://dev.my.umbc.edu/api/v0/pixel/news/59349/guest@my.umbc.edu/bb43ec29d3fc2de312f0759289abd928/api/pixel
computer-engineering
computer-science
cybersecurity
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 13 Apr 2016 10:54:05 -0400
Wed, 13 Apr 2016 10:54:05 -0400
talk: Statistical Methods for Integration and Analysis of Opinionated Text, 4/21
Distinguished Lecture Series, UMBC Department of Information Systems
Statistical Methods for Integration and Analysis of Opinionated Text Data
Dr. ChengXiang Zhai
Professor and Willett Faculty Scholar
University of Illinois at Urbana-Champaign
10:00am Thursday 21 April 2016, ITE 459, UMBC
Opinionated text data such as blogs, forum posts, product reviews and online comments are increasingly available on the Web. They are very useful sources for public opinions about virtually any topics. However, because the opinions are scattered and abundant, it is a significant challenge for users to collect all the opinions about a topic and digest them efficiently. In this talk, I will present a suite of general statistical text mining methods that can help users integrate, summarize and analyze scattered online opinions to obtain actionable knowledge for decision making. Specifically, I will first present approaches to integration of scattered opinions by aligning them to a well- structured article or relevant ontology. Second, I will discuss several techniques for generating a concise opinion summary that can reveal the major sentiments and opinion points buried in large amounts of opinionated text data. Finally, I will present probabilistic generative models for analyzing review data in depth to discover latent aspect ratings and relative weights placed by reviewers on different aspects. These methods are general and can thus potentially help users integrate and analyze large amounts of online opinionated text data on any topic in any natural language

ChengXiang Zhai is a Professor of Computer Science at the University of Illinois at Urbana-Champaign, where he also holds a joint appointment at the Institute for Genomic Biology, Statistics, and the Graduate School of Library and Information Science. His research interests include information retrieval, text mining, natural language processing, machine learning, and bioinformatics, and has published over 200 papers in these areas with an H-index of 58 in Google Scholar. He is an Associate Editor of ACM Transactions on Information Systems, and Information Processing and Management, and the Americas Editor of Springer’s Information Retrieval Book Series. He is a conference program co-chair of ACM CIKM 2004, NAACL HLT 2007, ACM SIGIR 2009, ECIR 2014, ICTIR 2015, and WWW 2015, and conference general co-chair for ACM CIKM 2016. He is an ACM Distinguished Scientist and a recipient of multiple best paper awards, Rose Award for Teaching Excellence at UIUC, Alfred P. Sloan Research Fellowship, IBM Faculty Award, HP Innovation Research Program Award, and the Presidential Early Career Award for Scientists and Engineers (PECASE).
]]>
Distinguished Lecture Series, UMBC Department of Information Systems Statistical Methods for Integration and Analysis of Opinionated Text Data Dr. ChengXiang Zhai Professor and Willett...
http://www.csee.umbc.edu/2016/04/talk-statistical-methods-for-integration-and-analysis-of-opinionated-text-421/
https://dev.my.umbc.edu/api/v0/pixel/news/59232/guest@my.umbc.edu/528ec35f2f746261851bbe59b01e3daf/api/pixel
information-systems
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sat, 09 Apr 2016 09:00:31 -0400
Mon, 18 Apr 2016 09:00:31 -0400
talk: Firmware Instruction Identification using Side-Channel Power Analysis
The UMBC Cyber Defense Lab presents
Firmware Instruction Identification
using Side-Channel Power Analysis
Deepak Krishnankutty
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
11:15am-12:30pm, Friday, April 8, 2016, ITE 237
Power supply transients of encryption devices have been analyzed from the perspective of performing attacks to extract secret key or confidential information. Such attacks are based on exploiting the correlation between the power consumption of the device under attack and its underlying logic operations. However, side channel leakage through the power supply of instruction level events occurring on soft/hard core processors has not been extensively studied. Power traces of firmware running on general purpose processing units observed at low frequencies tend to reveal not just the variations in current consumption during individual clock cycles, but also information related to the sequence of instruction executions. In this talk, we present results from Side-Channel Analysis performed over multiple power supply pins and demonstrate the relationship between the power transients and machine-level instructions on an instance of the openMSP430 processor on an FPGA. This process is also applicable to standalone ASIC instances. Our approach is based on templates constructed from principal components representing instructions identified from the power profiles of different instruction sequences. The templates are then utilized for determining the order of clock cycles per instruction. This technique can be used to predict the sequence of clock cycles per instruction from the observed power profiles and identify anomalies caused by modification of code on a tightly constrained embedded system.
Deepak Krishnankutty is a PhD student in computer engineering at UMBC, Sorry, you need javascript to view this email address.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
The UMBC Cyber Defense Lab meets biweekly Fridays. (April 22, Brian Kelley, Securing the cloud. May 8, Enis Enis Golaszewski, Hash bit sequences).
]]>
The UMBC Cyber Defense Lab presents Firmware Instruction Identification using Side-Channel Power Analysis Deepak Krishnankutty Computer Science and Electrical Engineering University of...
http://www.csee.umbc.edu/2016/04/talk-firmware-instruction-identification-using-side-channel-power-analysis/
https://dev.my.umbc.edu/api/v0/pixel/news/59175/guest@my.umbc.edu/827d531b884d1019e6663a9a2920d4c8/api/pixel
computer-engineering
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 07 Apr 2016 16:55:58 -0400
Thu, 07 Apr 2016 16:55:58 -0400
talk: Secret Life of Mobile Applications, 12pm 4/8

The Secret Life of Mobile Applications
Dr. Julia Rubin, MIT
12:00pm Friday, 8 April 2016, ITE 325b, UMBC
As software becomes increasingly more complex and yet more pervasive, poor understanding of software behavior compromises the quality and the integrity of software systems that we use. In this talk, I will show that automated analysis techniques can help to identify and reason about software behavior characteristics that matter to humans. After a brief overview of my current research directions, I will focus on techniques for identifying privacy violations in mobile applications, i.e., leakages of sensitive information such as user location and shopping preferences. I will present a set of solutions that rely on contextual, functional and usage-based clues for improving the accuracy of leakage detection and for distinguishing between “legitimate” and “illegitimate” information distribution patterns.
Julia Rubin is a Postdoctoral Researcher in the EECS department at MIT. Prior to that, she was a Research Staff Member and, part of the time, a manager at IBM Research in Haifa, Israel. She received her PhD in Computer Science from the University of Toronto, Canada in 2014. Julia’s research interests are in software engineering, program analysis and software security, focusing on improving the quality and the integrity of modern software systems. Her recent work in this area won an ACM Distinguished Paper Award at ASE, two Best Paper Awards, at SPLC and CSMR, and was nominated for Facebook’s Internet Defense Prize at the USENIX Security Symposium.
]]>
The Secret Life of Mobile Applications Dr. Julia Rubin, MIT 12:00pm Friday, 8 April 2016, ITE 325b, UMBC As software becomes increasingly more complex and yet more pervasive, poor...
http://www.csee.umbc.edu/2016/04/talk-secret-life-of-mobile-applications-12pm-48/
https://dev.my.umbc.edu/api/v0/pixel/news/59093/guest@my.umbc.edu/b83804b16bc6ee34054356659cebe02f/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 05 Apr 2016 09:40:16 -0400
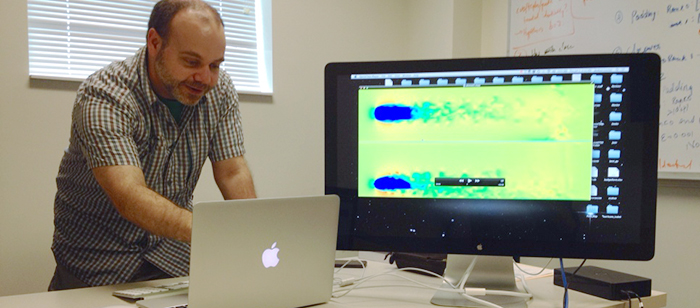
talk: Visualizing (Scientific) Simulations, 12pm 4/4, UMBC
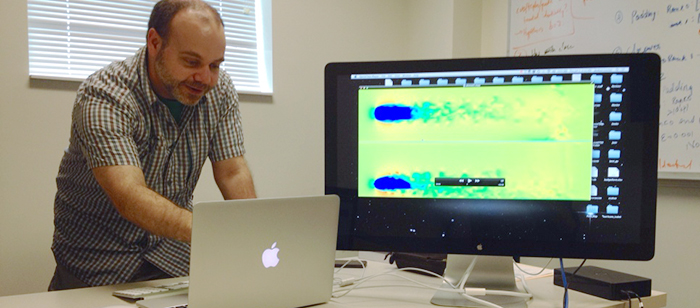
Visualizing (Scientific) Simulations with
Geometric and Topological Features
Prof. Joshua A. Levine, Clemson University
12:00pm Monday, 4 April 2016, ITE 325b, UMBC
Today’s HPC resources are an essential component for enabling new scientific discoveries. Specifically, scientists in all fields leverage HPC to do computational simulations that complement laboratory experimentation. These simulations generate truly massive data; visualization offers a mechanism to help understand the simulated phenomena this data describes.
This talk will present two recent research projects, both of which highlight new techniques for visualization based on characterizing and computing features of interest. The first project describes an algorithm for surface extraction from particle data. This data is commonly used in simulations for phenomena at small (molecular dynamics), medium (fluid flow, fracture), and large (astrophysics) length scales. Surface geometry allows standard computer graphics approaches to be used to visualize complex behaviors. The second project introduces a new data structure for representing vector field data commonly found in computational fluid dynamics and climate modeling. This data structure enables robust extraction of topological features that provide summary visualizations of vector fields. Both projects exemplify my vision for how collaborative efforts between experts in scientific and computational fields are necessary to make the best use of our HPC systems.
Joshua A. Levine is an assistant professor in the Visual Computing division of the School of Computing at Clemson University. He received his PhD from The Ohio State University after completing his BS and MS in Computer Science from Case Western Reserve University. His research interests include visualization, geometric modeling, topological analysis, mesh generation, vector fields, volume and medical imaging, computer graphics, and computational topology.
Host: Prof. Adam Bargteil (Sorry, you need javascript to view this email address. )
]]>
Visualizing (Scientific) Simulations with Geometric and Topological Features Prof. Joshua A. Levine, Clemson University 12:00pm Monday, 4 April 2016, ITE 325b, UMBC Today’s HPC resources are...
http://www.csee.umbc.edu/2016/03/talk-visualizing-scientific-simulations-12pm-44-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/59017/guest@my.umbc.edu/08db1b0356e24ff3d1cbdf6cb3147a35/api/pixel
computer-science
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 31 Mar 2016 23:02:37 -0400
Thu, 31 Mar 2016 23:02:37 -0400