talk: Reverse Engineering of Dynamic Regulatory Networks from Morphological Data, 11am 4/7
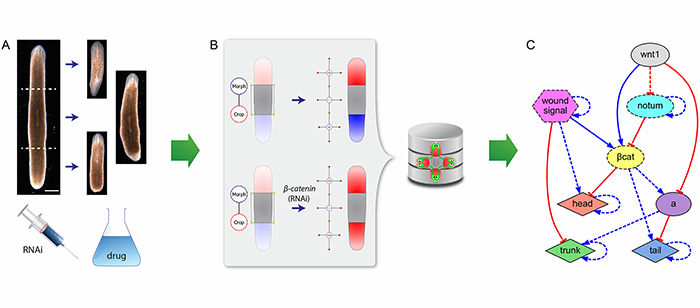
Reverse Engineering of Dynamic Regulatory Networks
from Morphological Experimental Data
Prof. Daniel Lobo, Biological Sciences, UMBC
3:00pm 11:00am April 7 6th, ITE Building, Room 325b
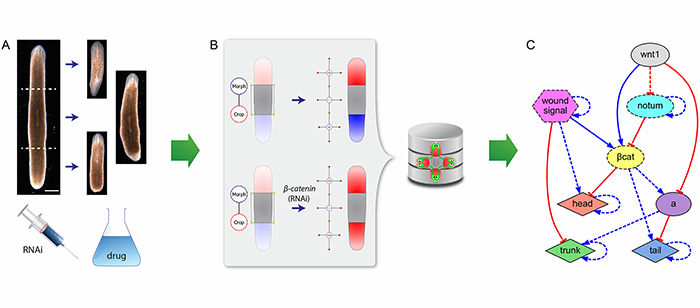
Many crucial experiments in developmental, regenerative, and cancer biology are based on manipulations and perturbations resulting in morphological outcomes. For example, planarian worms can regenerate a complete organism from almost any amputated piece, but knocking down certain genes can result in the regeneration of double-head phenotypes. However, the inherent complexity and non-linearity of biological regulatory networks prevent us from manually discerning testable comprehensive models from patterning and morphological results, and existent bioinformatics tools are generally limited to genomic or time-series concentration data. As a consequence, despite a huge experimental dataset in the literature, we still lack mechanistic explanations that can account for more than one or two morphological results in many model organisms. To bridge this gulf separating morphological data from an understanding of pattern and form regulation, we developed a computational methodology to automate the discovery of dynamic genetic networks directly from formalized phenotypic experimental data. In this seminar, I will present novel formal ontologies and databases of surgical, genetic, and pharmacological experiments with their resultant morphological phenotypes, together with artificial intelligence tools based on evolutionary computation and in silico simulators that can directly mine these data to reverse-engineer mechanistic dynamic genetic models. We demonstrated this approach by automatically discovering the first comprehensive model of planarian regeneration, which not only explains at once all the key experiments available in the literature (including surgical amputations, knock-down of specific genes, and pharmacological treatments), but also predicts testable novel pathways and genes. This approach is readily paving the way for understanding the regulation (and dis-regulation) of complex patterns and shapes in developmental, regenerative, and cancer biology.
Daniel Lobo is an Assistant Professor at the University of Maryland, Baltimore County. His research aims to understand, control, and design the dynamic regulatory mechanisms governing complex biological processes. To this end, his group develops new computational methods, ontologies, and high-performance in silico experiments to automate the reverse-engineering of quantitative models from biological data and the design of regulatory networks for specific functions. They seek to discover the mechanisms of development and regeneration, find therapies for cancer and other diseases, and streamline the application of synthetic biology. His work has received widespread media coverage including Wired, TechRadar, and Popular Mechanics.
]]>
Reverse Engineering of Dynamic Regulatory Networks from Morphological Experimental Data Prof. Daniel Lobo, Biological Sciences, UMBC 3:00pm 11:00am April 7 6th, ITE Building, Room 325b Many...
http://www.csee.umbc.edu/2016/03/talk-reverse-engineering-of-dynamic-regulatory-networks-from-morphological-experimental-data/
https://dev.my.umbc.edu/api/v0/pixel/news/58879/guest@my.umbc.edu/a025050bc8d884458540162747d5c2d0/api/pixel
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 29 Mar 2016 09:31:40 -0400
Tue, 29 Mar 2016 09:31:40 -0400
talk: Probabilistic Modeling of Socio-Behavioral Interactions, 12p 3/24

A Probabilistic Approach to Modeling Socio-Behavioral Interactions
Arti Ramesh, University of Maryland, College Park
Noon Thursday, 24 March 2016, ITE325b
The vast growth and reach of the Internet and social media have led to a tremendous increase in socio-behavioral interaction content on the web. The ever-increasing number of online interactions has led to a growing interest to understand and interpret online communications to enhance user experience. My work focuses on building scalable computational methods and models for representing and reasoning about rich, heterogeneous, interlinked socio-behavioral data. In this talk, I focus on one such emerging online interaction platform—online courses (MOOCs). I develop a family of probabilistic models to represent and reason about complex socio-behavioral interactions in the following real-world problems: 1) modeling student engagement, 2) predicting student completion and dropouts, 3) modeling student sentiment in discussion forums toward various course aspects (e.g., academic content vs. logistics) and its effect on their course completion, and 4) designing an automatic system to predict fine-grained topics and sentiment in online course discussion forums. I demonstrate the efficacy of these models via extensive experimentation on data from twelve Coursera courses. These methods have the potential to improve learning and teaching experience of online education participants and focus limited instructor resources to increase student retention.
Arti Ramesh is a PhD candidate at University of Maryland, College Park. Her primary research interests are in the field of machine learning and data science, particularly on probabilistic graphical models. Her advisor is Prof. Lise Getoor. Her research focuses on building scalable models for reasoning about interconnectedness, structure, and heterogeneity in socio-behavioral networks. She has published papers in peer-reviewed conferences such as AAAI and ACL. She has served on the TPC for ACL workshop on Building Educational Applications and has served as a reviewer for notable conferences and journals such as NIPS, Social Networks and Mining, and Computer Networks. She has won multiple awards during her graduate study including the outstanding graduate student Dean’s fellowship 2016, Dean’s graduate fellowship (2012-2014), and yahoo scholarship for grace hopper. She has worked at IBM research and LinkedIn during her graduate study. She received her Masters in Computer Science from University of Massachusetts, Amherst.
]]>
A Probabilistic Approach to Modeling Socio-Behavioral Interactions Arti Ramesh, University of Maryland, College Park Noon Thursday, 24 March 2016, ITE325b The vast growth and reach of the...
http://www.csee.umbc.edu/2016/03/talk-probabilistic-modeling-of-socio-behavioral-interactions-12p-324/
https://dev.my.umbc.edu/api/v0/pixel/news/58779/guest@my.umbc.edu/a88b439e84028815184c87e4842aedde/api/pixel
computer-science
data-science
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 23 Mar 2016 23:55:34 -0400
Wed, 23 Mar 2016 23:55:34 -0400
talk: Adversarial Machine Learning in Relational Domains, 12pm 3/22

Adversarial Machine Learning in Relational Domains
Prof. Daniel Lowd, University of Oregon
12:00-1:00 Tuesday, 22 March 2016, ITE 325b, UMBC
Many real-world domains, such as web spam, auction fraud, and counter-terrorism, are both adversarial and relational. In adversarial domains, a model that performs well on training data may do poorly in practice as adversaries modify their behavior to avoid detection. Previous work in adversarial machine learning has assumed that instances are independent from each other, both when manipulated by an adversary and labeled by a classifier. Relational domains violate this assumption, since object labels depend on the labels of related objects as well as their own attributes.
In this talk, I will present two different methods for learning relational classifiers that are robust to adversarial noise. Our first approach assumes that related objects have correlated labels and that the adversary can modify a certain fraction of the attributes. In this case, we can incorporate the adversary’s worst-case manipulation directly into the learning problem and find optimal weights in polynomial time. Our second method generalizes to any relational learning problem where the perturbations in feature space are bounded by an ellipse or polyhedron. In this case, we show that adversarial robustness can be achieved by a simple regularization term or linear transformation of the feature space. These results form a promising foundation for building robust relational models for adversarial domains.
Daniel Lowd is an Assistant Professor in the Department of Computer and Information Science at the University of Oregon. His research interests include learning and inference with probabilistic graphical models, adversarial machine learning, and statistical relational machine learning. He received his Ph.D. in 2010 from the University of Washington. He has received a Google Faculty Award, an ARO Young Investigator Award, and the best paper award at DEXA 2015.
Host: Cynthia Matuszek, Sorry, you need javascript to view this email address.
]]>
Adversarial Machine Learning in Relational Domains Prof. Daniel Lowd, University of Oregon 12:00-1:00 Tuesday, 22 March 2016, ITE 325b, UMBC Many real-world domains, such as web spam,...
http://www.csee.umbc.edu/2016/03/talk-adversarial-machine-learning-in-relational-domains-12pm-322/
https://dev.my.umbc.edu/api/v0/pixel/news/58634/guest@my.umbc.edu/ec70e2856b2535bbd7da1249f6171950/api/pixel
computer-science
cybersecurity
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 17 Mar 2016 18:00:42 -0400
Thu, 17 Mar 2016 18:00:42 -0400
talk: Rethinking the Cloud for Next-generation Applications, 3/21

Rethinking the Cloud for Next-generation Applications
Tian Guo, University of Massachusetts
11:00am Monday, 21 March 2016, ITE325b
Today’s cloud platforms serve an increasing number of requests from millions of mobile users. This mobile workload introduces new challenges and workload dynamics that differ from traditional workloads. In the future, billions of Internet-of-Things (IoT) devices will connect to cloud platforms and compete for cloud resources. Current cloud platforms are agnostic to the type of end-devices and are not well suited to emerging application needs. My work argues that these trends require a rethinking of current cloud platforms and focuses on the challenges of handling the dynamics introduced by these next-generation applications.
In this talk, I will describe two aspects of cloud design: handling demand-side dynamics from emerging cloud workloads and handling supply-side dynamics from varying cloud platform resources. Specifically, I will describe model-driven mechanisms to optimize user-perceived performance for global workloads that exhibit spatial variations, and mechanisms to effectively support running applications on transient servers—servers with unpredictable availability. Finally, I will conclude my talk with future work in cloud research to handle emerging mobile and IoT applications.
Tian Guo is a Ph.D. student in the College of Information and Computer Sciences at University of Massachusetts Amherst. Her research interests include distributed systems, cloud computing, mobile computing and cloud-enabled IoTs. Her current focus is on handling dynamics introduced by new cloud workloads and emerging cloud platforms. She received her B.E. in Software Engineering from Nanjing University, China in 2010 and her M.S. in Computer Science from University of Massachusetts Amherst in 2013.
]]>
Rethinking the Cloud for Next-generation Applications Tian Guo, University of Massachusetts 11:00am Monday, 21 March 2016, ITE325b Today’s cloud platforms serve an increasing number of...
http://www.csee.umbc.edu/2016/03/talk-rethinking-the-cloud-for-next-generation-applications-321-2/
https://dev.my.umbc.edu/api/v0/pixel/news/58616/guest@my.umbc.edu/7b865b95675584867733a3ee5900d894/api/pixel
computer-science
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 17 Mar 2016 08:59:55 -0400
Thu, 17 Mar 2016 08:59:55 -0400
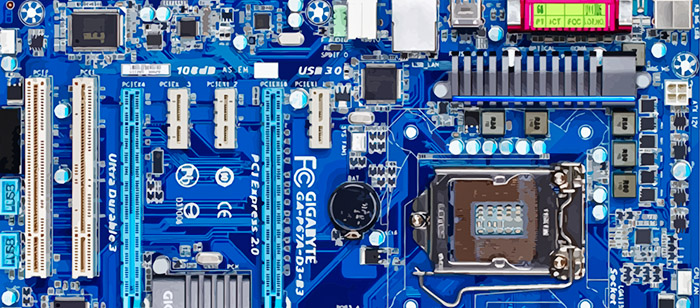
talk: Integrated Circuit Security and Trustworthiness, 11am 3/23
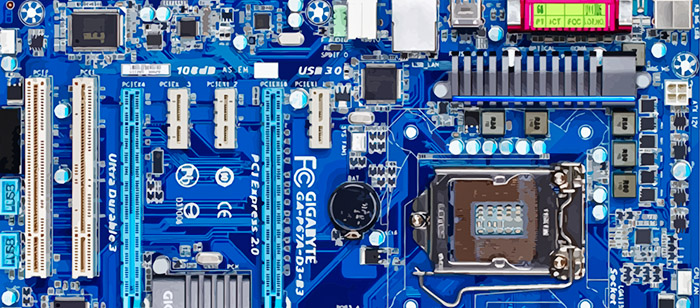
Integrated Circuit Security and Trustworthiness
Dr. Hassan Salmani, Howard University
11:00am Wednesday, 23 March 2016, ITE 325b, UMBC
Integrated Circuits are at the core of any modern computing system such as military systems and smart electric power grids, and their security and trustworthiness ground the security of entire system. Notwithstanding the central impact of ICs security and trustworthiness, the horizontal IC supply chain has become prevalent due to confluence of increasingly complex supply chains and cost pressures.
In this presentation, Professor Salmani will present an overview on some of his contribution into hardware security and trust including vulnerability of digital circuits to malicious modification called hardware Trojans at different levels, design methodologies and techniques to facilitate hardware Trojan detection, and design methodologies to prevent design counterfeiting. In a detailed discussion, Professor Salmani will focus on the vulnerability of ICs to hardware Trojan insertion at the layout level.
Professor Hassan Salmani received the Ph.D. degree from the University of Connecticut, in 2011. He is currently an Assistant Professor with Howard University. While his current research sponsored by Defense Advanced Research Projects Agency and Howard University, he has published tens of journal articles and refereed conference papers and has given several invited talks. He has published one book and one book chapter. His current research projects include hardware security and trust and supply chain security. He is a member of the SAE International’s G-19A Tampered Subgroup, ACM, and ACM SIGDA. He serves as a Program Committee and Session Chair of the Design Automation Conference, Hardware-Oriented Security and Trust, the International Conference on Computer Design, and VLSI Design and Test.
]]>
Integrated Circuit Security and Trustworthiness Dr. Hassan Salmani, Howard University 11:00am Wednesday, 23 March 2016, ITE 325b, UMBC Integrated Circuits are at the core of any modern...
http://www.csee.umbc.edu/2016/03/talk-integrated-circuit-security-and-trustworthiness/
https://dev.my.umbc.edu/api/v0/pixel/news/58743/guest@my.umbc.edu/b8338dfa06cb7ab183bf165971a13cc2/api/pixel
computer-engineering
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 14 Mar 2016 23:47:20 -0400
talk: Improving Password Security and Usability with Data-Driven Approaches, 3/11

Improving Password Security and Usability with Data-Driven Approaches
Blase Ur, CMU
12:30pm Friday, 11 March 2016, ITE325b
Users often must make security and privacy decisions, yet are rarely equipped to do so. In my research, I aim to understand both computer systems and the humans who use them. Armed with this understanding, I design and build tools that help users protect their security and privacy.
In this talk, I will describe how I applied this research approach to password security and usability. As understanding what makes a password good or bad is crucial to this process, I will first discuss our work on metrics for password strength. These metrics commonly involve modeling password cracking, which we found often vastly underestimates passwords’ vulnerability to cracking in the real world. We instead propose combining a series of carefully configured approaches, which we found to conservatively model real-world experts. We used these insights to implement a Password Guessability Service, which is already used by nearly two dozen research groups. I will then discuss our work on another key step to helping users create better passwords: understanding why humans create the passwords they do. I will focus on the impact of password-strength meters and users’ perceptions of password security. By combining better metrics with an understanding of users, I show how we can design tools that guide users toward better passwords.
Blase Ur is a Ph.D. candidate at Carnegie Mellon University’s School of Computer Science, where he is advised by Lorrie Cranor. His research interests lie at the intersection of security, privacy, and human-computer interaction (HCI). In addition to his work on password security, he has studied numerous aspects of online privacy and the Internet of Things (IoT). Previously, he obtained his A.B. in Computer Science from Harvard University. He is the recipient of an NDSEG fellowship, a Fulbright scholarship, a Yahoo Key Scientific Challenges Award, the best paper award at UbiComp 2014, and honorable mentions for best paper at both CHI 2012 and CHI 2016.
]]>
Improving Password Security and Usability with Data-Driven Approaches Blase Ur, CMU 12:30pm Friday, 11 March 2016, ITE325b Users often must make security and privacy decisions, yet are...
http://www.csee.umbc.edu/2016/03/talk-improving-password-security-and-usability-with-data-driven-approaches/
https://dev.my.umbc.edu/api/v0/pixel/news/58492/guest@my.umbc.edu/8662ae6a6344d590e9ec66ddf763b095/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 08 Mar 2016 19:00:41 -0500
Tue, 08 Mar 2016 19:00:41 -0500
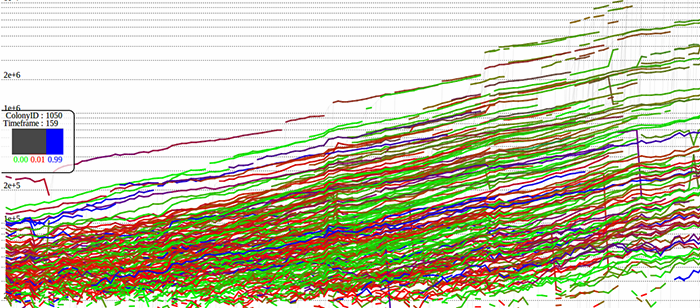
talk: To Measure or not to Measure Terabyte-Sized Images? 3pm 3/9
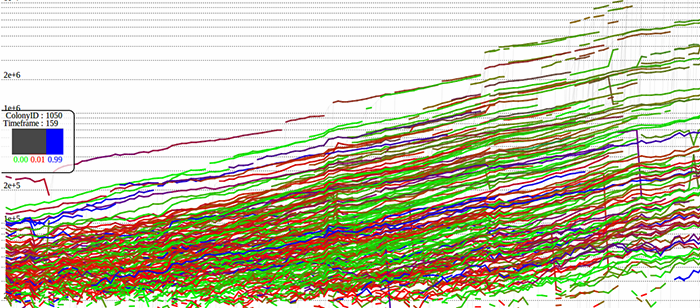
CHMPR Seminar
To Measure or not to Measure Terabyte-Sized Images?
Peter Bajcsy, PhD
Information Technology Laboratory
National Institute for Standards and Technology
3:00pm Wednesday, 9 March 2016, ITE325b, UMBC
This talk will elaborate on a basic question “To Measure or Not To Measure Terabyte-Sized Images?” posed by William Shakespeare if he were a bench scientist at NIST. This basic question is a dilemma for many traditional scientists that operate imaging instruments capable of acquiring very large quantities of images. However, manual analyses of terabyte-sized images and insufficient software and computational hardware resources prevent scientists from making new discoveries, increasing statistical confidence of data-driven conclusions, and improving reproducibility of reported results.
The motivation for our work comes from experimental systems for imaging and analyzing human pluripotent stem cell cultures at the spatial and temporal coverages that lead to terabyte-sized image data. The objective of such an unprecedented cell study is to characterize specimens at high statistical significance in order to guide a repeatable growth of high quality stem cell colonies. To pursue this objective, multiple computer and computational science problems have to be overcome including image correction (flat-field, dark current and background), stitching, segmentation, tracking, re-projection, feature extraction, data-driven modeling and then representation of large images for interactive visualization and measurements in a web browser.
I will outline and demonstrate web-based solutions deployed at NIST that have enabled new insights in cell biology using TB-sized images. Interactive access to about 3TB of image and image feature data is available at https://isg.nist.gov/deepzoomweb/.
Peter Bajcsy received his Ph.D. in Electrical and Computer Engineering in 1997 from the University of Illinois at Urbana-Champaign and a M.S. in Electrical and Computer Engineering in 1994 from the University of Pennsylvania. He worked for machine vision, government contracting, and research and educational institutions before joining the National Institute of Standards and Technology in 2011. At NIST, he has been leading a project focusing on the application of computational science in biological metrology, and specifically stem cell characterization at very large scales. Peter’s area of research is large-scale image-based analyses and syntheses using mathematical, statistical and computational models while leveraging computer science fields such as image processing, machine learning, computer vision, and pattern recognition. He has co-authored more than more than 27 journal papers and eight books or book chapters, and close to 100 conference papers.
]]>
CHMPR Seminar To Measure or not to Measure Terabyte-Sized Images? Peter Bajcsy, PhD Information Technology Laboratory National Institute for Standards and Technology 3:00pm Wednesday, 9...
http://www.csee.umbc.edu/2016/03/measure-terabyte-images-bajcsy/
https://dev.my.umbc.edu/api/v0/pixel/news/58396/guest@my.umbc.edu/3e4f7bd3497343c91210822033ecaafe/api/pixel
computer-science
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 06 Mar 2016 16:18:21 -0500
Sun, 06 Mar 2016 16:18:21 -0500
talk: Automated Privacy Policy Compliance, 11:30 Mon 3/7

Automated Privacy Policy Compliance
Dr. Omar Chowdhury, Purdue University
11:30am Monday, 7 March 2016, ITE325b, UMBC
Privacy regulations often govern data sharing and data use practices of organizations that collect personally identifiable information from their clients. For instance, in the US, healthcare organizations must comply with the federally mandated Health Insurance Portability and Accountability Act (HIPAA). Monetary penalties for non-compliance are high. The current practice of manual auditing for privacy violation is error-prone, cumbersome, and it does not scale well. It is thus crucial for the research community to develop automated tools and techniques to aid organizations in checking privacy policy compliance.
Within this context, I will first present encryption schemes that enable an organization to outsource the storage of audit logs and the computation of compliance checking to an untrusted cloud without completely giving up on privacy. Next, I will present an efficient compliance checker called précis, which leverages techniques from runtime verification and logic programming. Finally, I will conclude with a discussion of some remaining obstacles to practical deployment.
Omar Chowdhury is a Post-Doctoral Research Associate in the Department of Computer Science at Purdue University. Before joining Purdue, he was a Post-Doctoral Research Associate in Cylab at Carnegie Mellon University. He received his Ph.D. in Computer Science from the University of Texas at San Antonio. His research interest broadly lies in investigating practically relevant problems of Computer Security and Privacy. His current research focuses on leveraging formal verification and program analysis techniques to check compliance of a system implementation, against well-defined policies and properties. He won the best paper award at the ACM SACMAT’2012. He has also served as a program committee member of ACM SACMAT and ACM CCS.
host: Tim Finin, Sorry, you need javascript to view this email address.
]]>
Automated Privacy Policy Compliance Dr. Omar Chowdhury, Purdue University 11:30am Monday, 7 March 2016, ITE325b, UMBC Privacy regulations often govern data sharing and data use practices of...
http://www.csee.umbc.edu/2016/03/automated-privacy-policy-compliance/
https://dev.my.umbc.edu/api/v0/pixel/news/58310/guest@my.umbc.edu/8a993139466ed57714e4caba9bcdae67/api/pixel
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 03 Mar 2016 08:55:37 -0500
Thu, 03 Mar 2016 08:55:37 -0500
talk: Efficient Energy Delivery for Low Power IoT Devices, 11am 3/4
Efficient Energy Delivery for Low Power IoT Devices
Khondker Zakir Ahmed, Georgia Institute of Technology
11:00-12:00 Friday, 4 March 2016, ITE325b
Low power IoT Devices are growing in numbers and by 2020 there will be more than 25 Billion of those in areas such as wearables, smart homes, remote surveillance, transportation and industrial systems, including many others. Many IoT electronics either will operate from stand-alone energy supply (e.g., battery) or be self-powered by harvesting from ambient energy sources or have both options. Harvesting sustainable energy from ambient environment plays significant role in extending the operation lifetime of these devices and hence, lower the maintenance cost of the system, which in turn help make them integral to simpler systems. Both for battery-powered and harvesting capable systems, efficient power delivery unit remains an essential component for maximizing energy efficiency.
In this talk, I will discuss some of the most pressing challenges of energy delivery for low power electronics considering both energy harvesting as well as battery-powered conditions. Design techniques for very high conversion ratio, bias current reduction with autonomous bias gating, battery-less cold start, component and power stage multiplexing for reconfigurable and multi-domain regulators will be discussed. I will also present a highly integrated autonomous imaging system featuring a dual-purpose CMOS image sensor that is capable of both imaging and harvesting. This talk will focus only on the energy harvesting and power delivery aspect of this imaging system; presenting ‘a single inductor, single input, four output’power delivery unit with maximum power point tracking and prioritized output voltages. I will also present some silicon results from prototype chips developed in 130nm CMOS.
I will conclude the talk by discussing my vision of research on how low power analog electronics will play significant roles in realizing tomorrow’s ultra-low power, yet highly complex and smart electronic systems.
Khondker Zakir Ahmed is a PhD candidate in the School of Electrical and Computer Engineering at Georgia Institute of Technology, Atlanta, GA, where he works with the supervision of Professor Saibal Mukhopadhyay. He has received his MS in ECE from Georgia Tech in 2015 and BSc in EEE from Bangladesh University of Engineering and Technology in 2004. His primary research focus is power delivery circuit and systems design, specifically focused on low power electronics. His research accomplishments include innovative bias current reduction mechanism (Best in Session award, SRC TECHCON 2014), On-chip controller design for TEG/TEC for joint energy harvesting and hot-spot cooling (Best paper award, ISLPED 2014) and high conversion ratio hybrid down-converting regulator (Best in Session award, SRC TECHCON 2015). Khondker enjoys teaching; he has been a guest lecturer in several courses at Georgia Tech, and was a lecturer in the Department of Electrical and Electronic Engineering at East West University in Dhaka, Bangladesh for over a year before coming to Georgia Tech. Earlier, Khondker has worked as Analog IC Designer from 2005 to 2010 developing commercial power management ICs. He was a graduate intern at Intel Labs in the summers of 2013 and 2014, where he worked on adaptive voltage regulation for guardband reduction and cross-coupled voltage regulators with dynamic load sharing for microprocessors.
]]>
Efficient Energy Delivery for Low Power IoT Devices Khondker Zakir Ahmed, Georgia Institute of Technology 11:00-12:00 Friday, 4 March 2016, ITE325b Low power IoT Devices are growing in...
http://www.csee.umbc.edu/2016/03/talk-efficient-energy-delivery-for-low-power-iot-devices-11am-34/
https://dev.my.umbc.edu/api/v0/pixel/news/58283/guest@my.umbc.edu/369f1ead30f9b6347510a3474a197bf1/api/pixel
computer-engineering
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 02 Mar 2016 09:35:00 -0500
Wed, 02 Mar 2016 09:35:00 -0500
talk: Spatiotemporal Data Mining and Analytics, 3/3
Spatiotemporal Data Mining and Analytics:
Issues, Methods, and Applications
Shen-Shyang Ho, Nanyang Technological University
12:00pm Thursday, 3 March 2016, ITE325b, UMBC
The extensive and ubiquitous uses of sensors (e.g., satellites, in-situ sensors) and smartphones have resulted in the collection of huge amount of time-stamped data with location information. These large-scale dynamic datasets present many research challenges and application opportunities. In this talk, I describe my research work on spatiotemporal tasks related to (1) application-specific pattern mining, (2) prediction methods, (3) similarity search, and (4) privacy issue. Moreover, I highlight my new research direction in array-based distributed database for spatiotemporal domains.
Shen-Shyang Ho is a tenure-track assistant professor in the School of Computer Engineering at the Nanyang Technological University in Singapore since January 2012. Before this, he was a researcher at the University of Maryland, College Park from 2010 to 2011. He was a postdoctoral scholar at the California Institute of Technology from 2009 to 2010 and a NASA postdoctoral fellow at the Jet Propulsion Laboratory (JPL) from 2007 to 2009. Shen-Shyang received his Ph.D. in Computer Science from George Mason University in 2007 and his Bachelor (Honors) in Science (Mathematics and Computational Science) from the National University of Singapore in 1999. His research was supported by NASA, JPL, and GSFC between 2007 and 2012. His current research is supported by the Ministry of Education (Singapore), National Research Foundation (Singapore), Rolls Royce (UK), and BMW (Germany). He has two US patents and one pending Germany patent. He has given technical tutorials at AAAI (2011), IJCNN (2011), and ECML (2014).
Host: Cynthia Matuszek
]]>
Spatiotemporal Data Mining and Analytics: Issues, Methods, and Applications Shen-Shyang Ho, Nanyang Technological University 12:00pm Thursday, 3 March 2016, ITE325b, UMBC The extensive and...
http://www.csee.umbc.edu/2016/02/talk-spatiotemporal-data-mining-and-analytics-33/
https://dev.my.umbc.edu/api/v0/pixel/news/58245/guest@my.umbc.edu/916741acfe6f3442c092224691428b20/api/pixel
computer-science
data-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 29 Feb 2016 23:48:33 -0500