talk: Programming & Tuning a Quantum Annealing Computer to Solve Real-World Applications, 2pm 10/26, UMBC

Programming and Tuning a Quantum Annealing Computer to Solve Real-World Applications
Dr. Alejandro Perdomo-Ortiz
Quantum Artificial Intelligence Laboratory
NASA Ames Research Center
2:00pm Monday 26 October 2015, ITE 325b
Since September 2013 and through a partnership with Google and USRA, NASA Ames Research Center has been working with a quantum device that has the promise of harnessing quantum-mechanical effects to speed up the solution of optimization problems. Solving real-world applications with quantum algorithms requires overcoming several challenges, ranging from translating the computational problem at hand to the quantum-machine language, to tuning several other parameters of the quantum algorithm that have a significant impact on performance of the device. In this talk, we discuss these challenges, strategies developed to enhance performance, and also a more efficient implementation of several applications. Although we will focus on applications of interest to NASA’s Quantum Artificial Intelligence Laboratory, the methods and concepts presented here apply to a broader family of hard discrete optimization problems that might also be present in many machine-learning algorithms.
Alejandro Perdomo-Ortiz is a Research Scientist at NASA Ames Research Center, Quantum Artificial Intelligence Laboratory, where he works in the design of quantum algorithms to solve hard optimization problems. Alejandro received a Ph.D. in Chemical Physics from Harvard University. He is a three-time winner of Harvard’s Certificate of Excellence in Teaching and a recipient of the Dudley R. Herschbach Teaching Award. He is originally from Cali, Colombia where he performed undergraduate studies in Chemistry at Universidad del Valle. Within the NASA team, he is interested in understanding the scalability and performance of quantum annealing algorithms and their realistic experimental implementations for broad applications in space exploration research.
Host: Prof. Milton Halem, Sorry, you need javascript to view this email address.
]]>
CHMPR Distinguished Lecture Series Programming and Tuning a Quantum Annealing Computer to Solve Real-World Applications Dr. Alejandro Perdomo-Ortiz Quantum Artificial Intelligence Laboratory...
http://www.csee.umbc.edu/2015/10/talk-programming-tuning-a-quantum-annealing-computer-to-solve-real-world-applications-2pm-1026-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/55241/guest@my.umbc.edu/7bd5131bc744854c1386ae894c5e613a/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 22 Oct 2015 23:02:18 -0400
Thu, 22 Oct 2015 23:02:18 -0400
talk: Online Learning for Cognitive Radios, Power Grids & Brain Imaging, 1pm 10/23
 The UMBC CSEE Seminar Series Presents
The UMBC CSEE Seminar Series Presents
Online Learning for Cognitive Radios,
Power Grids, and Brain Imaging
Dr. Seung-Jun Kim
Department of CSEE, UMBC
1-2pm, Friday, 23 October 2015, ITE 325b
With the advent of big data era with pervasive sensors and powerful computational intelligence techniques, application of data-driven techniques to various domains is becoming quite popular. In this talk, some of our recent research activities in the signal processing and smart systems lab (SPSS) will be sampled. In particular, it will be highlighted how the online learning techniques can benefit different applications in the wireless communication, power systems, and medical imaging areas.
Seung-Jun Kim received his B.S. and M.S. degrees from Seoul National University in Seoul, Korea, and his Ph.D. from the University of California at Santa Barbara in 2005, all in electrical engineering. From 2005 to 2008, he worked for NEC Laboratories America in Princeton, New Jersey. He was with the University of Minnesota during 2008-2014, where his final title was Research Associate Professor. In August 2014, he joined the CSEE department at UMBC. Dr. Kim’s research interests include statistical signal processing, optimization, and machine learning, with applications to wireless communication and networking, future power systems, and big data analytics.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks. Upcoming talks include the following.
Signature Track (Fridays, 12noon-1pm, in ITE 102):
- Oct. 30, Rong Chen, SOM Faculty, computational neuroscience
- Nov.13, John Kloetzli (Firaxis), computer graphics
- Weekly Track (Thursday 12noon-1pm, or Friday 1-2pm, in ITE 325):
- Nov. 20 Hamed Pirsiavash (UMBC), computer vision
- Nov. 6 Nilanjan Banerjee (UMBC), Internet of Things
- Dec. 4 Ting Zhu (UMBC), energy system and big data
Other UMBC CSEE Seminar Series: The UMBC Cyber Defense Lab (CDL) meets biweekly Fridays 11:15am-12:30pm in ITE 231, for research talks about cybersecurity.
]]>
The UMBC CSEE Seminar Series Presents Online Learning for Cognitive Radios, Power Grids, and Brain Imaging Dr. Seung-Jun Kim Department of CSEE, UMBC 1-2pm, Friday, 23 October 2015, ITE...
http://www.csee.umbc.edu/2015/10/talk-online-learning-for-cognitive-radios-power-grids-brain-imaging-1pm-1023/
https://dev.my.umbc.edu/api/v0/pixel/news/55201/guest@my.umbc.edu/0a1d2cb495320a3451a3ba995fdefd65/api/pixel
computer-engineering
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 21 Oct 2015 09:47:06 -0400
Wed, 21 Oct 2015 09:47:06 -0400
talk: Personal data at risk? App analytics to the rescue, 11:15 10/23

The UMBC Cyber Defense Lab presents
Are your personal data at risk?
App analytics to the rescue
Prajit Kumar Das
Ebiquity, CSEE Department, UMBC
11:15am-12:30pm, Friday, 23 October 2015, ITE 231
According to the prominent virus and malware tool Virustotal, the Google Play Store has a few thousand apps from major malware families. Given such a revelation, access control systems for mobile data management have reached a state of critical importance. We propose developing a system that will help us detect pathways along which user data are being stolen from their mobile devices. We use a multi-layered approach including app meta data analysis, understanding code patterns, and detecting and eventually controlling dynamic data flow when such an app is installed on a mobile device. In this presentation we focus on the first part of our work and discuss the merits and flaws of our unsupervised learning mechanism to detect possible malicious behavior from apps in the Google Play Store.
Prajit Das is a PhD student in computer science at UMBC.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Are your personal data at risk? App analytics to the rescue Prajit Kumar Das Ebiquity, CSEE Department, UMBC 11:15am-12:30pm, Friday, 23 October 2015,...
http://www.csee.umbc.edu/2015/10/talk-personal-data-at-risk-app-analytics-to-the-rescue-1115-1023/
https://dev.my.umbc.edu/api/v0/pixel/news/55196/guest@my.umbc.edu/edf0cc9df1f44fd8b20f4a501a4c437f/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Wed, 21 Oct 2015 09:01:16 -0400
Wed, 21 Oct 2015 09:01:16 -0400
talk: Enhanced IP and OpenFlow Switching to Provide Zero Touch Traffic Engineering, 12pm 10/16

The UMBC CSEE Seminar Series Presents
Enhanced IP and OpenFlow Switching to
Provide Zero Touch Traffic Engineering
Dr. William Chimiak
Laboratory for Telecommunications Science (LTS)
12noon-1pm, Friday, 16 October, 2015, ITE 102
I propose a method using OpenFlow and Enhanced IP (64 bit IPv4) to provide an end-to-end method of creating traffic engineered flow paths for big data. With an SSL registered Northbound Application, a user with proper credentials requests an big data transfer. This is sent to a port with a hybrid Enhanced IP NAT. The Enhanced IP portion of the NAT is stateless making communication-set up faster, but allows the normal Carrier-grade NAT function, if necessary. With this system, there will be a mechanism to allow end-to-end awareness of the flow type to allow for an end-to-end traffic engineered path.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
About the CSEE Seminar Series: The UMBC Department of Computer Science and Electrical Engineering presents technical talks on current significant research projects of broad interest to the Department and the research community. Each talk is free and open to the public. We welcome your feedback and suggestions for future talks. Upcoming talks include the following.
Signature Track (Fridays, 12noon-1pm, in ITE 102):
- Oct. 30, Rong Chen, SOM Faculty, computational neuroscience
- Nov.13, John Kloetzli (Firaxis), computer graphics
Weekly Track (Thursday 12noon-1pm, or Friday 1-2pm, in ITE 325):
- Nov. 20 Hamed Pirsiavash (UMBC), computer vision
- Nov. 6 Nilanjan Banerjee (UMBC), Internet of Things
- Dec. 4 Ting Zhu (UMBC), energy system and big data
Other UMBC CSEE Seminar Series: The UMBC Cyber Defense Lab (CDL) meets biweekly Fridays 11:15am-12:30pm in ITE 231, for research talks about cybersecurity. Next talk is 10-23.
]]>
The UMBC CSEE Seminar Series Presents Enhanced IP and OpenFlow Switching to Provide Zero Touch Traffic Engineering Dr. William Chimiak Laboratory for Telecommunications Science (LTS)...
http://www.csee.umbc.edu/2015/10/talk-enhanced-ip-and-openflow-switching-to-provide-zero-touch-traffic-engineering-12pm-1016/
https://dev.my.umbc.edu/api/v0/pixel/news/55063/guest@my.umbc.edu/e4a98e05d22ca74c85e4501c4711bc12/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 14 Oct 2015 18:27:14 -0400
Wed, 14 Oct 2015 18:27:14 -0400
talk: Grounded Language Acquisition: A Physical Agent Approach, Fri 10/9

The UMBC CSEE Seminar Series Presents
Grounded Language Acquisition: A Physical Agent Approach
12:00-1:00pm Friday, 9 Oct. 2015, ITE 325b
A critical component of understanding human language is the ability to map words and ideas in that language to aspects of the external world. This mapping, called the symbol grounding problem, has been studied since the early days of artificial intelligence; however, advances in language processing, sensory, and motor systems have only recently made it possible to directly interact with tangibly grounded concepts. In this talk, I describe how we combine robotics and natural language processing to acquire and use physically grounded language specifically, how robots can learn to follow instructions, understand descriptions of objects, and build models of language and the physical world from interactions with users. I will describe our work on building a learning system that can ground English commands and descriptions from examples, making it possible for robots to learn from untrained end-users in an intuitive, natural way, and describe applications of our work in following directions and learning about objects. Finally, I will discuss how robots with these learning capabilities address a number of near-term challenges.
Cynthia Matuszek is an Assistant Professor at the University of Maryland, Baltimore County’s Computer Science and Electrical Engineering department. She completed her Ph.D. at the University of Washington in 2014, where she was a member of both the Robotics and State Estimation lab and the Language, Interaction, and Learning group. She is published in the areas of artificial intelligence, robotics, ubiquitous computing, and human-robot interaction. Her research interests include human-robot interaction, natural language processing, and machine learning.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
· directions and more information ·
]]>
The UMBC CSEE Seminar Series Presents Grounded Language Acquisition: A Physical Agent Approach Dr. Cynthia Matuszek Interactive Robotics and Language Lab Computer Science and Electrical...
http://www.csee.umbc.edu/2015/10/talk-grounded-language-acquisition-a-physical-agent-approach-fri-109/
https://dev.my.umbc.edu/api/v0/pixel/news/54796/guest@my.umbc.edu/d8183ff12798fcdf58a70e0fb0bf8d7a/api/pixel
ai
computer-science
news
research
robotics
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 06 Oct 2015 10:53:04 -0400
Tue, 06 Oct 2015 10:53:04 -0400
talk: Hack, Play, Win: Lessons Learned Running The Maryland Cyber Challenge, 10/9

The UMBC Cyber Defense Lab presents
Hack, Play, Win: Lessons Learned Running
The Maryland Cyber Challenge
11:15am-12:30pm, Friday, 9 Oct 2015, ITE 231
An oft-cited and prominent concern facing the Internet security community is the need to identify and hire qualified cybersecurity practitioners able to fill critical technical, analytical, and managerial positions within the global technology workforce. A 2014 report from the Education Advisory Board discusses the “exploding” demand for qualified cybersecurity practitioners, noting that cybersecurity jobs grew by 73% between 2007-2012 compared to 6% in all other industry sectors. Similarly, Burning Glass, a national employment research firm, notes that there are nearly 23,000 available cybersecurity positions in the Washington, DC metropolitan area. Nowhere is this need more evident, or discussed more frequently, than in Maryland, a region some dub the ‘epicenter of cybersecurity’ education, research, and industry.
In response to this concern, events in the cybersecurity discipline, known as cyber competitions” or “cyber challenges” seek to motivate and encourage high school and college students toward careers in cybersecurity by developing their technical and teamwork skills while also allowing more experienced cybersecurity professionals an opportunity to practice their expertise in a challenging venue for professional recognition. The popularity and number of these events as a form of intellectual competition at industry security conferences like the DEFCON CTF or Department of Defense DC3 Digital Forensics Challenge and those within educational communities such as the National Cyber League (NCL), CyberPatriot, or the Collegiate CyberDefense Competition (CCDC) are but a few examples of prominent cyber challenges drawing worldwide participation. Other competitions, both large and small, are under continual development, as is a National Science Foundation-backed effort to create a national federation to support and standardize the rules, activities, and conduct of cyber competitions.
Given the popularity of these events, and the ongoing global desire to launch new ones, this talk will draw upon the experiences of organizing and coordinating the Maryland Cyber Challenge (MDC3) from 2011-2014 in offering advice to current and future cyber competition planners. What lessons from current competitions can help future competition organizers run successful challenges of their own? And are such events enough to prepare the next generation of cybersecurity professional? While no event will ever run perfectly, organizers must always strive to “get it right” – or as close to “right” as possible!
(This talk previews a paper accepted for publication in the December 2015 USENIX ;login;)
Dr. Richard Forno directs the University of Maryland, Baltimore County’s Graduate Cybersecurity Program, serves as the Assistant Director of UMBC’s Center for Cybersecurity, and is a Junior Affiliate Scholar at the Stanford Law School’s Center for Internet and Society (CIS). His twenty-year career spans the government, military, and private sector, including helping build a formal cybersecurity program for the US House of Representatives, serving as the first Chief Security Officer for the InterNIC, and co-founding the Maryland Cyber Challenge. Richard was also one of the early researchers on the subject of “information warfare” and he remains a longtime commentator on the influence of Internet technology upon society.
Host: Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
The UMBC Cyber Defense Lab presents Hack, Play, Win: Lessons Learned Running The Maryland Cyber Challenge Richard Forno, UMBC 11:15am-12:30pm, Friday, 9 Oct 2015, ITE 231 An oft-cited and...
http://www.csee.umbc.edu/2015/10/talk-hack-play-win-lessons-learned-running-the-maryland-cyber-challenge-109/
https://dev.my.umbc.edu/api/v0/pixel/news/54745/guest@my.umbc.edu/1c8b3c735d6b30e024a9a55fc0e464f8/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 05 Oct 2015 08:29:08 -0400
Mon, 05 Oct 2015 08:29:08 -0400
talk: Capturing Brain Activity at Rest, Noon Fri 10/2
The UMBC CSEE Seminar Series Presents
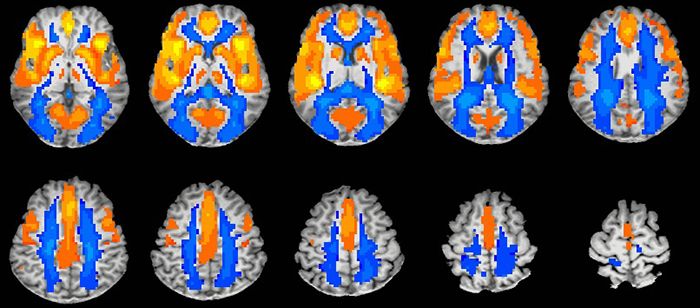
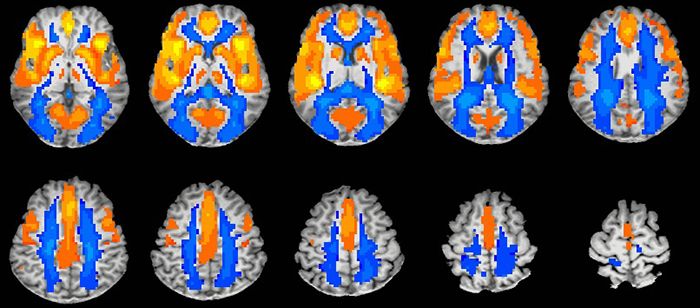
Capturing Brain Activity at Rest: Recent Development of Resting-State Functional MRI and Its Potential in Clinical Applications
Dr. Yihong Yang
Neuroimaging Research Branch
National Institute on Drug Abuse, NIH
12noon-1pm Friday, 2 Oct. 2015, ITE 102
There has been growing interest in the intrinsic brain activity at “rest” that may be used to reveal circuit-level information of brain functions. Alterations of resting-state brain activity have been implicated in various neurological and psychiatric disorders. In this seminar, the recent development of resting-state fMRI techniques will be introduced and discussed. Applications of these new imaging techniques in clinical applications such as cocaine addiction and traumatic brain injury will be demonstrated.
Dr. Yihong Yang received his Ph.D. in Biophysics, 1995, at University of Illinois at Urbana-Champaign, under Paul C. Lauterbur who share 2003 Physiology or Medicine Nobel price with Peter Mansfield on the development of MRI. He is currently a senior investigator and the chief of MR Imaging and Spectroscopy Section at NIDA. Dr. Yang has made significant contributions to the development of MRI methodology and application of neuroimaging techniques to neurological and psychiatric disorders. He has published over 130 original research papers in leading journals and contributed several book chapters in the fields of functional MRI, diffusion tensor imaging and MR spectroscopy, as well as applications of MRI technology to the assessment of brain disorders, particularly in drug addiction. He has served on many NIH Study Sections and other research foundations including Medical Research Council (UK), Alzheimer’s Association, and National Science Foundation of China (NSFC). He is an editorial board member of the Brain Connectivity and Open Neuroimaging Journal. He has trained many post-doctoral and pre-postdoctoral fellows in neuroimaging.
Hosts: Professors Fow-Sen Choa (Sorry, you need javascript to view this email address. ) and Alan T. Sherman (Sorry, you need javascript to view this email address. )
]]>
The UMBC CSEE Seminar Series Presents Capturing Brain Activity at Rest: Recent Development of Resting-State Functional MRI and Its Potential in Clinical Applications Dr. Yihong Yang...
http://www.csee.umbc.edu/2015/09/talk-capturing-brain-activity-at-rest-noon-fri-102/
https://dev.my.umbc.edu/api/v0/pixel/news/54560/guest@my.umbc.edu/f03a4fde4f2cfad3fdfde4beebb666a0/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 28 Sep 2015 16:52:59 -0400
Mon, 28 Sep 2015 16:52:59 -0400
talk: Inter-Disciplinary Research between Computer Science, Creativity and the Arts, 2pm 10/2

Appropriately Valuing Inter-Disciplinary Research
between Computer Science, Creativity and the Arts
Professor Celine Latulipe
Software and Information Systems
University of North Carolina at Charlotte
2:00pm Friday 2 October 2015, PAHB 132
Scientists and technologists conducting research in creativity and engaging with artists face political pressure to justify their work. A case study of the NSF-funded Dance.Draw project is used to illustrate the problematic aspects of pressure. I argue that a shift in dialogue is needed to appropriately value this type of inter-disciplinary research.
Dr. Celine Latulipe is an Associate Professor in the Department of Software and Information Systems in the College of Computing and Informatics at the University of North Carolina at Charlotte. Her research involves developing and evaluating novel interaction techniques, creativity and collaboration support tools and technologies to support the arts, and developing innovation computer science curriculum design patterns. Dr. Latulipe examines issues of how to support expression and exploration in complex interfaces and how interaction affordances impact satisficing behavior. She also conducts research into how to make computer science education a more social experience, both as a way of more deeply engaging students and as an approach to broadening participation in a field that lacks gender and racial diversity.
]]>
Appropriately Valuing Inter-Disciplinary Research between Computer Science, Creativity and the Arts Professor Celine Latulipe Software and Information Systems University of North Carolina at...
http://www.csee.umbc.edu/2015/09/talk-inter-disciplinary-research-between-computer-science-creativity-and-the-arts-2pm-102/
https://dev.my.umbc.edu/api/v0/pixel/news/54576/guest@my.umbc.edu/d91b3dd3feeaa02bc96947d90baa86bf/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 28 Sep 2015 16:00:37 -0400
talk: Sharon Gannot, Multi-Microphone Speech Enhancement, 10/14

Multi-Microphone Speech Enhancement
Sharon Gannot
Bar-Ilan University, Israel
1:30pm Wednesday, 14 October 2015, ITE 325B, UMBC
Microphone array algorithms emerged in the early 1990s as viable solutions to speech processing problems. However, the adaptation of beamforming methods to speech processing is still an open issue. There are many difficulties which arise from the characteristics of the speech signal and the acoustic environment. The speech signal is a wide-band and non-stationary signal. Very long room impulse responses (RIRs), which are several thousands of taps long, may be attributed to multiple reflections of the sound source on objects in the enclosure. Moreover, due to the inevitable movements of both sources (speakers) and receivers (microphones), the room impulse responses become time-varying.
In this talk, we will focus on spatial processors, a.k.a, beamformers, based on the linearly constrained minimum variance (LCMV) criterion, and its special case, the minimum variance distortionless (MVDR) beamformer. We show that classical beamformers that merely take into account angular information (as reflected by the so-called beam-pattern), are too simplistic to fully address the intricate propagation regime of the sound source in reverberant environment. We will therefore reformulate the LCMV beamformer in the shorttime Fourier transform (STFT) domain and substitute the free-field steering vector by the entire acoustic transfer function (ATF). The corresponding relative transfer function (RTF) will be then introduced, and its applicability to the design of beamformers in reverberant environments will be discussed. We will then elaborate on several blind RTF estimation techniques, e.g. based on subspace analysis, that enable the implementation of all necessary beamformer’s blocks. Several applications of the powerful LCMV beamformer, e.g. speech enhancement, extraction of desired speakers in multiple competing speaker environment, and binaural processing, will then be presented.
We will conclude the talk with an overview of the emerging field of distributed algorithms for ad hoc microphone arrays, and discuss the advantages and challenges they raise. The presentation will be accompanied by audio clips demonstrating the capabilities of the introduced schemes.
Sharon Gannot received his B.Sc. degree (summa cum laude) from the Technion-Israel Institute of Technology, Haifa, Israel in 1986 and the M.Sc. (cum laude) and Ph.D. degrees from Tel-Aviv University, Israel in 1995 and 2000 respectively, all in Electrical Engineering. In 2001 he held a post-doctoral position at the department of Electrical Engineering (ESAT-SISTA) at K.U.Leuven, Belgium. In 2002-2003 he held a research and teaching position at the Faculty of Electrical Engineering, Technion-Israel Institute of Technology, Haifa, Israel. Currently, he is a Full Professor at the Faculty of Engineering, Bar-Ilan University, Israel, where he is heading the Speech and Signal Processing laboratory and the Signal Processing Track. Prof. Gannot is the recipient of Bar-Ilan University outstanding lecturer award for 2010 and 2014. Prof. Gannot has served as an Associate Editor of the EURASIP Journal of Advances in Signal Processing in 2003-2012, and as an Editor of several special issues on Multi-microphone Speech Processing of the same journal. He has also served as a Guest Editor of ELSEVIER Speech Communication and Signal Processing journals. Prof. Gannot has served as an Associate Editor of IEEE Transactions on Speech, Audio and Language Processing in 2009-2013. Currently, he is a Senior Area Chair of the same journal. He also serves as a reviewer of many IEEE journals and conferences. Prof. Gannot is a member of the Audio and Acoustic Signal Processing (AASP) technical committee of the IEEE since Jan., 2010. He is also a member of the Technical and Steering committee of the International Workshop on Acoustic Signal Enhancement (IWAENC) since 2005. He was the general co-chair of IWAENC held at Tel-Aviv, Israel in August 2010. Prof. Gannot has served as the general co-chair of the IEEE Workshop on Applications of Signal Processing to Audio and Acoustics (WASPAA), New-Paltz, NY, USA in October 2013. Prof. Gannot was selected (with colleagues) to present a tutorial sessions in ICASSP 2012, EUSIPCO 2012, ICASSP 2013 and EUSIPCO 2013. His research interests include multi-microphone speech processing and specifically distributed algorithms for ad hoc microphone arrays for noise reduction and speaker separation; machine learning methods in speech processing; dereverberation; single microphone speech enhancement and speaker localization and tracking.
]]>
Multi-Microphone Speech Enhancement Sharon Gannot Bar-Ilan University, Israel 1:30pm Wednesday, 14 October 2015, ITE 325B, UMBC Microphone array algorithms emerged in the early 1990s as...
http://www.csee.umbc.edu/2015/09/talk-sharon-gannot-multi-microphone-speech-enhancement-1014/
https://dev.my.umbc.edu/api/v0/pixel/news/54463/guest@my.umbc.edu/35fd3f067993917b6a27898982d394ff/api/pixel
computer-engineering
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 24 Sep 2015 23:17:08 -0400
Proposal: Vatcher, Verifiable Randomness and its Applications, 10:30 9/24

Ph.D. Dissertation Proposal
Verifiable Randomness and its Applications
Christopher Vatcher
10:30am Thursday, 24 September 2015, ITE 325b
We propose to create a public verifiable randomness beacon, to integrate with the Random-Sample Voting system, constructed to be secure against adversaries who have even almost complete control over the system’s source of public randomness including the entropy source.
By verifiable randomness, we do not mean we can prove a sequence of bits to be random. Instead, verifiability means it is possible to prove: (a) a consumer used uniform bits originating from a specific entropy source and therefore cannot lie about the bits used; and (b) the bits used were unpredictable prior to their generation and, with overwhelming probability, were free of adversarial influence. This is in contrast to ordinary public randomness where parties must agree to trust some randomness provider, who becomes a target of corruption. Verifiable randomness is an enhancement of public randomness used to perform random selection in voting, conduct random audits, preserve privacy, generate random challenges for secure multi-party computation, and public lottery draws. Random-Sample Voting specifically requires verifiable randomness for random voter selection and random audits.
Our work extends the work of Eastlake and Clark and Hengartner by considering (a) adversaries who have fine control over the entropy source and (b) physical entropy sources, which we can make verifiable.
Our specific aims include (a) creating adversary models for three entropy source abstractions based on trusted providers, sensor networks, and distributed proof-of-work systems; (b) create a verifiable random beacon that integrates each model; (c) integrate our work with the Random-Sample Voting system; and (d) integrate with NIST’s beacon and propose a verifiable randomness standard based on our work.
Our method is to weaken the trust assumption on the entropy source by introducing verifiable entropy sources, which have mechanisms for limiting adversarial influence and accumulating evidence that their outputs obey a known distribution. Combined with an appropriate randomness extractor, we can generate verifiable random bits. Using sources like weather, we will construct a verifiable randomness beacon: a public randomness provider unencumbered by generous and often unfounded trust assumptions. Such a beacon can serve as a singular gateway for accessing and aggregating multiple entropy sources without compromising the randomness provided to consumers.
Committee: Drs. Alan T. Sherman (Chair), Konstantinos Kalpakis, Weining Kang (Math/Stat), David Chaum (Random-Sample Voting), Aggelos Kiayias (University of Athens)
]]>
Ph.D. Dissertation Proposal Verifiable Randomness and its Applications Christopher Vatcher 10:30am Thursday, 24 September 2015, ITE 325b We propose to create a public verifiable randomness...
http://www.csee.umbc.edu/2015/09/proposal-vatcher-verifiable-randomness-and-its-applications-1030-924/
https://dev.my.umbc.edu/api/v0/pixel/news/54373/guest@my.umbc.edu/001d44f1c767a22080f20c47b6f79b47/api/pixel
computer-science
cybersecurity
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 21 Sep 2015 22:41:38 -0400

 The UMBC CSEE Seminar Series Presents
The UMBC CSEE Seminar Series Presents