Two technical talks by Amazon senior staff, 4-6:30pm Tue 3/3

Senior Amazon staff members will give two technical talks on next week on Tuesday, March 3, in the UC Ballroom on topics of great practical interest and utility.
- Lydia Fitzpatrick, Senior Technical Program Manager for Amazon Mobile Business will give a talk on “Web Performance Optimization” from 4:00pm to 5:00pm.
- Leo Zhadanovsky, Senior Solutions Architect for Amazon Web Services will present an “Introduction to Amazon Web Services (AWS)” from 5:30pm to 6:30pm. The talk with introduce cloud computing and discuss the various Networking, Compute, Database, Storage, Application, Deployment and Management services that AWS offers. It will demonstrate how to launch a full three tier LAMP stack in minutes, as well as how to setup a simple web server on AWS. The presentation will also discuss several use-cases, demonstrating how customers such as Enterprises, Startups, and Government Agencies are using AWS to power their computing needs.
The talks will be preceded and followed by an open networking opportunity with Amazon Human Resource representatives. Amazon is interested in students for internships and full-time position who are majoring in Information Systems, Business Technology Administration, Computer Engineering, Computer Science, and Cybersecurity.
]]>
Senior Amazon staff members will give two technical talks on next week on Tuesday, March 3, in the UC Ballroom on topics of great practical interest and utility. Lydia Fitzpatrick, Senior...
https://www.csee.umbc.edu/2015/02/two-technical-talks-by-amazon-senior-staff-4-630pm-tue-33/
https://dev.my.umbc.edu/api/v0/pixel/news/57827/guest@my.umbc.edu/3776d28932e34e0a6d4633f2acd8f325/api/pixel
computer-engineering
computer-science
cybersecurity
jobs
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 26 Feb 2015 13:38:49 -0500
PhD proposal: User Identification in Wireless Networks

Ph.D. Dissertation Proposal
User Identification in Wireless Networks
Christopher Swartz
9:00-11:00pm Friday, 27 February 2015, ITE 325B
Wireless communication using the 802.11 specifications is almost ubiquitous in daily life through an increasing variety of platforms. Traditional identification and authentication mechanisms employed for wireless communication commonly mimic physically connected devices and do not account for the broadcast nature of the medium. Both stationary and mobile devices that users interact with are regularly authenticated using a passphrase, pre-shared key, or an authentication server. Current research requires unfettered access to the user’s platform or information that is not normally volunteered.
We propose a mechanism to verify and validate the identity of 802.11 device users by applying machine learning algorithms. Existing work substantiates the application of machine learning for device identification using Commercial Off-The-Shelf (COTS) hardware and algorithms. This research seeks the refinement of and investigation of features relevant to identifying users. The approach is segmented into three main areas: a data ingest platform, processing, and classification.
Initial research proved that we can properly classify target devices with high precision, recall, and ROC using a sufficiently large real-world data set and a limited set of features. The primary contribution of this work is exploring the development of user identification through data observation. A combination of identifying new features, creating an online system, and limiting user interaction is the objective. We will create a prototype system and test the effectiveness and accuracy of it’s ability to properly identify users.
Committee: Drs. Joshi (Chair/Advisor), Nicholas, Younis, Finin, Pearce, Banerjee
]]>
Ph.D. Dissertation Proposal User Identification in Wireless Networks Christopher Swartz 9:00-11:00pm Friday, 27 February 2015, ITE 325B Wireless communication using the 802.11...
http://www.csee.umbc.edu/2015/02/phd-proposal-user-identification-in-wireless-networks/
https://dev.my.umbc.edu/api/v0/pixel/news/50071/guest@my.umbc.edu/2874842c26c3b90ffe4f8576dc501105/api/pixel
computer-science
cybersecurity
graduate
news
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 24 Feb 2015 23:57:02 -0500
talk: Visual understanding of human actions, 12-1 Fri 2/27, ITE325b
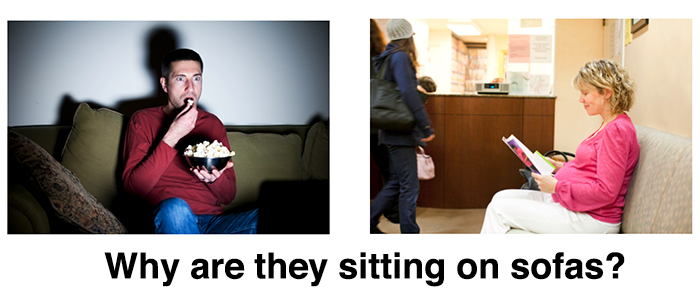
Visual understanding of human actions
Postdoctoral Research Associate
Computer Science and Artificial Intelligence Laboratory
Massachusetts Institute of Technology
12:00-1:00pm Friday, 27 February, 2015, ITE 325B
The aim in computer vision is to develop algorithms for computers to “see” the world as humans do. Central to this goal is understanding human behavior as an intelligent agent functioning in the visual world. For instance, in order for a robot to interact with us, it should understand our actions to produce the proper response. My work explores several directions towards computationally representing and understanding human actions.
In this talk, I will focus on detecting actions and judging their quality. First, I will describe simple grammars for modeling long-scale temporal structure in human actions. Real-world videos are typically composed of multiple action instances, where each instance is itself composed of sub-actions with variable durations and orderings. Our grammar models capture such hierarchical structure while admitting efficient, linear-time parsing algorithms for action detection. The second part of the talk will describe our algorithms for going beyond detecting actions to judging how well they are performed. Our learning-based framework provides feedback to the performer to improve the quality of his/her actions.
Host: Mohamed Younis
]]>
Visual understanding of human actions Dr. Hamed Pirsiavash Postdoctoral Research Associate Computer Science and Artificial Intelligence Laboratory Massachusetts Institute of Technology...
http://www.csee.umbc.edu/2015/02/talk-visual-understanding-of-human-actions-12-1-fri-227-ite325b/
https://dev.my.umbc.edu/api/v0/pixel/news/50040/guest@my.umbc.edu/dd5212df222c3b097fd06425b0a6134b/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 23 Feb 2015 14:30:42 -0500
Mon, 23 Feb 2015 14:30:42 -0500
PhD proposal: Scalable Storage System for Big Scientific Data

Ph.D. Dissertation Proposal
MLVFS: A Scalable Storage System For Managing Big Scientific Data
Navid Golpayegani
3:00-5:00pm Tuesday 24 February 2015, ITE 346
Managing peta or exabytes of data with hundreds of millions to billions of files is a necessary first step towards an effective big data computing and collaboration environment for distributed systems. Current file system designs have focused on providing better and faster data distribution. Managing the directory structure for data discovery becomes an essential element of the scalability problems for big data systems. Recent designs are addressing the challenge of exponential growth of files. Still largely unexplored is the research for dealing with the organizational aspect of managing big data systems with hundreds of millions of files. Most file systems organize data into static directory structures making data discovery, when dealing with large data sets, hard and slow.
This thesis will propose a unique Multiview Lightweight Virtual File System (MLVFS) design to primarily deal with the data organizational management problem in big data file systems. MLVFS is capable of the dynamic generation of directory structures to create multiple views of the same data set. With multiple views, the storage system is capable of organizing available data sets by differing criteria such as location or date without the need to replicate data or use symbolic links. In ad- dition, MLVFS addresses scalability issues associated with the growth of the stored files by removing the internal metadata system and replacing it with generally avail- able external metadata information (i.e. data base servers, project compute servers, remote repositories, etc.). This thesis, moreover, proposes to add, plug in capabilities not normally found in file systems that make this system highly flexible, in terms of specifying sources of meta data information, dynamic file format streaming and other file handling features.
The performance of MLVFS will be tested in both simulated environments as well as real world environments. MLVFS will be installed on the BlueWave cluster at UMBC for simulated load testing to measure the performance for various loads. Simultaneously, stable version of MLVFS will run in real world production environ- ments such as those of the NASA MODIS instrument processing system (MODAPS). The MODAPS system will be used to show examples of real world use cases for MLVFS. Additionally, there will be other systems explored for the real world use of MLVFS, such as at NIST for research into Biomedical Image Stitching.
Committee: Drs. Milton Halem (Chair, Advisor), Yelena Yesha, Charles Nicholas, John Dorband, Daniel Duffy
]]>
Ph.D. Dissertation Proposal MLVFS: A Scalable Storage System For Managing Big Scientific Data Navid Golpayegani 3:00-5:00pm Tuesday 24 February 2015, ITE 346 Managing peta or exabytes of...
http://www.csee.umbc.edu/2015/02/phd-proposal-scalable-storage-system-for-big-scientific-data/
https://dev.my.umbc.edu/api/v0/pixel/news/50003/guest@my.umbc.edu/d043fa58cc738e4724c939a53a5dc4a9/api/pixel
computer-science
defense
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 20 Feb 2015 17:24:21 -0500
talk: Understanding Social Spammers, Noon Tue 2/24, ITE325

Understanding Social Spammers: A Data Mining Perspective
Xia “Ben” Hu
Computer Science and Engineering
Arizona State University
12:00-1:00 Tuesday, 24 February 2015
With the growing popularity of social media, social spamming has become rampant on all platforms. Many (fake) accounts, known as social spammers, are employed to overwhelm legitimate users with unwanted information. Social spammers are unique due to their coordinated efforts to launch attacks such as distributing ads to generate sales, disseminating pornography and viruses, executing phishing attacks, or simply sabotaging a system’s reputation. In this talk, I will introduce a novel and systematic analysis of social spammers from a data mining perspective to tackle the challenges raised by social media data for spammer detection. Specifically, I will formally define the problem of social spammer detection and discuss the unique properties of social media data that make this problem challenging. By analyzing the two most important types of information, network and content information, I will introduce a unified framework by collectively using heterogeneous information in social media. To tackle the labeling bottleneck in social media, I will show how we can take advantage of the existing information about spam in email, SMS, and on the web for spammer detection in microblogging. I will also present a solution for efficient online processing to handle fast-evolving social spammers.
Xia Hu is a Ph.D. candidate in Computer Science and Engineering at Arizona State University, supervised by Professor Huan Liu. His research interests include data mining, machine learning, social network analysis, etc. As a result of his research work, he has published nearly 40 papers in several major academic venues, including WWW, SIGIR, KDD, WSDM, IJCAI, AAAI, CIKM, SDM, etc. One of his papers was selected for the Best Paper Shortlist in WSDM’13. He is the recipient of IEEE “Atluri Award” Scholarship, 2014 ASU’s President’s Award for Innovation, and Faculty Emeriti Fellowship. He has served on program committees for several major conferences such as WWW, IJCAI, SDM and ICWSM, and reviewed for multiple journals, including IEEE TKDE, ACM TOIS and Neurocomputing. His research attracts wide range of external government and industry sponsors, including NSF, ONR, AFOSR, Yahoo!, and Microsoft.
– more information and directions: http://bit.ly/UMBCtalks –
]]>
Understanding Social Spammers: A Data Mining Perspective Xia “Ben” Hu Computer Science and Engineering Arizona State University 12:00-1:00 Tuesday, 24 February 2015 With the growing...
http://www.csee.umbc.edu/2015/02/talk-understanding-social-spammers-noon-tue-224-ite325/
https://dev.my.umbc.edu/api/v0/pixel/news/49897/guest@my.umbc.edu/915e3a6ffbee6773435d003c20e6618b/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Tue, 17 Feb 2015 10:53:10 -0500
talk: Topic Modeling with Structured Priors for Text-Driven Science
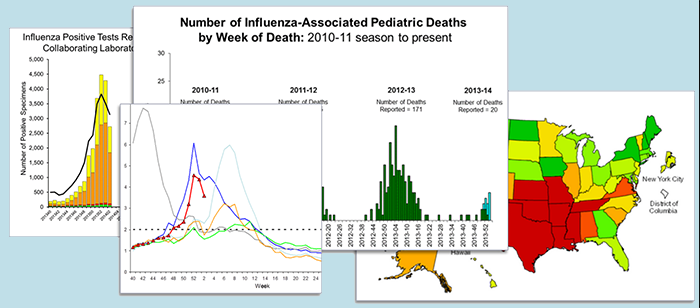
Topic Modeling with Structured Priors for Text-Driven Science
Michael Paul, JHU
12:00pm – 1:00pm, Monday, 2 March 2015, ITE 325
Many scientific disciplines are being revolutionized by the explosion of public data on the web and social media, particularly in health and social sciences. For instance, by analyzing social media messages, we can instantly measure public opinion, understand population behaviors, and monitor events such as disease outbreaks and natural disasters. Taking advantage of these data sources requires tools that can make sense of massive amounts of unstructured and unlabeled text. Topic models, statistical models that describe low-dimensional representations of data, can uncover interesting latent structure in large text datasets and are popular tools for automatically identifying prominent themes in text. However, to be useful in scientific analyses, topic models must learn interpretable patterns that accurately correspond to real-world concepts of interest.
In this talk, I will introduce Sprite, a family of topic models that can encode additional structures such as hierarchies, factorizations, and correlations, and can incorporate supervision and domain knowledge. Sprite extends standard topic models by formulating the Bayesian priors over parameters as functions of underlying components, which can be constrained in various ways to induce different structures. This creates a unifying representation that generalizes several existing topic models, while creating a powerful framework for building new models. I will describe a few specific instantiations of Sprite and show how these models can be used in various scientific applications, including extracting self-reported information about drugs from web forums, analyzing healthcare quality in online reviews, and summarizing public opinion in social media on issues such as gun control.
Michael Paul is a PhD candidate in Computer Science at Johns Hopkins University. He earned an M.S.E. in CS from Johns Hopkins University in 2012 and a B.S. in CS from the University of Illinois at Urbana-Champaign in 2009. He has received PhD fellowships from Microsoft Research, the National Science Foundation, and the Johns Hopkins University Whiting School of Engineering. His research focuses on exploratory machine learning and natural language processing for the web and social media, with applications to computational epidemiology and public health informatics.
– more information and directions: http://bit.ly/UMBCtalks –
]]>
Topic Modeling with Structured Priors for Text-Driven Science Michael Paul, JHU 12:00pm – 1:00pm, Monday, 2 March 2015, ITE 325 Many scientific disciplines are being revolutionized by the...
http://www.csee.umbc.edu/2015/02/talk-topic-modeling-with-structured-priors-for-text-driven-science/
https://dev.my.umbc.edu/api/v0/pixel/news/49894/guest@my.umbc.edu/0e6532abeb414f007bf9a5e471c9d870/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 17 Feb 2015 08:57:22 -0500
Fri, 27 Feb 2015 08:57:22 -0500
talk: Labrou on Studying Internet Latency via TCP Queries to DNS, 1:30pm Fri 2/27
ACM Tech Talk
Studying Internet Latency via TCP Queries to DNS
Dr. Yannis Labrou
Principal Data Architect, Verisign
1:30-2:30pm Friday, 27 February 2015, ITE 456, UMBC
Every day Verisign processes upwards of 100 billion authoritative DNS requests for .COM and .NET from all corners of the earth. The vast majority of these requests are via the UDP protocol. Because UDP is connectionless, it is impossible to passively estimate the latency of the UDP-based requests. A very small percentage of these requests though, are over TCP, thus providing the means to estimate the latency of specific requests and paths for a subset of the hosts that interact with Verisign’s network infrastructure.
In this work, we combine this relatively small number of datapoints from TCP (on the order of a few hundred million per day) with the much larger dataset of all DNS requests. Our focus is the process of data analysis of real world, imperfect data at very large scale with the goals of understanding network latency at an unprecedented magnitude, identifying large volume, high latency clients and improving their latency. We discuss the techniques we used for data selection and analysis and we present the results of a variety of analyses, such as deriving regional and country patterns, estimations for query latency for different countries and network locations, and techniques for identifying high latency clients.
It is important to note that latency results we will report are based on passive measurements from, essentially, the entire Internet. For this experiment we do not have control over the client side — where they are, which software, their configuration, their network congestion. This is significantly different from latency studied in any active measurement infrastructure such as Planet Lab, RIPE Atlas, Thousand Eyes, Catchpoint, etc.
Dr. Yannis Labrou is Principal Data Architect at Verisign Labs where he leads efforts to create value from the wealth of data that Verisign’s operations generate every day. He brings to Verisign 20 years of experience in conceiving, creating and bringing to fruition innovations; combining thinking big with laboring through the pains of materializing ideas. He has done so in an academic environment, at a startup company, while conducting government and DoD/DARPA sponsored research and for a global Fortune 200 company.
Before joining Verisign, Dr. Labrou was a Senior Researcher at Fujitsu Laboratories of America, Director of Technology and member of the executive staff of PowerMarket, an enterprise application software start-up company and a Research Assistant Professor at UMBC. He received his Ph.D. in Computer Science from UMBC, where his research focused on software agents, and a Diploma in Physics from the University of Athens, Greece. He has authored more than 40 peer-reviewed publications, with almost 4000 citations and he has been awarded 14 patents from the USPTO. His current research focus is data through the entire lifecycle from generation to monetization.
– more information and directions: http://bit.ly/UMBCtalks –
]]>
ACM Tech Talk Studying Internet Latency via TCP Queries to DNS Dr. Yannis Labrou Principal Data Architect, Verisign 1:30-2:30pm Friday, 27 February 2015, ITE 456, UMBC Every day Verisign...
http://www.csee.umbc.edu/2015/02/talk-labrou-on-studying-internet-latency-via-tcp-queries-to-dns-130pm-fri-227/
https://dev.my.umbc.edu/api/v0/pixel/news/49746/guest@my.umbc.edu/1cba413fd687fb38dd3a4de0c40f472a/api/pixel
alumni
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 11 Feb 2015 09:01:19 -0500
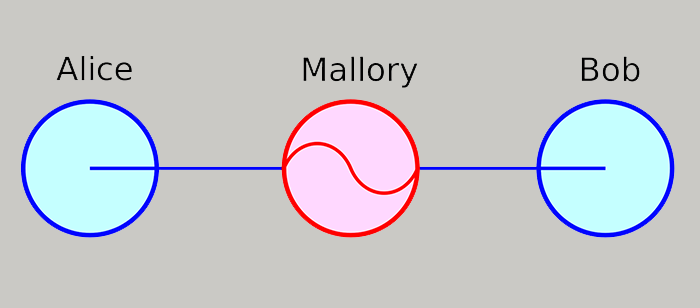
talk: Chaum’s Protocol for Detecting Man-in-the-Middle, 12pm Fri 1/30
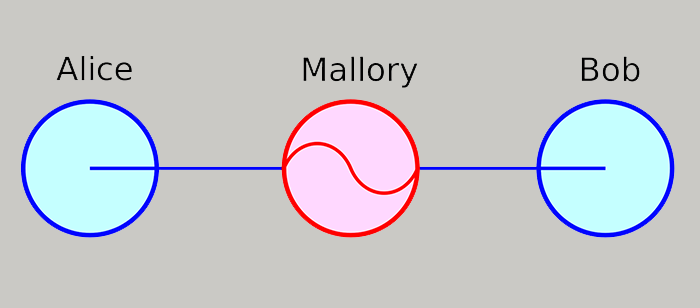
Chaum’s Protocol for Detecting Man-in-the-Middle: Explanation,
Demonstration, and Timing Studies for a Text-Messaging Scenario
12-1pm Friday, 30 January 2015, ITE 228, UMBC
We explain, demonstrate, and evaluate Chaum’s 2006 protocol for detecting a Man-in-the-Middle (MitM) of text-messaging network communications. MitM attacks pose serious risks to many network communications. Networks often mitigate these risks with robust protocols, such as TLS, which assume some type of public-key infrastructure that provides a mechanism for the authenticated exchange of public keys. By contrast, Chaum’s protocol aims to detect a MitM with minimal assumptions and technology, and in particular without assuming the authenticated exchange of public keys.
Joint work with John Seymour and Akshahraj Kore
]]>
Chaum’s Protocol for Detecting Man-in-the-Middle: Explanation, Demonstration, and Timing Studies for a Text-Messaging Scenario Prof. Alan T. Sherman UMBC Cyber Defense Lab 12-1pm Friday, 30...
http://www.csee.umbc.edu/2015/01/talk-chaums-protocol-for-detecting-man-in-the-middle-12pm-fri-130/
https://dev.my.umbc.edu/api/v0/pixel/news/49408/guest@my.umbc.edu/c5aa5fee422e5b5e26a5a33d05501153/api/pixel
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 28 Jan 2015 09:23:06 -0500
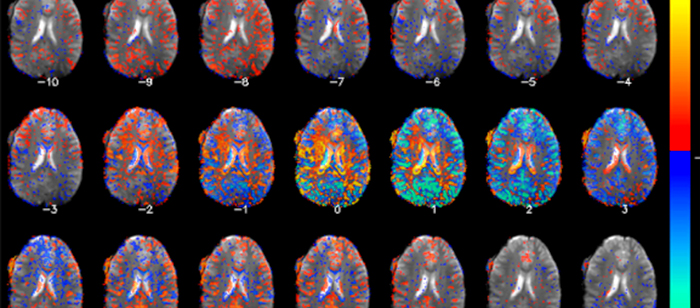
Phd proposal: Zhang on Brain Network Visualization Techniques
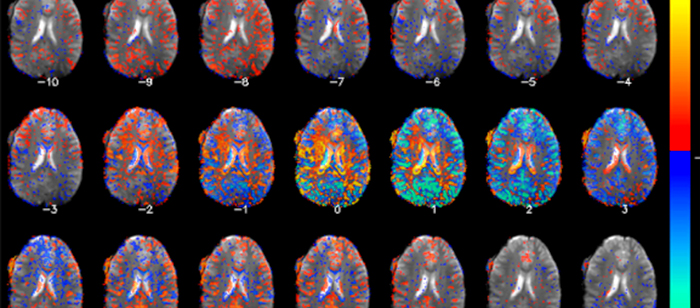
PhD Dissertation Proposal
Design and Validation of Brain Network
Visualization Techniques: A Unified Approach
Guohao Zhang
Time and Place:
8:00-10:00am, 22 Jan 22 2015, ITE325
We propose a unified approach to understand why and how visualization works, motivated by scientists’ difficulties in obtaining insights from increasingly complex data that involves multi-modality brain networks from structural and functional magnetic resonance imaging (dMRI and fMRI). Brain scientists are in need of visualization approaches to effectively analysis brain MRI data from different modalities. We design a unified theory expanded upon the classical 2D semiotics for the design and evaluation of brain network visualization approaches. Our research is divided to three-steps. First, we define a taxonomy that includes three dimensions: retinal variable, data continuity, and plane. Second, we demonstrated that this theory carries descriptive power in that we can use it to describe existing visualization techniques for brain imaging visualizations. We then propose five empirical studies to understand and evaluate encoding approaches in structure and functional networks accordingly. The first three studies focus on single modality and the last two studies differences in dual-modality multiplex network comparison based on cohort analyses. Using the results derived from the empirical studies, we present a visual analytics approach for brain scientists to explore cohort and individual brain network to let them answer research questions. We use computational methods to derive relationships from two modalities in cohorts of two modalities, and then represent cohort with uncertainty as well as individual ones for brain scientists to study uncertainty in network analysis.
Committee: Drs. Jian Chen (Chair), Penny Rheingans, Konstantinos Kalpakis, Peter Kochunov (UMB), Niklas Elmqvist (UMCP) and Alexander Auchus (UMC)
]]>
PhD Dissertation Proposal Design and Validation of Brain Network Visualization Techniques: A Unified Approach Guohao Zhang Time and Place: 8:00-10:00am, 22 Jan 22 2015, ITE325 We propose...
http://www.csee.umbc.edu/2015/01/phd-proposal-zhang-on-brain-network-visualization-techniques/
https://dev.my.umbc.edu/api/v0/pixel/news/49150/guest@my.umbc.edu/b6013b53440dadd8975b3c1a208c0b60/api/pixel
computer-science
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 22 Jan 2015 00:10:03 -0500
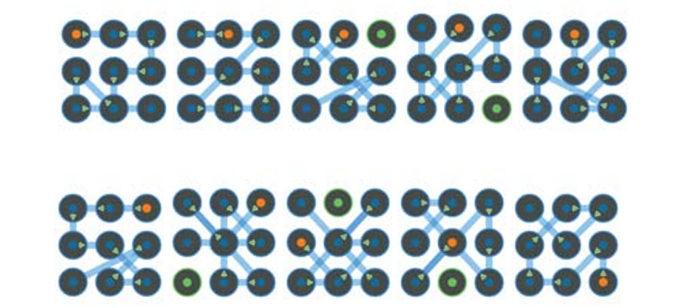
talk: Measuring Visual Perceptions of Security, 10am Fri 1/16, UMBC
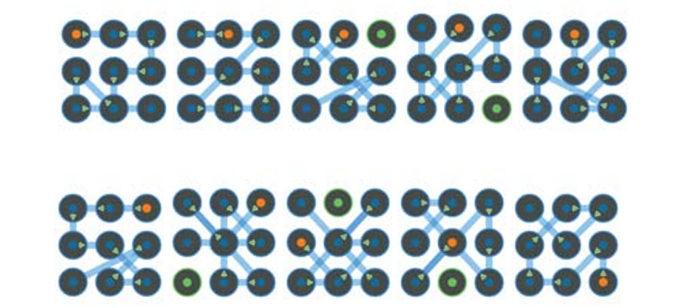
Top 10 highest rated passwords for most “Highly Usable” and “Highly Secure.” The highest rated is in the top left, and moving left-to-right by row, the tenth, highest rated is the lower right.
UMBC Information Systems
Measuring Visual Perceptions of Security
Professor Adam J. Aviv
United States Naval Academy
10:00am – 11:00am Friday, 16 January 2015, ITE 459
This talk presents the results of a user study of the Android graphical password system to measure visual perceptions of security. The survey methodology asked participants to select between carefully selected pairs of patterns indicating either a security or usability preference. By selecting password pairs that isolate a visual feature, a perception of usability and security of different features can be quantified in relatively. We conducted a large IRB-approved survey using pairwise preferences which attracted 384 participants on Amazon Mechanical Turk. Analyzing the results, we find that visual features that can be attributed to complexity indicated a stronger perception of security, while spatial features, such as shifts up/down or left/right are not strong indicators for security or usability.
We extended and applied the survey data by building logistic models to predict perception preferences by training on features used in the survey and other features proposed in related work. The logistic model accurately predicted preferences above 70%, twice the rate of random guessing, and the strongest feature in classification is password distance, the total length of all lines in the pattern, a feature not used in the online survey. This result provides insight into the internal visual calculus of users when comparing choices and selecting visual passwords, and the ultimate goal of this work is to leverage the visual calculus to design systems where inherent perceptions for usability coincides with a known metric of security.
Adam J. Aviv is an Assistant Professor of Computer Science at the United States Naval Academy, receiving his Ph.D. from the University of Pennsylvania under the advisement of Jonathan Smith and Matt Blaze. He has varied research interests including in system and network security, applied cryptography, smartphone security, and more recently in the area of usable security with a focus on mobile devices.
]]>
Top 10 highest rated passwords for most “Highly Usable” and “Highly Secure.” The highest rated is in the top left, and moving left-to-right by row, the tenth, highest rated is the lower right....
http://www.csee.umbc.edu/2015/01/talk-measuring-visual-perceptions-of-security-10am-fri-116-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/49015/guest@my.umbc.edu/c5fd955e57eb01af0f06fbba615f64f5/api/pixel
computer-engineering
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 15 Jan 2015 12:30:31 -0500