Talk: Zatyko on Cloud Forensics, Noon Fri 11/1, ITE 229, UMBC

Center for Information Security and Assurance
University of Maryland, Baltimore County
Cloud Forensics and its Many Challenges
Ken Zatyko
Assured Information Security, Inc.
12-1pm, Friday 1 November 2013, ITE 229, UMBC
In this presentation, we present a challenge question for today’s cyber experts, cyber scientists, and cyber analysts. Does Locard’s Exchange Principle apply in digital forensics? The dramatic increase in cybercrime and the repeated cyber intrusions into critical infrastructure demonstrate the need for improved security. The Executive Office of the President noted on May 12, 2011 “cyber threat is one of the most serious economic and national security challenges we face as a nation.” We believe addressing whether or not Locard’s Exchange Principle applies to digital forensics is a fundamental question that can guide or limit the scientific search for digital evidence.
Locard’s Exchange Principle is often stated in forensics publications “every contact leaves a trace…” Essentially Locard’s Exchange Principle is applied to crime scenes in which the perpetrator(s) of a crime comes into contact with the scene. The perpetrator(s) will both bring something into the scene, and leave with something from the scene. In the cyber world, the perpetrator may or may not come in physical contact with the crime scene, thus, this brings a new facet to crime scene analysis. According to the World of Forensic Science, Locard’s publications make no mention of an “exchange principle,” although he did make the observation “Il est impossible au malfaiteur d’agir avec l’intensité que suppose l’action criminelle sans laisser des traces de son passage.” (It is impossible for a criminal to act, especially considering the intensity of a crime, without leaving traces of this presence.)
The term “principle of exchange” first appears in Police and Crime-Detection, in 1940, and was adapted from Locard’s observations. The field of digital forensics can be strictly defined as “the application of computer science and investigative procedures for a legal purpose involving the analysis of digital evidence after proper search authority, chain of custody, validation with mathematics, use of validated tools, repeatability, reporting, and possible expert presentation. (Zatyko, 2007).” Furthermore, digital evidence is defined as information stored or transmitted in binary form that may be relied on in court. (National Institute of Justice, 2004). However, digital forensics tools and techniques have also been used by cyber analysts and researchers to conduct media analysis, compile damage assessments, build timelines, and determine attribution. According to the Department of Defense Cyber Crime Center’s training program, cyber analysts require knowledge on how network intrusions occur, how various logs are created, what is electronic evidence, how electronic artifacts are forensically gathered, and the ability to analyze data to produce comprehensive reports and link analysis charts.
Our hypothesis is that Locard’s Exchange Principle does apply to cyber crimes involving computer networks such as identity theft, electronic bank fraud, or denial of service attacks, even if the perpetrator does not need to physically come in contact with the crime scene. Although the perpetrator may make virtual contact with the crime scene through the use of a proxy machine, we believe he will still “leave a trace” and digital evidence will exist. This presentation will explore with audience input “where in the cloud is digital evidence found” and new ways it can lead to attribution. It will explore what new standards and techniques are needed to find these digital traces. Read ahead information can be found at here.
Ken Zatyko was previously the Director of the Department of Defense Computer Forensics Laboratory where he led the largest accredited, internationally recognized, leading-edge computer forensics laboratory located in Maryland. For several months, Mr. Zatyko has been working with NIST on a working group to further standards and technology to solve cloud forensics challenges. Mr. Zatyko is currently the Vice President of Maryland Operations with Assured Information Security.
Host: Dr. Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
Center for Information Security and Assurance University of Maryland, Baltimore County Cloud Forensics and its Many Challenges Ken Zatyko Assured Information Security, Inc. 12-1pm, Friday...
http://www.csee.umbc.edu/2013/10/digital-cloud-forensics/
https://dev.my.umbc.edu/api/v0/pixel/news/37694/guest@my.umbc.edu/3ab044be7b086401e302197f676d823e/api/pixel
computer-engineering
computer-science
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 29 Oct 2013 22:53:32 -0400
Tue, 29 Oct 2013 22:53:32 -0400
Defense: Tyler Simon on Task Scheduling for Scalable High Performance Computing
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Ph.D. Dissertation Defense
Multiple Objective Task Scheduling
for Scalable High Performance Computing
Tyler A. Simon
12:30-2:30 Friday, 8 November 2013, ITE 325b
Individual processor frequencies have reached an upper physical and practical limit. Processor designs now involve adding multiple processing elements to a single chip to enable increased performance. It is expected that all future processor designs will have multiple cores with a focus on reducing frequencies and adding more individual processing elements (cores) while having to balance power consumption, reliability and maintain high performance.
Due to the increased complexity as well as increased heterogeneity of parallel architectures, petascale and future exascale systems, with the number of processors on the order of 10^8-10^9, must incorporate more intelligent software tools that help manage parallel execution for the user. I demonstrate that by managing the parallel execution environment at runtime, we can satisfy performance tradeoffs for a particular application or application domain for a set of common HPC architectures. It is expected that future exascale computing systems will have to execute programs on many individual and potentially low powered processing elements. These processors need to be fed data efficiently and reliably through the duration of a parallel computation.
In this thesis I provide a performance analysis of two common graph algorithms for finding a minimum spanning tree and evaluate the multicore performance of a common high performance computing (HPC) benchmark on multicore processors. I also develop a novel autonomic execution model and adaptive runtime system (ARRIA) Adaptive Runtime Resource for Intensive Applications. ARRIA is designed with the intent of improving application programmability, scalability and performance while freeing the programmer from explicit message passing and thread management. Experiments are conducted that evaluate ARRIA’s capabilities on data intensive applications, those where the majority of execution time is spent reading and writing either to local or remote memory locations. In my approach, I focus on developing task schedules that satisfy multiple objectives for clusters of compute nodes during runtime. This approach is novel in that it can control application performance and satisfy constraints that are solved using multi objective optimization techniques as the program runs. The development and implementation of the ARRIA runtime system and subsequent optimization criteria likely provide reasonable models for the exascale computing era.
The results of this dissertation demonstrate, experimentally, that for high performance computing systems, a dynamic, task based, parallel programming environment and scheduler can provide lower total workload runtimes and high utilization compared with commonly used static scheduling policies.
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Ph.D. Dissertation Defense Multiple Objective Task Scheduling for Scalable High Performance Computing...
http://www.csee.umbc.edu/2013/10/defense-tyler-simon-on-task-scheduling-for-scalable-high-performance-computing/
https://dev.my.umbc.edu/api/v0/pixel/news/37519/guest@my.umbc.edu/18ddb363778f521ac0f7d94933a10586/api/pixel
computer-science
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Fri, 25 Oct 2013 16:57:25 -0400
Talks: two PhD students talk about their research on quantum computing
Computer Science and Electrical Engineering
Quantum Computing Seminar
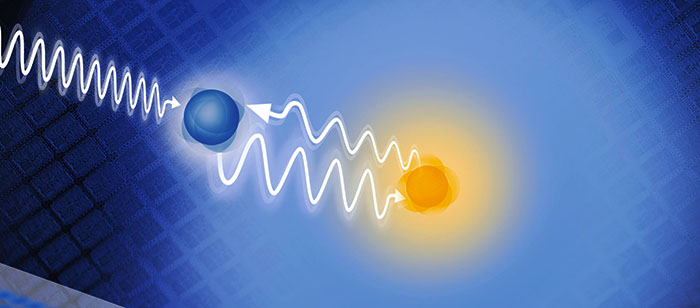
Thermal Light N-qubit
Tao Peng (PhD Advisor: Yanhua Shih)
UMBC Physics Department
2:30-3:00 Tuesday, 22 October 2013, ITE 325b
This talk will discuss the equipment and optical elements that required for building the incoherent thermal source, the qubit, and the detection scheme of the intensity fluctuation-fluctuation correlation.
All optical XOR, CNOT gates with initial insight
for quantum computation using linear optics
Omar Shehab (PhD Advisor: Samuel Lomonaco)
UMBC CSEE Department
3:00-3:30 pm, Tuesday, 22 October 2013, ITE 325b
The design for an all-optical XOR gate is proposed. The basic idea is to split the input beams, and let them cancel or strengthen each other selectively, or flip the encoded information based on their polarization properties. The information is encoded in terms of polarization of the beam. Polarization of a light beam is well understood, hence, the design should be feasible to implement. The truth table of the optical circuit is worked out and compared with the expected truth table. Then it is demonstrated that the design complies with the linear behavior of the XOR function.
Next, based on a similar idea, the design of an all-optical CNOT gate is proposed. The truth table for the gate is verified. Then, it is discussed how this approach can be used for Linear Optics Quantum Computation (LOQC). It is shown that a Hadamard gate, a rotation gate, and a CNOT gate make up a universal set of quantum gates based on linear optics. This novel approach requires no additional power supply, extra input beam or ancilla photon to operate. It also does not require an expensive and complex single photon source and detector. Only narrowband laser sources are required to operate these gates.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
Computer Science and Electrical Engineering Quantum Computing Seminar Thermal Light N-qubit Tao Peng (PhD Advisor: Yanhua Shih) UMBC Physics Department 2:30-3:00 Tuesday, 22 October 2013,...
http://www.csee.umbc.edu/2013/10/talk-quantum-computing-seminar/
https://dev.my.umbc.edu/api/v0/pixel/news/37226/guest@my.umbc.edu/85b47ba314606d64f1bb51a7d8ab5b5c/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 19 Oct 2013 16:07:50 -0400
Sat, 19 Oct 2013 16:07:50 -0400
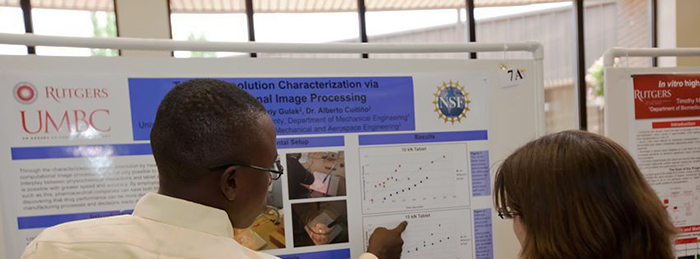
Talk on graduate school and summer research, Noon Wed. 10/16
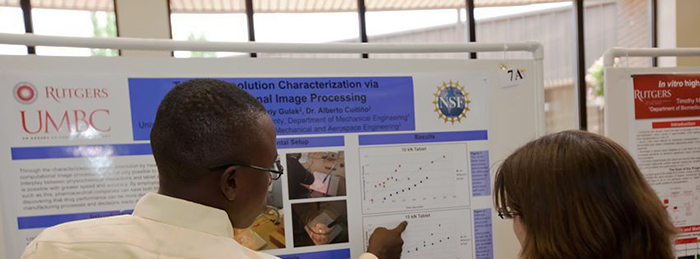
Dr. Evelyn Erenrich from Rutgers University will talk on “An Inside Look at Graduate School and Summer Research: How to Prepare, Get Accepted, and Succeed” at Noon on Wednesday, October 16 in room 208, Public Policy.
In addition to discussing strategies for research success, Dr. Erenrich will spotlight exciting programs and interdisciplinary training opportunities at Rutgers University, including a summer program, RiSE (Research in Science and Engineering), which has included many UMBC students. Mr. Immanuel Williams, a UMBC alumnus who is currently a doctoral Fellow at Rutgers, will be joining me to give his personal perspective. Students can also sign up for individual appointments by contacting Ms. Alicia Hall, Sorry, you need javascript to view this email address.
]]>
Dr. Evelyn Erenrich from Rutgers University will talk on “An Inside Look at Graduate School and Summer Research: How to Prepare, Get Accepted, and Succeed” at Noon on Wednesday, October 16 in room...
http://www.csee.umbc.edu/2013/10/talk-on-graduate-school-and-summer-research-noon-wed-1016/
https://dev.my.umbc.edu/api/v0/pixel/news/37005/guest@my.umbc.edu/2853389671fcc36e5934085de2016c28/api/pixel
news
students
talks
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 15 Oct 2013 09:01:28 -0400
Tue, 15 Oct 2013 09:01:28 -0400
talk: Thermal light N-qubits (part II), 2:30 Tue 10/8 ITE325b
UMBC Quantum Computation Seminar
Thermal light N-qubits, part II
Yanhau Shih
Physics Department, UMBC
2:30-4:00 Tuesday, 8 October 2013, ITE 325b
This talk will discuss a few recent experiments on Nth-order interference of N independent and incoherent thermal fields from their intensity fluctuation correlation measurement. The observed interference is similar to that of entangled states. These experiments have demonstrated the possibility of producing N-qubits from N incoherent thermal fields.
Yanhua Shih received his B.S. degree in theoretical physics from Northwestern University of China in 1981, and his Ph.D. in physics from the University of Maryland, College Park, in 1987. He joined the Faculty of the University of Maryland, Baltimore County in 1989 and established the Quantum Optics Program at UMBC. He is currently Professor of Physics at UMBC. His research interests include fundamental problems of quantum theory and general relativity.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
UMBC Quantum Computation Seminar Thermal light N-qubits, part II Yanhau Shih Physics Department, UMBC 2:30-4:00 Tuesday, 8 October 2013, ITE 325b This talk will discuss a few recent...
http://www.csee.umbc.edu/2013/10/talk-thermal-light-n-qubits-part-ii-230-tue-108-ite325b/
https://dev.my.umbc.edu/api/v0/pixel/news/36622/guest@my.umbc.edu/cd8f4870cd77bc4c2fcf691dbed893c5/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 05 Oct 2013 09:25:34 -0400
Sat, 05 Oct 2013 09:25:34 -0400
talk: Seymour on Quantum Computing and Cybersecurity, Noon Fri. 10/4, ITE228
UMBC Center for Information Security and Assurance
Quantum Computing and Cybersecurity
John Seymour
Noon-1:00 Friday, 4 October 2013
Cyber Defense Lab, room 228 ITE, UMBC
This talk will be a brief introduction to the topic of quantum computing for the computer scientist interested in cybersecurity. It will begin with a light summary of the fundamental quantum algorithms and move to discuss the recent advances in quantum computing, including the D-Wave quantum optimizer, University of Bristol’s new quantum chip, quantum programming languages, and more. Finally, it will introduce some current research questions and projects residing in the intersection of quantum computing and cybersecurity.
John Seymour is a Ph.D. student in the UMBC computer science graduate program. As a UMBC undergraduate, he was a triple major — Computer Science, — Mathematics and Philosophy. He is currently working on three research projects: evaluation of a detection protocol for Man-in-the-Middle attacks, a web-based game for teaching students basic concepts of internet security, and integration of social media with internet voting to facilitate collaborative decision making.
Host: Dr. Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
UMBC Center for Information Security and Assurance Quantum Computing and Cybersecurity John Seymour Noon-1:00 Friday, 4 October 2013 Cyber Defense Lab, room 228 ITE, UMBC This talk will...
http://www.csee.umbc.edu/2013/10/talk-seymour-on-quantum-computing-and-cybersecurity-noon-fri-104-ite228/
https://dev.my.umbc.edu/api/v0/pixel/news/36503/guest@my.umbc.edu/3b8571b1d206fd37b77d4d9fcce02ad3/api/pixel
cybersecurity
graduate
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 03 Oct 2013 09:42:20 -0400
Thu, 03 Oct 2013 09:42:20 -0400
talk: Thermal light N-qubits, 2:30 Tue 10/1 ITE325b

UMBC Quantum Computation Seminar
Thermal light N-qubits
Yanhau Shih
Physics Department, UMBC
2:30-4:00 Tuesday, 1 October 2013, ITE 325b
This talk will discuss a few recent experiments on Nth-order interference of N independent and incoherent thermal fields from their intensity fluctuation correlation measurement. The observed interference is similar to that of entangled states. These experiments have demonstrated the possibility of producing N-qubits from N incoherent thermal fields.
Yanhua Shih received his B.S. degree in theoretical physics from Northwestern University of China in 1981, and his Ph.D. in physics from the University of Maryland, College Park, in 1987. He joined the Faculty of the University of Maryland, Baltimore County in 1989 and established the Quantum Optics Program at UMBC. He is currently Professor of Physics at UMBC. His research interests include fundamental problems of quantum theory and general relativity.
Organizer: Prof. Samuel Lomonaco, Sorry, you need javascript to view this email address.
]]>
UMBC Quantum Computation Seminar Thermal light N-qubits Yanhau Shih Physics Department, UMBC 2:30-4:00 Tuesday, 1 October 2013, ITE 325b This talk will discuss a few recent experiments...
http://www.csee.umbc.edu/2013/09/talk-thermal-light-n-qubits-230-tue-101-ite325b/
https://dev.my.umbc.edu/api/v0/pixel/news/36295/guest@my.umbc.edu/d6a724862b1e90227df72798376e6c95/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 27 Sep 2013 22:04:43 -0400
Fri, 27 Sep 2013 22:04:43 -0400
IEEE Colloquium on Sensor Devices, 9/25

The Baltimore Chapter of IEEE Electron Devices and Solid-State Circuits is co-hosting a free, one-day Colloquium on Sensor Devices from 10:00 to 5:00 on Wednesday, September 25. The event will be held in the Benjamin Banneker Room (2212) of the Stamp Union Building at the University of Maryland, College Park.
Invited speakers include Dr. Philip Perconti (Army Research Laboratory), Prof. M. Alam (Purdue University), Dr. Parvez Uppal (Army Research Laboratory), Prof. Mark Reed (Yale University), Dr. Herbert Bennett (NIST), Prof. Michael Shur (RPI), Dr. Anupama Kaul (National Science Foundation) and Prof. Agis Iliadis (UMCP).
Attendance is free. To register please contact: Dr. Naresh C. Das (naresh.c.das2.civ at mail.mil), Dr. Victor Veliadis (victor.veliadis at ngc.com).
]]>
The Baltimore Chapter of IEEE Electron Devices and Solid-State Circuits is co-hosting a free, one-day Colloquium on Sensor Devices from 10:00 to 5:00 on Wednesday, September 25. The event will be...
http://www.csee.umbc.edu/2013/09/ieee-colloquium-on-sensor-devices-925/
https://dev.my.umbc.edu/api/v0/pixel/news/35485/guest@my.umbc.edu/8e524ffacdf4ebc734dd3508420187da/api/pixel
computer-engineering
computer-science
electrical-engineering
events
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 11 Sep 2013 11:30:43 -0400
talk: Computer-Assisted Reasoning In Digital Forensics (Noon, Fri 9/20)

UMBC Center for Information Security and Assurance
Computer-Assisted Reasoning In Digital Forensics
Dr. Eoghan Casey
Noon-1:00 Friday, 20 September 2013
Cyber Defense Lab, room 228 ITE, UMBC
The primary challenge in digital forensics today is uncovering not the right answer, but the right question. As in any scientific discipline, the formation of viable hypotheses that ultimately uncover meaning in available evidence is a central problem in digital forensics. Such hypothesis formation, based on intuition and experience, involves an underlying mental process that can be substantially aided by computers. This seminar delves into the cognitive science of investigative reasoning, and how research in artificial intelligence can help humans find the right questions in large quantities of data. The implications of this work for digital identity and privacy, as well as its potential uses in other areas, such as medical diagnosis and virtual learning environments, are also discussed.
Eoghan Casey is an internationally recognized expert in digital forensics and data breach investigations. For over a decade, he has dedicated himself to advancing the field of digital forensics. He wrote the foundational book Digital Evidence and Computer Crime, now in its third edition, and he created advanced smartphone forensics courses taught worldwide. He has also co-authored several advanced technical books including Malware Forensics, and is Editor-in-Chief of Digital Investigation: The International Journal of Digital Forensics and Incident Response. Dr. Casey received his Ph.D. from University College Dublin, and has taught digital forensics at the Johns Hopkins University Information Security Institute.
Dr. Casey has worked as R&D Team Lead at the Defense Cyber Crime Center (DC3) helping enhance their operational capabilities and develop new techniques and tools. He has also helped organizations handle security breaches and analyzes digital evidence in a wide range of investigations, including network intrusions with international scope. He has testified in civil and criminal cases, and has submitted expert reports and prepared trial exhibits for computer forensic and cyber-crime cases.
Host: Dr. Alan T. Sherman, Sorry, you need javascript to view this email address.
]]>
UMBC Center for Information Security and Assurance Computer-Assisted Reasoning In Digital Forensics Dr. Eoghan Casey Noon-1:00 Friday, 20 September 2013 Cyber Defense Lab, room 228 ITE,...
http://www.csee.umbc.edu/2013/09/talk-computer-assisted-reasoning-in-digital-forensics-920/
https://dev.my.umbc.edu/api/v0/pixel/news/35329/guest@my.umbc.edu/7cc3b52b1bd2949464f1a7c181042901/api/pixel
computer-engineering
computer-science
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 08 Sep 2013 14:40:37 -0400
Thu, 19 Sep 2013 07:40:37 -0400
Introduction to Quantum Computing and D-Wave Systems, 10am Tue 7/30
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
An Introduction to Quantum Computing: D-Wave Systems
Robert (Bo) Ewald and Edward (Denny) Dahl
D-Wave Systems, Inc
10:00-12:00 Tuesday, July 30, 2013, ITE 325b
Bo Ewald and Denny Dahl from D-Wave Systems, Inc. will present an introduction to quantum computing and its role in their computing systems, complex machines constructed using state of the art ideas and approaches from many different fields of science and technology. While the quantum processor itself is the heart of the machine, the infrastructure that makes the processor go is also designed, built and tested extensively by D-Wave. In 2011, D-Wave System announced the D-Wave One, "the world's first commercially available quantum computer" which incorporated their 128 qubit chip-set using quantum annealing to solve optimization problems. This year a collaboration between NASA, Google and the Universities Space Research Association was announced that will create a Quantum Artificial Intelligence Lab at the NASA Ames Research Center that will use a 512 qubit D-Wave Two system to study how quantum computing might advance machine learning.
Bo Ewald has been Chief Revenue Officer and President of U.S. Business at D-Wave Systems Inc. since May 02, 2013. Mr. Ewald served as Chief Executive Officer of Graphics Properties Holdings, Inc., since April 9, 2007. Mr. Ewald has over 25 years experience in the high performance computing industry. He served as Chief Executive Officer of Silicon Graphics, Inc. from 2007 to 2009. He served as Chief Operating Officer and Executive Vice President of Scale8 Inc. He served as Chief Executive Officer of Linux Networx, Inc. until April 3, 2007 and oversaw its strategy & direction to drive continued growth. From 1984 to 1996, he held various management and executive positions at Cray Research, Inc., including President and Chief Operating Officer since December 1994. Before joining Cray Research Inc., he served as Head of the Computing and Communications Division of the Los Alamos National Laboratory and was responsible for providing computing and communications services to government customers nationwide from 1980 to 1984. Mr. Ewald is involved in various industry organizations and was appointed to the President's Information Technology Advisory Committee from 1997 to 2001. Mr. Ewald holds an M.S. Degree in Civil Engineering and Applied Mathematics from the University of Colorado and a BS Degree in Civil Engineering from the University of Nevada.
Dr. Denny Dahl received his PhD in physics from Stanford University in 1985 after completing a thesis on Quantum Monte Carlo computational techniques. He took a postdoctoral research position at Lawrence Livermore National Labs in the Parallel Processing Project and worked on simulation, analysis and applications of neural networks. Following this, Denny joined Thinking Machines Corporation and worked in their Technical Marketing Department. He obtained a patent for novel work in routing messages through the communication fabric of the CM-2, which was a massively parallel high performance computing platform. He also helped in providing technical support to a number of customers across a range of business verticals, including the petroleum and defense industries. Following Thinking Machines, Dr. Dahl participated in a range of start-up companies and developed expertise in high volume / high complexity RDBMS environments. He worked at a number of companies (eBay, Wells Fargo, JP Morgan Chase, Travelers Insurance, Western Asset Management, Williams Sonoma, Kroger, Walgreens, Teradata) providing architectural and development services related to batch and real-time data processing. Denny joined D-Wave Systems at the beginning of 2012, and has been involved in algorithm research, training, technical support for sales and communication functions within the company.
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County An Introduction to Quantum Computing: D-Wave Systems Robert (Bo) Ewald and Edward (Denny) Dahl D-Wave...
http://www.csee.umbc.edu/2013/07/introduction-to-quantum-computing-and-d-wave-systems-10am-tue-730/
https://dev.my.umbc.edu/api/v0/pixel/news/33241/guest@my.umbc.edu/8859a19590ffe405aade40610504ade7/api/pixel
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 27 Jul 2013 16:07:07 -0400
Sat, 27 Jul 2013 16:07:07 -0400