Phd Defense: Dingkai Guo, Mid-Infrared Photonic Integration 6/4
Ph.D. Dissertation Defense
Mid-Infrared Photonic Integration
Dingkai Guo
10:00am Tuesday, 4 June 2013, TRC CASPR conference room
The mid-Infrared (Mid-IR) wavelength range is important for applications including medical and security imaging, environmental trace gas sensing and free space communications. However, photonic integrated circuits (PICs) in the mid-IR range are completely under-developed which significantly slows the reduction of mid-IR system size, weight, and coupling losses and limits the development of highly functional mid-IR photonic modules with lower cost. In this dissertation, a solution to mid-IR photonic integration was demonstrated using a compact widely tunable mid-IR transmitter and a mid-IR amplifying photo-detector, which can be integrated with the mid-IR source.
This integrated widely tunable mid-IR source is fabricated by incorporating super structure grating (SSG) to the mid-IR quantum cascade laser (QCL) waveguide. The emission wavelength of the fabricated SSG-DBR QCL can be well controlled by varying the injection currents to the two grating sections. The wavelength can be tuned from 4.58μm to 4.77μm (90cm-1) with a supermode spacing of 30nm. This SSG-DBR QCL can be a compact replacement for the external cavity QCL used in current mid-IR sensors.
Mid-IR amplification and detection can be achieved using the same material as the mid-IR source. This QCL amplifier has an adjustable bandwidth and tunable gain peak, so it can function as a tunable mid-IR filter. By biasing the QCL just below its threshold, we demonstrated more than 11dB optical gain and over 28dB electrical gain at specified wavelengths. In the electrical gain measurement process, the resonant amplifier also functioned as a detector. This indicates that intersubband-based gain materials are ideal candidates for mid-IR photonic integrations.
Beside the optimized fabrication processes, new characterization technique based on the electrical derivative of the QCL I-V curves is used to quickly acquire the QCL threshold and leakage current, and explore the device carrier transport. The leakage currents present in different QCL waveguide structures are also studied and compared using this technique.
Finally, we report that the telecom wavelengths induced optical quenching effects on mid-IR QCLs when the QCLs are operated well above their threshold. The quenching effect is a result of intersubband bandbending and it depends on the coupled near-IR intensity, wavelength, and the QCL voltage bias. The quenching effects not only can be used for mid-IR QCL optical switching and modulation but also reveal that the mid-IR QCLs can function as “converters” to convert the telecom optical signal into the mid-IR optical signal at the near-IR fiber end.
A coherent mid-IR transceiver with both transmitting and receiving functions can be realized based on each integrated component introduced in this dissertation. This compact transceiver includes an integrated widely tunable mid-IR source, a mid-IR filter, amplifier, and detector based on the same material system.
Committee: Drs. Fow-Sen Choa (Chair), Anthony Johnson, Terrance Worchesky (Physics) , Li Yan, Gymama Slaughter
]]>
Ph.D. Dissertation Defense Mid-Infrared Photonic Integration Dingkai Guo 10:00am Tuesday, 4 June 2013, TRC CASPR conference room The mid-Infrared (Mid-IR) wavelength range is important for...
http://www.csee.umbc.edu/2013/06/phd-defense-dingkai-guo-mid-infrared-photonic-integration-64/
https://dev.my.umbc.edu/api/v0/pixel/news/30718/guest@my.umbc.edu/4bbf7463d20ee8f86ccc2976eef499d7/api/pixel
defense
electrical-engineering
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Jun 2013 12:02:07 -0400
Mon, 03 Jun 2013 12:02:07 -0400
MS defense: A Multilayer Framework to Catch Data Exfiltration

MS Thesis Defense
A Multilayer Framework to Catch Data Exfiltration
Puneet Sharma
10:30am Wednesday, 5 June 2013, 325b ITE, UMBC
Data exfilteration is the unauthorized leakage of confidential data from a particular system. It is a specific form of intrusion that is particularly hard to catch due to the most common cause: an insider entity who is responsible for the leak. That entity could be a person employed in the organization or a malicious hardware component bought from an unreliable third party. Catching such intrusions, therefore, can be extremely difficult. We describe a framework comprising multiple parameters that are constantly monitored in a system. These parameters can cover the entire stack of the computer architecture, from the hardware up to the application layer. Malicious behavior is detected by different modules monitoring these parameters and an aggregated attack alert is produced if multiple modules detect malicious activity within a short period of time. A more distributed and comprehensive monitoring framework should ensure that designing an attack becomes extremely difficult since an attack must go through multiple detectors present in the system without raising any alarms.
Committee: Drs. Anupam Joshi (chair), Tim Finin, Chintan Patel
]]>
MS Thesis Defense A Multilayer Framework to Catch Data Exfiltration Puneet Sharma 10:30am Wednesday, 5 June 2013, 325b ITE, UMBC Data exfilteration is the unauthorized leakage of...
http://www.csee.umbc.edu/2013/06/ms-defense-a-multilayer-framework-to-catch-data-exfiltration/
https://dev.my.umbc.edu/api/v0/pixel/news/30679/guest@my.umbc.edu/6c3029458e7b688c7afe7970a2d4dd1b/api/pixel
computer-science
cybersecurity
defense
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sun, 02 Jun 2013 17:39:21 -0400
MS defense: Extracting cybersecurity related entities, terms and concepts from text
MS Thesis Defense
Extracting cybersecurity related entities,
terms and concepts from text
Ravendar Lal
10:30am Tuesday, 28 May 2013, ITE325b, UMBC
Securing computers, data, cyber-physical systems and networks is a growing problem as society's dependence on them increases while they remain vulnerable to attacks by both criminals and rival nation states. Creating 'situationally aware' computer systems that defend against new "zero day" software vulnerabilities requires them to automatically integrate and use new security-related data from a wide variety of sources. One important source is information found in text from security bulletins, vulnerability databases, news reports, cybersecurity blogs and Internet chat rooms.
We describe an information extraction framework to extract cybersecurity-relevant entities, terms and concepts from text. We use a Conditional Random Field based model trained on manually annotated data to identify and extract the relevant terms. These are then mapped to a previously developed OWL ontology and represented as RDF linked data. We evaluated the system's performance by comparing its results on test data from the National Vulnerability Database and security bulletins from Microsoft and Adobe.
Committee: Drs. Tim Finin (Advisor), Anupam Joshi, Tim Oates
]]>
MS Thesis Defense Extracting cybersecurity related entities, terms and concepts from text Ravendar Lal 10:30am Tuesday, 28 May 2013, ITE325b, UMBC Securing computers, data,...
http://www.csee.umbc.edu/2013/05/ms-defense-extracting-cybersecurity-related-entities-terms-and-concepts-from-text/
https://dev.my.umbc.edu/api/v0/pixel/news/30345/guest@my.umbc.edu/842d0a44fbd43e51abecae6094d94dd7/api/pixel
computer-science
cybersecurity
defense
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 24 May 2013 22:26:44 -0400
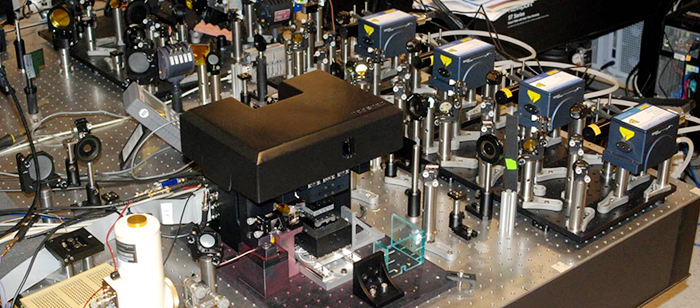
PhD defense: Quantum Cascade Laser Arrays for Standoff Photoacoustic Chemical Detection, 5/17
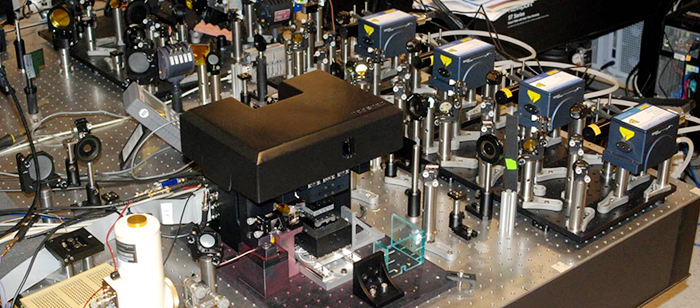
Ph.D. Dissertation Defense
High Power Mid-infrared Quantum Cascade Laser Array
for Standoff Photoacoustic Chemical Detection
Xing Chen
1:00-3:00pm Friday, 17 May 17 2013, TRC CASPR Conference Room
Quantum cascade lasers (QCLs) are compact, portable, powerful semiconductor laser sources with emission wavelengths from mid-infrared (mid-IR) to terahertz (THz) regions of the electromagnetic spectrum. Mid-IR (i.e. wavelengths from 3 to 20 µm) QCLs are of great importance in a wide range of applications such as trace gas sensing, environmental monitoring, free space communication, medical diagnosis and so on. High power QCLs are particularly important to applications such as infrared counter measure (IRCM) and standoff chemical detections. In such applications, the system performances critically depend on the amount of power a QCL can produce. This dissertation includes two major studies: the first part of the dissertation includes design, fabrication and characterization of high power mid-IR QCL arrays; the second part involves standoff chemical detection using QCLs as laser sources and photoacoustic effect as sensing technologies.
In the first part of the dissertation, we design, fabricate and characterize multi-emitter QCL arrays consisting of multiple narrow laser stripes. Simulation results indicate that the proposed multi-emitter laser arrays present much better thermal performance than a broad area laser device, while having the same thermal management ability as a single narrow stripe device. We have successfully fabricated edge emitting and surface emitting QCL arrays with 5 and 16 emitters. Experimental results show that, with the same laser cavity length, a QCL array with 5 emitters produces over 3 times more power than a single emitter laser device. QCL array with 16 emitters generates about 4 W output peak power at wavelength ~7.9 µm. We have also fabricated surface emitting QCL arrays and demonstrated single mode emission.
The second part of the dissertation involves using high power mid-IR QCLs to perform standoff chemical detections based on photoacoustic sensing technologies. Photoacoustic effect is a light-matter interaction effect that involves generation of acoustic waves when a medium absorbs electromagnetic energy from light. It has been known as a sensitive spectroscopic technique for chemical sensing.
Standoff photoacoustic chemical detection with distance more than 41 feet using quantum cascade laser operated at relatively low power, less than 40 mW, is demonstrated. A simplified theoretical model is developed for pulsed laser photoacoustic effect in open-air environment. The standoff photoacoustic signal can be calibrated as a function of different parameters such as laser pulse energy, gas vapor concentration and detection distance. The results yield good agreements with theoretical model. Standoff detection of solid phase explosive chemicals has also been demonstrated by the use of an ultra-sensitive microphone and acoustic reflector. More than 8 feet detection distance is obtained for standoff photoacoustic sensing of explosives.
Committee: Drs. Fow-Sen Choa (Chair), Brian Cullum, Yordan Kostov, Ryan Robucci, Chen-Chia Wang and Li Yan
]]>
Ph.D. Dissertation Defense High Power Mid-infrared Quantum Cascade Laser Array for Standoff Photoacoustic Chemical Detection Xing Chen 1:00-3:00pm Friday, 17 May 17 2013, TRC CASPR...
http://www.csee.umbc.edu/2013/05/13936/
https://dev.my.umbc.edu/api/v0/pixel/news/29563/guest@my.umbc.edu/f16a7877838a77217133f681c0cea497/api/pixel
defense
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 16 May 2013 12:01:02 -0400
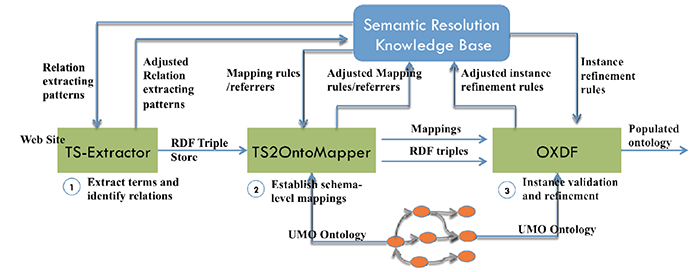
PhD proposal: A Semantic Resolution Framework for Manufacturing Capability Data Integration
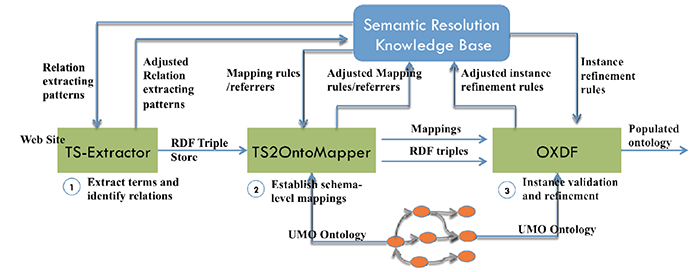
Ph.D. Dissertation Proposal
A Semantic Resolution Framework for
Manufacturing Capability Data Integration
10:30am Tuesday, May 14, 2013, ITE 346, UMBC
Yan Kang
Building flexible manufacturing supply chains requires interoperable and accurate manufacturing service capability (MSC) information of all supply chain participants. Today, MSC information, which is typically published either on the supplier’s web site or registered at an e-marketplace portal, has been shown to fall short of the interoperability and accuracy requirements. This issue can be addressed by annotating the MSC information using shared ontologies. However, ontology-based approaches face two main challenges: 1) lack of an effective way to transform a large amount of complex MSC information hidden in the web sites of manufacturers into a representation of shared semantics and 2) difficulties in the adoption of ontology-based approaches by the supply chain managers and users because of their unfamiliar of the syntax and semantics of formal ontology languages such as OWL and RDF and the lack of tools friendly for inexperienced users.
The objective of our research is to address the main challenges of ontology-based approaches by developing an innovative approach that can effectively extract a large volume of manufacturing capability instance data, accurately annotate these instance data with semantics and integrate these data under a formal manufacturing domain ontology. To achieve the objective, a Semantic Resolution Framework is proposed to guides every step of the manufacturing capability data integration process and to resolve semantic heterogeneity with minimal human supervision. The key innovations of this framework includes 1) three assisting systems, including a Triple Store Extractor, a Triple Store to Ontology Mapper and a Ontology-based Extensible Dynamic Form, that can efficiently and effectively perform the automatic processes of extracting, annotating and integrating manufacturing capability data.; 2) a Semantic Resolution Knowledge Base (SR-KB) that incrementally filled with, among other things, rules/patterns learned from errors. This SR-KB together with an Upper Manufacturing Domain Ontology (UMO) provide knowledge for resolving semantic differences in the integration process; 3) an evolution mechanism that enables SR-KB to continuously improve itself and gradually reduce the human involvement by learning from mistakes.
Committee: Yun Peng (chair), Charles Nicholas, Tim Finin, Yaacov Yesha, Boonserm Kulvatunyou (NIST)
]]>
Ph.D. Dissertation Proposal A Semantic Resolution Framework for Manufacturing Capability Data Integration 10:30am Tuesday, May 14, 2013, ITE 346, UMBC Yan Kang Building flexible...
http://www.csee.umbc.edu/2013/05/phd-proposal-a-semantic-resolution-framework-for-manufacturing-capability-data-integration/
https://dev.my.umbc.edu/api/v0/pixel/news/29402/guest@my.umbc.edu/61bd79367c125d7bd4157e7a3bcfdce5/api/pixel
computer-science
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Mon, 13 May 2013 21:31:40 -0400
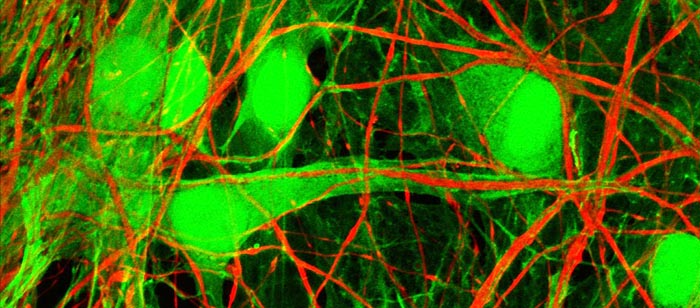
PhD proposal: Training Neural Networks and Recurrent Deep Learning Machines
Ph.D. Dissertation Proposal
Convexification/Deconvexification for Training Neural
Networks and Recurrent Deep Learning Machines
Yichuan Gui
9:30am Thursday, 16 May 2013, ITE 325b, UMBC
The development of artificial neural networks (ANNs) has been impeded by the local minimum problem for decades. One principle goal of this proposal focuses on devel- oping a methodology to alleviate the local minimum problem in training ANNs. A new training criterion called the normalized risk-averting error (NRAE) criterion is proposed to avoid nonglobal local minima in training multilayer perceptrons (MLPs) and deep learning machines (DLMs). Training methods based on the NRAE crite- rion are developed to achieve global or near-global minima with satisfactory learning errors and generalization capabilities.
Many advantages of DLMs have been analyzed in recent research works of ANNs, and effective architectures and training methods have been explored from those works. However, feedback structures are commonly ignored in previous research of DLMs. The next objective of this proposal is to develop recurrent deep learning machines (RDLMs) through adding feedback structures to deep architectures in DLMs. De- signing and testing works are expected to illustrate the efficiency and effectiveness of RDLMs with feedback structures comparing to feedforward DLMs.
Preliminary works presented in this proposal demonstrate the effectiveness of NRAE-based training methods in avoid nonglobal local minima for training MLPs. Methods based on the NRAE criterion will be tested in training DLMs, and the de- veloping and testing of RDLMs will be performed in subsequent works. Moreover, an approach that combining both the NRAE criterion and RDLMs will also be explored to minimize the training error and maximize the generalization capability. Contribu- tions of this proposed research are expected as (1) provide an effective way to avoid local minimum problem in training MLPs and DLMs with satisfactory performance; (2) develop a new type of RDLMs with feedback connections for training large-scale dataset efficiently; (3) apply the NRAE criterion to train RDLMs for minimizing training errors and maximizing generalization capabilities. Those contributions are expected to significantly boost research interests in ANNs' fields and stimulate new practical applications in the future.
Committee: James Lo (mentor), Yun Peng (mentor), Tim Finin, Tim Oates, Charles Nicholas
]]>
Ph.D. Dissertation Proposal Convexification/Deconvexification for Training Neural Networks and Recurrent Deep Learning Machines Yichuan Gui 9:30am Thursday, 16 May 2013, ITE 325b, UMBC...
http://www.csee.umbc.edu/2013/05/phd-proposal-training-neural-networks-and-recurrent-deep-learning-machines/
https://dev.my.umbc.edu/api/v0/pixel/news/29285/guest@my.umbc.edu/4cb3779e190eb3112965497ef5015a3b/api/pixel
computer-science
defense
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 10 May 2013 08:30:07 -0400
MS defense: Social Media Analytics: Digital Footprints, 5/13

MS Defense
Social Media Analytics: Digital Footprints
Sandhya Krishnan
9:00am Monday, 13 May 2013, ITE325b
In this work we describe an approach to distinguish real and impostor/ compromised accounts on social media. Compromising a user's social media account is not only a breach of security, but can also lead to dissemination of misinformation at a fast pace on social media. There have been several such high profile attacks recently, including on Twitter feeds of AP, CBS, and Delta Airlines. A fake account for the Prime Minister's Office in India was used to spread malicious rumors last year. Our approach builds a profile or footprint of users using both the content of their tweets and the structure of their network. We analyze the real time content of users (Tweets, Facebook posts, etc.) and compare them with information about the user from reliable sources on the Web (e.g., newspapers, news channels, etc.) in order to compute a similarity metric between content from the two sources. We also compute a metric based on the social network analysis of the users: who connects to them, who they are connected with, and how central they are in their network. We have shown how such an approach can easily detect fake accounts for not just well known people such as President Obama, but also for lesser known people and organizations. We also show promising initial results on how this approach can be used to detect an account which has been hacked.
Committee: Anupam Joshi (chair), Tim Finin, Tim Oates, Ponnurangam Kumaraguru (IIIT Delhi)
]]>
MS Defense Social Media Analytics: Digital Footprints Sandhya Krishnan 9:00am Monday, 13 May 2013, ITE325b In this work we describe an approach to distinguish real and impostor/...
http://www.csee.umbc.edu/2013/05/ms-defense-social-media-analytics-digital-footprints-513/
https://dev.my.umbc.edu/api/v0/pixel/news/29198/guest@my.umbc.edu/0dccbabde2bafe067668dc51e583fde1/api/pixel
computer-science
cybersecurity
defense
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 08 May 2013 21:32:10 -0400
Rick Forno gives CISPA Guest Lecture
On May 7, 2013, Dr. Richard Forno, Assistant Director of UMBC's Center for Cybersecurity and Director of UMBC's Graduate Cybersecurity Program, conducted an invited talk on the proposed Cybersecurity Information Sharing and Protection Act (CISPA) and moderated a discussion about general cybersecurity issues to UMBC's Delta Sigma Theta Sorority. The evening event was the second in a series of invited guest speakers as part of the Sorority's May Week festivities.
CISPA is a proposed law that would allow and encourage the sharing of Internet traffic information between the U.S. government and technology and manufacturing companies in order to help US government agencies investigate cyber threats and ensure the security of networks against cyberattacks.
Delta Sigma Theta Sorority, Inc. is a private, non-profit organization whose purpose is to provide assistance and support through established programs in local communities throughout the world. A sisterhood of more than 200,000 predominately Black college educated women, the Sorority currently has over 900 chapters located in the United States, England, Japan (Tokyo and Okinawa), Germany, the Virgin Islands, Bermuda, the Bahamas and the Republic of Korea.
]]>
On May 7, 2013, Dr. Richard Forno, Assistant Director of UMBC's Center for Cybersecurity and Director of UMBC's Graduate Cybersecurity Program, conducted an invited talk on the proposed...
http://www.csee.umbc.edu/2013/05/cispa-guest-lecture/
https://dev.my.umbc.edu/api/v0/pixel/news/29187/guest@my.umbc.edu/76b39533a95c9a9cccd9bf556b0c820c/api/pixel
cybersecurity
events
faculty-and-staff
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
1
true
Wed, 08 May 2013 12:36:38 -0400
Wed, 08 May 2013 12:36:38 -0400
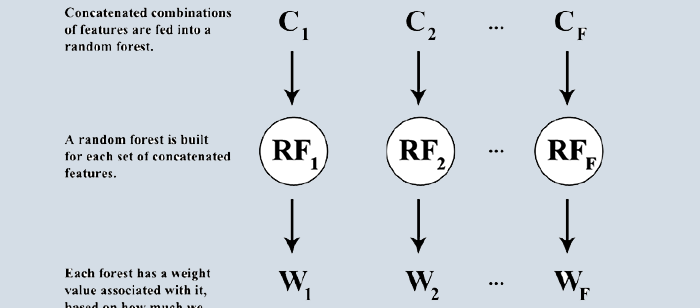
PhD proposal: Rapidly Deployable Image Classification System Using Multi-Views
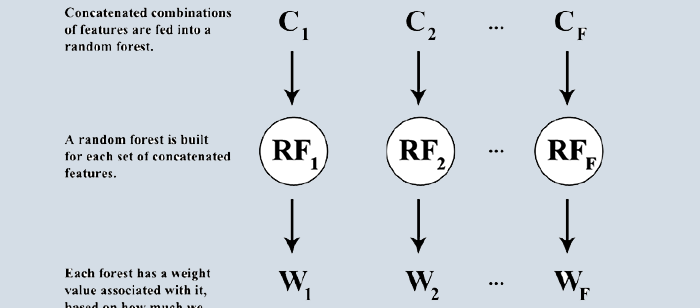
Ph.D. Dissertation Proposal
A Rapidly Deployable Image
Classification System Using Multi-Views
Adrian Rosebrock
11:00am Friday, 10 May, ITE 325, UMBC
Constructing an image classification system using strong, local invariant descriptors is time consuming and tedious, requiring many experimentations and parameter tuning to obtain an adequately performing model. Furthermore, training a system in a given domain and then migrating the model to a separate domain will likely yield poor performance. As computer vision systems become more prevalent in the academic, government, and private sectors, it is paramount that a framework to more easily construct these classification systems be created. In this work we present a rapidly deployable image classification system using multi-views, where each view consists of a set of weak global features. These weak global descriptors are computationally simple to extract, intuitive to understand, and require substantially less parameter tuning than their local invariant counterparts. We demonstrate that by combining weak features with ensemble methods we are able to outperform the current state-of-the-art methods or achieve comparable accuracy. Finally, we provide a theoretical justification for our ensemble framework that can be used to construct rapidly deployable image classification systems called "Ecosembles".
Committee: Dr. Tim Oates (chair), Dr. Jesus Caban, Dr. Tim Finin, Dr. Charles Nicholas
]]>
Ph.D. Dissertation Proposal A Rapidly Deployable Image Classification System Using Multi-Views Adrian Rosebrock 11:00am Friday, 10 May, ITE 325, UMBC Constructing an image classification...
http://www.csee.umbc.edu/2013/05/phd-proposal-rapidly-deployable-image-classification-system-using-multi-views/
https://dev.my.umbc.edu/api/v0/pixel/news/29084/guest@my.umbc.edu/d17c2aaaee61c9de6e0bba78da1d65f4/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 07 May 2013 01:14:10 -0400
MS defense: A Hybrid CPU/GPU Pipeline Workflow System

MS Thesis Defense
A Hybrid CPU/GPU Pipeline Workflow System
Tim Blattner
11:45am Thurday, 25 April 2013, ITE 325b, UMBC
Heterogeneous architectures can be problematic to program on, particularly when trying to schedule tasks on all available compute resources, overlapping PCI express transfers, and managing the limited memory available on the architectures. In this thesis we propose a workflow system that is capable of scheduling on all available compute resources, overlaps PCI express transfers, and manages the limited memory. A procedure for creating the workflow system is described and two case studies are analyzed.
- Image Stitching, which implements the workflow system and achieves two orders of magnitude speedup over an image stitching plugin found in the popular Fiji ImageJ application. Implementing the image stitching algorithm without the workflow system yielded only one order of magnitude speedup over the image stitching plugin.
- Out of Core LU Decomposition, which does not implement the workflow system. This case study demonstrates the impact of the PCI express on a problem with a large number of dependencies. A proposed workflow system for this algorithm is provided in Future Work.
Using the workflow system, programmers have a method for scheduling any algorithm on all available compute resources and is capable of hiding the I/O impact by overlapping computation with I/O.
Committee Members: Milton Halem, Yelena Yesha, Shujia Zhou, John Dorband, Walid Keyrouz
]]>
MS Thesis Defense A Hybrid CPU/GPU Pipeline Workflow System Tim Blattner 11:45am Thurday, 25 April 2013, ITE 325b, UMBC Heterogeneous architectures can be problematic to program on,...
http://www.csee.umbc.edu/2013/04/ms-defense-a-hybrid-cpugpu-pipeline-workflow-system/
https://dev.my.umbc.edu/api/v0/pixel/news/28228/guest@my.umbc.edu/6ee61e680648dce65e5b2a16ed35dcc7/api/pixel
computer-science
defense
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 25 Apr 2013 09:14:49 -0400
Sun, 21 Apr 2013 09:14:49 -0400