PhD Defense: Yasaman Haghpanah
Ph.D. Dissertation Defense
A Trust and Reputation Mechanism Through
Behavioral Modeling of Reviewers
Yasaman Haghpanah
11:00am Tuesday 21 August 2012, ITE 325b, UMBC
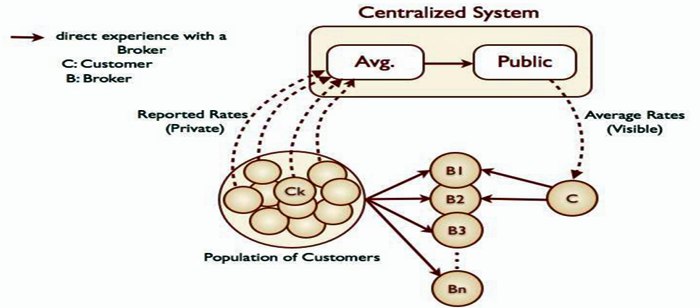
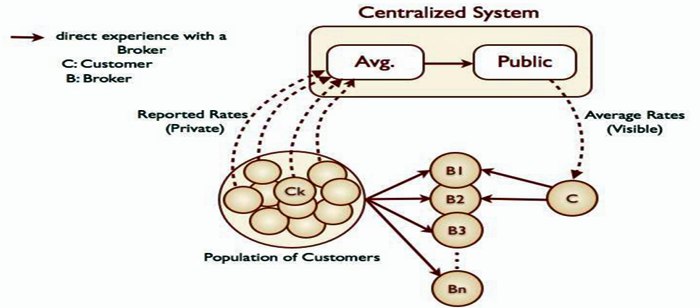
Trust and reputation have become important topics in various domains, such as online markets, supply chain management, auctions, social networks, and e-commerce applications. With the significant increase in transactions with people and organizations especially in online markets, people need to interact with strangers with whom they have little or no previous interactions. Reputation information as a form of world of mouth in auctions and supply chain management and as a form of provided reviews and ratings on online websites are two different sources for modeling trust and reputation in order to mitigate the risk of not knowing a stranger before actually start interacting with that stranger.
In providing reputation information, people can have different behavior, such as being biased based on incentives or they can have different preferences and viewpoints. In this dissertation, I introduce a novel trust and reputation mechanism that models and learns a reputation provider’s behavior based on probability theory. This learned behavior is then used to re-interpret the reputation information, thus making use of the entire reputation data effectively, even if they are biased or based on personal viewpoints and preferences.I show the importance of learning the behavior of reputation providers using different patterns of being biased or having different preferences and satisfaction thresholds in three different settings of game-theory, an online rating website, and an online marketplace. My results show that learning the behavior of reputation providers in all three above settings helps individuals to more effectively aggregate and adjust reputation information in order to make decisions, thereby increasing their satisfaction and overall payoffs in their interactions.
Committee: Drs. Marie desJardins (Chair), Tim Oates, Tim Finin, Wolfgang Ketter and David Aha
]]>
Ph.D. Dissertation Defense A Trust and Reputation Mechanism Through Behavioral Modeling of Reviewers Yasaman Haghpanah 11:00am Tuesday 21 August 2012, ITE 325b, UMBC Trust and reputation...
http://www.csee.umbc.edu/2012/08/phd-defense-yasaman-haghpanah/
https://dev.my.umbc.edu/api/v0/pixel/news/15986/guest@my.umbc.edu/eeb10eebcd8f9bad96b5d62e427ee4cd/api/pixel
computer-science
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Tue, 14 Aug 2012 20:48:06 -0400
PhD dissertation proposal: Albert Kir
PhD Dissertation Preliminary Examination
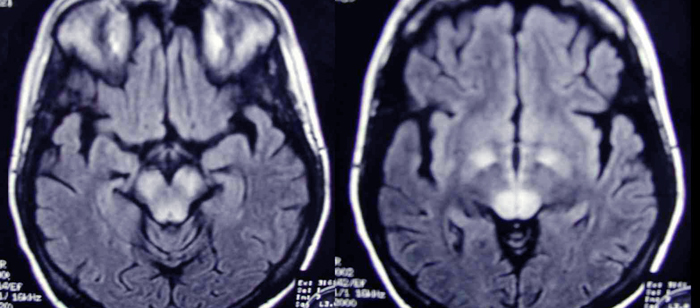
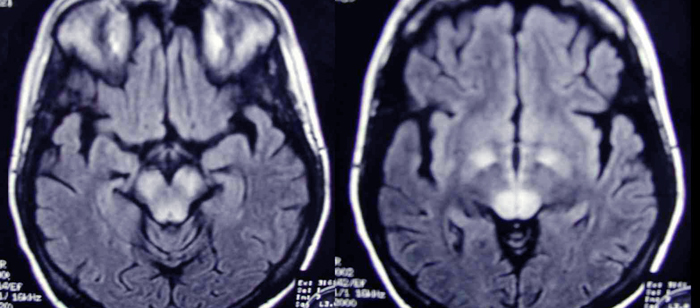
On Optimizing Contrast Quality and Acquisition Time of
SSFP-Sequence-Based techniques for Structural and Functional
MR Imaging via Extended Phase Graph (EPG) Analysis
Albert Kir
1:00pm Wednesday, 15 August 2012, ITE 325b
The extended phase graph (EPG) formalism provides an excellent description of the magnetization evolution (considering the magnetization as a vector quantity in space and its change through time) for steady-state free precession techniques (sequences). This dissertation demonstrates its accuracy by applying it to analyze/optimize structural and functional magnetic resonance imaging. An optimization framework for a structural imaging technique, Magnetization-Prepared RApid Gradient-Echo (MP-RAGE), based on the EPG algorithm is established for obtaining optimal images with respect to image signal strength, contrast, and acquisition time. In addition, a functional imaging technique, True Fast Imaging with Steady-state Precession (TruFISP) with improved quantitative sensitivity is developed using EPG analysis.
Committee: Drs. Joel M. Morris (chair and co-advisor), Alan McMillan (co-advisor), Rao Gullapalli (co-advosor), Janet Rutledge and Tulay Adali
]]>
PhD Dissertation Preliminary Examination On Optimizing Contrast Quality and Acquisition Time of SSFP-Sequence-Based techniques for Structural and Functional MR Imaging via Extended Phase...
http://www.csee.umbc.edu/2012/08/phd-dissertation-proposal-albert-kir/
https://dev.my.umbc.edu/api/v0/pixel/news/15979/guest@my.umbc.edu/c5ee20fe3b02b7c207cd812ebfe93e3a/api/pixel
electrical-engineering
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Tue, 14 Aug 2012 09:32:43 -0400
IEEE Colloquium on Energy Harvesting Devices, September 25
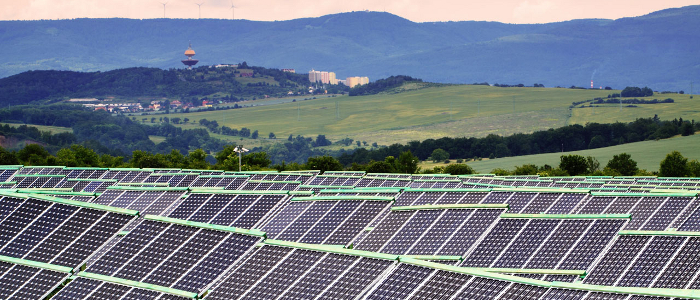
The IEEE Baltimore Electron Devices Society chapter, in collaboration with ARL, will be hosting a one day Colloquium on Energy Harvesting Devices at the University of Maryland, College Park on Tuesday, September 25, 10 a.m. to 5 p.m. in the Stamp Student Union Building, Benjamin Banneker Room (Room 2212).
Invited speakers include:
Dr. Edward Shaffer, Army Research Laboratory
Prof. Vikram Dalal, Iowa State University
Prof. Santosh Kurinec, Rochester Institute of Technology
Dr. James Horwitz, Dept. of Energy (DOE)
Prof. Edward Yu, University of Texas,Austin
Prof. Rajendra Singh, Univ. of South Carolina
Prof. Agis IliadisUniv. of MD, College Park
Panel discussion on paths to reliable, efficient and low cost solar cell development (Dr. Anu Kaul/NSF, Chair, Dr. Mike Wraback ARL, Mr. Scott Stephens, DOE).
Attendance is free. To register, please contact: Dr. Naresh C. Das (Sorry, you need javascript to view this email address. ) or Dr. Victor Veliadis (Sorry, you need javascript to view this email address. )
For more information, visit the website and download the flyer.
]]>
The IEEE Baltimore Electron Devices Society chapter, in collaboration with ARL, will be hosting a one day Colloquium on Energy Harvesting Devices at the University of Maryland, College Park on...
http://www.csee.umbc.edu/2012/08/ieee-colloquium-on-energy-harvesting-devices-september-25/
https://dev.my.umbc.edu/api/v0/pixel/news/15976/guest@my.umbc.edu/e6f5a3ee24e38b891ee3d0786ecba57b/api/pixel
army-research-laboratory
college-park
department-of-energy
energy
events
ieee
news
research
solar
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Tue, 14 Aug 2012 08:43:08 -0400
Tue, 14 Aug 2012 08:43:08 -0400
Dinghade MS defense: Approach to Unwrap a 3D Fingerprint to a 2D Equivalent

MS Defense
Approach to Unwrap a 3D Fingerprint to a 2D Equivalent
Ravikiran Dighade
10:00am Thursday, 2 August 2012, ITE 352
Fingerprints are the most widely used biometric feature for human identification because of their accuracy and uniqueness. Traditional fingerprint acquisition techniques are contact based and result in poor quality images. The new generation of non-contact based scanners captures high resolution and detailed 3D fingerprint scan, which addresses many of the problems of traditional fingerprint acquisition techniques. The majority of existing fingerprint databases available today are 2D, so there is a need for backward compatibility for the 3D scans captured. In order to solve this interoperability issue, I present an algorithm to unwrap the 3D fingerprint to its 2D equivalent image to be able used in an Automatic Fingerprint Identification System.
Program Committee: Drs. Marc Olano (Advisor, Chair), Penny Rheingans and Dr. Gymama Slaughter
]]>
MS Defense Approach to Unwrap a 3D Fingerprint to a 2D Equivalent Ravikiran Dighade 10:00am Thursday, 2 August 2012, ITE 352 Fingerprints are the most widely used biometric feature for...
http://www.csee.umbc.edu/2012/08/dinghade-ms-defense-approach-to-unwrap-a-3d-fingerprint-to-a-2d-equivalent/
https://dev.my.umbc.edu/api/v0/pixel/news/15853/guest@my.umbc.edu/ffb0072dbcfe5061fe4e821c53439df5/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
1
true
Wed, 01 Aug 2012 16:52:24 -0400
Wed, 01 Aug 2012 16:52:24 -0400
talk: Mountain on the DoD Advanced Computing Systems Research Program
COLLOQUIUM
Computer Science and Electrical Engineering
University of Maryland, Baltimore County
The Advanced Computing Systems Research Program
David J. Mountain
Technical Director, Center for Exceptional Computing
1:00pm Friday, 7 September 2012, ITE 227, UMBC
The Advanced Computing Systems (ACS) Research Program recently relocated from Adelphi, Maryland, to the Research Park complex next to UMBC. What type of computing research does ACS focus on? How is it organized? What opportunities for collaboration exist for UMBC? This talk will provide answers to these questions, explain how ACS tackles its research challenges, and provide a sneak preview of upcoming ACS presentations on specific research projects.
David J. Mountain is the Technical Director at the Center for Exceptional Computing (CEC), a Department of Defense research laboratory in the UMBC Research Park. The mission of the CEC is to collaborate with industry, academia, and the government to drive innovative research that will impact advanced computing systems at the multi-petaflop scale and beyond. His responsibilities include directing research activities in technical thrusts including power efficiency, chip IO, system level interconnects, file system IO, productivity, and resilience.
Mr. Mountain’s personal research projects have included radiation effects studies, hot carrier reliability characterization, and chip-on-flex process development utilizing ultra-thin circuits. He has been actively involved with 3D electronics research for nearly two decades. Mr. Mountain is the author of seven papers, has been awarded eight patents, and is a Senior Member of the IEEE.
Host: Yaacov Yesha, Sorry, you need javascript to view this email address.
Directions and more information on recent and upcoming talks.
]]>
COLLOQUIUM Computer Science and Electrical Engineering University of Maryland, Baltimore County The Advanced Computing Systems Research Program David J. Mountain Technical Director,...
http://www.csee.umbc.edu/2012/08/talk-mountain-on-the-dod-advanced-computing-systems-research-program/
https://dev.my.umbc.edu/api/v0/pixel/news/15851/guest@my.umbc.edu/fb11a2240c59c3787756958d2943ede2/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 01 Aug 2012 15:41:58 -0400
Wed, 01 Aug 2012 15:41:58 -0400
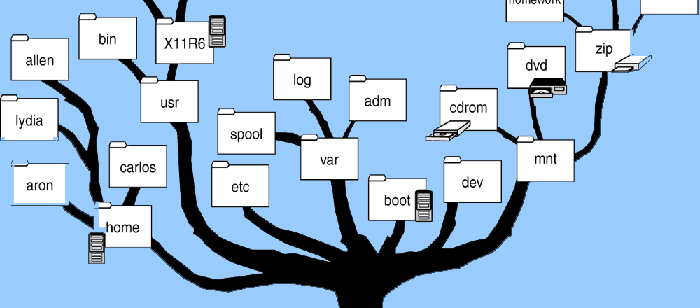
Venkatesh MS defense: Dynamically Reconfigurable Layered Filesystem
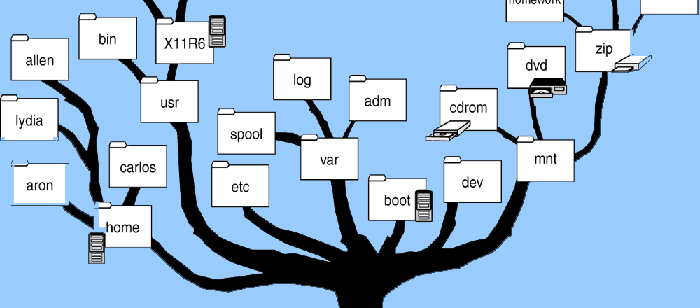
MS Thesis defense
Dynamically Reconfigurable Layered Filesystem
Sunil Venkatesh
10:00am Thursday, 26 July 2012, ITE 325b
Traditionally, all files and directories in Linux and UNIX-like systems have been organized in a hierarchical fashion under the root directory “/” adhering to the Filesystem Hierarchy Standard (FHS). Although there is sufficient flexibility in how the filesystem hierarchy is structured given it satisfies the FHS, there is little straightforward means to customize the filesystem structure to suit an individual user’s or a set of users’ needs without affecting rest of the users on a shared system. Our approach aims to eliminate such a restriction by providing isolated environments to individual users with the help of data being organized in the form of layers. Such an environment also provides an important advantage from security perspective by reducing the risk involved in unwarranted access to files by carefully choosing the layers a user has access. Maintainability at the layer level is another key advantage of our approach over the fine-grained approach of dealing with individual files.
Committee: Drs. John Dorband (Chair), Yelena Yesha, Mohamed Younis
]]>
MS Thesis defense Dynamically Reconfigurable Layered Filesystem Sunil Venkatesh 10:00am Thursday, 26 July 2012, ITE 325b Traditionally, all files and directories in Linux and...
http://www.csee.umbc.edu/2012/07/venkatesh-ms-defense-dynamically-reconfigurable-layered-filesystem/
https://dev.my.umbc.edu/api/v0/pixel/news/15765/guest@my.umbc.edu/f6300f00b14c7083febe37e457f6a6ab/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
6
0
true
Tue, 24 Jul 2012 13:20:26 -0400
MS thesis defense: Abbas on Federating Disjoint Wireless Networks Using a Mix of Stationary and Mobile Nodes
MS Thesis Defense
Federating Disjoint Wireless Networks
Using a Mix of Stationary and Mobile Nodes
Ahmad Abbas
12:00PM Thursday 26th July 2012, Room ITE 325b
In many applications need arises to connect a set of disjoint nodes or segments. Examples include repairing a partitioned network topology after failure, federating a set of standalone networks to serve an emerging event, and connecting a sparsely located data sources. Contemporary solutions either deploy stationary relay nodes (RN) to form data paths or employ one or multiple mobile data collectors (MDCs) that pick packets from sources and transport them to destinations. In this thesis we investigate the interconnection problem when the number of available RNs is insufficient for forming a stable topology and a mix of RNs and MDCs is to be used. We present two algorithms for determining where the RNs are to be placed and planning optimized travel routes for the MDCs so that the data delivery latency as well as the MDC motion overhead are minimized. The performance of the algorithm is validated through simulation.
Committee: Professors Mohamed Younis (chair), Ryan Robucci and Tinoosh Mohsenin
]]>
MS Thesis Defense Federating Disjoint Wireless Networks Using a Mix of Stationary and Mobile Nodes Ahmad Abbas 12:00PM Thursday 26th July 2012, Room ITE 325b In many applications...
http://www.csee.umbc.edu/2012/07/ms-thesis-defense-abbas-on-federating-disjoint-wireless-networks-using-a-mix-of-stationary-and-mobile-nodes/
https://dev.my.umbc.edu/api/v0/pixel/news/15700/guest@my.umbc.edu/93e45aa40e95668e2124bd1b12f582de/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Tue, 17 Jul 2012 14:22:19 -0400
Chandrasekaran MS Defense: MIMO Channel Modeling and Capacity Using the Channel Correlation Matrix
MS Thesis Defense
On MIMO Channel Modeling and Capacity
Using the Channel Correlation Matrix
Anush Chandrasekaran
1:00pm Wednesday, 18 July 2012, ITE 325b
Communication systems have always been affected by multipath propagation that causes a delay and distortion in receiving the signal, with a different delay for each path. Multiple-Input Multiple-Output (MIMO) communication systems were developed to combat this problem and use multipath propagation to their benefit. A MIMO communication system contains M transmitter antennas and N receiver antennas that are used to improve either the robustness of transmission or the throughput.
We assume an exponential channel correlation matrix R model for the MIMO channel with J = M = N and use it to compute the channel H-matrix, the receiver (RRx) and transmitter (RTx) correlation matrices, and the ergodic MIMO channel capacity (CH). We propose two algorithms to obtain RRx and RTx from R, which have been used to estimate/bound CH. We investigate and compare three ergodic MIMO channel capacity estimation/bound methods for our MIMO channel model in this thesis. The first two existing estimation/bound methods use the Kronecker model and an RRx-based bound, respectively. The third method is a novel method we propose and study to estimate the ergodic MIMO channel capacity using specific eigenvalues of RRx. The behavior of the eigenvalues of R and RRx are analyzed to identify the eigenvalues that can be used in this method. This method achieves less relative-error compared to the RRx-based bound. It is better than the Kronecker model for specific values of J and the correlation parameter r.
Committee: Drs. Joel M. Morris (Chair), E. F. Charles LaBerge, Mohamed Younis and Tinoosh Mohsenin
]]>
MS Thesis Defense On MIMO Channel Modeling and Capacity Using the Channel Correlation Matrix Anush Chandrasekaran 1:00pm Wednesday, 18 July 2012, ITE 325b Communication systems have...
http://www.csee.umbc.edu/2012/07/chandrasekaran-ms-defense-mimo-channel-modeling-and-capacity-using-the-channel-correlation-matrix/
https://dev.my.umbc.edu/api/v0/pixel/news/15692/guest@my.umbc.edu/bebd3f9f2fc3d9322c809ce7c97d48e7/api/pixel
electrical-engineering
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
3
true
Tue, 17 Jul 2012 09:29:26 -0400
Kugaonkar MS defense: Finding Associations among SNPs for Prostate Cancer

MS Thesis Defense
Finding associations among SNPs for
prostate cancer using collaborative filtering
Rohit Kugaonkar
9:00am Wed. 18 July 2012, Room ITE 325b
Prostate cancer is the second leading cause of cancer related deaths among men. Because of the slow growing nature of prostate cancer, sometimes surgical treatment is not required for less aggressive cancers. Recent debates over prostate-specific antigen (PSA) screening have drawn new attention to prostate cancer. Due to the complicated nature of prostate cancer, studying the entire genome is essential to find genomic traits. Due to the high cost of studying all Single Nucleotide Polymorphisms (SNPs), it is essential to find tag SNPs which can represent other SNPs. Earlier methods to find tag SNPs using associations between SNPs either use SNP's location information or are based on data of very few SNP markers in each sample. Our study is based on 2300 samples with 550,000 SNPs each. We have not used SNP location information or any predefined standard cut-offs to find tag SNPs. Our approach is based on using collaborative filtering methods to find pair wise associations among SNPs and thus list top-N tag SNPs. We have found 25 tag SNPs which have highest similarities to other SNPs. In addition we found 16 more SNPs which have high correlation with the known high risk SNPs that are associated with prostate cancer. We used some of these newly found SNPs with 5 different classification algorithms and observed some improvement in prediction accuracy over using the original known high risk SNPs. The classifier can be used in a decision to perform further testing in case of a "yes" answer by the classifier.
Committee: Drs. Yelena Yesha (chair), Anupam Joshi, Aryya Gangopadhyay and Micheal Grasso.
]]>
MS Thesis Defense Finding associations among SNPs for prostate cancer using collaborative filtering Rohit Kugaonkar 9:00am Wed. 18 July 2012, Room ITE 325b Prostate cancer is the second...
http://www.csee.umbc.edu/2012/07/ms-defense-kugaonkar-on-finding-associations-among-snps-for-prostate-cancer/
https://dev.my.umbc.edu/api/v0/pixel/news/15646/guest@my.umbc.edu/6115b70a9ca944e5cb14385fe25c6bdf/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 11 Jul 2012 17:30:07 -0400
Wed, 11 Jul 2012 17:30:07 -0400
Ph.D. defense: Fatih Senel on Relay Node Placement for Federating Segmented Wireless Sensor Networks

Ph.D. Dissertation Defense
Relay Node Placement for
Federating Segmented Wireless Sensor Networks
Fatih Senel
2:00pm Tuesday, 10 July 2012, ITE 325b
Recent years have witnessed a growing interest in the applications of Wireless Sensor Networks (WSNs). Most notable among these applications are those operating in hostile environments space exploration, border protection, combat field reconnaissance, and search and rescue. Due to the harsh surroundings, WSNs may suffer from a large scale damage that causes many nodes to fail simultaneously and the network to get partitioned into multiple disjoint segments and its services become very limited. In such a case, restoring the network connectivity is very important in order to avoid negative effects on the applications. Linking disjoint segments may not be feasible through coordinated repositioning of some set of nodes as the scope of the damage is so wide that cannot be determined. One of the viable solutions for federating damaged WSNs is to deploy additional resources, i.e. relay nodes, to form inter-segment multi-hop paths.
In this dissertation, we tackle technical challenges related to the federation of segmented WSNs. We present a set of effective techniques that for repairing the damaged WSN using the least number of relay nodes (RNs) as well as maintaining some desirable topology features such as robustness against failures, network coverage and balanced traffic load. The correctness and time-complexity of all proposed approaches are analyzed and their performance is validated through extensive simulation experiments.
Committee: Drs. Mohamed Younis (Chair), Charles Nicholas, Samuel Lomonaco, Tim Oates, Kemal Akkaya and Waleed Youssef
]]>
Ph.D. Dissertation Defense Relay Node Placement for Federating Segmented Wireless Sensor Networks Fatih Senel 2:00pm Tuesday, 10 July 2012, ITE 325b Recent years have witnessed a growing...
http://www.csee.umbc.edu/2012/06/ph-d-defense-fatih-senel-on-relay-node-placement-for-federating-segmented-wireless-sensor-networks/
https://dev.my.umbc.edu/api/v0/pixel/news/15419/guest@my.umbc.edu/4279eaff2f2561c6632926da0cd2fa93/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
true
Mon, 25 Jun 2012 09:19:11 -0400