MS defense: More on Situation Aware Intrusion Detection, 9am Fri 4/27

MS Thesis Defense
Situation Aware Intrusion Detection Model
Sumit More
9:00am Friday, 27 April 2012, ITE 346, UMBC
Today, information technology and cyber-services have become the foundation pillars of every business and manufacturing industry. The importance of cyber-services and their extensive use by every section of the society has paved the way for cyber-crimes like espionage, politically motivated attacks, credit card frauds, unauthorized infrastructure access, denial-of-service attacks, and stealing of valuable data. Intrusion Detection Systems (IDS) are applications which monitor cyber-systems to identify any malicious activities, generate an alert when such an activity is detected, and redress the problem if possible. Most of the intrusion detection/prevention systems available today are based on rule-based or signature based activity monitoring which detect threats and vulnerabilities by cross-referencing the threat or vulnerability signatures in their databases. These Intrusion Detection Systems (IDS) face limitations in detecting newly published attacks or variants of existing attacks. They are also point solutions that focus on a single system/component.
We argue that integrating information coming from multiple data channels can lead to a better threat detection model. Data source of web including blogs, chat-rooms, forums etc. can be a good source of information for upcoming attacks or attacks whose signatures have not yet been tracked for the intrusion detection systems to catch. Semantic integration of the data sources from web, information from IDS/IPS modules at the network and host level, and the expert knowledge can be used to create a ‘Situation Aware Intrusion Detection Model’ which can lead to better intrusion detection and prevention results. In this work, we present such a system which makes use of semantic web technologies to find relationships between the information gathered from the web, sensor data coming from IDS/IPS modules and network activity monitors, and reasons over this data and expert provided rules in-order to detect possibility of a cyber attack.
Thesis Committee: Professors Anupam Joshi (chair), Tim Finin and Yelena Yesha
]]>
MS Thesis Defense Situation Aware Intrusion Detection Model Sumit More 9:00am Friday, 27 April 2012, ITE 346, UMBC Today, information technology and cyber-services have become the...
http://www.csee.umbc.edu/2012/04/ms-defense-more-on-situation-aware-intrusion-detection-9am-fri-427/
https://dev.my.umbc.edu/api/v0/pixel/news/14691/guest@my.umbc.edu/9e2c7702b9843e0f817d9330d209d566/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 26 Apr 2012 18:18:50 -0400
talk: Todros on Canonical Correlation Analysis, 2pm Wed 5/2
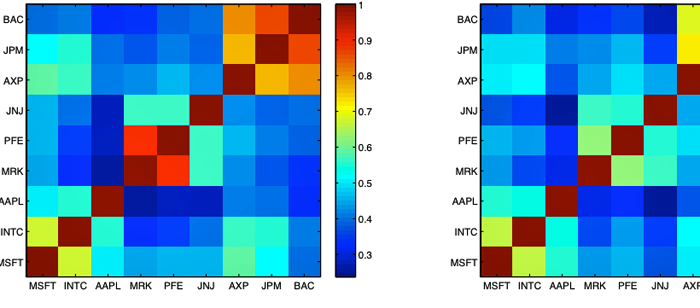
On Measure Transformed Canonical Correlation Analysis
Dr. Koby Todros, University of Michigan
2:00pm Wednesday, 2 May 2012, ITE 325b
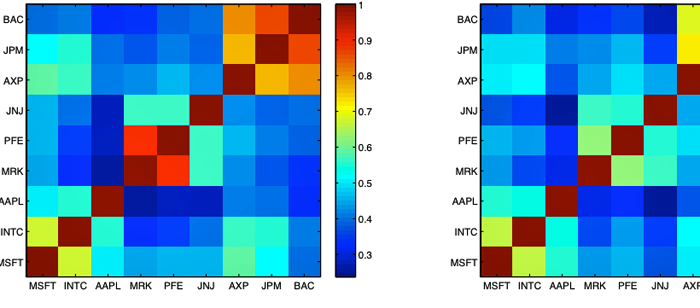
In this work linear canonical correlation analysis (LCCA) is generalized by applying a structured transform to the joint probability distribution of the considered pair of random vectors, i.e., a transformation of the joint probability measure defined on their joint observation space. This framework, called measure transformed canonical correlation analysis (MTCCA), applies LCCA to the data after transformation of the joint probability measure. We show that judicious choice of the transform leads to a modified canonical correlation analysis, which, in contrast to LCCA, is capable of detecting non-linear relationships between the considered pair of random vectors. Unlike kernel canonical correlation analysis, where the transformation is applied to the random vectors, in MTCCA the transformation is applied to their joint probability distribution. This results in performance advantages and reduced implementation complexity. The proposed approach is illustrated for graphical model selection in simulated data having non-linear dependencies, and for measuring long-term associations between companies traded in the NASDAQ and NYSE stock markets.
Koby Todros was born in Ashkelon, Israel, in 1974. He received his B.Sc., M.Sc., and Ph.D. degrees in electrical engineering at 2000, 2006, and 2011, respectively, from the Ben-Gurion University of the Negev. He is currently a post-doctoral fellow with the Department of Electrical Engineering and Computer Science, in the University of Michigan. His research interests include statistical signal processing and estimation theory with focus on association analysis, uniformly optimal estimation in the non-Bayesian theory, performance bounds for parameter estimation, blind source separation, and biomedical signal processing.
]]>
On Measure Transformed Canonical Correlation Analysis Dr. Koby Todros, University of Michigan 2:00pm Wednesday, 2 May 2012, ITE 325b In this work linear canonical correlation analysis (LCCA)...
http://www.csee.umbc.edu/2012/04/talk-todros-on-canonical-correlation-analysis-2pm-wed-52/
https://dev.my.umbc.edu/api/v0/pixel/news/14683/guest@my.umbc.edu/b816eb65a9fde4f69f08f899eba23a8b/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 26 Apr 2012 14:44:21 -0400
UMBC Digital Entertainment Conference, 10-4 Sat 4/28, LH1

The Sixth UMBC Digital Entertainment Conference (DEC) will be held this Saturday, April 28 from 10:00am to 4:00pm in LH1 in the Biological Sciences building.
Every year since 2007 the students ofn the UMBC Game Developer's Club has organized the conference and invited speakers from the videogames industry to come in and discuss important topics in the games industry. DEC 2012 is sponsored by Zynga, the studio that developed Farmville and many other Facebook games. One of the strenghts of the UMBC program in Graphics, Animation and Interactive Media (GAIM) is its strong ties to game development studios in the Maryland, DC and Northern Virginia area.
The 2012 DEC is open to anyone, and features an all-star lineup of speakers from Firaxis Games, Zynga East, Pure Bang, and Mythic Entertainment. Whether you are a high school student, go to UMBC or another university, or are already working in a different industry, you are sure find interesting information about how the games industry works, how some current developers got started, and what they do. If you are a game developer, you are sure to find high school students, UMBC students and students from other universities who are interested in jobs in the games industry.
Here is the schedule.
10:00am – Barry Caudill, Director of Gameplay Development at Firaxis
11:00am – Tim Train, Studio Manager at Zynga East
12:00pm – Lunch Break
1:00pm – Eric Jordan, Programmer at Firaxis
2:00pm – Ben Walsh, CEO of Pure Bang Games
3:00pm – Brian Johnson, Director of Online Operations at Mythic Entertainment
]]>
The Sixth UMBC Digital Entertainment Conference (DEC) will be held this Saturday, April 28 from 10:00am to 4:00pm in LH1 in the Biological Sciences building. Every year since 2007 the students...
http://www.csee.umbc.edu/2012/04/umbc-digital-entertainment-conference-10-4-sat-428-lh1/
https://dev.my.umbc.edu/api/v0/pixel/news/14520/guest@my.umbc.edu/d834e02b12ca51b75559a4dfce1be721/api/pixel
events
graduate
news
students
talks
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 25 Apr 2012 01:17:20 -0400
MS defense: Distributed Model Consensus for Models of Locally Biased Measurements in Wireless Sensor Networks
MS Thesis Defense
Distributed Model Consensus for Models of Locally
Biased Measurements in Wireless Sensor Networks
Jacob Thompson
4:00pm Wednesday, 25 April 2012, ITE 325B, UMBC
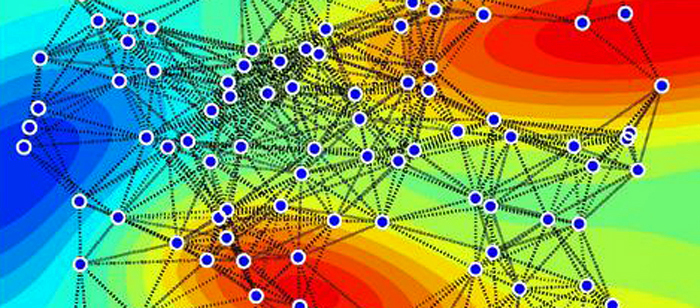
Wireless sensor networks (WSNs) consist of interconnected microsensors, each of which collects measurements from its local environment, which are often used in monitoring and control applications. These applications make inferences about the global and local states of the deployment environment. However, due to the limited communication and energy resources at the sensors, gathering all the raw data at a central fusion/control point is impractical.
Hence, it is essential to have distributed learning and inference in WSNs, such as learning a consensus model from the locally learned models. Consensus is challenging due to the limited resources of the sensors and the inherent bias of the individual sensor models learned from their local sensing environments. Two leading approaches for this problem are the approach by Zheng et al which uses loopy belief propagation on a certain graphical model based on the WSN topology and the local models, and the approach by Xiao et al which relies on gossip averaging of the parameters of the local models.
We focus on multivariate linear regression models, such as Bayesian, Ridge, and Lasso regression models. We analyze and extend the loopy Gaussian belief propagation (GaBP) approach to model consensus, and compare its performance to the gossip averaging approach. We experimentally find that GaBP tends to converge much faster than gossip averaging, but to a less accurate estimated consensus model (especially in the presence of multiple cycles in its corresponding graphical model). We also find that gossip averaging along paths in the WSN, tends to provide much faster convergence to more accurate estimated consensus models as compared to GaBP.
Committee: Professors Kostas Kalpakis (chair), Tim Oates and Yun Peng
]]>
MS Thesis Defense Distributed Model Consensus for Models of Locally Biased Measurements in Wireless Sensor Networks Jacob Thompson 4:00pm Wednesday, 25 April 2012, ITE 325B, UMBC...
http://www.csee.umbc.edu/2012/04/ms-defense-distributed-model-consensus-for-models-of-locally-biased-measurements-in-wireless-sensor-networks/
https://dev.my.umbc.edu/api/v0/pixel/news/14357/guest@my.umbc.edu/b49884a4df67ec8555195bf290cd5aa0/api/pixel
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Mon, 23 Apr 2012 17:49:08 -0400
MS Defense: Shamit Patel on a Working Theory of the Learning Rule for Dendritic Integration
MS Thesis Defense
Towards Implementation of a Pattern Recognition System based on
a Working Theory of the Learning Rule for Dendritic Integration
Shamit Patel
4:00pm Monday 23 April 2012, ITE 346, UMBC
My goal is to develop a working theory of the learning rule for dendritic integration, and to then implement a pattern recognition system based on that learning algorithm so that the algorithm can be evaluated for its generalization ability. In this regard, this thesis presents an implementation of Jeff Hawkins and Dileep George's Hierarchical Temporal Memory (HTM) pattern recognition system that's based on an existing theory of the learning rule for dendritic integration – spike-timing-dependent synaptic plasticity (STDP). The integration of this learning rule is the novel contribution of this thesis. I found that the STDP HTM system achieved much higher probabilistic classification accuracy and better generalization ability than the non-STDP HTM system. Probabilistic classification accuracy is a way of measuring classification accuracy in which a testing pattern is classified correctly if its label appears in the group of labels output by the top-level node of the HTM network.
Committee: Professors Tim Oates (Chair), Yun Peng and Tim Finin
]]>
MS Thesis Defense Towards Implementation of a Pattern Recognition System based on a Working Theory of the Learning Rule for Dendritic Integration Shamit Patel 4:00pm Monday 23 April 2012,...
http://www.csee.umbc.edu/2012/04/shamit-patel-dendritic-integration-pattern-recognition-machine-learning/
https://dev.my.umbc.edu/api/v0/pixel/news/14217/guest@my.umbc.edu/05ba953355971455f0b5d71ed6cb4a6a/api/pixel
computer-science
graduate
news
research
students
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 22 Apr 2012 11:39:41 -0400
PhD defense: DiffServ Assured Forwarded and Robust Header Compression: Performance Analysis
Ph.D. Dissertation Defense
DiffServ Assured Forwarded and Robust
Header Compression: Performance Analysis
Houcheng Lee
12:30pm Monday, 23 April 2012, ITE 201b
Performance analysis of network architecture and protocols can be done by using modeling and simulation or using emulation techniques. Modeling and simulation can be used to obtain qualitative results about a network protocol through building models of protocols under drastic abstractions. One major concern of the modeling approach is the fidelity of the results from a model simulation.
This dissertation presents detailed performance analyses of two major Internet standards using emulation techniques. The standards investigated are Differentiated Services (DiffServ) architecture and Robust Compression (ROHC) standard.
The DiffServ architecture was proposed to support quality of services (QoS) implementation in TCP/IP networks. In the first part of dissertation, a new and scalable approach to performance analysis of DiffServ architecture, based on fluid flow modeling approximation to TCP/UDP based traffic flows, is used to emulate millions of competing TCP and UDP flows across networks of various sizes, complexities and link speeds. The emulation involved real-world network constraints, including traffic prioritizations, limited buffers in routers, link congestion, active queue management (AQM) and packet drop policies on congested links. The results provided first quantitative understanding of the interactions of traffic with different drop precedencies in AF1 class traffic in a congested network.
The Robust Header Compression (ROHC) is proposed to implement efficient IP header compression on bandwidth constrained links in TCP/IP networks. In the second part of dissertation, an emulation tool, called CORE, developed at NRL is used to analyze the performance of ROHC. ROHC compresses packet headers at a sender side, and decompresses them at the receiver side to increase efficiency of a communication link. The results provided quantitative understanding of compression gains from using ROHC standard for compressing IPv4/UDP and IPv6/UDP traffic on links.
Committee:
- Dr. Deepinder Sidhu
- Dr. Yelena Yesha
- Dr. Konstantinos Kalpakis
- Dr. Ted M. Foster
- Dr. Edward Zieglar
]]>
Ph.D. Dissertation Defense DiffServ Assured Forwarded and Robust Header Compression: Performance Analysis Houcheng Lee 12:30pm Monday, 23 April 2012, ITE 201b Performance analysis...
http://www.csee.umbc.edu/2012/04/phd-defense-diffserv-assured-forwarded-and-robust-header-compression-performance-analysis/
https://dev.my.umbc.edu/api/v0/pixel/news/14049/guest@my.umbc.edu/8f5c5de540d5a96633cc1a92aee77364/api/pixel
computer-science
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 19 Apr 2012 23:18:52 -0400
MS defense: Heart Disease Prediction: A Data Mining Approach

Masters Thesis Defense
Heart Disease Prediction: A Data Mining Approach
Soma Das
2:00pm Monday, 23 April 2012, ITE 201B
Data mining is a field of computer science that combines statistical analysis and machine learning to detect hard-to-discern patterns from large amounts of data. It employs different algorithms to learn different patterns from training or experience and apply it to classify, predict or identify patterns. The healthcare environment is very information rich. There is a wealth of clinical data available within the healthcare systems. Also due to recent advancement of genomic research vast amount of genetic data are also available. Effective analysis tools are needed to discover hidden relationships and trends in these data. These tools are necessary to correctly diagnose people at risk of disease based on the derived knowledge from the data.
We used data mining techniques to evaluate the interaction between traditional risk factors and gene variants such as Single Nucleotide Polymorphisms (SNPs) towards Coronary Heart Disease (CHD) susceptibility in a prospective study of older population aged 65 and older. In our thesis we asked two questions whether we can predict CHD at birth or adding genetic information to traditional risk factors predict CHD better than traditional risk factors alone.We also analyzed two popular machine learning algorithms to determine the most efficient method on medical datasets mining. The evaluation is based on a set of performance metrics. We also applied a clustering method to identify different subgroups present in the selected datasets.
We chose eight traditional risk factors of CHD and 23 SNPs that had previously been reported to be associated with CHD. We then tested the association of these SNPs with CHD in cardiovascular Health Study (CHS). Based on previous studies, we pre specified a risk allele for each of 23 SNPs. We assigned coding values for homozygote, heterozygote, and the no risk homozygote SNPs and then combined these with traditional risk factors for each individual before feeding it to machine learning algorithms. We evaluated different classification algorithms using 10 fold cross validation test.
Receiver Operating Characteristic Curves (ROC) were plotted separately based on traditional risk factors alone and traditional risk factors plus SNPs. The increase in the Area Under Curve (AUC) was statistically significant for Whites and suggestive of improved CHD prediction for African American. We also found out that using only SNPs predicts CHD a little bit better than random guessing for only whites. The results gained from analysis suggest Naïve Bayes to be the best classifier for the given domain.
This study demonstrates the concept of using multiple SNPs as independent risk factors and indicates that it can improve prediction of incident CHD. Adding SNPs to traditional risk factors did not improve the prediction model dramatically as we expected but it was statistically significant.
Committee:
- Dr. Michael Grasso (co-chair)
- Dr. Anupam Joshi
- Dr. Yelena Yesha
]]>
Masters Thesis Defense Heart Disease Prediction: A Data Mining Approach Soma Das 2:00pm Monday, 23 April 2012, ITE 201B Data mining is a field of computer science that combines statistical...
http://www.csee.umbc.edu/2012/04/ms-defense-heart-disease-prediction-a-data-mining-approach/
https://dev.my.umbc.edu/api/v0/pixel/news/13996/guest@my.umbc.edu/0e3f11efb1128bb1935237c75a3d8e0a/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 19 Apr 2012 10:02:22 -0400
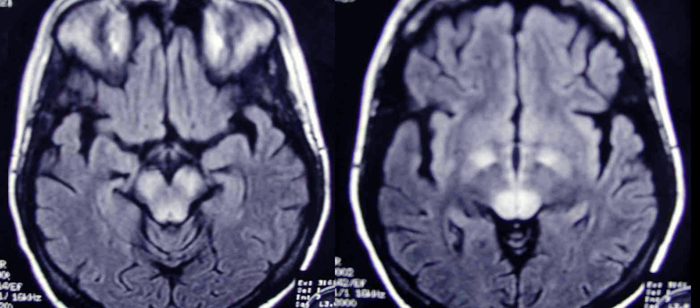
From Proton to Image: A Signal Processing Aspect of MRI
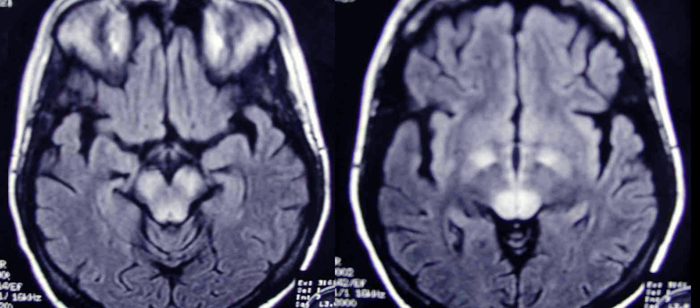
EE Graduate Seminar
From Proton to Image: A Signal Processing Aspect of MRI
Albert Kir
PhD (EE) Student, CSEE Dept/UMBC
11:30am-12:45pm Friday, 20 April 2012, ITE 237
Magnetic Resonance Imaging (MRI) is routinely used in clinical setting for its great diagnosis and prognosis ability, and is a heavily studied research area across multiple disciplines. MRI has its tie with signal and imaging processing community since it stemmed from the study of nuclear magnetic resonance (NMR). The technique of Fourier imaging makes MRI possible through manipulation of the NMR signals. The issue of imaging speed has always been at the heart of functional MRI (fMRI) and interventional imaging, where a high image frame rate is required or preferable. In the past decade, partly owing to the advance in imaging hardware, a wide range of image reconstruction algorithms have been developed to accelerate the image acquisition process. There has been SENSE, SMASH, GRAPPA, and many of their variations in the parallel imaging category from the early days to the current K-T techniques based on compressive sensing (CS). In this talk, the basic imaging principle for MRI will first be presented, and then a discussion of the first parallel imaging technique, SENSE, will be given. Lastly, the use of K-T FOCUSS on fMRI will be demonstrated.
Albert Kir received the BS degree in Computer Engineering n 2005 and the MSEE degree in 2009 from UMBC. He is currently a PhD (EE) student at UMBC. Mr. Kirs current research interest includes optimization of rapid imaging techniques for structural and functional images for MRI.
Host: Prof. Joel M. Morris
]]>
EE Graduate Seminar From Proton to Image: A Signal Processing Aspect of MRI Albert Kir PhD (EE) Student, CSEE Dept/UMBC 11:30am-12:45pm Friday, 20 April 2012, ITE 237 Magnetic Resonance...
http://www.csee.umbc.edu/2012/04/from-proton-to-image-a-signal-processing-aspect-of-mri/
https://dev.my.umbc.edu/api/v0/pixel/news/13924/guest@my.umbc.edu/8d884c71036725e09700de9c77f7d886/api/pixel
electrical-engineering
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 18 Apr 2012 11:14:22 -0400
talk: On Far-End Crosstalk Mitigation in VDSL Systems, 11:30am Fri 4/13, ITE227
EE Graduate Seminar
On Far-End Crosstalk Mitigation in VDSL Systems
Dr. Amitkumar Mahadevan
Ikanos Communications Inc., Red Bank, NJ
11:30am-12:45pm, Friday 13 April 2012, ITE 237, UMBC
Very-high-speed digital subscriber line (VDSL) is a last mile communications access solution that exploits the existing copper infrastructure to deliver high-speed internet access to homes and businesses. Far-end crosstalk (FEXT), i.e., interference seen at a VDSL receiver due to leakage from extraneous transmitters located at the other end (far end) of the line, is by far the most dominant impairment in VDSL. Left untreated, FEXT results in a considerable reduction in the service rates than can be delivered to users, or equivalently, a considerable reduction in the range over which a given service rate can be guaranteed. In this presentation, we will discuss the characteristics of FEXT in DSL systems and techniques employed in the industry to mitigate the impact of FEXT. Substantial attention will be devoted to 'vectoring': a per-frequency active FEXT mitigation scheme involving signal cooperation across different users at the central-office end of the system.
By design, vectoring necessitates the use of a pre-coder for downstream FEXT mitigation and a post-canceller for upstream FEXT mitigation. Low-complexity adaptive schemes for estimating the off-diagonal downstream FEXT pre-coder and the upstream FEXT canceller based on independent minimization of the per-frequency user error variances will be presented. These schemes do not involve any matrix inversion and are shown to achieve almost FEXT-free performance. We will also discuss key features of the recently published G.vector (G.993.5) ITU standard that allows for rapid and non-disruptive estimation of new elements of the pre-coder and canceller matrices when users join the vectored system.
Short Bio: Amitkumar Mahadevan was born in Mumbai, India. He received the B.E. degree in electrical engineering in 1998 from Sardar Patel College of Engineering, Mumbai University, India, and the MSEE degree in 2002 and the Ph.D. (EE) degree in 2005 from UMBC. In 2005, he joined Conexant Systems Inc., Red Bank, NJ, (now Ikanos Communications, Inc.) as a firmware engineer and has worked on advanced technology development for various flavors of DSL communication systems. More recently, he has been working on algorithm development and implementation for active crosstalk cancellation or 'vectoring' in VDSL systems. His research interests include discrete multi-tone and orthogonal frequency-division-multiplexing based communication systems, error correction codes, importance sampling techniques, and quantum information theory.
Host: Prof. Joel M. Morris
More infoformation
]]>
EE Graduate Seminar On Far-End Crosstalk Mitigation in VDSL Systems Dr. Amitkumar Mahadevan Ikanos Communications Inc., Red Bank, NJ 11:30am-12:45pm, Friday 13 April 2012, ITE 237, UMBC...
http://www.csee.umbc.edu/2012/04/talk-on-far-end-crosstalk-mitigation-in-vdsl-systems-1130am-fri-413-ite227/
https://dev.my.umbc.edu/api/v0/pixel/news/13646/guest@my.umbc.edu/2874f978592df7a68606dfefe27ef411/api/pixel
electrical-engineering
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Wed, 11 Apr 2012 15:50:27 -0400
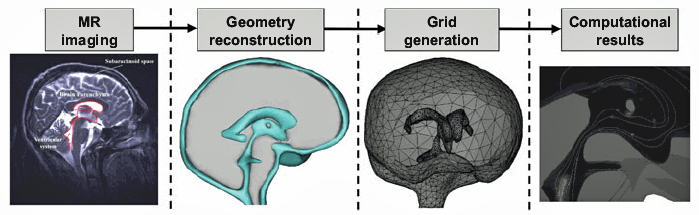
talk: Virtual Human Simulator: Computer-aided Exploration of Human Biology, 1pm Fri 4/13, UMBC
The Virtual Human Simulator:
Computer-aided Exploration of Human Biology
Professor Andreas Linninger
Laboratory for Product and Process Design
University of Illinois at Chicago
1:00pm Friday, 13 April 2012, 227 ITE, UMBC
Engineering has substantially impacted the world by creating material wealth through design of chemical production plants, synthesis of specialty chemicals and pharmaceuticals and sustainable processes for energy and the environment. Systematic engineering methods are also driving a transformation in biomedicine. We will present developments in advanced scientific computing for discovering the fundamental transport and reaction mechanisms in biological systems.
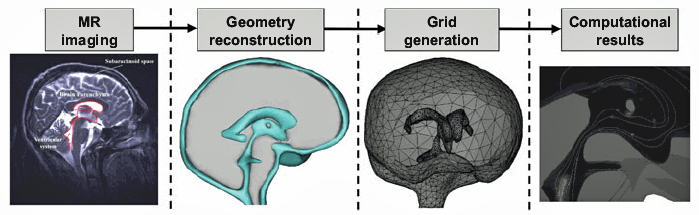
Novel medical imaging modalities open unprecedented views into organ function and cellular chemistry of whole organisms in vivo. The quantitative investigation of spatio-temporal reaction and transport phenomena opens a path for the rational design of drug delivery therapies to specific target areas of the human central nervous system. Image-based computational fluid dynamics (iCFD) will be introduced as a new methodology integrating medical imaging modalities with rigorous transport principles. System dynamics and control theory are centerpieces in the prediction of cerebral hemodynamics towards better treatment options for stroke. Non-linear mathematical programming techniques developed by chemical engineers for large scale process optimization are key to parameter estimation in pharmacokinetic and toxicity studies as well as novel techniques for design optimization of gene therapies. The integration of transport and reaction phenomena with anatomical and physiologically consistent computer models spanning the molecular, cellular through the macroscopic length scales lead us to progressively accurate predictions of metabolic functions in the normal and pathological conditions. Prototype developments of the virtual human simulator to engineer design solution in-silico will be demonstrated. Case studies will illustrate the state-of-the-art in computing cerebral blood flow patterns, computer-aided design of drug administration therapies and physiologically-based pharmacokinetic modeling for new drug leads.
Dr. Andreas A. Linninger is Professor of Chemical Engineering and Bioengineering and Director of the Laboratory for Product and Process Design at the University of Illinois in Chicago. He received Diploma and PhD degrees in Chemical Engineering from the Vienna University of Technology. He received postgraduate training at the Rijksuniversiteit Gent, the University of California at Berkeley and the Massachusetts Institute of Technology. His research interests in process system engineering include computer-aided process synthesis, mathematical modeling of complex systems and design under uncertainty. He has published more than 100 papers on parameter estimation in distributed systems, synthesis of distillative separation networks, integrated design and control, process design for the environment and computational fluid mechanics methods in biological systems.
Host: Yelena Yesha
]]>
The Virtual Human Simulator: Computer-aided Exploration of Human Biology Professor Andreas Linninger Laboratory for Product and Process Design University of Illinois at Chicago 1:00pm...
http://www.csee.umbc.edu/2012/04/talk-virtual-human-simulator-computer-aided-exploration-of-human-biology-1pm-fri-413-umbc/
https://dev.my.umbc.edu/api/v0/pixel/news/13598/guest@my.umbc.edu/3f1825e9f94e1eac98618ddde5a5a515/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 10 Apr 2012 08:49:09 -0400