MS defense: DNSSEC and PKI

MS Thesis Defense
An Operational Study of DNSSEC and its Practical
Application in Establishing a Secure PKI Framework
Colin Roby
4:00pm 19 June 2012, ITE 325b
With the recent completion of signing the DNS Root and various TLD (top level domain), DNSSEC is gradually progressing towards an internet-wide adoption. The extension of DNSSEC security measures addresses many of the security flaws plagued the underlying DNS architecture since its inception. Once widely deployed, DNSSEC will pave the way for extending security service to a wide range of applications. This study focuses on the practicability of current iteration of DNSSEC implementation. Through a virtual network configuration which mimics a typical corporate environment, we explore viable options to establish a secure PKI framework based on DNSSEC in spite of its current limitations. In this endeavour, we propose a simple yet effective method to combine a corporate existing LDAP based directory service with DNSSEC to form a PKI key exchange infrastructure – one which is intuitive to administer and easy to scale to any large corporate network. We demonstrate the advantage of such a PKI framework in one area of its application – the common use of email. Using a prototype email client application, we illustrate how such a framework can promote and facilitate a more secure email system in terms of authenticity, integrity and confidentiality.
Committee: Dr. Deepinder Sidhu (Chair), Dr. Chein-I Chang, Dr. Yun Peng
]]>
MS Thesis Defense An Operational Study of DNSSEC and its Practical Application in Establishing a Secure PKI Framework Colin Roby 4:00pm 19 June 2012, ITE 325b With the recent completion...
http://www.csee.umbc.edu/2012/06/ms-defense-dnssec-and-pki/
https://dev.my.umbc.edu/api/v0/pixel/news/15317/guest@my.umbc.edu/544046f53aae3b14c5032446dd5076a7/api/pixel
computer-science
cybersecurity
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 16 Jun 2012 08:46:27 -0400
College Park announces new Cybersecurity honors program

UMBC's sister school to the south, the University of Maryland, College Park just announced plans for a new honors program in Cybersecurity called Advanced Cybersecurity Experience for Students (ACES) that they will debut in Fall 2013.
Unlike UMBC's graduate Cybersecurity program, ACES is designed for undergraduate students from a range of majors including Computer Science, Engineering, Business, Public Policy, and the social sciences, says a UMD press release.
The Northrop Grumman corporation is supporting the program with a $1.1 million grant. They'll also supply guest lecturers and internship opportunities for students who want to gain some industry experience. The curriculum features courses like cybersercurity forensics, reverse engineering, secure coding, criminology, and law and public policy. Designed to graduate about 45 students per year, the program's aim is to encourage creative problem solving for Cybersecurity problems of the future, says a Baltimore Sun article.
Sound good? Undergraduates at UMBC may eventually be able to take advantage of College Park's new program. According to the UMD press release, over the next few years, College Park hopes to have universities across the University System of Maryland participate in the program through distance education programs, online course offerings, and competitions.
]]>
UMBC's sister school to the south, the University of Maryland, College Park just announced plans for a new honors program in Cybersecurity called Advanced Cybersecurity Experience for...
http://www.csee.umbc.edu/2012/06/college-park-announces-new-cybersecurity-honors-program/
https://dev.my.umbc.edu/api/v0/pixel/news/15289/guest@my.umbc.edu/f06c9e6f5946863ddbfe8f2db3ee179f/api/pixel
cybersecurity
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
1
true
Wed, 13 Jun 2012 08:21:16 -0400
Mon, 18 Jun 2012 08:57:13 -0400
How LinkedIn should have protected your password

Coulda, Woulda, Shoulda.
If you have a LinkedIn account, you probably noticed the news that 6.5 million of their passwords were leaked. While the passwords were encrypted, it's still a major problem for all LinkedIn users. In his column in the latest issue of ACM Queue, LinkedIn Password Leak: Salt Their Hide, security expert Poul-Henning Kamp, explains the flaws in LinkedIn's password management process and the simple steps that can make it much more secure.
Of course, this is more than just about LinkedIn. Similar password leaks from eHarmoney and last.fm were reported this week. If you use any of these popular Web services, you probably should change your password, especially if you use the same password on other Internet sites and services.
If you find this interesting, you should check out the monthly ACM Queue magazine. It is a good resource for people interested in computing and software engineering. Here's how it describes its mission.
"Queue is the ACM's magazine for practicing software engineers. Written by engineers for engineers, Queue focuses on the technical problems and challenges that loom ahead, helping readers to sharpen their own thinking and pursue innovative solutions. Queue does not focus on either industry news or the latest "solutions." Rather, Queue takes a critical look at current and emerging technologies, highlighting problems that are likely to arise and posing questions that software engineers should be thinking about."
Update 6/9: The League of Legends reports that their password database was compromised. It’s not clear how they were storing the passwords.
]]>
Coulda, Woulda, Shoulda. If you have a LinkedIn account, you probably noticed the news that 6.5 million of their passwords were leaked. While the passwords were encrypted, it's still a major...
http://www.csee.umbc.edu/2012/06/how-linkedin-should-have-protected-your-password/
https://dev.my.umbc.edu/api/v0/pixel/news/15239/guest@my.umbc.edu/5a3db1abd4276ea2a64e2486de743e18/api/pixel
computer-science
cybersecurity
news
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Fri, 08 Jun 2012 09:20:24 -0400
Fri, 08 Jun 2012 09:20:24 -0400
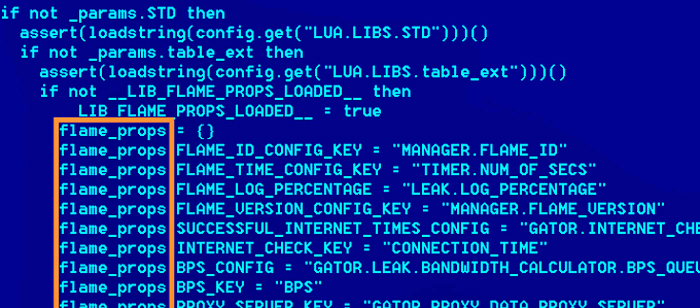
Flame spy malware infiltrating Middle East computers
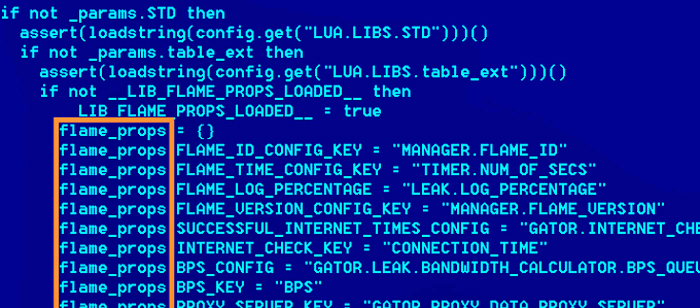
Russia-based anti-virus firm Kaspersky Labs has described a new cyber attack toolkit dubbed Flame (Worm.Win32.Flame) which they describe as "what might be the most sophisticated cyber weapon yet." Their analysis suggests that Flame is a state-supported effort rather than one created by hacktivists or cybercriminals.
"Flame shares many characteristics with notorious cyber weapons Duqu and Stuxnet: while its features are different, the geography and careful targeting of attacks coupled with the usage of specific software vulnerabilities seems to put it alongside those familiar 'super-weapons' currently deployed in the Middle East by unknown perpetrators. Flame can easily be described as one of the most complex threats ever discovered. It’s big and incredibly sophisticated. It pretty much redefines the notion of cyberwar and cyberespionage."
Flame appears to be designed "to systematically collect information on the operations of certain nation states in the Middle East, including Iran, Lebanon, Syria, Israel and so on." Initial infection can be from an infected USB drive, spear phishing or an infected web site. Here’s a map of the top seven affected countries.

More information is available in articles on Wired (Meet ‘Flame’, The Massive Spy Malware Infiltrating Iranian Computers) and the BBC (Flame: Massive cyber-attack discovered, researchers say).
]]>
Russia-based anti-virus firm Kaspersky Labs has described a new cyber attack toolkit dubbed Flame (Worm.Win32.Flame) which they describe as "what might be the most sophisticated cyber weapon yet."...
http://www.csee.umbc.edu/2012/05/flame-spy-malware-infiltrating-middle-east-computers/
https://dev.my.umbc.edu/api/v0/pixel/news/15131/guest@my.umbc.edu/f064428172794bed0cbe3b259aa07553/api/pixel
cybersecurity
fyi
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
8
5
true
Mon, 28 May 2012 11:26:56 -0400
Mon, 28 May 2012 11:26:56 -0400
Privacy Engineering

We've starting to see advertisements for a new kind of position: privacy engineer.
If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate Benjamin Braddock has with a friend of his father, who says "I just want to say one word to you. Just one word. … Are you listening? … Plastics.". Today, 45 years later, that one word might be Privacy.
Our lives are increasingly being lived online through social media systems, cloud based services, smart phones and other ubiquitous computing and sensing devices. Your smart phone, it's common to hear, knows more about you than your spouse or Mom. Data about us is being collected minute by minute, aggregated, integrated, analyzed, bought and sold. At the same time, we have develped powerful new datamining and machine learning techniques that, together with parallel computing, can extract surprising amounts of information and knowledge from the data.
This data can be put to good uses, such as providing you with better services, but can also result in a loss of privacy. Businesses and other organizations want to avoid a backlash in which they lose customers concerned about their privacy. We've seen recent ads for privacy engineers, such as these from Apple , Google and Intel. This is just a sample, many more exist, although the job title may be different.
The job of a privacy engineer doesn't yet have a well defined consensus description, but the focus is on designing an organization's information privacy policy and helping to ensure that it is accurately described and enforced. High level tasks include (i) protecting data from unauthorized access, use or disclosure (ii) providing users with appropriate tools to both understand and control what information is collected and how it is shared and used; and (iii) recognizing how the data can be usefully mined without revealing private information.
What courses can a UMBC undergraduate take to prepare for positions like these? After getting a good grounding in the required computer science or computer engineering courses, undergrads can take classes in the fundamentals of security (CMSC 426 and CMSC 487), information assurance (CMSC 444), and cryptography (CMSC 443), take a course in databases (CMSC 461), datamining and machine learning (CMSC 478) and/or visualization (CMSC 436), and perhaps mobile computing (CMSC 628). Interested students should also look for special topics course, like Security and Privacy in a Mobile Social World which is being offered this semester. We also have several research labs that work in privacy-related areas, including the Cyber Defense, Coral, Ebiquity, Diadic and Maple labs.
]]>
We've starting to see advertisements for a new kind of position: privacy engineer. If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate...
http://www.csee.umbc.edu/2012/04/privacy-engineering/
https://dev.my.umbc.edu/api/v0/pixel/news/20778/guest@my.umbc.edu/fbbbc7b1c24cc3b399ea2b5f387f8643/api/pixel
big-data
computer-engineering
computer-science
cybersecurity
datamining
jobs
news
privacy
research
security
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 14 Apr 2012 13:40:58 -0400
Privacy Engineering

We've starting to see advertisements for a new kind of position: privacy engineer.
If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate Benjamin Braddock has with a friend of his father, who says "I just want to say one word to you. Just one word. … Are you listening? … Plastics.". Today, 45 years later, that one word might be Privacy.
Our lives are increasingly being lived online through social media systems, cloud based services, smart phones and other ubiquitous computing and sensing devices. Your smart phone, it's common to hear, knows more about you than your spouse or Mom. Data about us is being collected minute by minute, aggregated, integrated, analyzed, bought and sold.
This data can be put to good uses, such as providing you with better services, but can also result in a loss of privacy. Businesses and other organizations want to avoid a backlash in which they loose customers concerned about their privacy. We've seen recent ads for privacy engineers, such as these from Apple , Google and Intel. This is just a sample, many more exist, although the job title may be different.
What courses can a UMBC undergraduate take to prepare for positions like these? After getting a good grounding in the required computer science or computer engineering courses, undergrads can take classes in the fundamentals of security (CMSC 426 and CMSC 487), information assurance (CMSC 444), and cryptography (CMSC 443), take a course in datamining and machine learning (CMSC 478) and/or visualization (CMSC 436), and perhaps mobile computing (CMSC 628). Interested students should also look for special topics course, like Security and Privacy in a Mobile Social World which is being offered this semester.
]]>
We've starting to see advertisements for a new kind of position: privacy engineer. If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate...
http://www.csee.umbc.edu/2012/04/privacy-engineering/
https://dev.my.umbc.edu/api/v0/pixel/news/13700/guest@my.umbc.edu/01020d2ef594d97166979861804ce6b6/api/pixel
computer-engineering
computer-science
cybersecurity
fyi
jobs
research
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sat, 14 Apr 2012 13:40:58 -0400
Sat, 14 Apr 2012 13:40:58 -0400
Privacy Engineering

We've starting to see advertisements for a new kind of position: privacy engineer.
If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate Benjamin Braddock has with a friend of his father, who says "I just want to say one word to you. Just one word. … Are you listening? … Plastics.". Today, 45 years later, that one word might be Privacy.
Our lives are increasingly being lived online through social media systems, cloud based services, smart phones and other ubiquitous computing and sensing devices. Your smart phone, it's common to hear, knows more about you than your spouse or Mom. Data about us is being collected minute by minute, aggregated, integrated, analyzed, bought and sold. At the same time, we have develped powerful new datamining and machine learning techniques that, together with parallel computing, can extract surprising amounts of information and knowledge from the data.
This data can be put to good uses, such as providing you with better services, but can also result in a loss of privacy. Businesses and other organizations want to avoid a backlash in which they lose customers concerned about their privacy. We've seen recent ads for privacy engineers, such as these from Apple , Google and Intel. This is just a sample, many more exist, although the job title may be different.
The job of a privacy engineer doesn't yet have a well defined consensus description, but the focus is on designing an organization's information privacy policy and helping to ensure that it is accurately described and enforced. High level tasks include (i) protecting data from unauthorized access, use or disclosure (ii) providing users with appropriate tools to both understand and control what information is collected and how it is shared and used; and (iii) recognizing how the data can be usefully mined without revealing private information.
What courses can a UMBC undergraduate take to prepare for positions like these? After getting a good grounding in the required computer science or computer engineering courses, undergrads can take classes in the fundamentals of security (CMSC 426 and CMSC 487), information assurance (CMSC 444), and cryptography (CMSC 443), take a course in databases (CMSC 461), datamining and machine learning (CMSC 478) and/or visualization (CMSC 436), and perhaps mobile computing (CMSC 628). Interested students should also look for special topics course, like Security and Privacy in a Mobile Social World which is being offered this semester. We also have several research labs that work in privacy-related areas, including the Cyber Defense, Coral, Ebiquity, Diadic and Maple labs.
]]>
We've starting to see advertisements for a new kind of position: privacy engineer. If you've seen the classic movie, The Graduate, you'll remember the conversation that recent college graduate...
http://www.csee.umbc.edu/2012/04/privacy-engineering/
https://dev.my.umbc.edu/api/v0/pixel/news/13706/guest@my.umbc.edu/8bd82e808edc13725952fd870a1cc349/api/pixel
big-data
computer-engineering
computer-science
cybersecurity
datamining
jobs
news
privacy
research
security
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 14 Apr 2012 13:40:58 -0400
Sat, 14 Apr 2012 13:40:58 -0400
UMBC Cyberdawgs are recruiting
UMBC's Cyber Defense Team is looking for new members. This semester the team competed in the Collegiate Cyber Defense Championship. In this competition, each team defended a mock corporate network against a horde of professional hackers in a fast-paced, real-time event over the course of two days. These competitions are a great way to network with government agencies and key companies in the security industry.
The UMBC Cyber Defense Team provides a great opportunity to gain practical, hands-on experience in information security, intrusion detection, cybersecurity, and network security. The team practices both penetration and defense of isolated networks similar to real business environments. The group meets at 7:00pm on Mondays in ITE 367 and will have special events that will be announced also. No experience is required, but you should be motivated to learn about computer networks and systems security.
You can find additional information and how to join our mailing list at the UMBC Cyberdawgs website. Contact Marc Warfield (marc9 at umbc.edu) for more information.
]]>
UMBC's Cyber Defense Team is looking for new members. This semester the team competed in the Collegiate Cyber Defense Championship. In this competition, each team defended a mock corporate network...
http://www.csee.umbc.edu/2012/03/umbc-cyberdawgs-are-recruiting/
https://dev.my.umbc.edu/api/v0/pixel/news/13066/guest@my.umbc.edu/5040a98ab0d772fcc6690cda6ffc6f6a/api/pixel
cybersecurity
news
research
students
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
9
1
true
Mon, 19 Mar 2012 11:51:09 -0400
talk: Securing Cyber-Physical Systems, 3/26
Securing Cyber-Physical Systems
Alvaro Cardenas
Fujitsu Laboratories of America
1:00pm Monday 26 March 2012, ITE 325b, UMBC
Our critical infrastructure systems are being modernized with information and communication technologies to face the operational requirements and efficiency challenges of the 21st century. The smart grid in particular, will introduce millions of new intelligent components to the electric grid, buildings, and homes within the next decade. While this modernization will bring many operational benefits to infrastructure systems, it will also introduce new vulnerabilities, a larger attack surface, and raise privacy concerns.
This presentation will be divided in three parts. The first part of the talk will cover the unique and fundamentally new challenges and solutions required for securing cyber-physical systems. The second part of the talk will focus on new mechanisms for securing cyber-physical systems. The final part of the talk will cover my other research interests in intrusion detection and future plans for big-data security.
Alvaro A. Cárdenas is a research staff engineer at Fujitsu Laboratories of America. Prior to this he was a postdoctoral fellow at the University of California, Berkeley working in securing critical infrastructure systems. His research focuses on network security, the smart grid and other cyber-physical systems, intrusion detection and big data security. He has received numerous awards for his research including a best paper award from the U.S. Army Research Office, a best presentation award from the IEEE, a fellowship from the University of Maryland, and a Distinguished Assistantship from the Institute of Systems Research. He has also been an invited visiting professor at the University of Cagliari. Alvaro holds M.S. and Ph.D. degrees from the University of Maryland, College Park, and a B.S. from Universidad de los Andes.
See http://csee.umbc.edu/talks for more information
]]>
Securing Cyber-Physical Systems Alvaro Cardenas Fujitsu Laboratories of America 1:00pm Monday 26 March 2012, ITE 325b, UMBC Our critical infrastructure systems are being modernized...
http://www.csee.umbc.edu/2012/03/talk-securing-cyber-physical-systems-326/
https://dev.my.umbc.edu/api/v0/pixel/news/13056/guest@my.umbc.edu/57fa7e3f0d89a046405e689b1e186e8b/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 18 Mar 2012 20:08:14 -0400
talk: Self-sustainable Cyber-physical System Design

Self-sustainable Cyber-physical System Design
Dr. Nilanjan Banerjee
University of Arkansas Fayetteville
1:00pm Tuesday 13 March 2012, ITE 325b UMBC
Renewable energy can enable diverse self-sustainable cyber-physical systems with applications ranging from healthcare to off-grid home energy management. However, there are several challenges that need to be addressed before such systems can be realized. For instance, how do we balance the small and often variable energy budgets imposed by renewables with system functionality? How can we design sensitive physical sensors and efficient harvesting circuits for mW energy sources such as sound and indoor light? For systems such as off-grid homes that interact with humans, how do we balance demand and supply while being cognizant to usability needs?
In this talk, I will present techniques that address these challenges. Specifically, I will propose a Hierarchical Power Management paradigm that combines platforms with varied energy needs to balance energy consumption and functionality, the design of an efficient harvester for sound scavenging, and sensitive ECG sensors. I will also present a measurement study that reveals the energy management challenges faced by off-grid home residents. Finally, I will conclude with the design of a solar replayer platform that allows immense flexibility in evaluating solar panel driven systems, and works for a wide range of panels.
Nilanjan Banerjee is an Assistant Professor in the department of Computer Science and Computer Engineering at University of Arkansas Fayetteville. He graduated with a M.S. and a Ph.D. from the University of Massachusetts at Amherst in 2009 and a BTech. (Hons.) from IIT Kharagpur in 2004. He has won the Yahoo! Outstanding dissertation award at UMass, a best undergraduate thesis award at IIT Kharagpur, and an Outstanding Researcher award at University of Arkansas. He is a 2011 NSF Career awardee and has won three other NSF awards (including the NSF I-Corp grant). His research interests span renewable energy driven systems, healthcare systems, and mobile systems.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Self-sustainable Cyber-physical System Design Dr. Nilanjan Banerjee University of Arkansas Fayetteville 1:00pm Tuesday 13 March 2012, ITE 325b UMBC Renewable energy can enable diverse...
http://www.csee.umbc.edu/2012/03/talk-self-sustainable-cyber-physical-system-design/
https://dev.my.umbc.edu/api/v0/pixel/news/12874/guest@my.umbc.edu/649502cf0ae91475c5e9a7f9d4e7c4e0/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 10 Mar 2012 00:33:07 -0500
Sat, 10 Mar 2012 00:33:07 -0500