talk: Analytics for Detecting Web and Social Media Abuse
Analytics for Detecting Web and Social Media Abuse
Dr. Justin Ma, UC Berkeley
1:00pm Friday 16 March 2012, ITE 325, UMBC
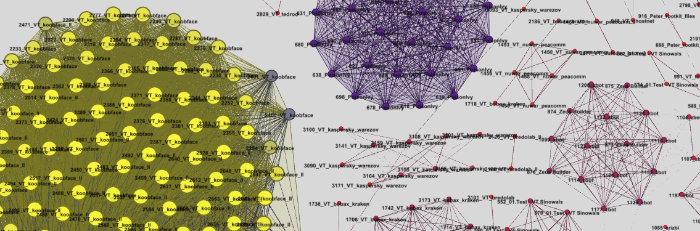
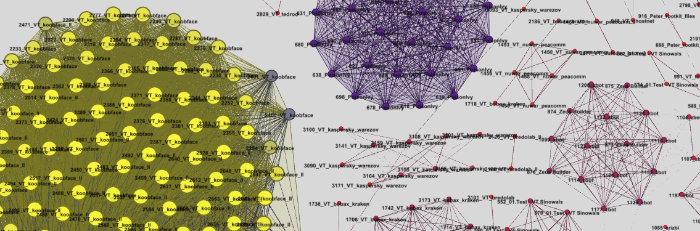
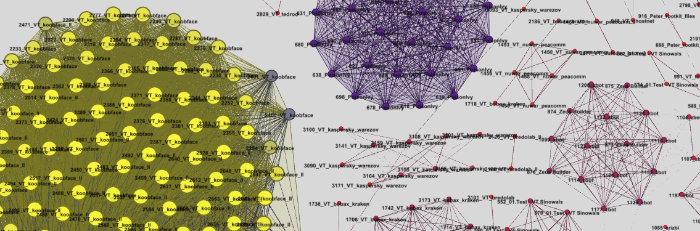
The Web and online social media provide invaluable communication services to a global Internet user base. The tremendous success of these services, however, has also created valuable opportunities for criminals and other miscreants to abuse them for their own gain. As a result, it is both an important yet challenging problem to detect, monitor, and curtail this abuse. However, the large scale and diversity of these services, combined with the tactics used by attackers, make it difficult to discern one clear and robust signal for detecting abuse. One approach, relying on domain expertise, is to construct a small set of well-crafted heuristics, but such heuristics tend to rapidly become obsolete. In this talk, I will describe more robust approaches based on machine learning, statistical modeling, and large-scale analytics of large data sets.
First I will describe online learning approaches for detecting malicious Web sites (those involved in criminal scams) using lexical and host-based features of the associated URLs. This application is particularly appropriate for online algorithms as the size of the training data is larger than can be efficiently processed in batch and because the features that typify malicious URLs evolve continuously. Motivated by this application, we built a real-time system to gather URL features and analyze them against a source of labeled URLs from a large Web mail provider. Our system adapts in an online fashion to the evolving characteristics of malicious URLs, achieving daily classification accuracies up to 99% over a balanced data set.
Next I will describe our ongoing efforts for creating analytics for detecting social media abuse. Deciding on a universal definition of social media abuse is difficult, as abuse is often in the eye of the beholder. In light of this challenge, we explore a more formal definition based on information theory. In particular, we hypothesize that messages with low information content are likely to be abusive. From this, we develop a measure of content complexity to identify abusive users that shows promise in our early evaluations.
In addition to our own experiments in the lab, this work has found success in practice as well. Companies serving hundreds of millions of users have adopted these ideas to improve abuse detection within their own services.
Justin Ma is a postdoc in the UC Berkeley AMPLab. His primary research is in systems security, and his other interests include applications of machine learning to systems problems, systems for large-scale machine learning, and the impact of energy availability on computing. He received B.S. degrees in Computer Science and Mathematics from the University of Maryland in 2004, and he received his Ph.D. in Computer Science from UC San Diego in 2010.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Analytics for Detecting Web and Social Media Abuse Dr. Justin Ma, UC Berkeley 1:00pm Friday 16 March 2012, ITE 325, UMBC The Web and online social media provide invaluable communication...
http://www.csee.umbc.edu/2012/03/talk-analytics-for-detecting-web-and-social-media-abuse-1pm-316/
https://dev.my.umbc.edu/api/v0/pixel/news/12876/guest@my.umbc.edu/6a06d76cfa8a670f2da3ca3d89138744/api/pixel
cybersecurity
news
research
security
social-media
talks
web
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Sat, 10 Mar 2012 00:01:06 -0500
Wed, 14 Mar 2012 00:01:06 -0400
talk: Using Static Analysis to Diagnose Misconfigured...
Full Title: talk: Using Static Analysis to Diagnose Misconfigured Open Source Systems Software
Using Static Analysis to Diagnose
Misconfigured Open Source Systems Software
Ariel Rabkin, UC Berkeley
1:00pm Monday 5 March 2012, ITE 325b UMBC
Ten years ago, few software developers worked on distributed systems. Today, developers often run code on clusters, relying on large open-source software stacks to manage resources. These systems are challenging to configure and debug. Fortunately, developments in program analysis have given us new tools for managing the complexity of modern software. This talk will show how static analysis can help users configure their systems. I present a technique that builds an explicit table mapping a program's possible error messages to the options that might cause them. As a result, users can get immediate feedback on how to resolve configuration errors.
Ari Rabkin is a PhD student in Computer Science at UC Berkeley working in the AMP lab. His current research interest is the software engineering and administration challenges of big-data systems. He is particularly interested in applying program analysis techniques to tasks like log analysis and configuration debugging. His broader interests focus on systems and security, including improving system usability by making systems easier to understand, the connections between computer science research and technology policy, developing program analysis techniques that work acceptably well on large, complex, messy software systems.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Full Title: talk: Using Static Analysis to Diagnose Misconfigured Open Source Systems Software Using Static Analysis to Diagnose Misconfigured Open Source Systems Software Ariel Rabkin, UC...
http://www.csee.umbc.edu/2012/03/using-static-analysis-to-diagnose-misconfigured-open-source-systems-software/
https://dev.my.umbc.edu/api/v0/pixel/news/12648/guest@my.umbc.edu/3ca2f0619dd821f9284ebf751e5536b4/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 02 Mar 2012 00:25:32 -0500
talk: Using Static Analysis to Diagnose Misconfigured...
Full Title: talk: Using Static Analysis to Diagnose Misconfigured Open Source Systems Software
Using Static Analysis to Diagnose
Misconfigured Open Source Systems Software
Ariel Rabkin, UC Berkeley
1:00pm Monday 5 March 2012, ITE 325b UMBC
Ten years ago, few software developers worked on distributed systems. Today, developers often run code on clusters, relying on large open-source software stacks to manage resources. These systems are challenging to configure and debug. Fortunately, developments in program analysis have given us new tools for managing the complexity of modern software. This talk will show how static analysis can help users configure their systems. I present a technique that builds an explicit table mapping a program's possible error messages to the options that might cause them. As a result, users can get immediate feedback on how to resolve configuration errors.
Ari Rabkin is a PhD student in Computer Science at UC Berkeley working in the AMP lab. His current research interest is the software engineering and administration challenges of big-data systems. He is particularly interested in applying program analysis techniques to tasks like log analysis and configuration debugging. His broader interests focus on systems and security, including improving system usability by making systems easier to understand, the connections between computer science research and technology policy, developing program analysis techniques that work acceptably well on large, complex, messy software systems.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Full Title: talk: Using Static Analysis to Diagnose Misconfigured Open Source Systems Software Using Static Analysis to Diagnose Misconfigured Open Source Systems Software Ariel Rabkin, UC...
http://www.csee.umbc.edu/2012/02/using-static-analysis-to-diagnose-misconfigured-open-source-systems-software/
https://dev.my.umbc.edu/api/v0/pixel/news/12457/guest@my.umbc.edu/4bfe61c1801493608302c3961aa0d712/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 26 Feb 2012 12:25:32 -0500
Wed, 29 Feb 2012 22:25:32 -0500
talk: Self-sustainable Cyber-physical System Design

Self-sustainable Cyber-physical System Design
Dr. Nilanjan Banerjee
University of Arkansas Fayetteville
1:00pm Tuesday 13 March 2012, ITE 325b UMBC
Renewable energy can enable diverse self-sustainable cyber-physical systems with applications ranging from healthcare to off-grid home energy management. However, there are several challenges that need to be addressed before such systems can be realized. For instance, how do we balance the small and often variable energy budgets imposed by renewables with system functionality? How can we design sensitive physical sensors and efficient harvesting circuits for mW energy sources such as sound and indoor light? For systems such as off-grid homes that interact with humans, how do we balance demand and supply while being cognizant to usability needs?
In this talk, I will present techniques that address these challenges. Specifically, I will propose a Hierarchical Power Management paradigm that combines platforms with varied energy needs to balance energy consumption and functionality, the design of an efficient harvester for sound scavenging, and sensitive ECG sensors. I will also present a measurement study that reveals the energy management challenges faced by off-grid home residents. Finally, I will conclude with the design of a solar replayer platform that allows immense flexibility in evaluating solar panel driven systems, and works for a wide range of panels.
Nilanjan Banerjee is an Assistant Professor in the department of Computer Science and Computer Engineering at University of Arkansas Fayetteville. He graduated with a M.S. and a Ph.D. from the University of Massachusetts at Amherst in 2009 and a BTech. (Hons.) from IIT Kharagpur in 2004. He has won the Yahoo! Outstanding dissertation award at UMass, a best undergraduate thesis award at IIT Kharagpur, and an Outstanding Researcher award at University of Arkansas. He is a 2011 NSF Career awardee and has won three other NSF awards (including the NSF I-Corp grant). His research interests span renewable energy driven systems, healthcare systems, and mobile systems.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Self-sustainable Cyber-physical System Design Dr. Nilanjan Banerjee University of Arkansas Fayetteville 1:00pm Tuesday 13 March 2012, ITE 325b UMBC Renewable energy can enable diverse...
http://www.csee.umbc.edu/2012/02/talk-self-sustainable-cyber-physical-system-design/
https://dev.my.umbc.edu/api/v0/pixel/news/12456/guest@my.umbc.edu/10781512f4d6c51fb19c6d20dc6a4708/api/pixel
cybersecurity
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 26 Feb 2012 11:33:07 -0500
talk: Analytics for Detecting Web and Social Media Abuse
Analytics for Detecting Web and Social Media Abuse
Dr. Justin Ma, UC Berkeley
1:00pm Friday 16 March 2012, ITE 325, UMBC
The Web and online social media provide invaluable communication services to a global Internet user base. The tremendous success of these services, however, has also created valuable opportunities for criminals and other miscreants to abuse them for their own gain. As a result, it is both an important yet challenging problem to detect, monitor, and curtail this abuse. However, the large scale and diversity of these services, combined with the tactics used by attackers, make it difficult to discern one clear and robust signal for detecting abuse. One approach, relying on domain expertise, is to construct a small set of well-crafted heuristics, but such heuristics tend to rapidly become obsolete. In this talk, I will describe more robust approaches based on machine learning, statistical modeling, and large-scale analytics of large data sets.
First I will describe online learning approaches for detecting malicious Web sites (those involved in criminal scams) using lexical and host-based features of the associated URLs. This application is particularly appropriate for online algorithms as the size of the training data is larger than can be efficiently processed in batch and because the features that typify malicious URLs evolve continuously. Motivated by this application, we built a real-time system to gather URL features and analyze them against a source of labeled URLs from a large Web mail provider. Our system adapts in an online fashion to the evolving characteristics of malicious URLs, achieving daily classification accuracies up to 99% over a balanced data set.
Next I will describe our ongoing efforts for creating analytics for detecting social media abuse. Deciding on a universal definition of social media abuse is difficult, as abuse is often in the eye of the beholder. In light of this challenge, we explore a more formal definition based on information theory. In particular, we hypothesize that messages with low information content are likely to be abusive. From this, we develop a measure of content complexity to identify abusive users that shows promise in our early evaluations.
In addition to our own experiments in the lab, this work has found success in practice as well. Companies serving hundreds of millions of users have adopted these ideas to improve abuse detection within their own services.
Justin Ma is a postdoc in the UC Berkeley AMPLab. His primary research is in systems security, and his other interests include applications of machine learning to systems problems, systems for large-scale machine learning, and the impact of energy availability on computing. He received B.S. degrees in Computer Science and Mathematics from the University of Maryland in 2004, and he received his Ph.D. in Computer Science from UC San Diego in 2010.
Host: Anupam Joshi
See http://csee.umbc.edu/talks for more information
]]>
Analytics for Detecting Web and Social Media Abuse Dr. Justin Ma, UC Berkeley 1:00pm Friday 16 March 2012, ITE 325, UMBC The Web and online social media provide invaluable communication...
http://www.csee.umbc.edu/2012/02/talk-analytics-for-detecting-web-and-social-media-abuse-1pm-316/
https://dev.my.umbc.edu/api/v0/pixel/news/12450/guest@my.umbc.edu/7716330b5c8708f060907f80cb3c33c8/api/pixel
cybersecurity
news
research
security
social-media
talks
web
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 26 Feb 2012 08:50:06 -0500
Sun, 26 Feb 2012 08:50:06 -0500
Stripe capture the flag wargame
Stripe, a San Francisco startup with an online-payment system, is hosting a simple online cybersecurity capture the flag (CTF) challenge. See their blog post for the details.
“The hardest part of writing secure code is learning to think like an attacker. For example, every programmer is told to watch out for SQL injections, but it’s hard to appreciate just how exploitable they are until you’ve written a SQL injection of your own.
We built Stripe Capture the Flag, a security wargame inspired by SmashTheStack’s IO, to help the community (as well our team!) practice identifying and exploiting common security problems.
After completing our CTF, you should have a greatly improved understanding of how attackers will try to break your code (and hopefully will have fun in the process!).”
If you can crack their system, they’ll send you a t-shirt. Since security is important to their business, maybe they will also talk to you about a job.
]]>
Stripe, a San Francisco startup with an online-payment system, is hosting a simple online cybersecurity capture the flag (CTF) challenge. See their blog post for the details. “The hardest...
http://www.csee.umbc.edu/2012/02/stripe-capture-the-flag-wargame/
https://dev.my.umbc.edu/api/v0/pixel/news/12378/guest@my.umbc.edu/9d10504999a3e7b3ca8734bd9271ca3d/api/pixel
cybersecurity
fyi
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Thu, 23 Feb 2012 01:03:00 -0500
Using data visualization techniques to support...
Full Title: Using data visualization techniques to support digital forensics
UMBC Cyber Defense Lab Research Meeting
Using data visualization techniques to support digital forensics
Tim Leschke
11:00am-12:15pm, Friday, Feb 3, 2012
ITE Room 228
Digital forensic examiners explore large datasets in search of evidence of a crime. In order to keep pace with the growing amount of data that is subject to a forensic examination, digital forensic examiners need to be more selective about the data they examine. One way to be selective about data is to focus attention at data that has changed-over-time. We present Change-Link, a data exploration tool which allows the user to see directories that have changed within an operating system. Our novel contributions are 1) the development of a segmented-box-and-whisker icon for representing change to individual directories, and 2) the first data visualization tool developed specifically for the domain of digital forensic data. We show that by using Change-Link to view change to a directory-tree structure, digital forensic examiners can enhance their ability to perform forensic examinations.
Tim Leschke is a Ph.D. student in the Computer Science program at UMBC.
Host: Professor Alan Sherman
]]>
Full Title: Using data visualization techniques to support digital forensics UMBC Cyber Defense Lab Research Meeting Using data visualization techniques to support digital forensics Tim...
http://www.csee.umbc.edu/2012/01/using-data-visualization-techniques-to-support-digital-forensics/
https://dev.my.umbc.edu/api/v0/pixel/news/11670/guest@my.umbc.edu/1fd19283b4b1e403362e356149042212/api/pixel
cybersecurity
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Tue, 31 Jan 2012 10:26:37 -0500
Cyber Challenge Hones Students’ Cyber Skills

Tyler Campbell, Nick Ducq, Ryan King, Andrew Nguyen and Tim Spillman walked out of the Baltimore Convention Center elated. Their team, the Sherwood Cyber Warriors, had just won the high school division of the inaugural Maryland Cyber Challenge. Their success netted them each a $5,000 scholarship from the National Security Agency.
The entire experience was rewarding for both the students and their parents, says Steve Weiss, one of the team’s advisers. “Winning first place was the icing on the cake.”
In a conference with over 800 attendees, the excitement over the cyber competition was palpable. With scoreboards changing in real time, onlookers crowded around to see who was in the lead.
Following the competition, held October 21 and 22, eight teams from each division — professional, college and high school — walked away with scholarships and cash prizes. The scholarships for students, put up by the National Security Agency (NSA), totaled more than $84,000.
Members of first place high school and college teams took home $5,000 scholarships each. Members of second place high school and college teams took home $2,000 scholarships. Each member of the first place professional teams won $2,000 and each second place member won $1,000.
First place winners in the college and high school categories were from, respectively, the University of Maryland, College Park and Sherwood High School. Second place winners were Towson University and Poolesville High School. In the professional category Team ICF came in first, with Team Pr3tty coming in second.
The Sherwood Cyber Warriors, four seniors and a junior, are mostly undecided in their future careers, although one does plan to work cybersecurity. Jim Kirk, the team’s senior advisor, says that regardless of the their ultimate career choices, the students learned valuable skills from the competition — such as how to communicate effectively and work as a team.
The Cyber Warriors began practicing for the competition in May, often meeting twice a week. The team developed strategies to pick the low hanging fruit — what hackers go for first. That, says Kirk, includes developing strong passwords and removing unnecessary software from servers.
The challenge for the high school teams, says Rick Forno, Director of UMBC's Graduate Cybersecurity Program and an organizer of the Cyber Challenge, was purely defensive. “They were being attacked and their job was to keep services open.”
The challenge was run using CyberNEXS, a software system developed by SAIC for cybersecurity training and exercises.The system is self-contained and runs both Windows and UNIX systems.
But, more than just the chance to compete, the event gave college and high school students a taste of what cybersecurity work is like. And that, involves more than technical skills say professionals in the field.
“The cyber challenge is especially interesting to me, since all the students participating are passionate about cyber security and the teams will only excel if every member is doing their job,” says Neil Furukawa, vice president of CyberPoint International. “We’re looking for people who can lead, but who can also roll up their sleeves and get the work done.”
Phyllis Villani, Director of Talent acquisition at Northrop Grumman says that to get a job, “networking is key.” Besides honing “soft skills” like communication, Furukawa says, people should never stop their education because cybersecurity is a rapidly evolving field.
Fittingly, education is what the Maryland Cyber Challenge is all about.
Originally posted by Nicole Ruediger at November 18, 2011 1:02 PM
]]>
Tyler Campbell, Nick Ducq, Ryan King, Andrew Nguyen and Tim Spillman walked out of the Baltimore Convention Center elated. Their team, the Sherwood Cyber Warriors, had just won the high school...
http://www.csee.umbc.edu/2011/12/cyber-challenge-hones-students-cyber-skills/
https://dev.my.umbc.edu/api/v0/pixel/news/10956/guest@my.umbc.edu/cc42d367060008b73d2f2cffc9b458ef/api/pixel
cybersecurity
graduate
news
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Tue, 20 Dec 2011 23:30:25 -0500
UMBC team places second in the DARPA Shredder Challenge

Just over a month ago, DARPA announced The Shredder Challenge competition to develop a system to solve puzzles by reassembling images of shredded documents with a $50,000 prize for the winning entry. Yesterday the prize was won by All Your Shreds Are Belong to U.S., a San Francisco-based team that was the first to correctly reconstructed each of the five challenge documents.

UMBC Assistant VP for
Research Don Engel
It's unfortunate that there was no prize for second place, because that honor was won by Schroddon, a two-person effort including UMBC Assistant Vice President for Research Don Engel. While most of the top teams had a handful of software engineers and used commercial crowdsourcing services, Schroddon was a part-time effort by Dr. Engel and his wife, Dr. Marianne Engel.
Both Don and Marianne have Ph.D.s in Physics, but Don also has an undergraduate degree in Computer Science, did graduate work in computational linguistics, and develops software in his spare time for fun. Two of his active software development projects are ShowMe3D, an application for Mac and iOS that can be used to take and view 3D photos, and When2meet, a free web-based tool for finding the best time for a group to meet.
The Shredder Challenge was the latest competition run by DARPA as a low cost way to spur research on new problems. The press release describes it this way.
"The Shredder Challenge represents a preliminary investigation into the area of information security to identify and assess potential capabilities that could be used by war fighters operating in war zones to more quickly obtain valuable information from confiscated, shredded documents and gain a quantitative understanding of potential vulnerabilities inherent to the shredding of sensitive U.S. National security documents."
"Lots of experts were skeptical that a solution could be produced at all let alone within the short time frame,” said Dan Kaufman, director, DARPA Information Innovation Office. “The most effective approaches were not purely computational or crowd-sourced, but used a combination blended with some clever detective work. We are impressed by the ingenuity this type of competition elicits."
Over 9,000 teams registered for the Shredder Challenge and it is quite an achievement for the Engles to have placed second, especially against many much larger teams. If you are interested in seeing what the data is like, you can download it from the DARPA site.
These challenge competitions are becoming more common and are a great way for students to get involved in independent research and maybe win fame and fortune.
]]>
Just over a month ago, DARPA announced The Shredder Challenge competition to develop a system to solve puzzles by reassembling images of shredded documents with a $50,000 prize for the winning...
http://www.csee.umbc.edu/2011/12/umbc-team-places-second-in-the-darpa-shredder-challenge/
https://dev.my.umbc.edu/api/v0/pixel/news/10655/guest@my.umbc.edu/6e763604b5be9c84148b3f90414c1f53/api/pixel
computer-science
cybersecurity
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
19
5
true
Sat, 03 Dec 2011 15:42:51 -0500
Sat, 03 Dec 2011 15:42:51 -0500
Summer research in cybersecurity and trustworthy systems
The Team for Research in Ubiquitous Secure Technology (TRUST) will sponsor 20 undergraduate students from diverse backgrounds and cultures, to participate in the Summer Undergraduate Research Experience located at TRUST partner campuses: UC Berkeley, Cornell University, Stanford University, Vanderbilt University. These students will work with graduate student and faculty mentors throughout the summer performing research and supporting activities in the area of information technology and TRUST related topics. The program will run from June 3 to July 27, 2012 and provide room and board, a travel allowance and a $4,000 stipend. Apply by February 17. See the flyer for more information and the Trust REU site for details and to apply.
]]>
The Team for Research in Ubiquitous Secure Technology (TRUST) will sponsor 20 undergraduate students from diverse backgrounds and cultures, to participate in the Summer Undergraduate Research...
http://www.csee.umbc.edu/2011/11/summer-research-in-cybersecurity-and-trustworthy-systems/
https://dev.my.umbc.edu/api/v0/pixel/news/10251/guest@my.umbc.edu/5c63393941c599754a75ceaf7ead42f5/api/pixel
cybersecurity
news
undergraduate
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 09 Nov 2011 08:04:46 -0500