MS defense: Mahale on Group Centric Information...
Full Title: MS defense: Mahale on Group Centric Information Sharing, 10am Tue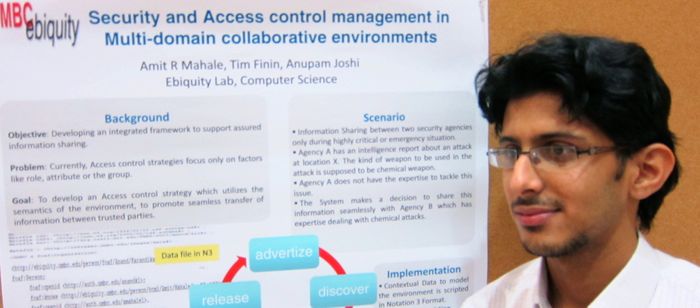
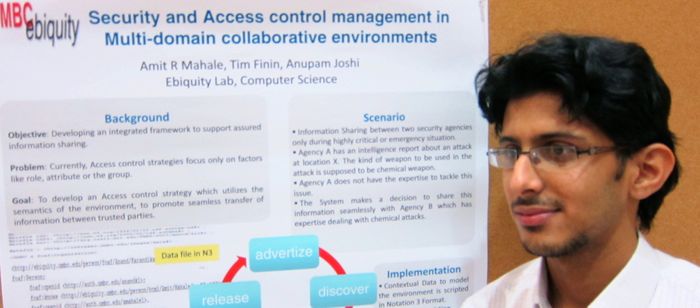
MS Thesis Defense
Group Centric Information Sharing
using Hierarchical Models
Amit Mahale
10:00am Tuesday, 10 May 2011, ITE 346, UMBC
Traditional security policies are often based on the concept of “need to know” and are typified by predefined and often rigid specifications of which principals and roles are pre-authorized to access what information. A recommendations of the 9/11 commission was to find ways to move from this traditional perspective toward one that emphasizes the “need to share”. Ravi Sandhu and his colleagues have developed the Group centric secure information sharing model (gSIS) as a new model that is more adaptible to highly dynamic situations requiring information sharing. We present an implementation of gSIS and demonstrate its usefulness to usecases in information sharing in social media. Our contributions include the prototype implementation, extension to the model such as hierarchical groups and necessary and sufficient conditions, and the use of the semantic Web language OWL for representing the central gSIS concepts and associated data. Our framework uses a pragmatic approach of using semantic web technology to represent and reason about the hierarchy and procedural method to compute access decisions relying on the gSIS semantics.
Thesis Committee:
- Dr. Tim Finin (chair)
- Dr. Anupam Joshi
- Dr. Yelena Yesha
- Dr. Laura Zavala
]]>
Full Title: MS defense: Mahale on Group Centric Information Sharing, 10am Tue MS Thesis Defense Group Centric Information Sharing using Hierarchical Models Amit Mahale 10:00am Tuesday,...
http://www.cs.umbc.edu/2011/05/ms-defense-mahale-on-group-centric-information-sharing-10am-tue/
https://dev.my.umbc.edu/api/v0/pixel/news/6834/guest@my.umbc.edu/e90ca681916052b7056dee7badbec24a/api/pixel
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Sun, 08 May 2011 16:11:09 -0400
Sun, 08 May 2011 16:11:09 -0400
MS defense: Detection of Unsafe Action in...
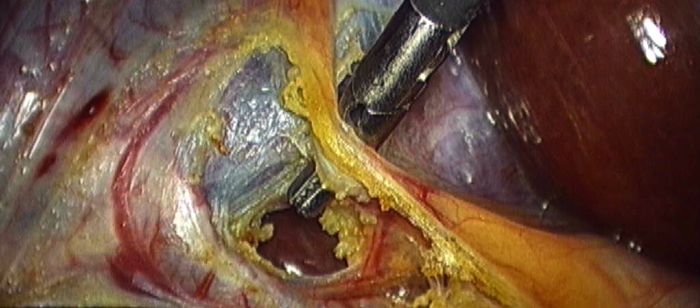
Full Title: MS defense: Detection of Unsafe Action in Laparoscopic Cholecystectomy Video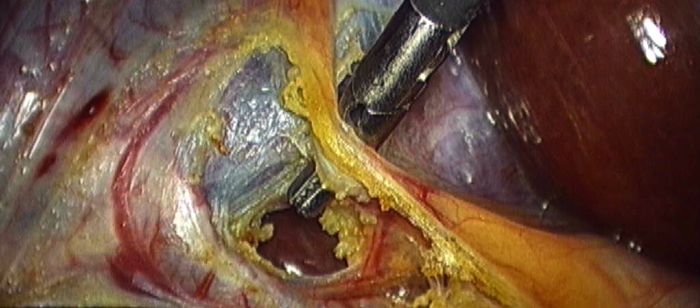
MS defense
Detection of Unsafe Action in Laparoscopic Cholecystectomy Video
Ashwini Lahane
10:00am Thursday, 28 April 2011, ITE 346
Wellness and healthcare are central to the lives of all people. Information technology has already contributed in significant ways towards enhancement of healthcare delivery and to improving the quality of life. And it will continue to do so with the development of “smarter” technologies and environments. Recent years have seen context awareness as one of the most important aspects in the emerging pervasive computing paradigm. We focus our work on situation awareness; a more holistic variant of context awareness where situations are regarded as logically aggregated contexts. We demonstrate an application of situation aware computing in healthcare. We primarily focus on laparoscopic cholecystectomy, a complex yet commonly performed surgical procedure. The outcome of the surgery is influenced greatly by the training, skill, and judgment of the surgeon. Many surgical simulators have been developed to meet the training and practice needs of the surgeons. However few systems provide feedback during the actual surgery. We present a method to detect a situation, that shows possibility of injury to an artery by analyzing the laparoscopic cholecystectomy surgical video. The system can be used to provide feedback to the operating surgeon in case of a possible risk. We have also built a prototype to demonstrate the use of our system in telemedicine, in the form of a web service.
Thesis Committee:
- Dr. Yelena Yesha (chair)
- Dr. Anupam Joshi
- Dr. Milton Halem
- Dr. Michael Grasso
]]>
Full Title: MS defense: Detection of Unsafe Action in Laparoscopic Cholecystectomy Video MS defense Detection of Unsafe Action in Laparoscopic Cholecystectomy Video Ashwini Lahane 10:00am...
http://www.cs.umbc.edu/2011/04/3640/
https://dev.my.umbc.edu/api/v0/pixel/news/6631/guest@my.umbc.edu/e04a4c0a7da4632d440e4da3d622f9d4/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
false
Wed, 27 Apr 2011 00:31:42 -0400
Complex-valued Adaptive Signal Processing:...
Full Title: Complex-valued Adaptive Signal Processing: Applications in Medical Imaging
EE Graduate Seminar
Complex-valued Adaptive Signal Processing:
Applications in Medical Imaging
Prof. Tulay Adali
Machine Learning for Signal Processing Laboratory
CSEE Dept/UMBC
1-2pm Friday, 29 April 2011, ITE 237
Complex-valued signals arise frequently in applications as diverse as communications, radar, geophysics, optics, and biomedicine, as most practical modulation formats are of complex type and applications such as radar and magnetic resonance imaging lead to data that are inherently complex valued. The complex domain, however, presents unique challenges for signal processing, in particular for adaptive nonlinear processing, and as a result, until recently, most algorithms derived for the complex domain have taken engineering shortcuts limiting their usefulness. The most common one among those has been assuming the circularity of the signal, thus ignoring the information conveyed by the phase. Similarly when taking gradients in the complex domain, a "split" approach that performs optimization separately with respect to the real and imaginary variables has been the dominant practice.
There have been important advances in the area within the last decade that clearly demonstrate that noncircularity is an intrinsic characteristic of many signals of practical interest, and when taken into account, the methods developed for their processing may provide significant performance gains. Similarly, it has been shown that using Wirtinger calculus, all calculations can be carried out in a manner similar to real-valued calculus while keeping all the computations in the complex domain.
In this talk, after a brief introduction to optimization using Wirtinger calculus and statistics in the complex domain, and then I will give examples from some of the recent work conducted at the MLSP-Lab.
]]>
Full Title: Complex-valued Adaptive Signal Processing: Applications in Medical Imaging EE Graduate Seminar Complex-valued Adaptive Signal Processing: Applications in Medical Imaging Prof....
http://www.cs.umbc.edu/2011/04/complex-valued-adaptive-signal-processing-applications-in-medical-imaging/
https://dev.my.umbc.edu/api/v0/pixel/news/6630/guest@my.umbc.edu/2da1cbafb245f25aa2d3cd5a43b753c9/api/pixel
electrical-engineering
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
false
Wed, 27 Apr 2011 00:15:37 -0400
MS defense: Boosting Base Station Anonymity in...
Full Title: MS defense: Boosting Base Station Anonymity in Wireless Sensor Networks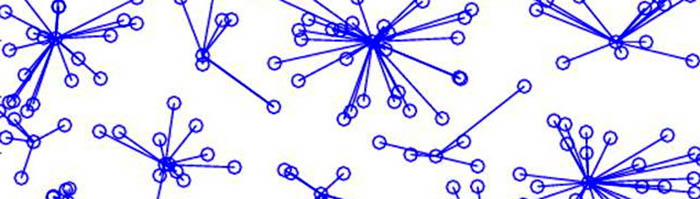
MS Defense
Exploiting Architectural Techniques for Boosting
Base Station Anonymity in Wireless Sensor Networks
Zhong Ren
2:00pm Thursday, 28 April 2011, ITE 346
Wireless Sensor Networks (WSNs) can be deployed to serve mission-critical applications in hostile environments such as battlefield and territorial borders. In these setups, the WSN may be subject to attacks in order to disrupt the network operation. The most effective way for an adversary to do so is by targeting the Base-Station (BS), where the sensor data are collected in the field. By identifying and locating the BS, the adversary can launch attacks to damage or disrupt the operation of the BS. Therefore, maintaining the BS anonymity is of utmost importance in WSNs.
In this thesis we propose three novel approaches to boost the anonymity of the BS nodes to protect them from potential threats. We first explore the deployment of more BS nodes. We compare the BS anonymity of one versus multiple stationary BS under different network topologies. Our results show that having more base-stations can boost both the average and max anonymity of BS nodes. We further provide guidelines on a cost versus anonymity trade-off to determine the most suitable BS count for a network. Second we exploit the mobility of base-stations and explore the effect of relocating some of the existing BS nodes to the lowest anonymity regions. Our results show that having one mobile BS can dramatically boost the anonymity of the network and moving multiple BS does not provide much value. Finally, we propose to pursue dynamic sensor to cluster re-association to confuse the adversary. This can be employed when base-stations cannot safely move.
Committee members:
- Mohamed Younis (Chair)
- Yun Peng
- Charles Nicholas
]]>
Full Title: MS defense: Boosting Base Station Anonymity in Wireless Sensor Networks MS Defense Exploiting Architectural Techniques for Boosting Base Station Anonymity in Wireless Sensor...
http://www.cs.umbc.edu/2011/04/ms-defense-boosting-base-station-anonymity-in-wireless-sensor-networks/
https://dev.my.umbc.edu/api/v0/pixel/news/6623/guest@my.umbc.edu/7cb8d0d59285480b0f11eedb1904ef39/api/pixel
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
false
Tue, 26 Apr 2011 16:19:16 -0400
Two bioinfomatics talks, Wed 27 April

The UMBC Biological Sciences Department will host two talks on bioinformatics on Wednesday, April 27.
Bioinformatics: Illustrations from 20 years at NCB*I, Dr. Jim Ostell, NCBI, NIH, 11:00am Wednesday 27 April, BS-004
Jim Ostell is one of the founders of NCBI, he will give a general audience talk, ideal for students and faculty from Biology, CS, Chemistry, Statistics and Math that would like to learn what Bioinformatics is about and the history of one of the main bioinformatic center in the world.
Network and state space models: science and science fiction approaches to cell fate predictions, John Quackenbush, Harvard, 12:00pm Wednesday 27 April BS-004
Two trends are driving innovation and discovery in biological sciences: technologies that allow holistic surveys of genes, proteins, and metabolites and a realization that biological processes are driven by complex networks of interacting biological molecules. However, there is a gap between the gene lists emerging from genome sequencing projects and the network diagrams that are essential if we are to understand the link between genotype and phenotype. ‘Omic technologies were once heralded as providing a window into those networks, but so far their success has been limited, in large part because the high-dimensional they produce cannot be fully constrained by the limited number of measurements and in part because the data themselves represent only a small part of the complete story. To circumvent these limitations, we have developed methods that combine ‘omic data with other sources of information in an effort to leverage, more completely, the compendium of information that we have been able to amass.Here we will present a number of approaches we have developed, with an emphasis on the how those methods have provided into the role that particular cellular pathways play in driving differentiation, and the role that variation in gene expression patterns influences the development of disease states. Looking forward, we will examine more abstract state-space models that may have potential to lead us to a more general predictive, theoretical biology.
]]>
The UMBC Biological Sciences Department will host two talks on bioinformatics on Wednesday, April 27. Bioinformatics: Illustrations from 20 years at NCB*I, Dr. Jim Ostell, NCBI, NIH, 11:00am...
http://www.cs.umbc.edu/2011/04/two-bioinfomatics-talks-wednesday-april-27/
https://dev.my.umbc.edu/api/v0/pixel/news/6607/guest@my.umbc.edu/e2989c5307dd1f7cc00613cae136065c/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
false
Tue, 26 Apr 2011 09:12:41 -0400
MS defense: Privacy Preservation in Context-Aware Systems

MS Defense
Privacy Preservation in Context-Aware Systems
Pramod Jagtap
1:00pm Wednesday, 27 April 2011, ITE 210
Recent years have seen a confluence of two major trends – the increase of mobile devices such as smart phones as the primary access point to networked information and the rise of social media platforms that connect people. Their convergence supports the emergence of a new class of context-aware geosocial networking applications. While existing systems focus mostly on location, our work centers on models for representing and reasoning about a more inclusive and higher-level notion of context, including the user’s location and surroundings, the presence of other people and devices, feeds from social networking systems they use, and the inferred activities in which they are engaged. A key element of our work is the use of collaborative information sharing where devices share and integrate knowledge about their context. This introduces the need for privacy and security mechanisms. We present a framework to provide users with appropriate levels of privacy to protect the personal information their mobile devices are collecting including the inferences that can be drawn from the information. We use Semantic Web technologies to specify high-level, declarative policies that describe user’s information sharing preferences. We have built a prototype system that aggregates information from a variety of sensors on the phone, online sources, and sources internal to the campus intranet, and infers the dynamic user context. We show how our policy framework can be effectively used to devise better privacy control mechanisms to control information flow between users in such dynamic mobile systems.
Presentation
Thesis Committee:
- Dr. Anupam Joshi (chair)
- Dr. Tim Finin
- Dr. Yelena Yesha
- Dr. Laura Zavala
]]>
MS Defense Privacy Preservation in Context-Aware Systems Pramod Jagtap 1:00pm Wednesday, 27 April 2011, ITE 210 Recent years have seen a confluence of two major trends – the increase of...
http://www.cs.umbc.edu/2011/04/privacy-preservation-in-context-aware-systems/
https://dev.my.umbc.edu/api/v0/pixel/news/6604/guest@my.umbc.edu/841b685c5410a71517c5b2df8c2fd0bb/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
false
Mon, 25 Apr 2011 22:52:55 -0400
Mon, 25 Apr 2011 22:52:55 -0400
MS defense: A Framework for GPU 3D Model...
Full Title: MS defense: A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion
MS Defense
A Framework for GPU 3D Model Reconstruction
Using Structure-from-Motion
Yu Wang
10:00am Thursday, 28 April 2011, ITE 352
A framework for three-dimensional (3D) model reconstruction is described in this thesis. The primary application is scanning forest canopies and assisting scientific applications such as fire hazard evaluation and vegetation biomass estimation, using photos taken from a radio-controlled helicopter, although the methods apply to any series of photographs taken along a path. The approach is based on the fact that the photos are taken in a continuous path, thus taking advantage of the adjacency between images. The major contributions of this project are 1) introduce a linear time complexity algorithm that reduces number of image pairs to match for datasets obtained in a continuous path. 2) present an optimized high performance framework for GPU 3D reconstruction using structure-from-motion.
Thesis Committee:
- Dr. Marc Olano, Chair
- Dr. Penny Rheingans
- Dr. Erle Ellis
]]>
Full Title: MS defense: A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion MS Defense A Framework for GPU 3D Model Reconstruction Using Structure-from-Motion Yu Wang...
http://www.cs.umbc.edu/2011/04/3569/
https://dev.my.umbc.edu/api/v0/pixel/news/6593/guest@my.umbc.edu/f7ee8e2e9b9790faf06d980848806cc5/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Mon, 25 Apr 2011 20:51:44 -0400
MS defense: eXtensible Dynamic Form (XDF) for...
Full Title: MS defense: eXtensible Dynamic Form (XDF) for Supplier Discovery
MS Thesis Defense
eXtensible Dynamic Form (XDF) for Supplier Discovery
Yan Kang
1:00PM Tuesday, 26 April 2011, ITE 346
Discovery of suppliers (supplier discovery) is essential for building a flexible network of suppliers in a supply chain. The first step for supplier discovery is to collect manufacturing capabilities of suppliers and requirements of customers. In traditional e-marketplaces, online form interfaces are typically used to collect the requirements and capabilities. However, those forms are mostly lack of flexibility to capture a variety of requirements and capabilities in a structured way. In this thesis, we propose new innovative form architecture called eXtensible Dynamic Form (XDF) to facilitate data collection process of supplier discovery.
This architecture provides several key innovations including: 1) architecture for users (suppliers or customers) to create new structure of form for their own contents; 2) an intelligent search engine facilitating users to reuse the existing form components 3) hierarchical representation of the requirements and capabilities as XML instances. Experimental results demonstrate that the proposed architecture is valuable for facilitating the supplier discovery process.
Thesis Committee:
- Dr. Charles Nicholas
- Dr. Yun Peng (Chair)
- Dr. Yelena Yesha
]]>
Full Title: MS defense: eXtensible Dynamic Form (XDF) for Supplier Discovery MS Thesis Defense eXtensible Dynamic Form (XDF) for Supplier Discovery Yan Kang 1:00PM Tuesday, 26 April 2011,...
http://www.cs.umbc.edu/2011/04/ms-defense-extensible-dynamic-form-xdf-for-supplier-discovery/
https://dev.my.umbc.edu/api/v0/pixel/news/6585/guest@my.umbc.edu/97312fabd23cb4829febec3f4df9dd11/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
3
0
false
Mon, 25 Apr 2011 14:18:06 -0400
Mon, 25 Apr 2011 14:18:06 -0400
MS defense: Recovering from Soft Node Failures in...
Full Title: MS defense: Recovering from Soft Node Failures in Wireless Sensor Networks using Neural Networks
MS Thesis Defense
Recovering from Soft Node Failures in
Wireless Sensor Networks using Neural Networks
Shivvasangari Subramani
9:00am Tuesday, 26 April 2011, ITE 346
In the past few years, wireless sensor networks (WSNs) have become important in different applications because of their robustness in hostile environments. WSNs need to perform in a timely manner in the face of interference, attacks, accidents, and failures. Being a battery operated system, there is a trade-off between performance and energy utilization. In this thesis we focus on WSN accuracy and consider ways to improve the performance of WSNs when sensors become damaged, resulting in poor input signal quality. When all other components of the sensor like the processor, memory, and battery are working, our proposed solution is to learn to undo the damage in a node by training on neighbors sensor values.
Thesis Committee:
- Dr. Anupam Joshi
- Dr. Tim Oates (chair)
- Dr. Mohamed Younis
]]>
Full Title: MS defense: Recovering from Soft Node Failures in Wireless Sensor Networks using Neural Networks MS Thesis Defense Recovering from Soft Node Failures in Wireless Sensor Networks...
http://www.cs.umbc.edu/2011/04/3555/
https://dev.my.umbc.edu/api/v0/pixel/news/6581/guest@my.umbc.edu/11f5133ee01961143c83041c7a699b8d/api/pixel
computer-science
events
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Mon, 25 Apr 2011 11:59:11 -0400
Mon, 25 Apr 2011 11:59:11 -0400
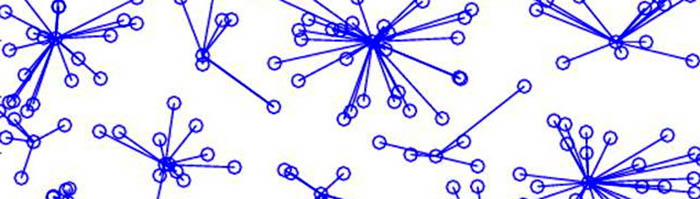
MS defense: Graph-Theoretic Approach to Collusion...
Full Title: MS defense: Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems
MS Thesis Defense
A Graph-Theoretic Approach to
Collusion Detection in Multi-Agent Systems
Peter Hamilton
9:00am Thursday, 28 April 28 2011, ITE 325B
The study of trust and cooperation is a major component of multi-agent systems research. Such work often focuses on how best to estimate the reliability of a specific agent, or how to create strategies and protocols that engender the most cooperation from the most agents. However, when cooperation is not a desired aspect of a multi-agent system, these actions define collusive behavior, which can have a significant impact on the dynamics of the system.
This thesis defines a generic, graph-theoretic approach to collusion detection known as CODING. This approach detects group-based collusion, targeting two basic collusion mechanisms that rely on large numbers of colluding agents for success. CODING analyzes and classifies agent interactions from the system and constructs a series of interaction graphs from this data. These graphs are processed for structures that correspond to collusion mechanisms; the agents composing these structures are reported as colluders. CODING is applied to a game theory domain, in which it must detect agents adhering to group strategies in round-robin tournaments composed of single-player strategies.
Thesis Committee:
- Dr. Marie desJardins (chair)
- Dr. Tim Finin
- Dr. Tim Oates
]]>
Full Title: MS defense: Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems MS Thesis Defense A Graph-Theoretic Approach to Collusion Detection in Multi-Agent Systems...
http://www.cs.umbc.edu/2011/04/ms-defense-graph-theoretic-approach-to-collusion-detection-in-multi-agent-systems/
https://dev.my.umbc.edu/api/v0/pixel/news/6571/guest@my.umbc.edu/c44e3e2bab826ef200fa4aa79e13bb83/api/pixel
computer-science
events
graduate
news
other
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
false
Sun, 24 Apr 2011 23:38:20 -0400