PhD defense: Michael Tope, 2-4pm 8/16, ITE325
Ph.D. Dissertation Defense
Near Optimal Sampling to Discover and Bound the Communication Rate of a Discrete Memoryless Channel
Michael Tope
Date: August 16, 2023 at 2:00pm -- 4:00pm EDT
Location: ITE 325B conference room or Webex
Committee: Drs. Joel Morris (Chair/Advisor), Tulay Adali (Co-Chair), E. F. Charles LaBerge, Christopher Marron, Anindya Roy
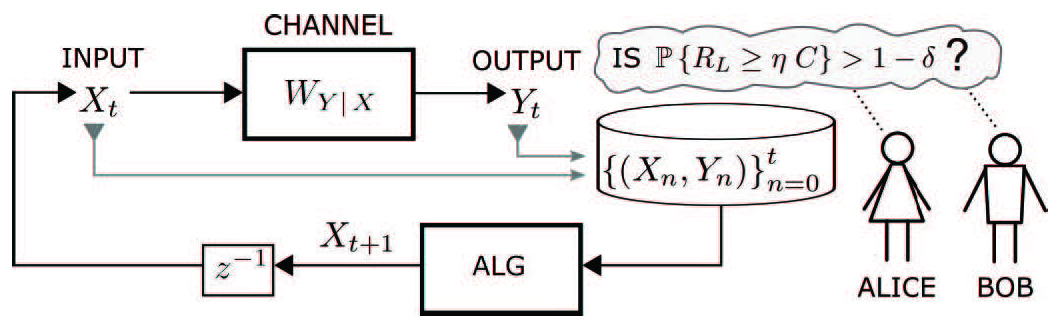
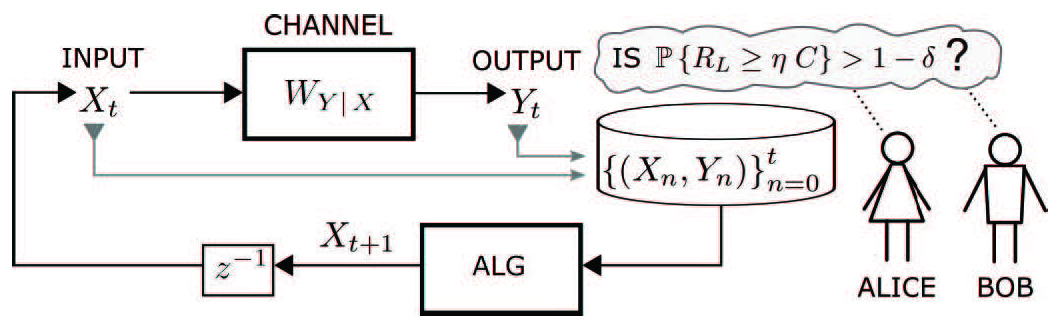
The aim of this research is to introduce, develop and evaluate active learning algorithms that provide near-optimal high-probability bounds on the channel capacity across a discrete memoryless channel (DMC), where the only information about the channel internals (i.e., the channel law) is from a set of observed input-output sample pairs (i.e., channel probes). Channel capacity is the maximum rate (on average for each value sent into the channel) at which information can flow across the channel with an arbitrarily low error rate.
Extending results on the discrete memoryless compound channel, which is comprised of deterministic constraints on the channel law uncertainty, we first develop an offline algorithm to process an observed set of N input-output sample pairs (probes) to compute lower and upper bounds on channel capacity (such that the bounds hold with high probability). A key ingredient of this result is our new probability approximately correct (PAC) sublevel set bound that improves the convergence rate of Sanov's Theorem from O(log(N)/N) to O(log(log(N)/N) (where the convergence rate is the 'big Oh' Bachmann-Landau limiting behavior). The experimental (simulation) results match the analytical results.
Adapting techniques from pure-exploration multi-arm bandit problems, we further develop an online algorithm aimed at minimizing the sample complexity (i.e., the number of channel probes or samples of the DMC) required to establish a lower-bound channel rate RL that satisfies several stopping criteria, where the lower bound rate RL approaches the channel capacity with high probability. We show that if the sample complexity of any optimal online algorithm (including a non-feasible clairvoyant algorithm that is given side information to simplify the analysis) is O(N) samples, then our online algorithm requires less than O(N*log(log(N))) sequential channel probes. Thus, we prove that our algorithm is within a sub-logarithmic factor of optimal (i.e. near optimal).
The results of this research may provide a deeper general understanding of active machine learning algorithms.
]]>
Ph.D. Dissertation Defense Near Optimal Sampling to Discover and Bound the Communication Rate of a Discrete Memoryless Channel Michael Tope Date: August 16, 2023 at 2:00pm -- 4:00pm EDT...
https://dev.my.umbc.edu/api/v0/pixel/news/134461/guest@my.umbc.edu/1db881c130dcae75d75086a9331a8ae7/api/pixel
defense
phd
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 31 Jul 2023 09:41:38 -0400
UMBC alumnus Kemal Akkaya selected as a 2023 IEEE Fellow
Received Ph.D. in 2005, mentored by Prof. Mohamed Younis
Congratulations to UMBC alumnus Kemal Akkaya, Ph.D. '
05, Computer Science, for his selection as an IEEE fellow in 2023. He was cited for contributions to routing and topology management in wireless ad hoc and sensor networks.
Dr.
Akkaya completed his dissertation at UMBC on Energy and QoS Aware Routing Protocols for Wireless Sensor Networks in Computer Science in 2005 under the guidance of mentor Professor Mohamed Younis.
The IEEE Grade of Fellow is conferred by the IEEE Board of Directors upon a person with an outstanding record of accomplishments in any of the IEEE fields of interest. The total number selected in any one year cannot exceed one-tenth of one- percent of the total voting membership. IEEE Fellow is the highest grade of membership and is recognized by the technical community as a prestigious honor and an important career achievement.
We congratulate the 363 students who graduated from one of the CSEE programs last week and look forward to the wonderful things they will accomplish as they embark on their careers.
The
Fall 2022 graduates included:
- 155 undergraduate students receiving BS degrees in computer engineering or computer science
- 77 graduate students awarded an MS degree in computer engineering, computer science, or electrical engineering;
- 116 graduate students receiving an MPS (Masters of Professional Studies) degree in cybersecurity or data science
- 15 graduate students obtaining a Ph.D. in computer engineering, computer science, or electrical engineering.
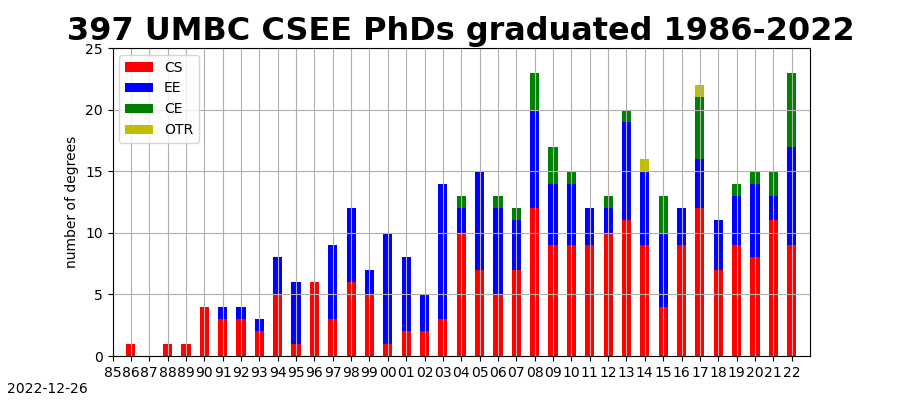
A total of
397 students have received
Ph.D. degrees from the department since
Dr. Sanjeev Ahuja completed his dissertation in 1986 on applying abductive reasoning to analyzing and classifying errors in discrete sequential processes. We are very proud of our Ph.D. graduates, who contributed to advancing knowledge in their fields as doctoral students and continue to contribute in their current positions in academia, industry, or government organizations. See our
complete list of Ph.D. graduates with information on their dissertations, mentors, and positions.
PhD Dissertation Defense
Backdoor Attacks in Computer Vision: Towards Adversarially Robust Machine Learning Models
12-2 ET Friday, 18 November 2022, WebEx
Committee: Drs. Hamed Pirsiavash (Advisor/Co-Chair), Anupam
Joshi (Chair), Tim Oates, Tom Goldstein (UMCP), Dr. Pin-Yu Chen (IBM)
Deep Neural Networks (DNNs) have become the standard building block in numerous machine learning applications, including computer vision, speech recognition, machine translation, and robotic manipulation, achieving state-of-the-art performance on complex tasks. The widespread success of these networks has driven their deployment in sensitive domains like health care, finance, autonomous driving, and defense-related applications.
However, DNNs are vulnerable to adversarial attacks. An adversary is a person with malicious intent whose goal is to disrupt the normal functioning of a machine learning pipeline. Research has shown that an adversary can tamper with the training process of a model by injecting misrepresentative data (poisons) into the training set. Moreover, if provided control over the training process as a third party, they can deliver a model to a victim, which deviates from normal behavior. These are called backdoor attacks. The manipulation is done in a way that the victim's model will malfunction only when a trigger is pasted on a test input. For instance, a backdoored model in a self-driving car might work accurately for days before it suddenly fails to detect a pedestrian when the adversary decides to exploit the backdoor. Vulnerability to backdoor attacks is dangerous when deep learning models are deployed in safety-critical applications.
This dissertation studies ways in which state-of-the-art deep learning methods for computer vision are vulnerable to backdoor attacks and proposes defense methods to remedy the vulnerabilities. We push the limits of our current understanding of backdoors and address the following research questions.
Can we design practical backdoor attacks? We propose Hidden Trigger Backdoor Attack - a novel clean-label backdoor attack where the poisoned images do not contain a visible trigger. This enables the attacker to keep the trigger hidden until its use at test-time. We believe such practical attacks reveal an important vulnerability of deep learning models. These flaws need to be studied extensively before deploying models in critical real-world applications.
Is it secure to train models on large-scale public data? Self-supervised learning (SSL) methods for vision have utilized large-scale unlabeled data to learn rich visual representations. These methods use public images downloaded from the web, e.g., Instagram-1B and Flickr image datasets. We show that if a small part of the unlabeled training data is poisoned, SSL methods are vulnerable to backdoor attacks. Backdoor attacks are more practical in self-supervised learning, since the use of large unlabeled data makes data inspection to remove poisons prohibitive. Hence, using large and diverse data to remove data biases and reduce labeling costs might unknowingly set up avenues for adversarial manipulation. Practitioners must make informed choices when choosing training data for machine learning models.
Can we design efficient and generalizable backdoor detection methods? Methods to detect backdoors in trained models have relied on analysis of model behavior on carefully chosen inputs. But often, this analysis has to be repeated for a new model. We propose a backdoor detection method that optimizes for a set of images which, when forwarded through any model, indicates successfully whether the model contains a backdoor. Our "litmus" test for backdoored models improves on state-of-the-art methods without requiring access to clean data during detection. It is computationally efficient and generalizes to new triggers as well as new architectures. We effectively detect backdoor attacks on thousands of networks with different architectures trained on four benchmark datasets, namely the German Traffic Sign Recognition Benchmark (GTSRB), MNIST, CIFAR10, and Tiny-ImageNet. This will serve as a benchmark for future research.
Do architectural design choices contribute to backdoor robustness? We find an intriguing difference between Vision Transformers and Convolutional Nets; interpretation algorithms effectively highlight the backdoor trigger on test images for transformers but not for CNNs when attacked with Hidden Trigger Backdoor Attacks. Based on this observation, we find that a test-time image blocking defense reduces attack success rate by a large margin for transformers. We show that such blocking mechanisms can be incorporated during the training process to improve robustness even further. We believe our findings will encourage the community to make better design choices in developing novel architectures robust to backdoor attacks.
]]>
PhD Dissertation Defense Backdoor Attacks in Computer Vision: Towards Adversarially Robust Machine Learning Models PhD Candidate: Aniruddha Saha (Computer Science) 12-2 ET Friday, 18...
https://dev.my.umbc.edu/api/v0/pixel/news/129142/guest@my.umbc.edu/6086ff0dc18b53a492753e50848966c0/api/pixel
ai
defense
phd
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 11 Nov 2022 17:08:36 -0500
Janerra Allen, EE PhD student, in UMBC Magazine
Her brain imaging research helps understand brain functions

Allen (far left) celebrates with UMBC colleagues as UMBC President Valerie Sheares Ashby accepts the 2022 Technologist of the Year award at the Women of Color STEM DTX Conference.
The latest issue of UMBC Magazine features CSEE Ph.D. student Janerra Allen who is working with Professor Fow-Sen Choa on advancing and applying brain imaging research. Janerra is a first-generation college student from Brooklyn, a student leader, and a Meyerhoff Graduate Fellow.
She recently presented research results on analyzing how different regions of the brain are engaged and if they are working together at the SPIE conference on Defense and Commercial Sensing.
In addition to her academic studies and research, Janerra is an active student leader. She is the president of the Black Graduate Student Organization (BGSO), GSA Senator for the College of Engineering and Information Technology, and serves on the tenure track search committee for the CSEE Department.
You can read the full interview with Janerra Allen in the Fall UMBC Magazine here.
]]>
Allen (far left) celebrates with UMBC colleagues as UMBC President Valerie Sheares Ashby accepts the 2022 Technologist of the Year award at the Women of Color STEM DTX Conference. The latest...
https://umbc.edu/stories/meet-a-retriever-janerra-allen-ph-d-student-in-electrical-engineering/
https://dev.my.umbc.edu/api/v0/pixel/news/129076/guest@my.umbc.edu/7c7fc5e147d306f7f8887f04998de435/api/pixel
phd
research
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
7
0
true
Thu, 10 Nov 2022 11:09:47 -0500
Sat, 12 Nov 2022 13:03:17 -0500
PhD Defense: Lifelong Multitask Learning Algorithms
Nonlinearity, Scalability, and Applications
Dissertation Defense
Lifelong Multitask Learning Algorithms: Nonlinearity, Scalability and Applications
Rami Mowakeaa
Electrical Engineering, CSEE Department
4-6:00 pm Wed., 5 October 2022, ITE 325B
With the deluge of data in the modern world, machine learning has become a mainstay of industry and science. Machine learning algorithms aim to find underlying relationships hidden in a task that agree with prior knowledge and best generalize to unseen data making as few assumptions about the nature of the data as possible. In cases where several tasks are expected to share underlying structure, multitask learning aims to identify and exploit this shared structure to benefit all tasks. In functional magnetic resonance imaging (fMRI), for example, datasets collected from a group of subjects can be separated into statistically independent sources by joint processing to yield improved performance over what can be achieved considering each dataset alone. In other applications, such as recommender systems, tasks and the corresponding datasets may arrive sequentially over time. This introduces further challenges associated with online processing and modeling of the joint structure in an efficient manner -- key issues toward lifelong learning. Furthermore, where linear models are insufficient to adequately describe underlying task relations, it is desirable to capitalize on rich nonlinear function spaces to develop machine learning algorithms.
In this work, multitask learning is developed and applied to various machine learning problems. In unsupervised statistical learning, an independent vector analysis algorithm is developed based on a flexible, yet simple, family of distributions termed the complex-valued multivariate generalized Gaussian distribution. In lifelong supervised and reinforcement learning, kernel dictionary learning is used to capture the joint structure of streaming tasks in rich reproducing kernel Hilbert spaces. A sparsification technique is utilized to mitigate the effects of growing computational and storage complexity typical of kernel methods without sacrificing convergence guarantees. This approach is further generalized to tasks where the data emanate from different sources, or views, yielding a kernel lifelong multitask multiview learning algorithm. To affirm the effectiveness of the algorithms developed, experiments based on synthetic as well as real-world datasets are performed. The convergence of the developed supervised lifelong learning algorithms is also rigorously established.
Committee: Drs. Seung-Jun Kim (Chair), Tulay Adali, Tim Oates, Mohamed Younis, Ramana Vinjamuri
]]>
Dissertation Defense Lifelong Multitask Learning Algorithms: Nonlinearity, Scalability and Applications Rami Mowakeaa Electrical Engineering, CSEE Department 4-6:00 pm Wed., 5 October...
https://dev.my.umbc.edu/api/v0/pixel/news/128164/guest@my.umbc.edu/d149463d674322b1224220ec271bd47a/api/pixel
defense
machine-learning
phd
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 04 Oct 2022 10:38:15 -0400
Interweave Cognitive Radio for 4G Long Term Evolution and 5G
PhD Defense: Brian Stevens, Computer Engineering
Ph.D. Dissertation Defense
Interweave Cognitive Radio for 4G Long Term Evolution and 5G New Radio Self-Reliant Networks
Brian Stevens, Computer Engineering
1-3 pm ET Tuesday, 20 September 2022, Zoom
Committee: Drs. Mohamed Younis (Chair), Tulay Adali, Sunita Bhatia
(JHUAPL), Seung-Jun Kim, Dmitri Perkins, Ting Zhu
Existing cellular networks have untapped radio frequency resources, also known as white space, available for cognitive radio applications. A secondary network can opportunistically interweave communication within the white space of an existing cellular signal by leveraging cognitive radio. This thesis presents a novel methodology for forming a cognitive interwoven self-reliant secondary network with no additional physical infrastructure, collaboration from the existing primary network, and software or hardware changes in the primary network. The methodology is tested first with 4G and later with 5G cellular technological standards. For the physical layer, this thesis optimizes synchronization as the initial step in aligning to a cellular signal in time, frequency, and sector identity. We improve synchronization through sensitivity, execution time, and applies a threshold to form a "cell detector" instead of the traditional "cell search," which only considers the most detectable signal.
After synchronization, resource detectors monitor the available spectral resources of the entire cellular infrastructure. Modern cellular networks have grown in complexity and become an ecosystem that includes the host technologies, such as 4G Long Term Evolution (LTE) and 5G New Radio (NR), along with subsystems such as narrowband internet of things (NB-IoT), category M1 (Cat-M1/LTE-M), observed time difference of arrival (OTDOA), and support for 4G/5G coexistence using dynamic spectrum sharing (DSS). Such an increased complexity has driven the need for network monitoring to enable load tracking, congestion control, spectral efficiency analysis, intrusion detection, and cognitive radio communications.
This thesis develops resource monitoring that can passively monitor the entire cellular ecosystem, including reservations configured with high-layer messages that are only accessible to in-network, active, and sometimes user-specific equipment. Resource monitoring provides white-space reservations for cognitive communications. We define interference control to prevent interference with the primary network through physical layer access schemes and power control cluster protocols to access resources safely. With the added complexity of 5G as a host technology, our research leverages geospatial beamforming of known signals as spatially dependent white space. In this case, the known synchronization signal burst must be detected with a "beam detector" instead of a "beam search" to properly use beam resources that are not close to cognitive radio nodes. The thesis applies the self-reliant methodology, which defines opportunistic access and power control protocols that limit interference between cellular networks in both the time and frequency domains with additional support in the geospatial domain for 5G NR. Our research determines that an adapted version of Slotted ALOHA for medium access control (MAC) with a no-back-off contention fits the self-reliant approach of our work and timing constraints found in 4G LTE and 5G NR networks.
]]>
Ph.D. Dissertation Defense Interweave Cognitive Radio for 4G Long Term Evolution and 5G New Radio Self-Reliant Networks Brian Stevens, Computer Engineering 1-3 pm ET Tuesday, 20...
https://dev.my.umbc.edu/api/v0/pixel/news/127760/guest@my.umbc.edu/e64a5f0ad7f42f9b06c9171ad1fbc11c/api/pixel
cognitive
defense
phd
radio
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 19 Sep 2022 16:52:50 -0400
PhD Defense: Md Shafiqul Islam, Computer Eng., 9-11am 9/14
Communication Across the Air-Water Interface

PhD Defense, Computer Engineering
Analysis and Protocols to Establish Downlink for
Communication Across the Air-Water Interface
Md Shafiqul Islam
9-11 am Wed. 14 Sept. 2022 via WebEx
In underwater wireless networks (UWNs), conventionally there is no direct communication between an underwater node and a remote command center, because there is no known physical signal that propagates well in both the water and air mediums. Radio signals are the popular choice in the air while acoustics are the prime means for communication underwater. Hence, the typical architecture of an UWN includes surface nodes or gateways which have dual modems, an acoustic modem to communicate with underwater nodes and a radio modem to interact with terrestrial command centers. However, such an architecture is logistically complicated and could expose the network to security threat. Therefore, it is desirable to establish a direct communication from air to underwater without having any intermediate surface node.
This dissertation opts to fulfill such a need by pursuing two viable solutions, namely, using visual light communications (VLC) and exploiting the optoacoustic (photoacoustic) effect. Through extensive analysis and experiments we show that VLC is an effective means for scenarios where the distance between the airborne and underwater nodes is relatively short. We first analyze the coverage area and intensity inside the water for a light transmitter placed in the air. We then provide guidelines for using single and multiple light sources to establish robust VLC links under rough environmental conditions like high water current and turbidity. Furthermore, we investigate effective modulation techniques that suit VLC. For long distance communication, VLC is not a viable option since light gets absorbed at an exponentially growing rate with the increase of water depth. Photoacoustic (PA) energy transfer mechanism is the promising method for long distance communication.
Although the use of the photoacoustic mechanism is quite common in medical imaging, little progress has been made on building the communication protocol stack for air-to-underwater communication. In our research work, at first, we have studied the channel characteristics of the PA based air-to-underwater communication. We show that by carefully choosing the relative position of the airborne unit and underwater node, we can generate a narrowband acoustic signal which is very crucial for long distance communication. Moreover, we develop suitable modulation and demodulation schemes for PA communication.
Committee: Drs. Mohamed Younis, Fow-Sen Choa, Gary Carter, Lloyd Emokpae, Akram Fadhl N. Ahmed
]]>
PhD Defense, Computer Engineering Analysis and Protocols to Establish Downlink for Communication Across the Air-Water Interface Md Shafiqul Islam 9-11 am Wed. 14 Sept. 2022 via WebEx ...
https://dev.my.umbc.edu/api/v0/pixel/news/127467/guest@my.umbc.edu/7195032010c7ec3a0266f38c0b84b179/api/pixel
computer-engineering
defense
phd
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 11 Sep 2022 22:08:42 -0400
Sun, 11 Sep 2022 22:10:58 -0400