A Beginner’s Guide to Privilege

This guest post by Madison Miller was originally posted on the Women’s Center at UMBC blog.
In addition to working at the Women’s Center as a student staff member, I also serve as a Resident Assistant in a first-year residential hall on campus. Recently, my paraprofessional staff and I have been exploring the topic of privilege by participating in meaningful discussions about the different forms that it can take on in our society. These conversations and shared experiences of my fellow staff members have encouraged me to dive into a deeper, more personal investigation of privilege and how it relates to my identity and my unique life experiences.
For those who may be unfamiliar with the concept of privilege, a dictionary definition classifies it as a unique benefit or immunity available only to a particular community or group of people. Yet what the dictionary definition fails to mention is that privilege is neither earned nor deserved by any specific group that reaps its benefits. In reality, privilege is innate; it is a birthright that is automatically given to those who hold membership in a certain group or community. Privilege takes on several forms in society relating to identities such as gender, ability, class, race, and sexuality. It should be mentioned that one may simultaneously experience a certain level of privilege in one area of their identity while also experiencing a lack of privilege in another area. Privilege, or the lack thereof, isn’t also always necessarily visible to the eye of a passerby. Yet these privileges are often at the root of social inequalities that exist in our society today They may also cloud and bias our viewpoints of who don’t share the same privileges as ourselves, causing us to make unwarranted assumptions and conclusions about others. Therefore, it is important that we have conversations with each other in order to better recognize and effectively deal with our own unique privileges. In my experience, it seems that when a privilege is pointed out to it’s owner, that person often has a tendency to become defensive about the fact that they are not responsible for their privilege. While there is some truth to be found in this statement, I believe that privilege is not necessarily something of which to be ashamed, but something of which we should be aware. In order to remedy the social inequalities caused by our privileges, we must first understand how these privileges negatively affect and immobilize others. Perhaps our privileges aren’t necessarily the problem: maybe it’s us. After all, we do not choose our privileges, but we do choose how we live with them. 
What are my privileges? One of the privileges that I am most connected to is my educational privilege. Although I take out student loans and receive aid from my university, I have access to higher education and I am a college student (at an honors university, nonetheless) that is financially able to support myself through my undergraduate education. Because my reality is not possible for everyone, I consider myself to be truly fortunate in this situation. But in my eyes, simply being grateful is not enough. I want to use my privileges to help better others. As a psychology and elementary education double major, I have recently been thinking a lot about working in a high needs school after my graduation from UMBC. I am a strong believer in the idea that everyone, regardless of geographic location, socioeconomic status, disability, or race, is deserving of a quality education that enables success and potential. Although I am aware that this will be a great challenge, I am hopeful for the changes I wish to make in the world, even if only in the life of one child.
One of my favorite sayings comes from the movie Spiderman and it says, “With great power, comes great responsibility.” It is no secret that our privileges put us in a place of power. What may not be so obvious, however, is that this power should call upon us to think critically about ourselves and our ability to support and help advance those who experience a lack of privilege. It isn’t an easy task by any means, but it is a necessary challenge that we must undertake should we ever hope to remedy the social inequalities that paralyze so many members of our society.

Think about it: What privileges do you have? How are you “owning” them for the better?
To learn more about privilege, check out these helpful resources:
Pedagogy of Privilege Ted Talk A helpful TED Talk that discusses how to begin conversations with others about privilege.
Privilege Walk Activity An activity that highlights examples of various privileges.
A Comic on White Privilege A Buzzfeed comic that explains what it means to have white privilege.
The Reproduction of Privilege An NY Times Article that discusses the privileges associated with post-secondary education.
For more on power and privilege, be sure to check out the upcoming CSJ event Critical White Male Allies: C’Mon In! The Water’s Fine! on Wednesday from 5-6pm in Commons 318. Jeff Cullen, Director of Student Judicial Programs, will lead an interactive workshop on critical allyship. With a frank discussion of some of the ways he has made mistakes and learned from them as a white male ally, he will create a space for participants to have an honest dialogue about the challenges and strategies to effective and self-reflexive allyship.
]]>
This guest post by Madison Miller was originally posted on the Women’s Center at UMBC blog. In addition to working at the Women’s Center as a student staff member, I also serve as a Resident...
https://critsocjustice.wordpress.com/2014/03/04/a-beginners-guide-to-privilege/
https://dev.my.umbc.edu/api/v0/pixel/news/48366/guest@my.umbc.edu/c328d00bd2a139b7118f6e100e439a56/api/pixel
uncategorized
Women's, Gender, & Equity Center
https://dev.my.umbc.edu/groups/womenscenter
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xsmall.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/original.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xxlarge.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xlarge.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/large.png?1750974263
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/medium.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/small.png?1750974263
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xsmall.png?1750974263
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xxsmall.png?1750974263
Women's Center
0
0
false
Tue, 04 Mar 2014 05:20:15 -0500
Tue, 04 Mar 2014 05:20:15 -0500
Talk: From Terabyte-Sized Stem Cell Images to Knowledge, 10am Mon 3/10

From Terabyte-Sized Stem Cell Images to Knowledge
Peter Bajcsy, PhD
Information technology Laboratory
National Institute of Standards and Technology
10:00am Monday, 10 March 2014, ITE 346, UMBC
This talk will present the computational challenges and approaches to knowledge discovery from terabyte-sized images. The motivation comes from experimental systems for imaging and analyzing human pluripotent stem cell cultures at the spatial and temporal coverage of colonies that lead to terabyte-sized image data. The objective of such an unprecedented cell study is to characterize pluripotency of stem cell colonies over time at high statistical significance in order to understand the stem cell culture quality parameters and guide a repeatable growth of high quality stem cell colonies. The terabyte- sized images represented a stem cell line that was engineered to produce green fluorescent protein (GFP) under the influence of Oct4 promoter and then imaged in a mosaic of contiguous frames covering approximately 180 square millimeters, over five days under both phase contrast and GFP channels.
We overview multiple computer and computational science problems related to correcting (flat-field, dark current and background), stitching, segmenting, tracking, re-projecting and then representing large images for interactive visualization and sampling in a web browser. We researched extensions to Amdahl’s law for Map-Reduce computations, established benchmarks for image processing on a Hadoop platform, and introduced cluster node utilization coefficients for modeling memory demanding computations running on a computer cluster/cloud. The theoretical aspects of algorithmic complexity and cluster utilization at terabyte scale are extended to the experimental aspects of efficient image representation and client-server workload distribution in the context of visualization interactivity and image sampling. We report such experimental results for the NIST extensions to the Deep Zoom paradigm. The presentation will conclude with illustrations of enabled stem cell discoveries and collaboration opportunities to create a reference resource not only for cell biologists but also for computer scientists focusing on terabyte scale image analyses.
Peter Bajcsy received his Ph.D. in Electrical and Computer Engineering in 1997 from the University of Illinois at Urbana-Champaign and a M.S. in Electrical and Computer Engineering in 1994 from the University of Pennsylvania. He worked for machine vision, government contracting, and research and educational institutions before joining the National Institute of Standards and Technology (NIST) in 2011. At NIST, he has been leading a project focusing on the application of computational science in biological metrology, and specifically stem cell characterization at very large scales. Peter’s area of research is large-scale image-based analyses and syntheses using mathematical, statistical and computational models while leveraging computer science fields such as image processing, machine learning, computer vision, and pattern recognition. He has co-authored more than more than 24 journal papers and eight books or book chapters, and close to 100 conference papers.
Host: Yelena Yesha (Sorry, you need javascript to view this email address. )
]]>
From Terabyte-Sized Stem Cell Images to Knowledge Peter Bajcsy, PhD Information technology Laboratory National Institute of Standards and Technology 10:00am Monday, 10 March 2014, ITE 346,...
http://www.csee.umbc.edu/2014/03/talk-from-terabyte-sized-stem-cell-images-to-knowledge-10am-mon-310/
https://dev.my.umbc.edu/api/v0/pixel/news/41996/guest@my.umbc.edu/6593206c5375cd5c72149d6639ca1ab9/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 21:46:58 -0500
Mon, 03 Mar 2014 21:46:58 -0500
Talk: From Terabyte-Sized Stem Cell Images to Knowledge, 10am Mon 3/10

From Terabyte-Sized Stem Cell Images to Knowledge
Peter Bajcsy, PhD
Information technology Laboratory
National Institute of Standards and Technology
10:00am Monday, 10 March 2014, ITE 346, UMBC
This talk will present the computational challenges and approaches to knowledge discovery from terabyte-sized images. The motivation comes from experimental systems for imaging and analyzing human pluripotent stem cell cultures at the spatial and temporal coverage of colonies that lead to terabyte-sized image data. The objective of such an unprecedented cell study is to characterize pluripotency of stem cell colonies over time at high statistical significance in order to understand the stem cell culture quality parameters and guide a repeatable growth of high quality stem cell colonies. The terabyte- sized images represented a stem cell line that was engineered to produce green fluorescent protein (GFP) under the influence of Oct4 promoter and then imaged in a mosaic of contiguous frames covering approximately 180 square millimeters, over five days under both phase contrast and GFP channels.
We overview multiple computer and computational science problems related to correcting (flat-field, dark current and background), stitching, segmenting, tracking, re-projecting and then representing large images for interactive visualization and sampling in a web browser. We researched extensions to Amdahl’s law for Map-Reduce computations, established benchmarks for image processing on a Hadoop platform, and introduced cluster node utilization coefficients for modeling memory demanding computations running on a computer cluster/cloud. The theoretical aspects of algorithmic complexity and cluster utilization at terabyte scale are extended to the experimental aspects of efficient image representation and client-server workload distribution in the context of visualization interactivity and image sampling. We report such experimental results for the NIST extensions to the Deep Zoom paradigm. The presentation will conclude with illustrations of enabled stem cell discoveries and collaboration opportunities to create a reference resource not only for cell biologists but also for computer scientists focusing on terabyte scale image analyses.
Peter Bajcsy received his Ph.D. in Electrical and Computer Engineering in 1997 from the University of Illinois at Urbana-Champaign and a M.S. in Electrical and Computer Engineering in 1994 from the University of Pennsylvania. He worked for machine vision, government contracting, and research and educational institutions before joining the National Institute of Standards and Technology (NIST) in 2011. At NIST, he has been leading a project focusing on the application of computational science in biological metrology, and specifically stem cell characterization at very large scales. Peter’s area of research is large-scale image-based analyses and syntheses using mathematical, statistical and computational models while leveraging computer science fields such as image processing, machine learning, computer vision, and pattern recognition. He has co-authored more than more than 24 journal papers and eight books or book chapters, and close to 100 conference papers.
Host: Yelena Yesha (Sorry, you need javascript to view this email address. )
]]>
From Terabyte-Sized Stem Cell Images to Knowledge Peter Bajcsy, PhD Information technology Laboratory National Institute of Standards and Technology 10:00am Monday, 10 March 2014, ITE 346,...
http://www.csee.umbc.edu/2014/03/talk-from-terabyte-sized-stem-cell-images-to-knowledge-10am-mon-310/?utm_source=rss&utm_medium=rss&utm_campaign=talk-from-terabyte-sized-stem-cell-images-to-knowledge-10am-mon-310
https://dev.my.umbc.edu/api/v0/pixel/news/42618/guest@my.umbc.edu/378c08460b7437155e3928b20d08b512/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 21:46:58 -0500
Mon, 03 Mar 2014 21:46:58 -0500
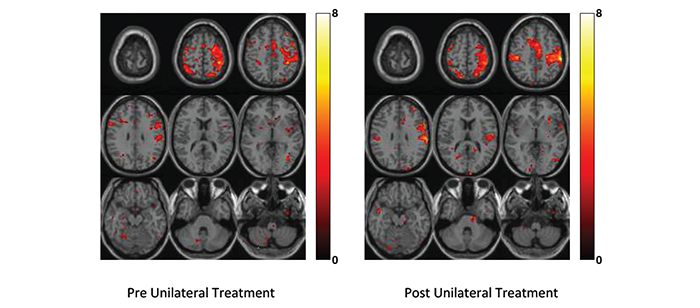
Professors Adali and Westlake receive grant to improve treatment for stroke victims
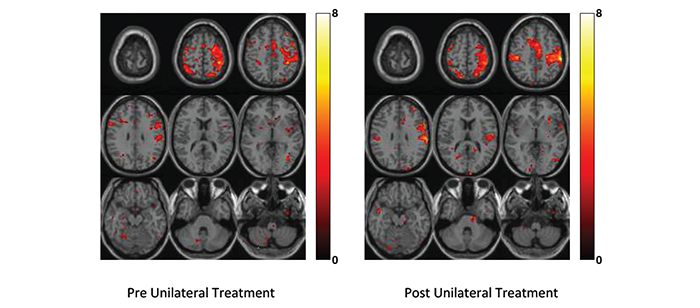
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed Grant Program for a project that ultimately will improve the recovery of stroke victims. The new joint UMBC-UMB Seed Grant Program pairs primary investigators from UMBC and the University of Maryland, Baltimore to conduct research as a team. Successful partners are offered research funding of up to $75,000 over twelve months to pursue their collaboration.
Nearly 800,000 U.S. citizens have a stroke each year, making it the leading cause of long-term disability. Treatment for stroke victims is mainly targeted towards residual functional deficits, especially regaining hand functions. Their project (“Independent Vector Analysis to Investigate Cognitive Neural Networks after Stroke: A Comparison between Two Rehabilitation Interventions”) will have a direct impact on stroke rehabilitation through objective evaluation of the two main treatment paradigms currently in use: unimanual (involving one hand) and bimanual (involving both hands) training. The evaluation will use the new class of medical image analysis techniques, independent vector analysis (IVA) algorithms, developed by Dr. Adali and her research group. The new class of IVA algorithms successfully captures subject variability and perform significantly better than the approaches traditionally used for the problem.
The initial results of the project demonstrate the advantages using IVA for the problem and will be presented this month at the 48th Annual Conference on Information Sciences and Systems in Princeton, NJ. The PIs are preparing two journal submissions, one based on the methods developed for the task and a second one emphasizing clinical significance of the results. These results will also provide the preliminary data for the proposal that Professors Adali and Westlake plan to submit to the NIH later this year.
]]>
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed...
http://www.csee.umbc.edu/2014/03/professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims/
https://dev.my.umbc.edu/api/v0/pixel/news/41982/guest@my.umbc.edu/d7a850947a7fbd58dd2708b3734ccfad/api/pixel
faculty-and-staff
news
research
research-awards
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 12:56:02 -0500
Mon, 03 Mar 2014 12:56:02 -0500
Professors Adali and Westlake receive grant to improve treatment for stroke victims
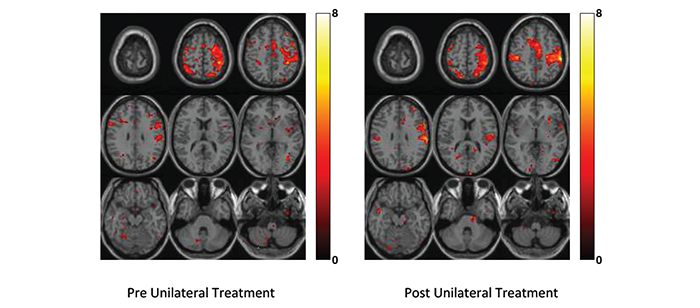
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed Grant Program for a project that ultimately will improve the recovery of stroke victims. The new joint UMBC-UMB Seed Grant Program pairs primary investigators from UMBC and the University of Maryland, Baltimore to conduct research as a team. Successful partners are offered research funding of up to $75,000 over twelve months to pursue their collaboration.
Nearly 800,000 U.S. citizens have a stroke each year, making it the leading cause of long-term disability. Treatment for stroke victims is mainly targeted towards residual functional deficits, especially regaining hand functions. Their project (“Independent Vector Analysis to Investigate Cognitive Neural Networks after Stroke: A Comparison between Two Rehabilitation Interventions”) will have a direct impact on stroke rehabilitation through objective evaluation of the two main treatment paradigms currently in use: unimanual (involving one hand) and bimanual (involving both hands) training. The evaluation will use the new class of medical image analysis techniques, independent vector analysis (IVA) algorithms, developed by Dr. Adali and her research group. The new class of IVA algorithms successfully captures subject variability and perform significantly better than the approaches traditionally used for the problem.
The initial results of the project demonstrate the advantages using IVA for the problem and will be presented this month at the 48th Annual Conference on Information Sciences and Systems in Princeton, NJ. The PIs are preparing two journal submissions, one based on the methods developed for the task and a second one emphasizing clinical significance of the results. These results will also provide the preliminary data for the proposal that Professors Adali and Westlake plan to submit to the NIH later this year.
]]>
CSEE Professor Tülay Adali and Professor Kelly Westlake from the University of Maryland School of Medicine received an award from the joint UMBC-UMB Research and Innovation Partnership Seed...
http://www.csee.umbc.edu/2014/03/professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims/?utm_source=rss&utm_medium=rss&utm_campaign=professors-adali-and-westlake-receive-grant-to-improve-treatment-for-stroke-victims
https://dev.my.umbc.edu/api/v0/pixel/news/42619/guest@my.umbc.edu/14c837573ac6d2cec7960704cd65db6d/api/pixel
faculty-and-staff
news
research
research-awards
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Mon, 03 Mar 2014 12:56:02 -0500
URA Applications due TUESDAY, MARCH 4 due to campus closure
Because of the campus closure on Monday, the URA application
deadline has been extended to TUESDAY, March 4 at 5 p.m. This
is a final deadline. All materials, including mentor support
materials, must be received by that time. URA applications should be
delivered in hard copy, no staples, to Sherman Hall 114.
Proposal reminders:
- Advice on a strong proposal
http://www.umbc.edu/undergrad_ed/research/URA/documents/successfulURAproposals10_Evergreen.doc
- Your proposal content must be on the form provided on the URA
web site. The two page narrative must be only two pages long.
Longer proposals are not accepted.
- Print the cover sheet, proposal, and your transcript all
SINGLE SIDED and deliver with NO STAPLES.
- You and your mentor should both sign the cover page of the
proposal. IF your mentor is not available to sign in person on
Tuesday, AND has read and approved your final proposal copy, the
mentor signature can be skipped. Just let me know of the
situation.
- Mentor materials include a letter from your mentor and the
very short form linked from the URA forms page. Mentor materials
may be submitted by e-mail. Student materials must be delivered
in hard copy.
- Deliver on Tuesday between 8:30 a.m. and 5 p.m. to Sherman
Hall Suite 114.
If you have already submitted a completed application, you may take
advantage of this time to make revisions if you feel any need to.
Just bring in the revised text on Tuesday and exchange it for text
you already delivered.
If you have any questions or concerns about the application process,
reply to this message. (Replying should now be safe. I have made the
list address bcc, so no replies should go to the list. Do LOOK at
the TO field of your reply message to be sure.)
Stay warm and safe!
Best regards,
Janet McGlynn
mcglynn@umbc.edu
]]>
Because of the campus closure on Monday, the URA application deadline has been extended to TUESDAY, March 4 at 5 p.m. This is a final deadline. All materials, including mentor support...
http://www.umbc.edu/undergrad_ed/research/URA/index.html
https://dev.my.umbc.edu/api/v0/pixel/news/41963/guest@my.umbc.edu/4f01e69715b5d6425ba877ccd8789f3c/api/pixel
Undergraduate Research
https://dev.my.umbc.edu/groups/undergradresearch
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/xsmall.png?1600355057
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/original.jpg?1600355057
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/xxlarge.png?1600355057
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/xlarge.png?1600355057
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/large.png?1600355057
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/medium.png?1600355057
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/small.png?1600355057
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/xsmall.png?1600355057
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/006/875606ced2b629148af4caa1a4e8dd3c/xxsmall.png?1600355057
Undergraduate Research
3
0
true
Sun, 02 Mar 2014 22:01:33 -0500
1st International Engineering Security and Project Coming Up
ISSA, IEEE, and PMI all at One Conference
From the Baltimore Chapter of ISSA:
There is a unique and exciting training opportunity occurring in our
area. The First International Engineering Security and Project (iESP)
Professionals Conference will be held at the University of Maryland on May 1.
It is the first joint venture between
Information System Security Association (ISSA), Institute of Electrical
and Electronic Engineers (IEEE) and Project Management Institute (PMI)
. Each organization will be providing a track of renowned specialists
in their field of expertise as well as a keynote
speaker The costs is only $150 for members or $200 for non-members.
You will receive full day of training plus breakfast and lunch. There
will be speakers from the fields of security, engineering, and project
management including Interpol, Department of
Treasury, and NASA. Attendees will not only have the opportunity to
choose from wide range of presentation topics, but will also have the
chance to network with career-oriented professionals in all three
fields. For more information and to register, check
out the web site.http://www.iespconference.org/
The treasurer of Baltimore ISSA says that students would pay the lower price.
]]>
From the Baltimore Chapter of ISSA: There is a unique and exciting training opportunity occurring in our area. The First International Engineering Security and Project (iESP) Professionals...
https://dev.my.umbc.edu/api/v0/pixel/news/41959/guest@my.umbc.edu/3d8ec4e914584d8b45254762d946feb6/api/pixel
ieee
issa
pmi
Information Systems Security Association, UMBC Chapter
https://dev.my.umbc.edu/groups/issa
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
1
0
true
Sun, 02 Mar 2014 19:49:24 -0500
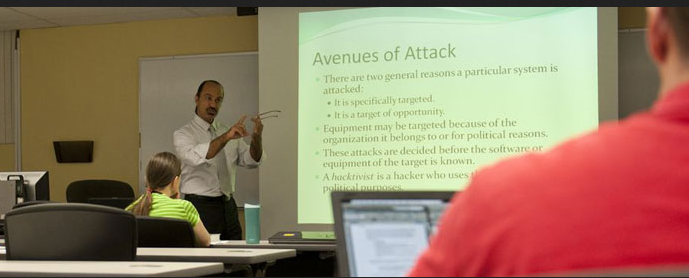
talk: Predictive Analytics for Insider Threats, 4pm Wed 3/5
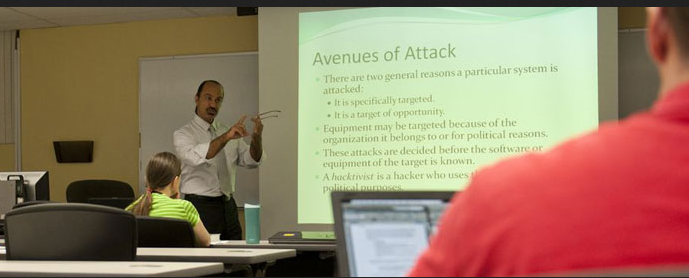
Predictive Analytics for Insider Threats
Ben Shariati
Visiting Lecturer & Interim Assistant CYBR GPD
4:00pm Wednesday, 5 March 2014, ITE325b
This talk will discuss how using operational cyber analytics for predictive security intelligence support a powerful defensive cybersecurity capability. Specifically, I will share elements of my commercial research on how organizations can predict malicious behavior (both user and digital) on their networks by incorporating tailored algorithms and artificial intelligence capabilities as part of an overall cybersecurity sensor architecture. Additionally, this talk will briefly discuss the impact that mobile devices have on the insider threat vulnerability within the government and private sector.
Ben Shariati is a Ph.D. candidate in Information Assurance/Cybersecurity at the George Washington University, where his dissertation work examines the analysis and management of cybersecurity concerns of critical infrastructures. His research and professional interests include mobile device security, emerging technology evaluation, risk analysis, audit, and compliance. For AY13-14, Mr. Shariati is a visiting lecturer and Interim Assistant Director of the Graduate Cybersecurity Program overseeing program activities at The Universities at Shady Grove. In addition to teaching several courses at UMBC, Mr. Shariati has taught graduate cybersecurity courses at George Washington University and undergraduate technical certification classes Hagerstown Community College.
Mr. Shariati is a technology and business executive with over 20 years of experience specializing in strategic and operational cybersecurity program activities and development for international organizations. His career highlights include serving as a lead enterprise security architect at the Federal Reserve Bank in Richmond, VA, a cybersecurity advisor at Cell Trust Corporation, and Technology Advisor/Cybersecurity Architect for the United Nations Pan American Health Organization.
]]>
Predictive Analytics for Insider Threats Ben Shariati Visiting Lecturer & Interim Assistant CYBR GPD 4:00pm Wednesday, 5 March 2014, ITE325b This talk will discuss how using operational...
http://www.csee.umbc.edu/2014/03/talk-predictive-analytics-for-insider-threats/
https://dev.my.umbc.edu/api/v0/pixel/news/41960/guest@my.umbc.edu/bbd49e0ac74987523077d3af39379525/api/pixel
csee
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 02 Mar 2014 19:46:31 -0500
Sun, 02 Mar 2014 19:46:31 -0500
talk: Predictive Analytics for Insider Threats, 4pm Wed 3/5
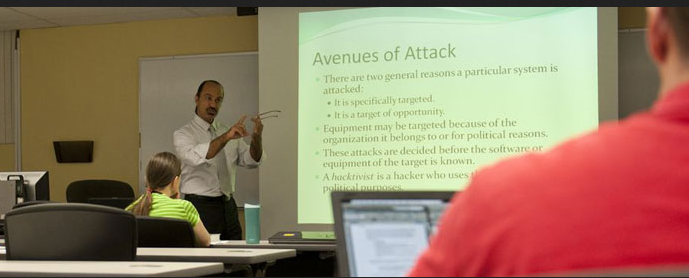
Predictive Analytics for Insider Threats
Ben Shariati
Visiting Lecturer & Interim Assistant CYBR GPD
4:00pm Wednesday, 5 March 2014, ITE325b
This talk will discuss how using operational cyber analytics for predictive security intelligence support a powerful defensive cybersecurity capability. Specifically, I will share elements of my commercial research on how organizations can predict malicious behavior (both user and digital) on their networks by incorporating tailored algorithms and artificial intelligence capabilities as part of an overall cybersecurity sensor architecture. Additionally, this talk will briefly discuss the impact that mobile devices have on the insider threat vulnerability within the government and private sector.
Ben Shariati is a Ph.D. candidate in Information Assurance/Cybersecurity at the George Washington University, where his dissertation work examines the analysis and management of cybersecurity concerns of critical infrastructures. His research and professional interests include mobile device security, emerging technology evaluation, risk analysis, audit, and compliance. For AY13-14, Mr. Shariati is a visiting lecturer and Interim Assistant Director of the Graduate Cybersecurity Program overseeing program activities at The Universities at Shady Grove. In addition to teaching several courses at UMBC, Mr. Shariati has taught graduate cybersecurity courses at George Washington University and undergraduate technical certification classes Hagerstown Community College.
Mr. Shariati is a technology and business executive with over 20 years of experience specializing in strategic and operational cybersecurity program activities and development for international organizations. His career highlights include serving as a lead enterprise security architect at the Federal Reserve Bank in Richmond, VA, a cybersecurity advisor at Cell Trust Corporation, and Technology Advisor/Cybersecurity Architect for the United Nations Pan American Health Organization.
]]>
Predictive Analytics for Insider Threats Ben Shariati Visiting Lecturer & Interim Assistant CYBR GPD 4:00pm Wednesday, 5 March 2014, ITE325b This talk will discuss how using operational...
http://www.csee.umbc.edu/2014/03/talk-predictive-analytics-for-insider-threats/?utm_source=rss&utm_medium=rss&utm_campaign=talk-predictive-analytics-for-insider-threats
https://dev.my.umbc.edu/api/v0/pixel/news/42620/guest@my.umbc.edu/04b3dcbde13cb738b1decfe32bc76ab4/api/pixel
csee
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Sun, 02 Mar 2014 19:46:31 -0500
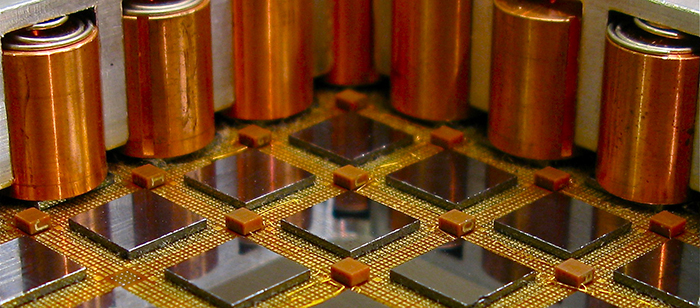
Samuel Lomonaco: Strange World of Quantum Computing, NASA Mon. 3/10
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the Building 3 Auditorium.
Abstract: Quantum computers have the potential to greatly increase computational power beyond the capabilities of conventional computers by exploiting the bizarre quantum properties of the subatomic world. This talk will give an introductory overview of quantum computing in an intuitive and conceptual fashion. No prior knowledge of quantum mechanics will be assumed.
]]>
CSEE Professor Samuel Lomonaco will give an invited talk on “The Strange World of Quantum Computing” as art of the NASA Goddard Engineering Colloquium Series at 3:00pm Monday, March 10 in the...
http://www.csee.umbc.edu/2014/03/samuel-lomonaco-strange-world-of-quantum-computing-nasa-mon-310/
https://dev.my.umbc.edu/api/v0/pixel/news/41956/guest@my.umbc.edu/f07bef95672ee9cc8bad65bd43a229db/api/pixel
computer-science
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Sun, 02 Mar 2014 14:11:12 -0500