Talk: Securing Distributed Networks with Reinforcement Learning & Game Theory
10-11am Thursday, Jan. 30, 2025; ITE459 and online
Securing Distributed Networks: Leveraging Reinforcement Learning and Game Theory for Attack Detection and Mitigation
10-11am January 30, 2025; ITE 459, UMBC and online
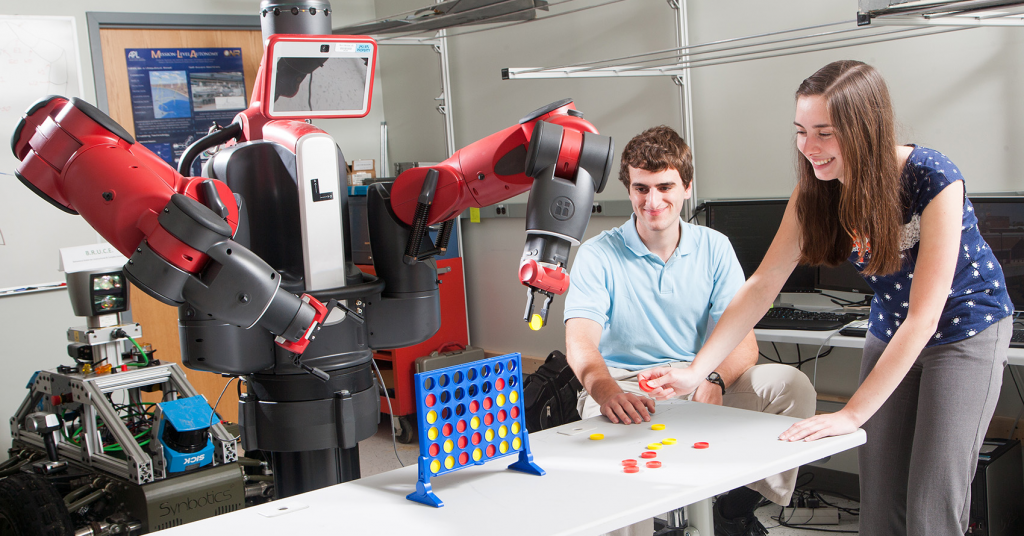
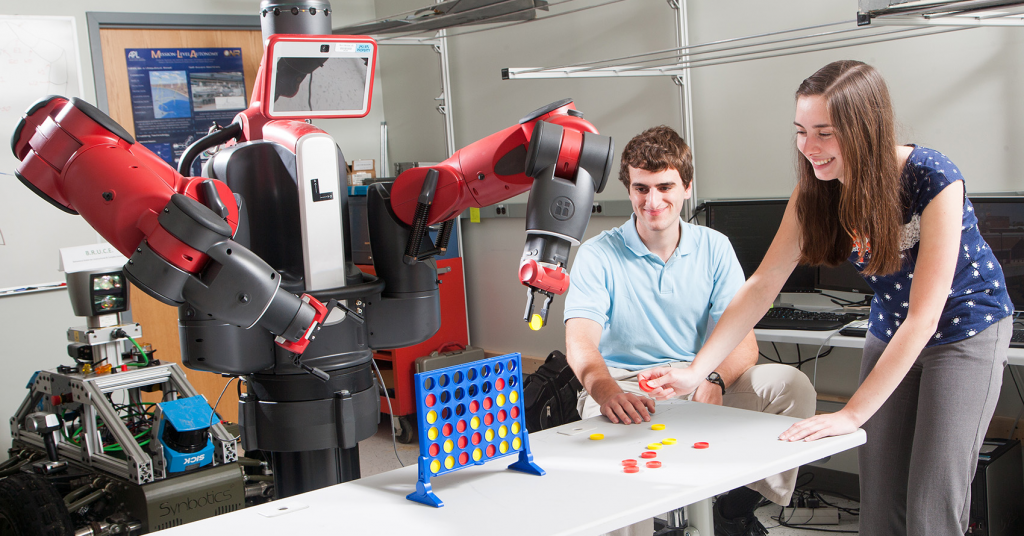
Reinforcement learning (RL) has demonstrated remarkable success across diverse domains, from mastering complex games to optimizing real-time feedback systems in robotics and industrial control. However, its potential in cybersecurity, particularly for autonomous attack detection and mitigation in distributed systems, remains largely underexplored. Traditional single-agent RL approaches struggle in decentralized environments where multiple entities make independent decisions, necessitating multi-agent reinforcement learning (MARL). Our research explores blockchain networks as an ideal test case due to their decentralized architecture and trustless consensus mechanisms. We developed a novel MARL-based consensus mechanism for Proof-of-Stake blockchains, enabling nodes to collaboratively identify and penalize malicious behavior while preserving decentralization. This approach effectively mitigated six major blockchain attack types with minimal computational overhead. Building on these results, we propose integrating game-theoretic principles into the MARL framework to model adversarial strategies and enhance system resilience. The synergy between reinforcement learning and game theory establishes a robust foundation for dynamic and adaptive security in distributed systems, effectively addressing current vulnerabilities while anticipating and countering future threats. This integrated approach enables the design of resilient, scalable defense mechanisms tailored to the complex dynamics of decentralized architectures.
Dr. Md Tariqul Islam is an Assistant Professor of Trustworthy Cyberspace in the School of Information Studies (iSchool) at Syracuse University. His research focuses on advancing the security, efficiency, and fault tolerance of networks and distributed systems, particularly in the domains of cloud and blockchain technologies. To this end, he designs and develops novel algorithms, protocols, and frameworks that enhance system reliability and security. In his doctoral dissertation, "Algorithms for Achieving Fault-Tolerance and Ensuring Security in Cloud Computing Systems," he developed dynamic scheduling algorithms for cloud computing that optimize resource usage and reduce the risk of system failures. He also devised several cloud storage schemes to protect data confidentiality, integrity, and availability while mitigating potential security vulnerabilities. Expanding his work to blockchain, his current research seeks to strengthen the security of the Proof-of-Stake (PoS) consensus mechanism by using multi-agent reinforcement learning (MRL) to detect malicious nodes in blockchain network and integrating Game Theory and Zero-Shot Learning (ZSL) to ensure consensus integrity. His long-term vision is to build resilient distributed networks that prioritize security, trust, and scalability and support the evolving demands of next-generation decentralized applications. Dr. Islam earned his bachelor’s degree in Computer Science and Engineering from the University of Dhaka, Bangladesh (2008), and both a master’s (2016) and Ph.D. (2020) in Computer Science from the University of Kentucky.
]]>
Securing Distributed Networks: Leveraging Reinforcement Learning and Game Theory for Attack Detection and Mitigation Dr. Md Tariqul Islam, Syracuse University 10-11am January 30, 2025; ITE 459,...
https://informationsystems.umbc.edu/home/calendar/events/
https://dev.my.umbc.edu/api/v0/pixel/news/146655/guest@my.umbc.edu/1662b1eba791abbe21e897be7fc2f7e4/api/pixel
ai
cybersecurity
machine-learning
reinfircement-learning
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Cybersecurity Institute Group
0
0
true
Wed, 22 Jan 2025 10:20:34 -0500
Sat, 08 Mar 2025 15:52:14 -0500
CodeBot'25 Workshop: Can We Trust AI-Generated Code?
Workshop Feb. 25-26, 2025 in Columbia, MD and online
Can We Trust AI-Generated Code?
Workshop sponsored by UMBC & Army Research Laboratory
Feb. 25-26, 2025 UMBC Training Centers, Columbia, MD & online
position paper deadline extended to 1/20/2025
The era of generative AI is upon us, and chatbots such as chatGPT are being used by programmers at all levels of experience to produce code. Some generative AI systems, such as
Gemini Code Assist, specialize in code generation. Unfortunately, AI-generated code often contains errors in the form of functionality that fails to meet specifications or vulnerabilities that can be exploited by hackers. People have been working on program verification and secure coding for sixty years, but even so, the skill needed to find such errors is possessed by only a fraction of software engineers, and these skills are not being passed on to student programmers as they should be.
The goal of this FREE workshop is to gather and produce actionable ideas and suggestions that may be of use to the IT profession. The workshop will consist of invited speakers, panels, and open discussion.
We invite would-be participants to submit short position papers offering comments, observations, experiences, and suggestions that pertain to any or all of the following workshop themes:- What is or could be done to make AI-generated code more trustworthy, from the perspective of functionality and/or cybersecurity?
- How can we do better at instilling the ideas and tools of secure development into the software profession?
- Being able to produce quality code, with or without the aid of AI, seems to be related to system skills in general. How can we do better at giving students these skills before (or as) they enter the workplace?
Position papers should limited to three pages and submitted according to this
template. Submit your position paper via email to
codebot25@umbc.edu after
registering for the workshop.
The organizing committee will select several papers for live presentation at the workshop. Selection will be based on relevance to the workshop themes, technical merit, and perceived interest to the audience. Position papers that are mere marketing pieces will not be considered, but descriptions of hardware and software solutions tying into the themes described above are welcome. Limited travel support may be available for non-local speakers. Position papers and summaries of the discussions that follow will make up the core of the workshop report.
UMBC students, both graduate or undergraduate, are welcome to submit position papers that describe their own personal experience and observations with AI-generated code in their own words. Students may include their resumes with position papers if they wish to have their work/resume circulated to other attendees. Domestic and international students are welcome to participate in this workshop.
Important Dates:
Position paper submission deadline: January 20, 2025
Notice of acceptance: January 31, 2025
Registration deadline: February 18, 2025
(no registration fee, but space is limited)
Workshop dates: February 25-26, 2025
The workshop will take place at
UMBC Training Centers, 6996 Columbia Gateway Dr #100, Columbia, MD 21046
REGISTER @
https://forms.gle/CipmPbbBVBLfHc728In-person space is limited, so register early! Based on RSVPs received, the organizing committee reserves the right to be selective in whom it selects to join the in-person meeting.
Instructions for virtual participation will be made available prior to the workshop.
Organizing Committee:
Prajna Bhandary, UMBC
Mike De Lucia, Army Research Laboratory
Richard Forno, UMBC
Lindsay Gaughan, UMBC Training Centers
Cynthia Matuszek, UMBC
Charles Nicholas, UMBC
Steve Simske, Colorado State University
Larry Wagoner, Dept. of Defense
Linda Kidder Yarlott, UMBC
Paul Yu, Army Research Laboratory
]]>
Can We Trust AI-Generated Code? Workshop sponsored by UMBC & Army Research Laboratory Feb. 25-26, 2025 UMBC Training Centers, Columbia, MD & online position paper deadline extended...
https://dev.my.umbc.edu/api/v0/pixel/news/146467/guest@my.umbc.edu/3963cf670aae6c0ef88607f359dd9477/api/pixel
ai
assistant
codebot
coding
genai
llm
workshop
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Cybersecurity Institute
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/xxlarge.jpg?1736288331
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/xlarge.jpg?1736288331
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/large.jpg?1736288331
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/medium.jpg?1736288331
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/small.jpg?1736288331
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/xsmall.jpg?1736288331
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/467/e786a1f9c39521096c70fd762406108e/xxsmall.jpg?1736288331
0
0
true
Tue, 07 Jan 2025 17:22:27 -0500
CodeBot '25: Can We Trust AI-Generated Code? 2/25-26
Workshop Feb. 25-26, 2025 in Columbia, MD and online
Can We Trust AI-Generated Code?
Workshop sponsored by UMBC & Army Research Laboratory
Feb. 25-26, 2025 UMBC Training Centers, Columbia, MD & online
The era of generative AI is upon us, and chatbots such as chatGPT are being used by programmers at all levels of experience to produce code. Some generative AI systems, such as
Gemini Code Assist, specialize in code generation. Unfortunately, AI-generated code often contains errors in the form of functionality that fails to meet specifications or vulnerabilities that can be exploited by hackers. People have been working on program verification and secure coding for sixty years, but even so, the skill needed to find such errors is possessed by only a fraction of software engineers, and these skills are not being passed on to student programmers as they should be.
The goal of this FREE workshop is to gather and produce actionable ideas and suggestions that may be of use to the IT profession. The workshop will consist of invited speakers, panels, and open discussion.
We invite would-be participants to submit short position papers offering comments, observations, experiences, and suggestions that pertain to any or all of the following workshop themes:- What is or could be done to make AI-generated code more trustworthy, from the perspective of functionality and/or cybersecurity?
- How can we do better at instilling the ideas and tools of secure development into the software profession?
- Being able to produce quality code, with or without the aid of AI, seems to be related to system skills in general. How can we do better at giving students these skills before (or as) they enter the workplace?
Position papers should limited to three pages and submitted according to this
template. The organizing committee will select several papers for live presentation at the workshop. Selection will be based on relevance to the workshop themes, technical merit, and perceived interest to the audience. Position papers that are mere marketing pieces will not be considered, but descriptions of hardware and software solutions tying into the themes described above are welcome. Limited travel support may be available for non-local speakers. Position papers and summaries of the discussions that follow will make up the core of the workshop report.
UMBC students, both graduate or undergraduate, are welcome to submit position papers that describe their own personal experience and observations with AI-generated code in their own words. Students may include their resumes with position papers if they wish to have their work/resume circulated to other attendees. Domestic and international students are welcome to participate in this workshop.
Important Dates: Position paper submission deadline:
January 7, 2025 Notice of acceptance: January 31, 2025
Registration deadline: February 18, 2025
(no registration fee, but space is limited)
Workshop dates: February 25-26, 2025
The workshop will take place at
UMBC Training Centers, 6996 Columbia Gateway Dr #100, Columbia, MD 21046
REGISTER @
https://forms.gle/CipmPbbBVBLfHc728In-person space is limited, so register early! Based on RSVPs received, the organizing committee reserves the right to be selective in whom it selects to join the in-person meeting.
Instructions for virtual participation will be made available prior to the workshop.
Organizing Committee:
Prajna Bhandary, UMBC
Mike De Lucia, Army Research Laboratory
Richard Forno, UMBC
Lindsay Gaughan, UMBC Training Centers
Cynthia Matuszek, UMBC
Charles Nicholas, UMBC
Steve Simske, Colorado State University
Larry Wagoner, Dept. of Defense
Linda Kidder Yarlott, UMBC
Paul Yu, Army Research Laboratory
UMBC Cybersecurity Institute
]]>
Can We Trust AI-Generated Code? Workshop sponsored by UMBC & Army Research Laboratory Feb. 25-26, 2025 UMBC Training Centers, Columbia, MD & online The era of generative AI is upon us,...
https://dev.my.umbc.edu/api/v0/pixel/news/146246/guest@my.umbc.edu/d5167d07b6a032b83194a6f4a657be2e/api/pixel
ai
code
programming
trust
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC and Army Research Laboratory
0
0
true
Thu, 12 Dec 2024 13:16:07 -0500
Thu, 12 Dec 2024 13:18:11 -0500
AI Lunchbox: Security Risk in AI/ML, 12/12
12:00-1:00 pm EST, Thursday, December 12, 2024
In the AI Lunchbox session Security Risk in AI/ML, participants will learn about attacks on AI models and how to defend against them. Designed for a general audience, this presentation will teach participants how to incorporate AI security risk into their organizational strategy and AI development workflows. Randy Abernethy from RX-M, LLC will be a speaker. The session will be held online from 12 to 1 p.m. EST on December 12, 2024. Register here to receive a link to the event from the UMBC Training Centers Center for Applied AI.
UMBC Cybersecurity Institute
]]>
In the AI Lunchbox session Security Risk in AI/ML, participants will learn about attacks on AI models and how to defend against them. Designed for a general audience, this presentation will teach...
https://dev.my.umbc.edu/api/v0/pixel/news/146242/guest@my.umbc.edu/4dedc88a7fdb994c7c9d405ab1ebd828/api/pixel
ai
risk
security
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Cybersecurity Institute Group
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/xxlarge.jpg?1734019439
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/xlarge.jpg?1734019439
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/large.jpg?1734019439
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/medium.jpg?1734019439
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/small.jpg?1734019439
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/xsmall.jpg?1734019439
https://assets3-dev.my.umbc.edu/system/shared/thumbnails/news/000/146/242/cb605bcf2c880ac784cb1a694e5940e6/xxsmall.jpg?1734019439
0
0
true
Thu, 12 Dec 2024 11:05:19 -0500
Talk: Privacy-Preserving Data Sharing in Intrusion Detection Systems, 12/6 online
12–1pm EST Friday, December 6, 2024, online
UMBC Cyber Defense Lab presents
Privacy-Preserving Data Sharing in Intrusion Detection Systems
Zhiyuan Chen
Professor and Chair, UMBC Information Systems Department
12:00–1pm, Friday, December 6, 2024, online
Intrusion detection systems increasingly use machine learning methods, which require large volumes of data to be effective. Sharing such data sets will benefit the research community and industry. One obstacle to sharing such data is data privacy because network trace data or server log data often contains sensitive information, such as IP addresses. Even if IP addresses are encrypted, adversaries may still inject packets with unique patterns (e.g., with a certain packet sizes) such that they can use these packets to infer encrypted information. Another challenge arises when multiple intrusion detection systems from multiple organizations need to correlate their detected alerts to identify a larger threat, but the information they exchange may contain sensitive information such as network topology and traffic. This talk covers two approaches to address this problem. First, we propose a data anonymization approach that de-identifies network trace data. Compared to existing approaches, this approach provides stronger privacy protection and is robust to injection attacks. Second, we propose two privacy-preserving distributed alert correlation methods, one using additive secret sharing and the other using differential privacy. We also investigate tradeoffs between these two methods.
Dr. Zhiyuan Chen is a Professor in the Department of Information Systems at UMBC. He received a BS and a MS from Fudan University, China, and a PhD in Computer Science from Cornell University. His research covers the areas of data science, big data, privacy preserving data mining and data management, data exploration and navigation, and semantic-based search and data integration using semantic networks, adversarial learning and its applications in cybersecurity. He has published extensively in these areas and has received funding from NSF, Department of Energy, IBM, Office of Naval Research, MITRE, and Department of Education.
Host: Alan T. Sherman. Support for this event was provided in part by NSF under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public.
]]>
UMBC Cyber Defense Lab presents Privacy-Preserving Data Sharing in Intrusion Detection Systems Zhiyuan Chen Professor and Chair, UMBC Information Systems Department 12:00–1pm, Friday, December...
https://dev.my.umbc.edu/api/v0/pixel/news/145965/guest@my.umbc.edu/e0574ed2de8fc798b31101e61e796b54/api/pixel
ai
cybersecurity
privacy
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/xxlarge.jpg?1732912896
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/xlarge.jpg?1732912896
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/large.jpg?1732912896
https://assets2-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/medium.jpg?1732912896
https://assets4-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/small.jpg?1732912896
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/xsmall.jpg?1732912896
https://assets1-dev.my.umbc.edu/system/shared/thumbnails/news/000/145/965/b9e9567763877786d428f0d3f7731e97/xxsmall.jpg?1732912896
0
0
true
Fri, 29 Nov 2024 17:28:15 -0500
Interested in AI? Join free Discover AI program this Fall
Apply by Fri 9/3 for 8 week online program
AI systems and machine learning software are increasingly being used to address cybersecurity problems.
UMBC has partnered with AI4ALL to offer its free online Discover AI class introducing AI technology to selected UMBC undergraduate students from any major this Fall. The eight-week program starts in the third week of September, includes both synchronous and asynchronous instruction, and requires about 15-20 hours over the eight weeks. It is open to all freshmen, sophomores, and juniors and is structured to accommodate students with and without prior computer science or AI experience. Students finishing the program will get a certificate and the opportunity to apply for free follow-on programs.
AI4ALL programs are designed to bring together and highlight voices that have been historically excluded and that will lead and shape the future of AI. It aims to serve the following students, especially those at the intersection of two or more of these identities:
Indigenous Peoples, Black, Hispanic or Latinx, Pacific Islander, and Southeast Asian
Trans and non-binary; two-spirit; cis women and girls
Lesbian, gay, bisexual, asexual, and queer
Students with a demonstrated financial need (e.g., students receiving financial aid)
First-generation college student
JHU/APL CIRCUIT internship program information session
3:00-4:00 pm Friday, 31 January 2020
ITE 459, UMBC
There will be a special information session on the JHU/APL CIRCUIT internship program from 3:00 pm to 4:30 pm on Friday, 31 January 2020 in room ITE 459.
This session is for undergraduates who want to spend their summer (June through August) getting paid to do mentored research at the Johns Hopkins University Applied Physics Lab. The research areas include AI, data science, cybersecurity, precision medicine, and planetary exploration.
Interns selected for the program will do mission-oriented research on-site at JHU/APL in Laurel MD mentored by STEM professionals. There will also be year-round opportunities for engagement and enrichment. The selection for an internship will be based on a combination of potential, need and commitment.
Email *protected email* or *protected email* with questions.
The post JHU/APL CIRCUIT internship program information session, 3pm Fri 1/31 appeared first on Department of Computer Science and Electrical Engineering.
]]>
JHU/APL CIRCUIT internship program information session 3:00-4:00 pm Friday, 31 January 2020 ITE 459, UMBC There will be a special information session on the JHU/APL CIRCUIT...
https://www.csee.umbc.edu/2020/01/jhu-apl-circuit-internship-program-information-session-3pm-fri-1-31/
https://dev.my.umbc.edu/api/v0/pixel/news/89804/guest@my.umbc.edu/78328c3f0e19647545384211b4aa76f6/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
news
research
students
uncategorized
undergraduate
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
false
Wed, 22 Jan 2020 16:05:36 -0500
Wed, 01 Jan 2020 16:05:36 -0500
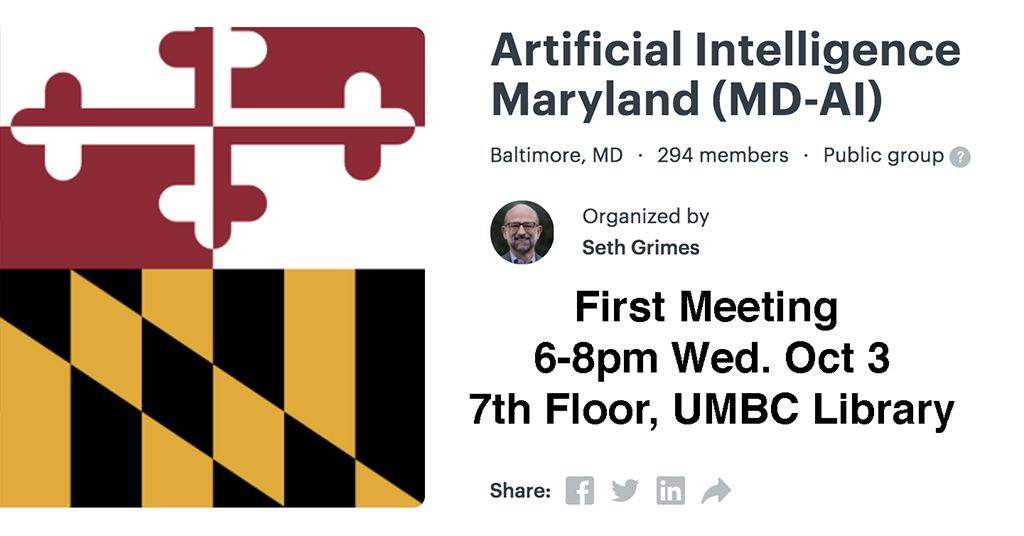
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library
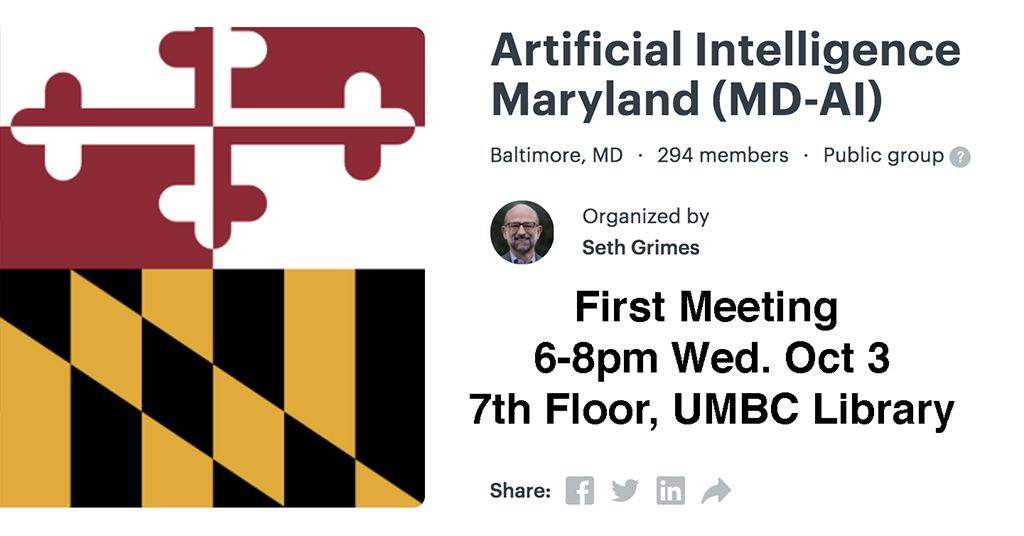
MD-AI Meetup holds 1st event at UMBC
6-8pm Wed 10/3, 7th floor library
A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will have its first meeting at UMBC this coming Wednesday (Oct 3) from 6:00-8:00pm in the 7th floor of the library. The first meeting will feature a talk by UMCP Professor Phil Resnik on the state of NLP and an AI research agenda. Refreshments will be provided. The meetup is organized by Seth Grimes and supported by TEDCO, local AI startup RedShred, and the Maryland Tech Council.
If you are interested in attending this and possibly future meetings (which will probably be monthly), go to the Meetup site and join (it’s free) and RSVP to attend this meeting (if there’s still room). If you join the meetup and RSVP, you can see who’s registered to attend.
These meetups are good opportunities to meet and network with people in the area who share interests. It’s a great opportunity for students who are will be looking for internships or jobs in the coming year.
The post MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library appeared first on Department of Computer Science and Electrical Engineering.
]]>
MD-AI Meetup holds 1st event at UMBC 6-8pm Wed 10/3, 7th floor library A new Maryland-based meetup interest group has been established for Artificial Intelligence (MD-AI Meetup) and will...
https://www.csee.umbc.edu/2018/09/md-ai-meetup-holds-1st-event-at-umbc-6-8pm-wed-10-3-7th-floor-library/
https://dev.my.umbc.edu/api/v0/pixel/news/78988/guest@my.umbc.edu/9f971bc6300fd641f11e4a00be96e2fb/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
events
nlp
robotics
talks
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Sat, 29 Sep 2018 23:50:53 -0400
Sat, 29 Sep 2018 23:50:53 -0400
Machine learning and AI for cybersecurity: a technical chat with DISA

The UMBC Cyber Defense Lab
Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency
James Curry
Lead Engineer–DoD Cyber Security Range
Defense Information Systems Agency (DISA)
12:00–1:00pm Friday, 28 September 2018, ITE 227, UMBC
A broad reaching brief on the scope and scale of the DISA Mission, followed by a dive into DISA’s efforts to develop Machine Learning and Artificial Intelligence to help defend the nation’s cyber infrastructure. Attendees are highly encouraged to ask questions.
James Curry is the Lead Engineer of the DoD Cyber Security Range (CSR). The CSR’s mission is to replicate the DoD Information Network (DODIN) environment at lab scale, while maintaining high-fidelity realism. As Lead Engineer, Mr. Curry led the design, acquisition, and implementation of two first-of-its-kind technologies: a Virtual Internet Access Point (vIAP) and a Virtual Joint Regional Security Stack (vJRSS). These technologies enable the DoD Workforce to train in an IaaS-on-demand environment that realistically matches DISA’s core infrastructure. Mr. Curry is a Scholarship for Service (SFS) recipient (2008-2009) and received his masters and bachelors of science in computer science from New Mexico Tech. Email: *protected email*
Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public. Upcoming meetings for Fall 2018 include the following.
- Oct 12 Enis Golaszewski, The 2018 UMBC SFS study
- Oct 26 Enis Golaszewski, Using tools in the formal analysis of cryptographic protocols
- Nov 9 Razvan Mintesu, Legal aspects privacy
- Dec 7 Tim Finin, A knowledge graph for cyber threat intelligence
The post Machine learning and AI for cybersecurity: a technical chat with DISA appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab Machine Learning and Artificial Intelligence: A Technical Chat with the Defense Information Systems Agency James Curry Lead Engineer–DoD Cyber Security Range...
https://www.csee.umbc.edu/2018/09/machine-learning-and-ai-for-cybersecurity-a-technical-chat-with-disa/
https://dev.my.umbc.edu/api/v0/pixel/news/78945/guest@my.umbc.edu/1d7e79c959c784379822047cd7dd1737/api/pixel
ai
computer-engineering
computer-science
cybersecurity
data-science
machine-learning
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
0
0
true
Thu, 27 Sep 2018 12:49:08 -0400

The UMBC Cyber Defense Lab presents
Classifying Malware using Data Compression
Charles Nicholas, UMBC
12:00–1:00pm Friday, 20 April 2018, ITE 229
Comparing large binary objects can be tricky and expensive. We describe a method for comparing such strings, using ideas form data compression, that is both fast and effective. We present results from experiments applying this method, which we refer to as LZJD, to the areas of malware classification and digital forensics.
Charles Nicholas (*protected email*) earned his B.S. in Computer Science from the University of Michigan – Flint in 1979, and the M.S. and Ph.D. degrees in Computer Science from Ohio State University in 1982 and 1988, respectively. He joined the Computer Science Department at UMBC in 1988. His research interests include electronic document processing, intelligent information systems, and software engineering. In recent years he has focused on the problems of storing and retrieving information from large collections of documents. Intelligent software agents are an important aspect of this work. Host: Alan T. Sherman, *protected email*
The UMBC Cyber Defense Lab meets biweekly Fridays. All meetings are open to the public.
The post 🗣 talk: Classifying Malware using Data Compression, 12-1 Fri 4/20, ITE229 appeared first on Department of Computer Science and Electrical Engineering.
]]>
The UMBC Cyber Defense Lab presents Classifying Malware using Data Compression Charles Nicholas, UMBC 12:00–1:00pm Friday, 20 April 2018, ITE 229 Comparing large binary objects can be...
https://www.csee.umbc.edu/2018/04/talk-classifying-malware-using-data-compression-umbc-nicholas-cybersecurity/
https://dev.my.umbc.edu/api/v0/pixel/news/75698/guest@my.umbc.edu/af742b2d5bd0e690e50299c23c102811/api/pixel
ai
cybersecurity
data-science
machine-learning
news
talks
UMBC Cybersecurity Institute Group
https://dev.my.umbc.edu/groups/cybersecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/original.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxlarge.png?1734891477
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xlarge.png?1734891477
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/large.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/medium.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/small.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xsmall.png?1734891477
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/485/196da6a7ec6f4c31eab2e474c17a9ab7/xxsmall.png?1734891477
UMBC Center for Cybersecurity
1
0
true
Sun, 15 Apr 2018 18:08:07 -0400
Sun, 15 Apr 2018 18:08:07 -0400