Job Phishing Alert: Department of Biological Sciences
An Example of Red Flags In A Phishing Message
Recently, the Division of Information Technology(DoIT) received multiple reports of a job phishing email. The scammers sending these emails are impersonating Professor Mendelson of the Department of Biological Sciences. Below is an example of such an email. For privacy purposes, we removed the To field.
From: Majoro Diarra Stanley <majorodstanley@gmail.com> Date: Wed, Oct 27, 2021 at 6:07 PM Subject: REMOTE JOB OFFER To:
The services of a student administrative assistant is urgently required to work part-time in Mendelson Laboratory and get paid $300 weekly. Tasks will be carried out remotely and work time is 7 hours/week. If interested, send a copy of your updated resume and a functional whatsapp number to Mendelson Laboratory via this email address to proceed with the job description/responsibilities. Sincerely Tamra Mendelson Professor, Biological Sciences Department of Biological Sciences University of Maryland, Baltimore County Office: Biological Sciences 426 Lab: Mendelson Lab BS 402/427/428
|
Please note that the Biological Sciences Department or Professor Mendelson did not send this message. Three visible red flags in this email are:
The From address is not a UMBC email. If the Biological Sciences Department or Prof. Mendelson were sending this email, the From address would have been a UMBC email address. However, it was sent from <majorodstanley@gmail.com>, which is not a UMBC affiliate. Please note that it could have been spoofed, even if it appears to originate from a UMBC email. Therefore, always check with DoIT(security@umbc.edu) or email/contact the impersonated person on a completely different email when you see a conflict in the address.
Whatsapp number. A lot of scammers will ask for your WhatsApp number. If their number gets reported, they could easily create a new one. The same can be said for an email address; however, if their email is blocked, they will lose responses from other phishing email recipients. If you ever receive a job offer asking for a WhatsApp number or a phone number in general, BE SUSPICIOUS!
The email template. This template is very common. After a quick Google search, we found a few Job scams articles with the same template. So if you are ever in doubt, Google it! UMBC will not use a known phishing template to offer you a job opportunity.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, the Division of Information Technology(DoIT) received multiple reports of a job phishing email. The scammers sending these emails are impersonating Professor Mendelson of the Department...
https://dev.my.umbc.edu/api/v0/pixel/news/115555/guest@my.umbc.edu/79db6b5e7e5828bb7eda3580d6639140/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
1
0
true
Tue, 07 Dec 2021 14:53:07 -0500
Account data breach: Thingiverse
Another Breach Of An Online Service
In 2020, the 3D model sharing service Thingiverse suffered a data breach. On October 13, 2021, the data compromised in the breach was posted in various hacker forums. This breach contained data for approximately 228 thousand customers. The information included usernames, email addresses, names, passwords, IP addresses, and geographical addresses.
The compromised data was shared in an online hacking forum. Four UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a Thingiverse account, please contact them to see if you have been affected by this breach.
To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about Thingiverse data breach:
https://www.databreachtoday.com/thingiverse-data-leak-affects-25-million-subscribers-a-17729
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In 2020, the 3D model sharing service Thingiverse suffered a data breach. On October 13, 2021, the data compromised in the breach was posted in various hacker forums. This breach contained data...
https://dev.my.umbc.edu/api/v0/pixel/news/113398/guest@my.umbc.edu/c9fc8cf28cf8646c6eb6eeb9c24dcdde/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 18 Oct 2021 16:53:55 -0400
Tue, 19 Oct 2021 11:20:04 -0400
Commemorative Coin Spam
Spam Claiming Celebrity Endorsement For Trump Coin
The UMBC Department of Information Technology (DoIT) received a report of spam invoking former President Trump, collectible coins, and the security-focused Telegram messaging system. See the example below:
Excerpt:
Telegram just announced that TRUMP COIN will be added as their official payment method starting from 31th of January, 2022!
The skyrocket to 10.000$ will happen in the beginning of the next year!
They are running of of stock and here are the last few coins, almost 14 million coins were sold in the US these previous days.
We are honored that our President Trump’s face will be on the most powerful coin that will change the world.
The Trump Coin has been approved as the ONLY COIN that will change the HISTORY and all you need to do is to TRUST THE PLAN.
Get at least 25 coins for you and your family and be ready for new beginnings, claim them today because these are the last free stocks available!
Check availability and get yours here:
|
Account data breach: LinkedIn
In April 2021, an employment-oriented online service, LinkedIn, was targeted by attackers who scraped data from hundreds of millions of public profiles and later sold them online. Whilst the scraping did not constitute a data breach, nor did it access any personal data not intended to be publicly accessible, the data was still monetized and later broadly circulated in hacking circles. The information included education levels, email addresses, genders, geographic locations, job titles, names, social media profiles. No financial information was leaked.
2029 UMBC accounts were victims of this scrape. The victims are being notified via their UMBC emails and/or their alternate emails. If you have a LinkedIn account, we suggest changing your password there and anywhere else that you used the same password.
To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about LinkedIn data breach:
https://www.businessinsider.com.au/linkedin-data-scraped-500-million-users-for-sale-online-2021-4
https://news.linkedin.com/2021/june/an-update-from-linkedin
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this scraped was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Account data breach: LinkedIn In April 2021, an employment-oriented online service, LinkedIn, was targeted by attackers who scraped data from hundreds of millions of public profiles and later...
https://dev.my.umbc.edu/api/v0/pixel/news/113139/guest@my.umbc.edu/59b3d75390a08e7a3dab411a4eb26b79/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 11 Oct 2021 10:29:06 -0400
Phishing Alert: I need your quick response
Tip: This Isn't Dr. Hrabowski
The Division of Information Technology( DoIT) recently received reports about a phishing email impersonating Dr. Hrabowski. Below is an example of such an email. We removed the recipient’s information for privacy reasons.
From: President Freeman A. Hrabowski, III <msgrenaway7511@gmail.com> Date: Thu, Oct 7, 2021 at 3:04 PM Subject: I need your quick response To:
Hi <Your Name>, How’s your day going? Do you have time to chat now? If yes please send me your text phone number now.
Thanks.
President Freeman A. Hrabowski, III |
This email originated from <msgrenaway7511@gmail.com>, which is not Dr. Hrabrowski’s email nor a UMBC email. So even though we would all love to have a chat with Dr. Hrabrowski, this is too good to be true.
If you have received any message similar to the one listed above, DO NOT RESPOND. Instead, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
The Division of Information Technology( DoIT) recently received reports about a phishing email impersonating Dr. Hrabowski. Below is an example of such an email. We removed the recipient’s...
https://dev.my.umbc.edu/api/v0/pixel/news/113138/guest@my.umbc.edu/948628d2adb4bf893b8c7aa5e3230846/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 11 Oct 2021 10:26:08 -0400
Phishing Alert: You have (#) new pending incoming emails
A New Twist On Phishing
The Division of Information Technology (DoIT) recently received reports of a new form of phishing campaign. This campaign informs recipients that they have “# new pending incoming emails” where # represents some actual number. Below are examples of the different kinds of emails that we received. We removed the recipients’ information for privacy purposes.
From: Email Administrator <noreply-mailbox@umbc.edu> Date: Sat, Sep 11, 2021 at 7:52 AM Subject: You have (4) new pending incoming emails To: <CampusID@umbc.edu>
|
You have (4) new pending incoming emails |
| Your allowed Email Quota usage has been exceeded on your account. <CampusID>@umbc.edu
Please kindly verify your Human and not a robot by following the below link, so we can get your account running normal again. |
| Verify Email Account |
| If no action is taken, you may cease to receive incoming emails This Email was sent to <CampusID>@umbc.edu as a User from umbc.edu Mail Box Admin |
|
|
This example originated from <noreply-mailbox@umbc.edu>, which looks like a UMBC account; however, this account was spoofed. An outside person created this @umbc.edu email for phishing purposes.
Below is another similar email that is spoofed. It originated from <cpanel@umbc.edu>, which is also not a UMBC account.
From: Mail Delivery System <cpanel@umbc.edu> Date: Fri, Sep 10, 2021 at 9:09 AM Subject: Mail delivery failed: <CampusID>@umbc.edu have 6 Pending incoming messages. To: <CampusID@umbc.edu>
You have Incoming Pending Messages The following messages have been blocked by your mail-server due to validation error. You have six pending messages .
Note: The messages will be delivered within 1-2 hours after you receive a confirmation mail notice. This message was sent by the MailDaemon server umbc.edu notification.
Thank you! Copyright© 2021 Webmail, Inc.
|
The links in both of these emails will take you to separate domains https://sign-in-verification-929bb.web.app and https://firebasestorage.googleapis.com respectively. The links in these emails will ask you to sign in. By signing in, they will be able to steal your passwords.
Below is a copy of the https://sign-in-verification-929bb.web.appwebsite. The Firebase page has been removed.

If you have received this email, please DO NOT CLICK on the link. However, if you have clicked on the link, DO NOT ENTER your password. If you entered your UMBC password, immediatelyCHANGE YOUR PASSWORD.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
The Division of Information Technology (DoIT) recently received reports of a new form of phishing campaign. This campaign informs recipients that they have “# new pending incoming emails” where #...
https://dev.my.umbc.edu/api/v0/pixel/news/113136/guest@my.umbc.edu/7cd8f1d1c5a4c20269788f7508d32901/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 11 Oct 2021 10:21:59 -0400
Mon, 11 Oct 2021 13:24:53 -0400
Phishing Alert: "Received AWB Documents via WeTransfer"
A "File Transfer" Phishing Campaign
The Division of Information Technology( DOIT) recently received reports of a ‘file transfer’ phishing campaign. Below is an example of this phishing email. We removed the To field for privacy purposes.
To: <CampusID>@umbc.edu Date:21 Sep 2021 03:43:00 -0400 From:"Wetransfer" <offices@mekre-net.uno> Subject: <CampusID>@umbc.edu Received PO-20210921GL via WeTransfer
<CampusID>@umbc.edu You have received a PO-20210921GL files via Wetransfer | 1 files, 1.74 MB in total · Will be deleted on 22 Sept 2021 |
|
Download link https:/wetranster,com/ downloads/ 7fa32f92e5e6536721c0c454c64efb520180304192959/ 6c03cb9a8f23fd6c89dac4d8c16a09220180304193000/184ee46
1 file PO-20210921GL.pdf 1.74MB
|
|
To make sure our emails arrive, please add noreply@wetransfer.com to your contacts. sent by wetransfersupport.wetransfer.com About WeTransfer - Help - Legal - Report this transfer as spam
|
This example originated from <offices@mekre-net.uno>; however, there are several more senders:
If you receive a similar email, please forward it immediately to: security@umbc.edu along with the headers.
At first glance, the download link seems to originate from Wetransfer.com, however if you look closely, there is a comma between Wetransfer and com:
https:/wetranster,com/ downloads/ 7fa32f92e5e6536721c0c454c64efb520180304192959/ 6c03cb9a8f23fd6c89dac4d8c16a09220180304193000/184ee46 |
Another flaw in the link is that copying the link address will take you to a completely different domain, https://firebasestorage.googleapis.com. Below is the full link and its website.
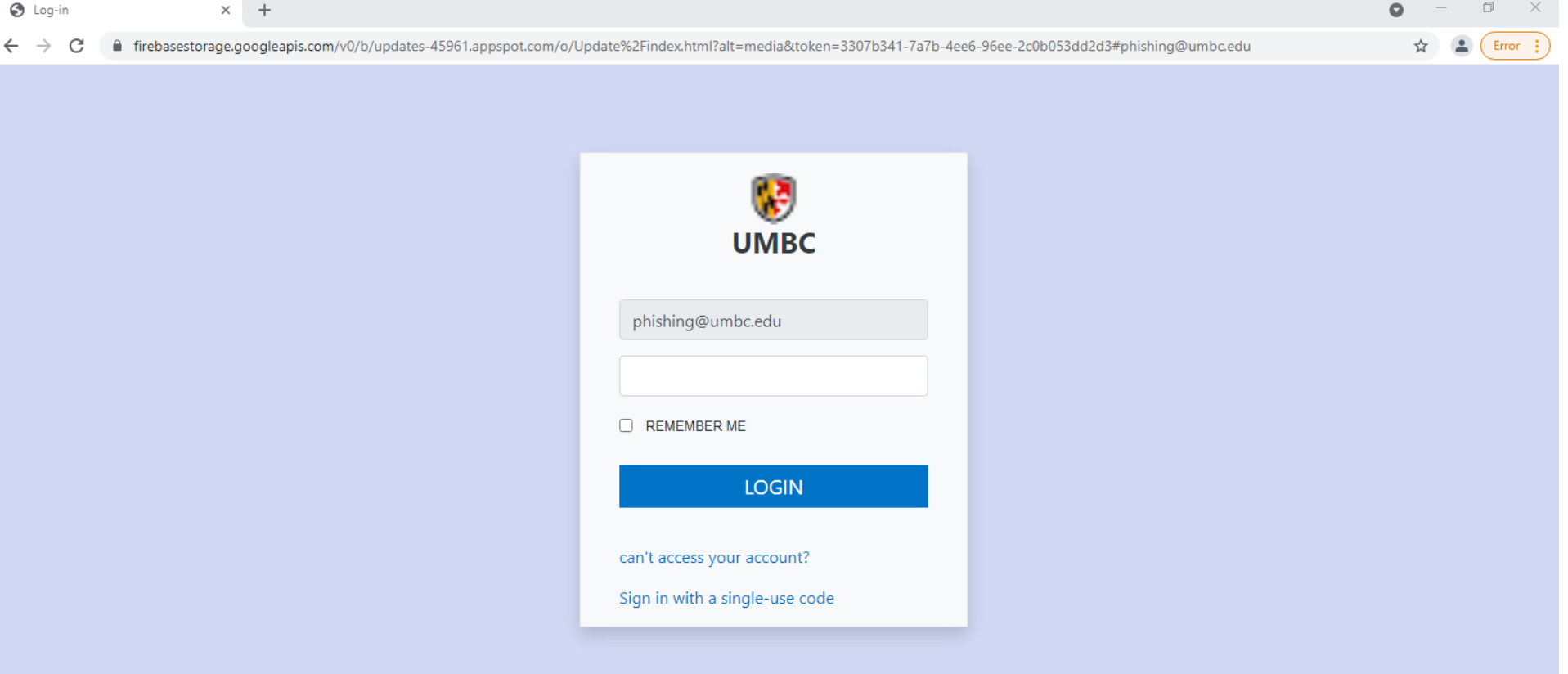
This format is similar to a previous phishing email. However, the background is different, and the link takes you directly to https://firebasestorage.googleapis.com and asks you to log in.
If you have received this email, please DO NOT CLICK on the link. However, if you have clicked on the link, DO NOT ENTER your password. If you entered your UMBC password, immediatelyCHANGE your password.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
The Division of Information Technology( DOIT) recently received reports of a ‘file transfer’ phishing campaign. Below is an example of this phishing email. We removed the To field for privacy...
https://dev.my.umbc.edu/api/v0/pixel/news/112745/guest@my.umbc.edu/96f5663d5d9e92c50b43e07071f4583b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Tue, 28 Sep 2021 19:19:04 -0400
Account data breach: Ajarn
Why You Should Not Use Your UMBC Password At Any Other Site
In September 2021, Thai-based English language teaching website, Ajarn, learnt that they suffered a data breach back in September 2018. This breach contained data for approximately 266 thousand Ajarn customers. The information included email addresses, names, genders, phone numbers, dates of birth, education levels, genders, geographic locations, job applications, marital statuses, nationalities, passwords, and profile photos. No financial information was leaked.
Two UMBC accounts were victims of this breach. The victims are being notified via their UMBC emails and/or their alternate emails. If you have an Ajarn account, please contact them to see if you have been affected by this breach.
To see if you were involved in any other breach, visit: https://haveibeenpwned.com/.
More about Ajarn data breach:
https://www.ajarn.com/data-breach
If you have any questions or concerns, email us at: security@umbc.edu.
Information about this breach was provided to us by Have I Been Pwned(HIBP).
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
In September 2021, Thai-based English language teaching website, Ajarn, learnt that they suffered a data breach back in September 2018. This breach contained data for approximately 266 thousand...
https://dev.my.umbc.edu/api/v0/pixel/news/112698/guest@my.umbc.edu/073a69a5101e6e970cae12c37302b55b/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 27 Sep 2021 17:34:02 -0400
Notice of a LEGITIMATE E-mail Survey!
"Your UMBC Feedback is Requested" Is A VALID Survey Request
Normally, these posts warn of various types of fraud and misdirection that try to mislead victims into giving up personal information and/or money. The Division of Information Technology (DoIT) encourages and appreciates vigilance and caution among members of the UMBC community.
That said, there are occasions when messages are sent out to account holders asking them to click on a link or fill in a form are legitimate. DoIT received a report about a message that appears to be a legitimate request to participate in a survey about intercultural development at UMBC. After investigation, we have established that the message is exactly that! If you receive such a message (see excerpt below), please feel free to respond. The survey is overseen by Dr. Irina Golubeva and Dr. Jasmine A. Lee of the Division of Students Affairs.
Good afternoon,
We are reaching out to you today as a part of a Hrabowski Innovation Fund (HIF) grant project. One overall goal of the project is to develop the intercultural communication skills of undergraduate and graduate students through intercultural dialogues on campus and to enhance their preparedness for working in a culturally diverse world. By completing this survey, you will assist us in this endeavor by sharing your perspectives on campus climate and sharing your insights on where you engage in intercultural development at UMBC. This survey should take about 15 minutes to complete. As an incentive, your name will be entered into a drawing to win a $25 UMBC Bookstore Gift Card. The survey will be available from September 16, 2021 through October 2, 2021. |
We appreciate your mindfulness and ask you to continue taking care in the future. E-mail and text message scams surged at the start of the COVID-19 lockdown and show no sign of abating. As always, if you have a question about the validity of any message you receive at your UMBC email address, please contact us at security@umbc.edu.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
_________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Normally, these posts warn of various types of fraud and misdirection that try to mislead victims into giving up personal information and/or money. The Division of Information Technology (DoIT)...
https://dev.my.umbc.edu/api/v0/pixel/news/112696/guest@my.umbc.edu/0958fa3c814495248a0cb44c6cd997a1/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Mon, 27 Sep 2021 16:50:49 -0400
Job Phishing Alert: Department of Psychology
Another Day, Another Job Scam.
Recently, the Division of Information Technology(DOIT) received multiple reports of a job phishing email. The scammers sending these emails are impersonating Professor Cheah of the Department of Psychology. Below is an example of such an email. For privacy purposes, we removed the To field.
From: Department of Psychology <timothyj.sloan2@gmail.com> Date: Tue, Sep 14, 2021 at 12:38 PM Subject: Fall 2021 Campus Job Offer To: <YOUR CAMPUS ID@umbc.edu>
<YOUR CAMPUS ID>@umbc.edu The services of a student administrative assistant is urgently required to work part-time and get paid $300 weekly. Tasks will be carried out remotely and work time is 7hrs/week. If interested, send a copy of your updated resume and a functional whatsapp number to our Department of Psychology via this email address to proceed. Sincerely Charissa Cheah Professor Department of Psychology Office: Math/Psychology 330 Lab: Sondheim 404
|
Please note that the Psychology Department or Professor Cheah did not send this message. Three visible red flags in this email are:
The From address is not a UMBC email. If the Psychology Department or Prof. Cheah were sending this email, the From address would have been a UMBC email address. However, it was sent from <timothyj.sloan2@gmail.com>, which is not a UMBC affiliate. Please note that it could have been spoofed, even if it appears to originate from a UMBC email. Therefore, always check with DoIT(security@umbc.edu) or email/contact the impersonated person on a completely different email when you see a conflict in the address.
Whatsapp number. A lot of scammers will ask for your WhatsApp number. If their number gets reported, they could easily create a new one. The same can be said for an email address; however, if their email is blocked, they will lose responses from other phishing email recipients. If you ever receive a job offer asking for a WhatsApp number or a phone number in general, BE SUSPICIOUS!
The email template. This template is very common. After a quick Google search, we found three Job scams articles with the same template. So if you are ever in doubt, Google it! UMBC will not use a known phishing template to offer you a job opportunity.
For more information about phishing, visit:https://itsecurity.umbc.edu/critical/?id=98136.
If you have received any message similar to the one listed above, please forward it with its headers tosecurity@umbc.edu. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
______________________________________________________________________________________________________________________________________
Receive any suspicious emails?
Forward it to security@umbc.edu along with the email headers. For instructions, visit: https://wiki.umbc.edu/pages/viewpage.action?pageId=1867970.
Follow us on myUMBC:https://my3.my.umbc.edu/groups/itsecurity.
]]>
Recently, the Division of Information Technology(DOIT) received multiple reports of a job phishing email. The scammers sending these emails are impersonating Professor Cheah of the Department of...
https://dev.my.umbc.edu/api/v0/pixel/news/112661/guest@my.umbc.edu/5988209a4398f746f32066abad48bb68/api/pixel
notice
IT Security - DoIT Cybersecurity Assurance and Digital Trust
https://dev.my.umbc.edu/groups/itsecurity
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/original.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxlarge.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xlarge.png?1761588639
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/large.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/medium.png?1761588639
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/small.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xsmall.png?1761588639
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/660/859c6838736bc30c98279ed45d7fd70a/xxsmall.png?1761588639
IT Security - DoIT
0
0
true
Sun, 26 Sep 2021 21:25:43 -0400