Talk: Data-Efficient Robot Learning, 10-11am Mon. Oct. 23
Gaussian process models for learning good control strategies
Data-Efficient Robot Learning
Marc Deisenroth, University College London
10:00-11:00 am Monday, October 23, 2023
ITE 325b, UMBC
Data efficiency, i.e., learning from small datasets, is of practical importance in many real-world applications and decision-making systems. Data efficiency can be achieved in multiple ways, such as probabilistic modeling, where models and predictions are equipped with meaningful uncertainty estimates, Bayesian optimization, transfer learning, or the incorporation of valuable prior knowledge. In this talk, I will focus on how robot learning can benefit from data-efficient learning. In particular, I will motivate the use of Gaussian process models for learning good control strategies in three different settings: model-based reinforcement learning, transfer learning, and Bayesian optimization.
Professor Marc Deisenroth is the DeepMind Chair of Machine Learning and Artificial Intelligence at University College London, Deputy Director of the UCL Centre for Artificial Intelligence, and part of the UNESCO Chair on Artificial Intelligence at UCL. He also holds a visiting faculty position at the University of Johannesburg. Marc co-leads the Sustainability and Machine Learning Group at UCL. His research interests center around data-efficient machine learning, probabilistic modeling and autonomous decision making with applications in weather, nuclear fusion, and robotics. Marc was Program Chair of EWRL 2012, Workshops Chair of RSS 2013, EXPO Chair at ICML 2020, Tutorials Chair at NeurIPS 2021, and Program Chair at ICLR 2022. He is an elected member of the ICML Board. He received Paper Awards at ICRA 2014, ICCAS 2016, ICML 2020, AISTATS 2021, and FAccT 2023.
]]>
Data-Efficient Robot Learning Marc Deisenroth, University College London 10:00-11:00 am Monday, October 23, 2023 ITE 325b, UMBC Data efficiency, i.e., learning from small datasets, is...
https://dev.my.umbc.edu/api/v0/pixel/news/136443/guest@my.umbc.edu/064b72549cb88e77513217dcdc0e8b12/api/pixel
machine-learning
robotics
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 20 Oct 2023 14:04:18 -0400
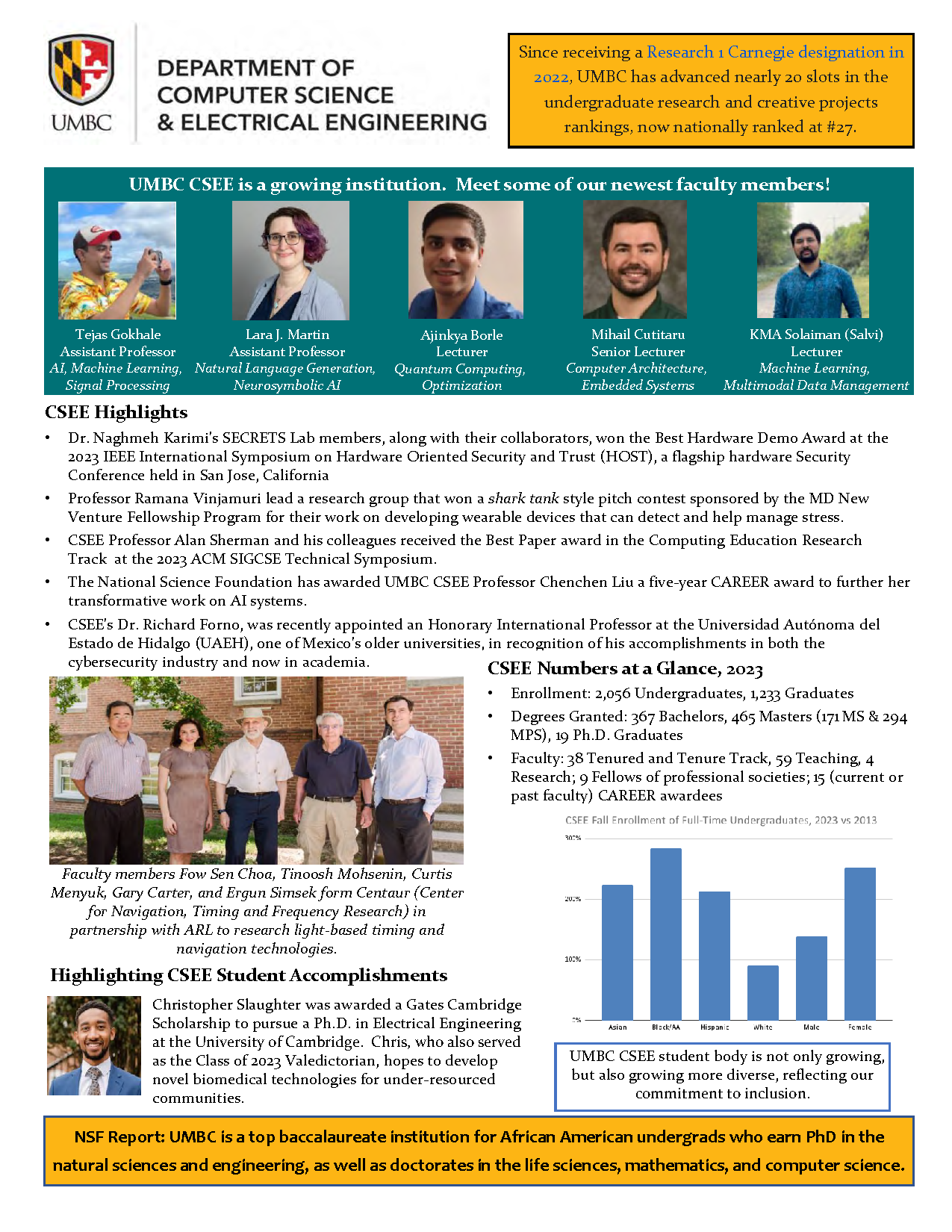
CSEE's 2023 CRA one-page overview
From the 2023 Computing Research Association Member Book
The Computing Research Association (CRA) published its 2023 Academic Member Book, which has one-page overviews for 126 of its academic department members in North America, including pages for CSEE and the UMBC Department of Information Systems. These one-page overviews highlight the latest achievements, news, and developments of their member's faculty and students. The CSEE 2023 one-page overview is shown below.
]]>
The Computing Research Association (CRA) published its 2023 Academic Member Book, which has one-page overviews for 126 of its academic department members in North America, including pages for CSEE...
https://cra.org/crn/2023/10/2023-cra-member-book-now-available/
https://dev.my.umbc.edu/api/v0/pixel/news/136359/guest@my.umbc.edu/118d6fc76038d7f7cf970f30c2246d85/api/pixel
cra
csee
hustler-v-falwell
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 17 Oct 2023 14:58:32 -0400
talk: Verifiable Election Technologies, 1-2pm Fri. Oct 20
How Voters Can Independently Verify their Votes
The UMBC Cyber Defense Lab presents
Verifiable Election Technologies:
How Voters Can Independently Verify that
their Votes have been Accurately Counted
Senior Principal Cryptographer, Microsoft Research
1-2pm Friday, October 20, 2023, via WebEx
With traditional election technologies, voters have little choice but to trust that others will curate and count their votes properly. They must trust their local election officials; they must trust the equipment that they use and, by extension, the vendors who built and programmed the equipment; and they must trust numerous other individuals and processes of which they may not even be aware. Even with hand-counted paper ballots, individual voters can observe at most a tiny fraction of the process and must trust others to ensure that the election tallies are correct. We can do better. This talk will show how "end-to-end verifiability" can be used in elections to enable voters to confirm for themselves that their votes have been accurately counted -- without having to trust any software, hardware, or personnel. This strategy is not just an academic exercise. Systems have been built and piloted in actual elections, and there is reason to be optimistic about broader deployments in the near future.
Josh Benaloh is the Senior Principal Cryptographer at Microsoft Research and an Affiliate Professor in the Allen School of Computer Science and Engineering at the University of Washington. His 1987 doctoral dissertation, "Verifiable Secret-Ballot Elections," introduced the use of homomorphic encryption to enable election verifiability, and he has published and spoken extensively on election technologies and systems. Dr. Benaloh is an author of numerous studies and reports including the 2015 U.S. Vote Foundation report on "The Future of Voting," the 2018 U.S. National Academies of Science, Engineering, and Medicine report "Securing the Vote -- Protecting American Democracy," and a 2022 report on the feasibility of Internet voting by the Goldman School of Public Policy of the University of California at Berkeley. He currently chairs the over 200-member Election Verification Network and is the principal designer of Microsoft's free, open-source ElectionGuard toolkit which is being used by numerous vendors to incorporate end-to-end verifiability into their election systems.
Host: Alan T. Sherman,
sherman@umbc.edu, Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681.
]]>
The UMBC Cyber Defense Lab presents Verifiable Election Technologies: How Voters Can Independently Verify that their Votes have been Accurately Counted Josh Benaloh Senior Principal...
https://dev.my.umbc.edu/api/v0/pixel/news/136272/guest@my.umbc.edu/00f18b2a39226f139e76f684dd060cba/api/pixel
cybersecurity
security
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
UMBC Cyber Defense Lab
0
0
true
Fri, 13 Oct 2023 17:45:07 -0400
Professor Zaidi Slides and Notes
Hello everyone! Thanks for attending Professor Zaidi's guest speaker event yesterday! Here are the slides Professor Zaidi made, along with the notes from the event!
]]>
Hello everyone! Thanks for attending Professor Zaidi's guest speaker event yesterday! Here are the slides Professor Zaidi made, along with the notes from the event! Link to the...
https://dev.my.umbc.edu/api/v0/pixel/news/136216/guest@my.umbc.edu/0f76063047ac631e1673ab1516f78c39/api/pixel
Information Systems Security Association, UMBC Chapter
https://dev.my.umbc.edu/groups/issa
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/original.jpg?1772925484
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxlarge.png?1772925484
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xlarge.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/large.png?1772925484
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/medium.png?1772925484
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/small.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xsmall.png?1772925484
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/514/0bdfb1231eca53e69ca24c2de2eb6912/xxsmall.png?1772925484
Information Systems Security Association, UMBC Chapter
1
0
true
Thu, 12 Oct 2023 10:12:30 -0400
Thu, 12 Oct 2023 10:12:49 -0400
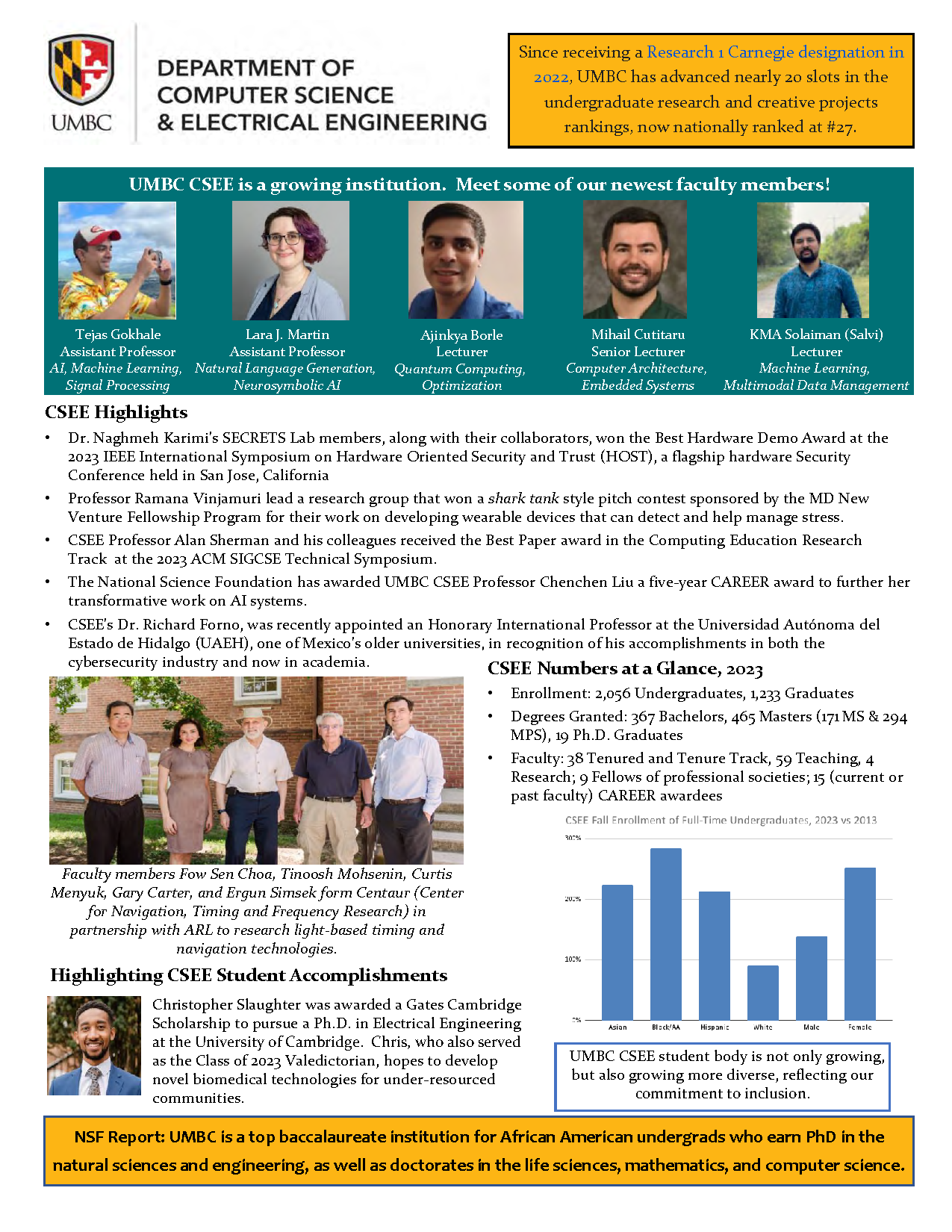
Prof. Matuszek on Talking to Robots, GRIT-X 2-4pm, Sat 10/14
The Role of Language in Human-Robot Interaction
CSEE professor Dr. Cynthia Matuszek will be one of this year's GRIT-X event speakers during the 2023 UMBC Homecoming celebration. Each of the nine speakers will give a 10-12 minute talk on their research and creative achievement.
Dr. Matuszek's topic is "Talking to Robots - The Role of Language in Human-Robot Interaction." As robots become more common and begin to make their way into human environments, it becomes more important for them to interact comfortably with end users. One way to accomplish that is to build robotic systems that can use natural languages (human languages, such as English) to interact with and learn from people around them. In her talk, she will describe the concept of grounded language -- language that robots can use to understand the physical world around them -- and talk about the promise, as well as some of the risks, of language-using robots.
The
2023 UMBC GRIT-X event takes place on Saturday, October 14, from 2-4 pm in the Fine Arts Recital Hall. After the talks, you can join the speakers for a post-event reception in the lobby.
]]>
CSEE professor Dr. Cynthia Matuszek will be one of this year's GRIT-X event speakers during the 2023 UMBC Homecoming celebration. Each of the nine speakers will give a 10-12 minute talk on their...
https://research.umbc.edu/grit-x/
https://dev.my.umbc.edu/api/v0/pixel/news/136198/guest@my.umbc.edu/2128bc74d58e74ecb64e06e071bbb07e/api/pixel
grit-x
homecoming
nlp
robot
robotics
umbc
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
University of Maryland, Baltimore County
0
0
true
Wed, 11 Oct 2023 17:35:30 -0400
Talk: MalDICT Benchmark Malware Datasets,12-1 ET Fri. Oct 6
Data on Behaviors, Platforms, Exploitation, and Packers
The UMBC Cyber Defense Lab presents
MalDICT: Benchmark Datasets on Malware Behaviors, Platforms, Exploitation, and Packers
RJ Joyce, CSEE Department, UMBC
12-1pm ET, Friday, 6 October 2023, via WebEx
Joint work with Edward Raff, Charles Nicholas, and James Holt
Existing research on malware classification focuses almost exclusively on two tasks: distinguishing between malicious and benign files, and classifying malware by family. Malware, however, can be categorized according to many other types of attributes, and the ability to identify these attributes in newly-emerging malware using machine learning will provide significant value to analysts. In particular, we have identified four tasks which are under-represented in prior work: classification by behaviors that malware exhibit, platforms that malware run on, vulnerabilities that malware exploit, and packers that packed the malware. To obtain labels for training and evaluating ML classifiers on these tasks, we created an antivirus (AV) tagging tool called ClarAVy. ClarAVy's sophisticated AV label parser distinguishes itself from prior AV-based taggers with the ability to parse 882 different AV label formats used by 90 different AV products accurately. We are releasing benchmark datasets for each of these four classification tasks, tagged using ClarAVy and comprising nearly 5.5 million malicious files in total. Our malware behavior dataset includes 75 distinct tags -- nearly seven times more than the only prior benchmark dataset with behavioral tags. To our knowledge, we are the first to release datasets with malware platform, exploitation, and packer tags.
RJ Joyce (
joyce8@umbc.edu) is a PhD student at UMBC under the supervision of Dr. Charles Nicholas and Dr. Edward Raff. Presently, RJ works as a data scientist at Booz Allen Hamilton performing research at the intersection of malware analysis and machine learning. RJ is also a visiting lecturer at UMBC and is teaching CMSC-426 Principles of Computer Security course this semester.
Host: Alan T. Sherman,
sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681. The UMBC Cyber Defense Lab meets biweekly Fridays 12-1pm. All meetings are open to the public. Upcoming CDL meetings: Oct. 20 (1-2pm) Josh Benaloh (Microsoft), ElectionGuard; Nov. 3, Jason Rheinhart (Sandia), Risk analysis; Nov. 17 (1-2pm) Austin Murdoch (Sixmap); Dec. 1, Enis Golaszewski (UMBC), Automatic cryptographic bindings; Jan. 16-19, 2024, UMBC SFS/CySP Research Study.
]]>
The UMBC Cyber Defense Lab presents MalDICT: Benchmark Datasets on Malware Behaviors, Platforms, Exploitation, and Packers RJ Joyce, CSEE Department, UMBC 12-1pm ET, Friday, 6 October...
https://dev.my.umbc.edu/api/v0/pixel/news/135903/guest@my.umbc.edu/dae74886999cf28e98b8b45457d022a9/api/pixel
antivirus
cybersecurity
dataset
malware
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
UMBC Cyber Defense Lab
1
0
true
Sun, 01 Oct 2023 14:30:22 -0400
talk: Community Detection in Multilayer Networks, 1-2pm 10/3
Community Detection in Multilayer Networks:
Algorithms and Applications
Prof. Selin Aviyente, Michigan State University
1-2pm Tue 3 October 2023, ITE 325b
Modern data analysis and processing tasks typically involve large sets of structured data, where the structure carries critical information about the nature of the data. Typically, graphs are used as mathematical tools to describe the structure of such data. Traditional network models employ simple graphs where the nodes are connected to each other by a single, static edge. However, in many contemporary applications, this relatively simple structure cannot capture the diverse nature of the networks, e.g., multiple types of entities and interactions between them. Multilayer networks (MLNs) allow one to represent the interactions between a pair of nodes through multiple types of links. MLNs can further be categorized based on the homogeneity of the nodes and complexity of topological structure as: i) multiplex networks where each layer has the same set of entities of the same type and inter-layer edges are not shown as they are implicit; ii) heterogenous multilayer networks where the set and types of entities may be different for each layer and the relationships of entities across layers are shown using explicit inter-layer edges. A core task in the complexity reduction of these high-dimensional networks is community detection. In this talk, a joint nonnegative matrix factorization approach is proposed to detect the community structure in both multiplex and multilayer networks. The proposed approach considers the heterogeneity of layers and formulates community detection as a regularized optimization problem. Applications of the proposed approach for social and biological networks will be highlighted.
Selin Aviyente received her B.S. degree with high honors in Electrical and Electronics engineering from Bogazici University, Istanbul. She received her M.S. and Ph.D. degrees, both in Electrical Engineering: Systems, from the University of Michigan, Ann Arbor. She joined the Department of Electrical and Computer Engineering at Michigan State University in 2002, where she is currently a Professor and Associate Chair for Undergraduate Studies. Her research focuses on statistical and nonstationary signal processing, higher-order data representations and network science with applications to neuronal signals. She has authored more than 150 peer-reviewed journal and conference papers. She is the recipient of a 2005 Withrow Teaching Excellence Award, a 2008 NSF CAREER Award and 2021 Withrow Excellence in Diversity Award. She is currently serving as the chair of IEEE Signal Processing Society Bioimaging and Signal Processing Technical Committee, on the Steering Committees of IEEE SPS Data Science Initiative and IEEE BRAIN. She has served as an Associate Editor and Senior Area Editor for IEEE Transactions on Signal Processing, IEEE Transactions on Signal and Information Processing over Networks, IEEE Open Journal of Signal Processing and Digital Signal Processing.
]]>
Community Detection in Multilayer Networks: Algorithms and Applications Prof. Selin Aviyente, Michigan State University 1-2pm Tue 3 October 2023, ITE 325b Modern data analysis and...
https://dev.my.umbc.edu/api/v0/pixel/news/135813/guest@my.umbc.edu/2d7421ab49c73e50248b72e6c590e7b1/api/pixel
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 27 Sep 2023 13:36:59 -0400
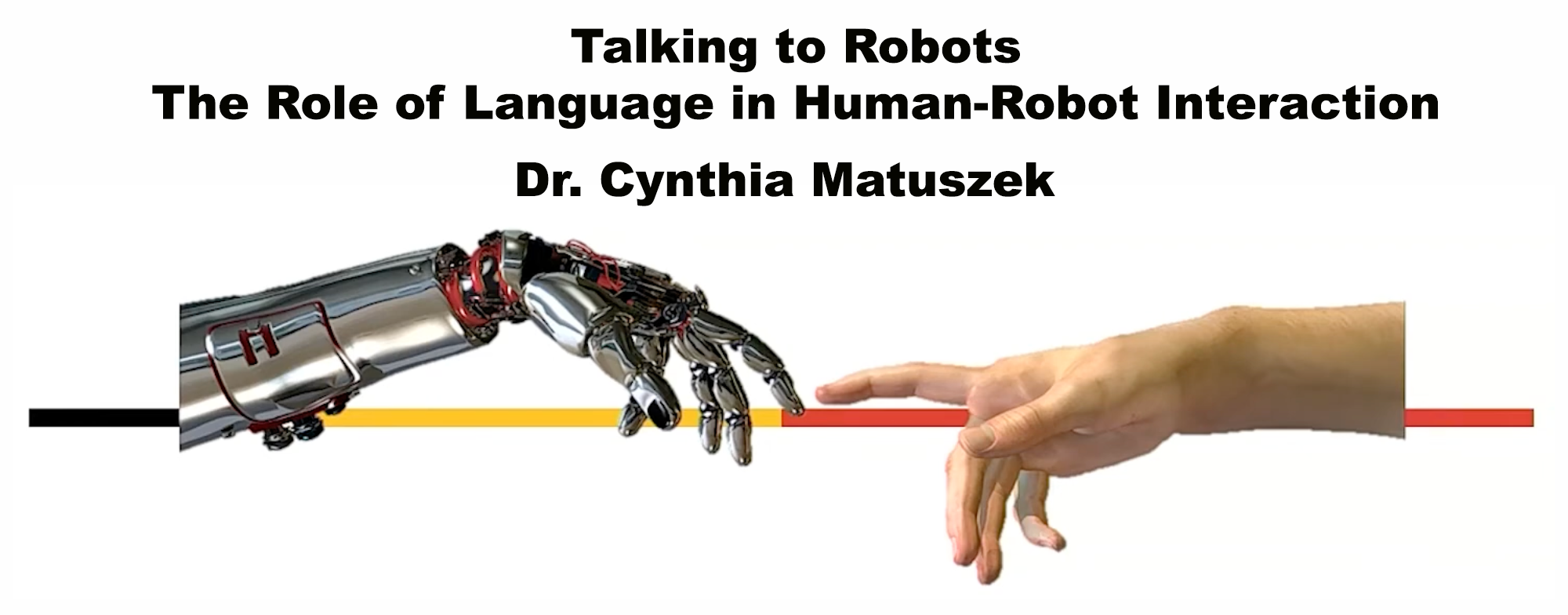
talk: Analysis of Session Binding Proxy Protocol, 12-1 9/29
Advantages and Dangers of Oblivious Protocol Participants
SBP protocol prevents session hijacking by binding application session to underlying network session
The UMBC Cyber Defense Lab presents
Formal-Methods Analysis of the Session Binding Proxy Protocol:
Advantages and Dangers of Oblivious Protocol Participants
12-1:00 pm, Friday, 29 September 2023, via WebEx
Enis Golaszewski, PhD Student, CSEE, UMBC
Joint work with Alan T. Sherman, Edward Zieglar, and Kirellos Abou Elsaad
We present a formal-methods analysis of the
Session Binding Proxy (SBP) protocol, in which we highlight the advantages and dangers of an oblivious protocol participant: an unaware web server residing behind an SBP reverse-proxy. We carry out our analysis using the
Cryptographic Protocol Shapes Analyzer (CPSA) on three deployment variations of SBP: a server that embeds a proxy, a stand-alone proxy on a private network, and a stand-alone proxy on a public network. Our analysis reveals fundamental issues affecting oblivious protocol participants in a Dolev-Yao (DY) network: to mitigate adversarial protocol interactions, deployments of SBP must ensure that the server authenticate and communicate exclusively with a legitimate proxy by establishing a private communication channel, deploying mutual authentication such as mutual Transport Layer Security (mTLS), or embedding the proxy with the server.
Our work identifies benefits and risks of wrapper protocols such as SBP, which wrap existing legacy or third-party systems to mitigate known vulnerabilities. Additionally, we identify minimal requirements for cryptographic binding, a vital tool for resisting protocol interactions, implement a "tailgating" attack on SBP, and discuss the pitfalls of ad-hoc, overly constrained adversarial models.
About the Speaker. Enis Golaszewski (
golaszewski@umbc.edu) is a computer science PhD student at UMBC working with Prof. Alan T. Sherman, where he studies, researches, and teaches cryptographic protocol analysis.
Host: Alan T. Sherman,
sherman@umbc.edu. Support for this event was provided in part by the National Science Foundation under SFS grant DGE-1753681.
]]>
SBP protocol prevents session hijacking by binding application session to underlying network session The UMBC Cyber Defense Lab presents Formal-Methods Analysis of the Session Binding...
https://dev.my.umbc.edu/api/v0/pixel/news/135790/guest@my.umbc.edu/f43d9419df494363831473d9c64dea63/api/pixel
cyberseccurity
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
UMBC Cyber Defense Lab
0
0
true
Tue, 26 Sep 2023 20:39:44 -0400
Cybersecurity Scholarships Available
NSF CyberCorps Scholarship for Service, apply by 11/30

Due to available funding, we are able to continue accepting applications from graduate and undergraduate students for the elite
NSF CyberCorps: Scholarship For Service (SFS) Program. Applications will be reviewed and awards made on a rolling basis through 30 November so those interested are *strongly* encouraged to apply ASAP while funds are available. Awards can be made for the current semester!
SFS funding includes full-time tuition, fees, annual stipends of $27,000 (undergrad) to $37,000 (graduate), and generous professional development funds for equipment, training, conferences, etc. After graduation, SFS Scholars must work for the US government in a cybersecurity role for each year of funding received. USA citizenship or permanent residency required - MINIMUM GPA of 3.00 needed.
]]>
Due to available funding, we are able to continue accepting applications from graduate and undergraduate students for the elite NSF CyberCorps: Scholarship For Service (SFS) Program. Applications...
https://dev.my.umbc.edu/api/v0/pixel/news/135680/guest@my.umbc.edu/ac464e275de6bcdbeb75824d39f0d800/api/pixel
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Fri, 22 Sep 2023 11:14:38 -0400
Talk: Alternative Perspectives on Cyber Warfare 10/2
Monday 2 October 2023 7-8:15pm ET (online via Webex)
Alternative Perspectives on Cyber Warfare
Dr. Rain Ottis
Associate Professor, Tallinn University of Technology
Monday 2 Oct. 2023 7-8:15pm ET (online via WebEx)
UMBC's CYBR program and the UMBC Center for Cybersecurity welcomes Dr. Rain Ottis for a virtual lecture/discussion about cybersecurity and cyber warfare! Estonia is one of the global centers of cyber with the NATO Cooperative Cyber Defense Centre of Excellence (CCDCOE) located in Tallinn. Dr. Ottis' remarks will explore and foster discussion on cyber warfare issues by approaching and framing them from alternative and/or non-Western perspectives. Such contexts can provide valuable insight given the global nature of cyber warfare and especially Estonia's close proximity to Russia and the ongoing war in Ukraine.
Dr. Rain Ottis is the Director of the Centre for Digital Forensics and Cyber Security in Tallinn University of Technology, Estonia. From 2008 to 2012, he served as a scientist at the NATO Cooperative Cyber Defence Centre of Excellence, where he worked on cyber security in the context of national and international security. Prior to that assignment he served as a communications officer in the Estonian Defence Forces, focusing primarily on cyber defense training and awareness. His research interests include cyber conflict, national cyber security, cyber defence exercises, and the role of serious games in cyber security.
Dr. Ottis holds a PhD in Computer Science from Tallinn University of Technology (TalTech), MSc in Engineering Informatics from TalTech, and a BS in Computer Science from the United States Military Academy at West Point.
]]>
Alternative Perspectives on Cyber Warfare Dr. Rain Ottis Associate Professor, Tallinn University of Technology Monday 2 Oct. 2023 7-8:15pm ET (online via WebEx) UMBC's CYBR program and...
https://dev.my.umbc.edu/api/v0/pixel/news/135647/guest@my.umbc.edu/9122926ae3c041449c0df97088de0fc9/api/pixel
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 21 Sep 2023 11:42:28 -0400
Thu, 28 Sep 2023 17:57:41 -0400