talk: Morik on Data Analytics for Sustainability, 11am Thr 5/22, ITE456

Computer Science and Electrical Engineering
University of Maryland, Baltimore County
Data Analytics for Sustainability
Professor Katharina Morik
TU Dortmund University, Germany
11:00am-12:30pm, Thursday 22 May 2014, ITE 456, UMBC
Sustainability has many facets and researchers from many disciplines are working on them. Particularly knowledge discovery always considered sustainability an important topic (e.g., special issue on data mining for sustainability in Data Mining and Knowledge Discovery Journal, March 2012).
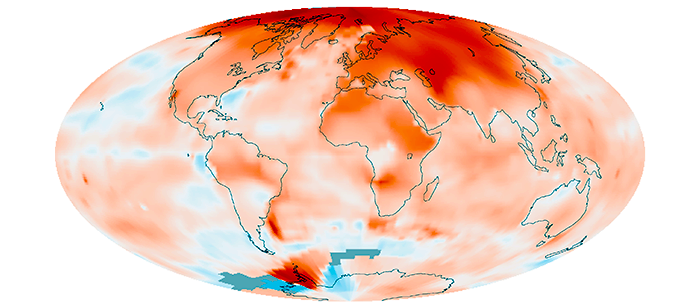
- Environmental tasks include risk analysis concerning floods, earthquakes, fires, and other disasters as well as the ability to react to them in order to guarantee resilience. The climate is certainly of influence and the debate on climate change received quite some attention.
- Energy efficiency demands energy-aware algorithms, operating systems, green computing. System operations are to be adapted to a predicted user behavior such that the required processing is optimized with respect to minimal energy consumption.
- Engineering tasks in manufacturing, assembly, material processing, and waste removal or recycling offer opportunities to save resources to a large degree. Adding the prediction precision of learning algorithms to the general knowledge of the engineers allows for surprisingly large savings.
Global reports on the millennium goals and open government data regarding sustainability are publicly available. For the investigation of influence factors, however, data analytics is necessary. Big data challenges the analysis to create data summaries. Moreover, the prediction of states is necessary in order to plan accordingly. In this talk, two case studies will be presented. Disaster management in case of a flood combines diverse sensor data streams for a better traffic administration. A novel spatiotemporal random field approach is used for smart routing based on traffic predictions. The other case study is in engineering and saves energy in the steel production based on the multivariate prediction of the processing end-point by the regression support vector machine.
Further reading:
- Katharina Morik, Kanishka Bhaduri, Hillol Kargupta “Introduction to Data Mining for Sustainability”, Data Mining and Knowledge Discovery Journal, Vol. 24, No.2, pp. 311 – 324, 2012.
- Nico Piatkowski, Sangkyun Lee, Katharina Morik “Spatio-Temporal Random Fields: Compressible Representation and Distributed Estimation”, Machine Learning Journal Vol.93, No. 1, pp: 115-139, 2013.
- Jochen Streicher, Nico Piatkowski, Katharina Morik, Olaf Spinczyk “Open Smartphone Data for Mobility and Utilization Analysis in Ubiquitous Environments” In: Mining Ubiquitous and Social Environments (MUSE) workshop at ECML PKDD, 2013.
- Norbert Uebbe, Hans Jürgen Odenthal, Jochen Schlüter, Hendrik Blom, Katharina MorikA novel data-driven prediction model for BOF endpoint. In: The Iron and Steel Technology Conference and Exposition in Pittsburgh (AIST), 2013.
- Alexander Artikis, Matthias Weidlich, Francois Schnitzler, Ioannis Boutsis, Thomas Liebig, Nico Piatkowski, Christian Bockermann, Katharina Morik, Vana Kalogeraki, Avigdor Gal, Shie Mannor, Dimitrios Gunopulos, Dermot Kinane, “Heterogeneous Stream Processing and Crowdsourcing for Urban Traffic Management” Procs. 17th International Conference on Extending Database Technology, 2014.

Katharina Morik is full professor for computer science at the TU Dortmund University, Germany. She earned her Ph.D. (1981) at the University of Hamburg and her habilitation (1988) at the TU Berlin. Starting with natural language processing, her interest moved to machine learning ranging from inductive logic programming to statistical learning, then to the analysis of very large data collections, high-dimensional data, and resource awareness.
Her aim to share scientific results strongly supports open source developments. For instance, RapidMiner started out at her lab, which continues to contribute to it. She was one of those starting the IEEE International Conference on Data Mining together with Xindong Wu, and was chairing the program of this conference in 2004. She was the program chair of the European Conference on Machine Learning (ECML) in 1989 and one of the program chairs of ECML PKDD 2008. She is in the editorial boards of the international journals “Knowledge and Information Systems” and “Data Mining and Knowledge Discovery”. Since 2011 she is leading the collaborative research center SFB876 on resource-constrained data analysis, an interdisciplinary center comprising 12 projects, 19 professors, and about 50 Ph. D students or Postdocs.
Host: Hillol Kargupta, Sorry, you need javascript to view this email address.
]]>
Computer Science and Electrical Engineering University of Maryland, Baltimore County Data Analytics for Sustainability Professor Katharina Morik TU Dortmund University, Germany...
http://www.csee.umbc.edu/2014/05/talk-morik-on-data-analytics-for-sustainability-11am-thr-522-ite456/
https://dev.my.umbc.edu/api/v0/pixel/news/44684/guest@my.umbc.edu/5594e32f6dbe7a42cdd631cb6774c343/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 15 May 2014 09:25:48 -0400
Thu, 15 May 2014 09:25:48 -0400
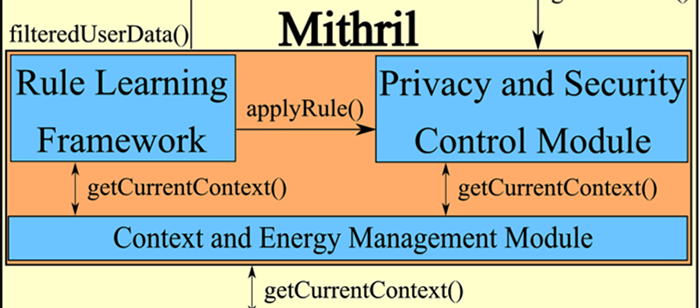
PhD proposal: Das on Privacy & Security Management on Mobile Devices, 8am Fri 5/16
PhD Dissertation Proposal
Learning and Executing Energy Efficient, Context-Dependent
Rules for Privacy and Security Management on Mobile Devices
Prajit Kumar Das
8:00am Friday, 16 May 2014, ITE325b
There are ongoing security and privacy concerns around mobile platforms that are increasingly being used by citizens. For example a newly discovered security flaw in WhatsApp that allows hackers using a malicious app to read chat messages stored on the SD card. The Brightest Flashlight application was reported to have logged precise location and a unique user identifier, which have nothing to with its intended functionality. Current mobile platform privacy and security mechanisms are limited to an initial installation phase permission acquisition method. In addition to that, the permissions are of the all or none form. This means that either the users accept all the permissions requested by the mobile app or they cannot use the app in question. Even if permissions were not structured as such, typically, users do not understand the permissions being requested or are too eager to use the application to even care to read them. These issues are present in all major mobile operating systems. Given the penetration of mobile devices into our lives, a fine-grained context-dependent security and privacy control approach needs to be created.
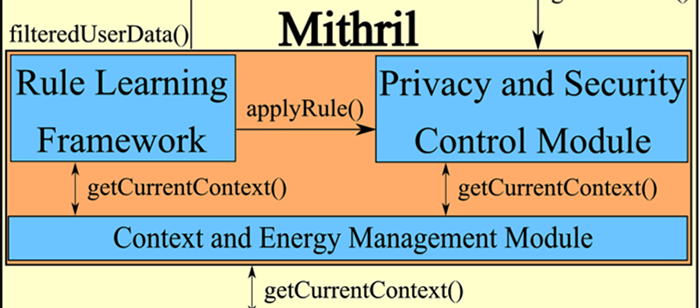
We propose a framework that will allow us to learn the privacy and security rules for a particular user, on their mobile devices. We do this by employing a simple user feedback mechanism. The rule learning framework consists of a “learning mode” where it observes and learns from user behavior and a “working mode” where it implements the learned rules to protect user privacy and provide security. The rules are represented to the user in plain English using an easily understandable construct. The rules are internally written in a logic based language and using Semantic Web technologies. The antecedents of the rules are context elements that are derived from an ontology using a query engine and an inference mechanism. The main contributions of our work include learning modifications to current rules and learning new rules to control the data flow between the various data providers on the user’s mobile device, including sensors and services and the consumer of such data. The privacy and security rule execution consumes significant energy due to the context detection. We create an energy model that allows us to make energy cost optimizations with regards to rule execution. We use a three-fold solution for achieving the said energy cost optimizations.
Committee: Drs. Anupam Joshi (chair), Nilanjan Banerjee, Dipanjan Chakraborty (IBM), Tim Finin, Tim Oates, Arkady Zaslavsky (CSIRO)
]]>
PhD Dissertation Proposal Learning and Executing Energy Efficient, Context-Dependent Rules for Privacy and Security Management on Mobile Devices Prajit Kumar Das 8:00am Friday, 16 May 2014,...
http://www.csee.umbc.edu/2014/05/phd-proposal-das-on-privacy-security-management-on-mobile-devices-8am-fri-516/
https://dev.my.umbc.edu/api/v0/pixel/news/44675/guest@my.umbc.edu/0669d08ce16124c5d8716994e0eaad16/api/pixel
graduate
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Thu, 15 May 2014 00:28:11 -0400
Wed, 14 May 2014 00:28:11 -0400
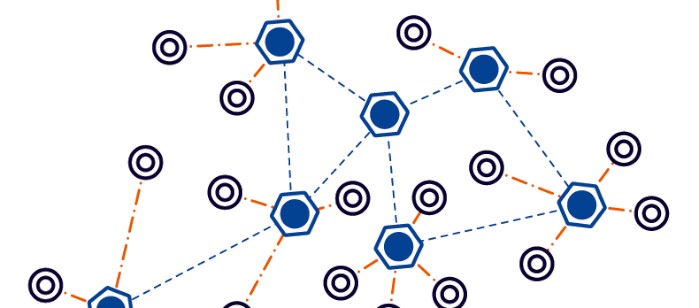
PhD proposal: Yatish Joshi on connectivity restoration in wireless sensor networks
PhD Proposal
Distributed protocols for connectivity restoration
in damaged wireless sensor networks
Yatish K. Joshi
1:00pm Monday, 12 May 2014, ITE325b, UMBC
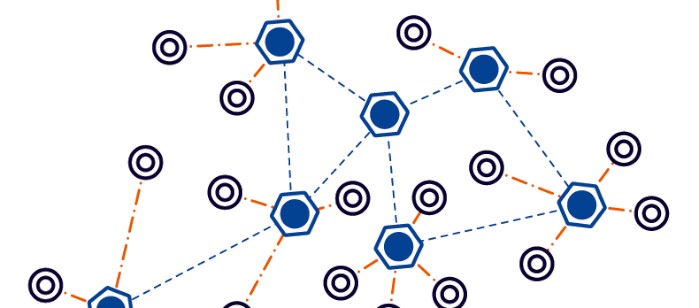
Decreasing costs and increasing functionality of embedded computation and communication devices have made Wireless Sensor Networks (WSNs) attractive for applications that serve in inhospitable environments like battlefields, planetary exploration or environmental monitoring. WSNs employed in these environments are expected to work autonomously and extend network lifespan for as long as possible while carrying out their designated tasks. The harsh environment exposes the individual nodes to q high risk of failure, which can potentially partition the network into disjoint segments. Therefore, a network must be able to self-heal and restore lost connectivity using available resources. The ad-hoc nature of deployment, harsh operating environment and lack of resources makes distributed approaches the most suitable choice for recovery.
Most solution strategies for tolerating the failure of multiple collocated nodes are based on centralized approaches that pursue the placement of additional relays to form a connected inter-segment topology. While they are the ideal solution for dealing with simultaneous multi-node failures, they need to utilize the entire network state to determine where and how recovery should occur. In addition to the scalability concern of these approaches, controlled placement of stationary relays in remote and inhospitable deployment area may not be logistically feasible due to resource unavailability and would not be responsive due to the delay in transporting the resources to the area. Space exploration is an example of those WSN applications in which placement of stationary relays is not practical.
In this proposal, we tackle the problem of connectivity restoration in a partitioned WSN in a distributed manner. We consider multiple variants of the problem based on the available resources and present novel recovery schemes that suit the capabilities and count of existing nodes.
Committee: Drs. Mohamed Younis (Chair), Dr. Charles Nicholas, Dr. Chintan Patel, Dr. Kemal Akkaya (SIU-Carbondale)Dr. Waleed Youssef (IBM)
]]>
PhD Proposal Distributed protocols for connectivity restoration in damaged wireless sensor networks Yatish K. Joshi 1:00pm Monday, 12 May 2014, ITE325b, UMBC Decreasing costs and...
http://www.csee.umbc.edu/2014/05/16920/
https://dev.my.umbc.edu/api/v0/pixel/news/44516/guest@my.umbc.edu/507c48b92adeb93d4f814c24ae9b5bb3/api/pixel
defense
graduate
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Fri, 09 May 2014 10:34:04 -0400
Mobile computing & smart home automation demos, 12:30-2:00 Mon 5/12, ITE

Demos: Introduction to mobile computing and
systems for smart home automation
12:30-2:00 Monday, 12 May 2014, 3rd floor corridor, ITE Building
The students in Professor Banerjee’s Introduction to Mobile Computing and Systems for Smart Home Automation classes will showcase their cutting edge projects and application that use mobile phones, tablets, cloud services, and smarthome sensors.
Come and enjoy the demonstrations that range from cool smartphone games to smartphone-based educational tools to smartphone-controlled robots to location-based mobile phone services to voice and mind controlled home appliances.
The demonstrations will take place from 12:30 to 2:00pm on Monday, May 12 in the central corridor of the third floor of the ITE building at UMBC.
For more information, contact Dr. Nilanjan Banerjee (Sorry, you need javascript to view this email address. )
]]>
Demos: Introduction to mobile computing and systems for smart home automation 12:30-2:00 Monday, 12 May 2014, 3rd floor corridor, ITE Building The students in Professor Banerjee’s...
http://www.csee.umbc.edu/2014/05/mobile-computing-smart-home-automation-demos-1230-200-mon-512-ite/
https://dev.my.umbc.edu/api/v0/pixel/news/44413/guest@my.umbc.edu/063ca7437e7972ca550d84f8451eba5f/api/pixel
computer-engineering
computer-science
events
news
students
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 07 May 2014 09:35:16 -0400
Wed, 07 May 2014 09:35:16 -0400
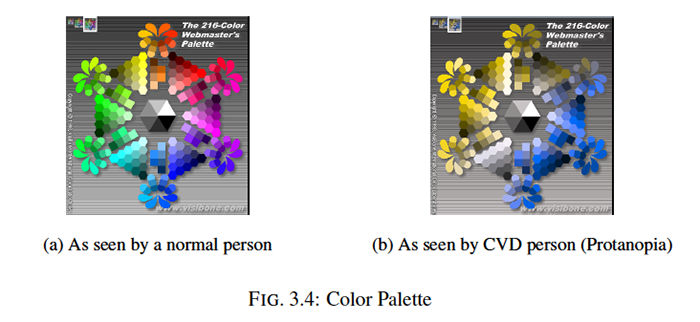
MS defense: Bansal on Recoloring Web Pages for CVD
MS Thesis Defense
Recoloring Web Pages For Color Vision Deficiency Users
Vikas Bansal
11:00am Thursday, May 8, 2014, ITE346, UMBC
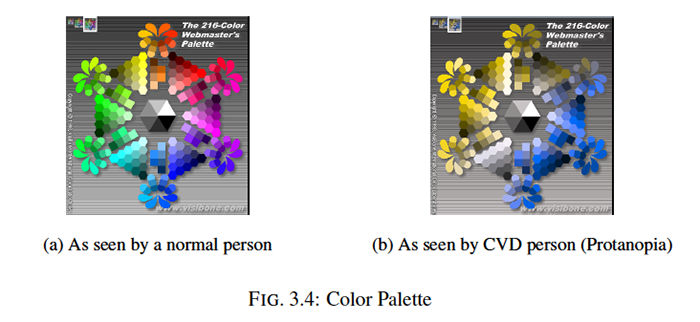
Color vision begins with the activation cone cells. When one of the cone cells dysfunction, color vision deficiency (CVD) ensues. Due to CVD, users become unable to differentiate as many colors a normal person can. Lack of this ability results in less rich web experience, incomprehension of basic information and thus frustration. Solutions such as carefully choosing colors while designing or recolor web pages for CVD users exist. We first present the improvement in the time complexity of an existing tool SPRWeb to recolor web pages. After that we present our tool which explores the foreground-background relationship between colors in a web page. Using this relationship we propose an algorithm which preserves naturalness, pair-differentiability and subjectivity. In the last part, we add an additional step in to algorithm to ensure that the contrast in the parsed color pairs meets the required W3C guidelines. In evaluation, we found that our algorithm does significantly better in preserving pair-differentiability and produces lower total cost solutions than SPRWeb. Quantitative experimentation of modified algorithm shows that contrast ratio in each replacement pair is more than 4.5 as required for readability.
Committee: Drs. Lina Zhou (co-chair), Tim Finin (ch-chair), Yelena Yesha, Dongsong Zhang
]]>
MS Thesis Defense Recoloring Web Pages For Color Vision Deficiency Users Vikas Bansal 11:00am Thursday, May 8, 2014, ITE346, UMBC Color vision begins with the activation cone cells. When...
http://www.csee.umbc.edu/2014/05/ms-defense-bansal-on-recoloring-web-pages-for-cvd/
https://dev.my.umbc.edu/api/v0/pixel/news/44373/guest@my.umbc.edu/617ab398f3b2de30b3dac5e61da9cd79/api/pixel
computer-science
defense
graduate
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Tue, 06 May 2014 12:40:17 -0400
talk: Ron Ross (NIST) on Cybersecurity, 6pm Wed 4/30

UMBC Information Systems Security Association Seminar
Framework for Improving Critical
Infrastructure in Cybersecurity
Dr. Ron Ross, NIST
6:00-8:00pm Wednesday, 30 April 20014
Meyerhoff 030 Building Lecture Hall 2
RSVP
Schedule:
6:00-6:30pm Introductions to UMBC ISSA, Networking & Pizza
6:30-7:30pm Cyber Security Lecture From Dr. Ron Ross
7:30-8:00pm Networking
Host: Monique Jeffrey, UMBC ISSA President, Sorry, you need javascript to view this email address.
Ron Ross is a Fellow at the National Institute of Standards and Technology (NIST). His current areas of specialization include information security and risk management. Dr. Ross leads the Federal Information Security Management Act (FISMA) Implementation Project, which includes the development of security standards and guidelines for the federal government, contractors, and the United States critical information infrastructure.
A graduate of the United States Military Academy at West Point, Dr. Ross served in a variety of leadership and technical positions during his over twenty-year career in the United States Army. While assigned to the National Security Agency, he received the Scientific Achievement Award for his work on an inter-agency national security project and was awarded the Defense Superior Service Medal upon his departure from the agency. Dr. Ross is a three-time recipient of the Federal 100 award for his leadership and technical contributions to critical information security projects affecting the federal government and is a recipient of the Department of Commerce Gold and Silver Medal Awards.
Dr. Ross has been inducted into the Information Systems Security Association (ISSA) Hall of Fame and given its highest honor of ISSA Distinguished Fellow. Dr. Ross has also received several private sector cyber security awards and recognition including the Vanguard ChairmanÕs Award, the Symantec Cyber 7 Award, InformationWeek’s Government CIO 50 Award, Best of GTRA Award, and the ISACA National Capital Area Conyers Award. During his military career, Dr. Ross served as a White House aide and as a senior technical advisor to the Department of the Army. Dr. Ross is a graduate of the Defense Systems Management College and holds Masters and Ph.D. degrees in Computer Science from the U.S. Naval Postgraduate School specializing in artificial intelligence and robotics.
]]>
UMBC Information Systems Security Association Seminar Framework for Improving Critical Infrastructure in Cybersecurity Dr. Ron Ross, NIST 6:00-8:00pm Wednesday, 30 April 20014 Meyerhoff...
http://www.csee.umbc.edu/2014/04/talk-ron-ross-nist-on-cybersecurity-6pm-web/
https://dev.my.umbc.edu/api/v0/pixel/news/43973/guest@my.umbc.edu/f5aaf3ffb7a5cdf8100ce141a97fe73e/api/pixel
cybersecurity
news
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
2
0
true
Mon, 28 Apr 2014 23:46:57 -0400
Mon, 28 Apr 2014 23:46:57 -0400
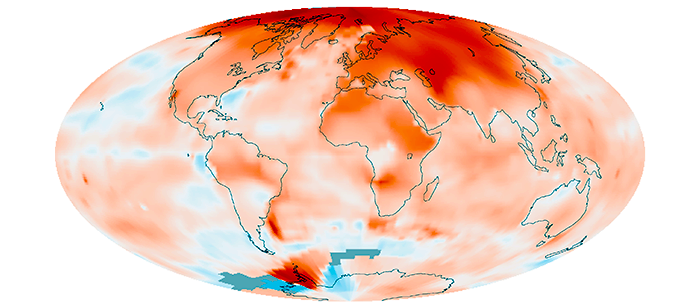
talk: White House Climate Data Initiative, 3pm Tue 4/29
Center for Hybrid Multicore Productivity Research
Distinguished Computational Science Lecture Series
The White House Climate Data Initiative
Eric Letvin
Director, Disaster and Failure Studies
National Security Council
3:00pm Tuesday, 29 April 2014, ITE 456, UMBC
Delivering on the commitment in the President’s Climate Action Plan, the White House recently launched the Climate Data Initiative — a broad effort to leverage the Federal Government’s extensive, freely- available climate-relevant data resources to advance awareness of and preparedness for climate change impacts. This effort will help give communities across America the information and tools they need to plan for current and future climate impacts. Data from NOAA, NASA, the U.S. Geological Survey, the Department of Defense, and other Federal agencies was recently launched on climate.data.gov. Data and innovation challenges issued by public, private, nonprofit, and other organizations can help catalyze new, data-driven solutions that help communities understand and build resilience to climate change. NOAA and NASA recently announced an innovation challenge calling on researchers and developers to create data-driven simulations to help plan for the future and to educate the public about the vulnerability of their own communities to sea level rise and flood events.
Mr. Eric Letvin PE, Esq, is the Director of Hazard Mitigation and Risk Reduction Policy within the National Security Council in the Executive Office of the President. He coordinates the development and effective delivery of mitigation capabilities identified in the National Preparedness Goal, such as threat and hazard identification, risk and disaster resilience assessment, planning, and long-term vulnerability reduction.
When at NIST, Mr. Letvin is the Disaster and Failure Studies Program Director within NIST’s Engineering Laboratory. Mr. Letvin provides national coordination for conducting field data collection studies. He is also responsible for creating and maintaining a repository related to hazard events (earthquakes, hurricanes, tornadoes, windstorms, community-scale fires in the wildland-urban interface, structural fires, storm surge, flood, tsunami) and human-made hazards (accidental, criminal, or terrorist), the performance of the built environment during hazard events, associated emergency response and evacuation procedures.
Before coming to NIST, Mr. Letvin was Leader of Infrastructure Research and Resiliency in the Homeland Security Group of URS. He has participated in numerous post-disaster studies including the bombing of the Murrah Building in Oklahoma City, and Hurricanes Opal, Ike and Katrina. He has assessed over 200 buildings for risk from terrorist threats and natural disasters.
Mr. Letvin holds a bachelor’s and master’s degree in environmental engineering from Syracuse University and received his Juris Doctor from the University of Maryland. He has taught many courses on risk assessments and protection of infrastructure for FEMA/DHS and made related presentations throughout the world over the last ten years.
]]>
Center for Hybrid Multicore Productivity Research Distinguished Computational Science Lecture Series The White House Climate Data Initiative Eric Letvin Director, Disaster and Failure...
http://www.csee.umbc.edu/2014/04/talk-white-house-climate-data-initiative-3pm-tue-429/
https://dev.my.umbc.edu/api/v0/pixel/news/43932/guest@my.umbc.edu/eb512b27fffdff5375203bc4dcef166b/api/pixel
news
research
talks
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
4
0
true
Sat, 26 Apr 2014 07:57:55 -0400
Graduate Cybersecurity Internships at NCCoE

The NIST National Cybersecurity Center for Excellence (NCCoE) is seeking full- and part-time paid interns from UMBC graduate students studying cybersecurity at the Universities at Shady Grove (USG). The program is part of NCCoE’s ongoing efforts to build and sustain academic partnerships in the Montgomery County region.
The NCCoE internship will identify and immerse students in practical cybersecurity experiences at the NCCoE in Rockville, MD. NCCoE’s Cybersecurity Graduate Researchers will work in a state-of-the-art facility with expert cybersecurity practitioners from government and academia, along with engineers from some of the largest and most influential IT and cybersecurity companies in the world, including Intel, Microsoft, Symantec, HP, Cisco, Splunk, Palo Alto Networks, and Hytrust.
During their internships, NCCoE’s Graduate Cybersecurity Researchers may assist NCCoE staff and contractors in areas such as:
the design and building of cybersecurity reference designs to demonstrate platform capabilities that address one or more challenges identified by industry.
mentoring undergraduate cybersecurity researchers and helping build teams to work on research projects.
working with NCCoE industry partners and collaborators to identify relevant commercially available technologies that can serve as a component of these reference designs.
supporting the NCCoE lab infrastructure, including the provisioning of hardware, creation and management of both virtual and physical equipment, and the installation and configuration of cybersecurity tools and components.
These NCCoE internships are open to UMBC cybersecurity students enrolled at the USG campus who are US citizens. The deadline for Summer 2014 consideration is Monday, May 5, however internships are available during the 2014-15 academic year as well.
For more information and/or to apply, please contact the USG Career & Internship Services Center at 301-738-6338 or Sorry, you need javascript to view this email address.
]]>
The NIST National Cybersecurity Center for Excellence (NCCoE) is seeking full- and part-time paid interns from UMBC graduate students studying cybersecurity at the Universities at Shady Grove...
http://www.csee.umbc.edu/2014/04/graduate-cybersecurity-internships-at-nccoe/
https://dev.my.umbc.edu/api/v0/pixel/news/43911/guest@my.umbc.edu/721a0b8ed443dd844f616689f5cc0850/api/pixel
computer-science
csee
cybersecurity
news
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 24 Apr 2014 21:34:34 -0400
Thu, 24 Apr 2014 21:34:34 -0400
ACTIVE Center Open House, 4-5 Mon 4/28, ENGR 231

ACTIVE Center Open House
4:00-5:00pm Monday, 28 April 2014 in ENGR 231
The ACTIVE Center (Engineering 231) is a new classroom that was created by the CSEE Department with support from the Hrabowski Fund for Innovation, BAE Systems, and Northrup Grumman. The ACTIVE Center is designed to facilitate active student learning and laptop-based laboratory activities, and features movable furniture and whiteboards, a smart projector, and flat-panel displays around the room. We are also developing and documenting a “virtual environment” for the classroom, by creating “design patterns” for how computing technology can be used in this type of space to facilitate student learning.
The classroom came online in February 2014, and four pilot courses are currently being offered in the space. On Monday, April 28, we will hold an open house and presentation in the ACTIVE Center to show the campus community how an intentionally designed classroom space can increase student engagement and improve learning outcomes. The open house will include a presentation by Dr. Marie desJardins, a Hrabowski Academic Innovation Fellow and lead PI for the ACTIVE Center project, and a Q&A session with instructors and students who are currently teaching and learning in the ACTIVE Center. We will share best practices for developing and using similar teaching spaces, and will present the current policy for requesting to use the space for future classes.
Please note that no food or drink (other than covered containers of water) are permitted in the ACTIVE Center, but light refreshments will be provided in the hallway following the presentation.
Capacity is limited, so please RSVP. For more information, contact Marie desJardins (Sorry, you need javascript to view this email address. ).
]]>
ACTIVE Center Open House 4:00-5:00pm Monday, 28 April 2014 in ENGR 231 The ACTIVE Center (Engineering 231) is a new classroom that was created by the CSEE Department with support from the...
http://www.csee.umbc.edu/2014/04/active-center-open-house-4-5-mon-428-engr-231/
https://dev.my.umbc.edu/api/v0/pixel/news/43888/guest@my.umbc.edu/4e95ed3ca073826446ee582c8ee40b30/api/pixel
active
news
teaching-innovation
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
1
0
true
Thu, 24 Apr 2014 00:34:56 -0400
Thu, 24 Apr 2014 00:34:56 -0400
Defense: Feature Extraction and Fusion for Supervised and Semi-supervised Classification: Application to fMRI and LTM Data
Dissertation Defense
Feature Extraction and Fusion for Supervised and Semi-supervised
Classification: Application to fMRI and LTM Data
Wei Du
2:00pm Thursday, 24 April 2014, ITE 325B
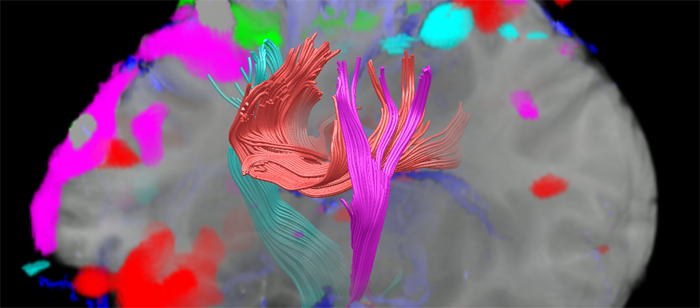
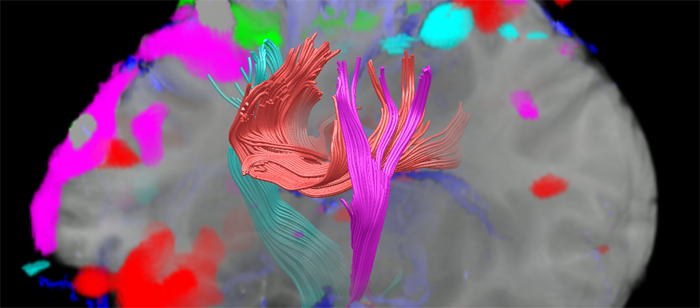
Extracting powerful features from high dimensional noisy data promises to significantly improve the effectiveness of further analysis, especially of classification. Since there is no single feature selection and extraction method or classifier that works best on all given problems, developing effective and efficient feature selection and extraction methods and classifiers for specific applications has became one of the most active areas in the machine learning field. The aim of this dissertation is to develop novel data-driven methods for extracting and selecting the most distinguishing features for performing classification using functional magnetic resonance imaging (fMRI) and laser tread mapping (LTM) tire data.
FMRI data have the potential to characterize and classify various brain disorders including schizophrenia. However, the high dimensionality and unknown nature of fMRI data present numerous challenges to accurate analysis and interpretation. Independent component analysis (ICA), as a data-driven method, has proven very useful for fMRI analysis in extracting spatial components as multivariate features used in classification, and more recently, for the analysis of fMRI data in its native complex-valued form. In this dissertation, we first present a novel framework to extract powerful features from components estimated by ICA, allowing us to remove the redundancy and retain the most discriminative activation patterns from multivariate ICA features. We apply the proposed three-phase feature extraction framework to two real-valued fMRI data sets, and achieve high classification rates in discriminating healthy controls from patients with schizophrenia. Second, due to the iterative nature of ICA algorithms, typically independent components (ICs) are not estimated consistently during different ICA runs, and hence it is not clear which result to use further. We present a statistical framework that utilizes an objective criterion to select the best of multiple ICA runs such that the multivariate ICA features from the best run can be used for further analysis and inference. Using the proposed framework, we study the performance of a novel complex ICA algorithm for fMRI analysis, entropy rate bound minimization, which takes all three types of diversity into account, including non-Gaussianity, sample dependence and noncircularity that are present in the complex-valued fMRI data. We show that CERBM leads to significant improvement in ICs that provide higher classification accuracy, and thus is a promising ICA algorithm for the analysis of complex-valued fMRI data.
Classification using LTM data is another problem we address where we first study the use of highly multivariate solutions such as ICA and then note the advantages using lower-level features for classification. In this case, an important problem is the selection of best set of features for the best classification performance. Additionally, there are a large amount of unlabeled tire data that are easy to collect but only a few of them can be easily labeled by expert. In this dissertation, we propose a novel mutual information (MI) based approach to achieve feature splits for co-training, a practical and powerful data-driven method in semi-supervised learning. Inspired by the idea of dependent component analysis, the proposed MI-based approach presents feature splits that are maximally independent between- or within- subsets, and thus selects and fuses features more effectively than other feature split methods. Experimental results on both simulated study and LTM tire data indicate that co-training with MI-based feature splits yields significantly higher accuracy than supervised classification.
Committee: Profs. Tulay Adali (Chair), Joel Morris, Janet Rutledge, Charles E. Laberge, Vince D. Calhoun (University of New Mexico and the Mind Research Network), and Dr. Matthew Anderson (Northrop Grumman Corp.)
]]>
Dissertation Defense Feature Extraction and Fusion for Supervised and Semi-supervised Classification: Application to fMRI and LTM Data Wei Du 2:00pm Thursday, 24 April 2014, ITE 325B...
http://www.csee.umbc.edu/2014/04/defense-feature-extraction-and-fusion-for-supervised-and-semi-supervised-classification-application-to-fmri-and-ltm-data/
https://dev.my.umbc.edu/api/v0/pixel/news/43889/guest@my.umbc.edu/bd7e3827cbf460e70bd82781aac32c15/api/pixel
defense
electrical-engineering
graduate
news
research
Computer Science and Electrical Engineering
https://dev.my.umbc.edu/groups/csee
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/original.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxlarge.png?1314043393
https://assets4-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xlarge.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/large.png?1314043393
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/medium.png?1314043393
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/small.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xsmall.png?1314043393
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/099/d117dca133c64bf78a4b7696dd007189/xxsmall.png?1314043393
Computer Science and Electrical Engineering
0
0
true
Wed, 23 Apr 2014 23:50:08 -0400