What’s a “cyberbomb?” UMBC cybersecurity experts explain in Scientific American

U.S. Deputy Defense Secretary Robert Work recently spoke about cyberwarfare and U.S. efforts to fight online security threats, leaving analysts wondering about the nature of today’s battles in cyberspace. UMBC’s Anupam Joshi and Rick Forno shed light on this world in a new Scientific American article that explains how online tactics known as “cyberbombs” work to prevent potential attacks, or could potentially be directed at U.S. targets.
Joshi is director of UMBC’s Center for Cybersecurity and professor and chair of the department of computer science and electrical engineering, and Forno serves as assistant director of the UMBC Center for Cybersecurity and director of UMBC’s graduate program in cybersecurity.
Cyberattacks can disrupt essential components of infrastructure people use every day, from cell phone networks to electric network generators, Joshi and Forno explain. They point out that “a ‘cyberbomb’ is not a single weapon,” but rather a collection of computer hardware and software that can be used to protect against cyber threats. This work might involve a broad range of professionals, including technological experts, military strategists, researchers, policy analysts, and lawyers, and as technology changes so do cyber weapons and tactics.
“We can analyze the underlying technologies and look at the global strategic considerations of those of those seeking to wage cyber warfare,” Joshi and Forno write. “That work allows us to offer ideas about cyber weapons and how they might be used.”
Read the full article, “America is ‘dropping cyberbombs’—but how do they work?” originally published in The Conversation. The original article was also mentioned in Tech Republic.
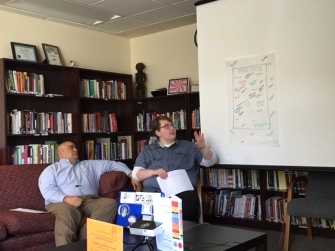
Images: Anupam Joshi presenting during cybersecurity forum hosted by the School of Public Policy. Photo by Marlayna Demond ’11 for UMBC.
]]>
U.S. Deputy Defense Secretary Robert Work recently spoke about cyberwarfare and U.S. efforts to fight online security threats, leaving analysts wondering about the nature of today’s battles in...
https://umbc.edu/stories/u-s-using-cyberbombs-to-protect-against-online-threats-umbc-cybersecurity-experts-explain/
https://dev.my.umbc.edu/api/v0/pixel/news/121140/guest@my.umbc.edu/bed633abac4289c94f81c6f7071e15d4/api/pixel
coeit
csee
cybersecurity
science-and-technology
UMBC News & Magazine
https://dev.my.umbc.edu/groups/umbc-news-magazine
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/xsmall.png?1748556657
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/original.png?1748556657
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/xxlarge.png?1748556657
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/xlarge.png?1748556657
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/large.png?1748556657
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/medium.png?1748556657
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/small.png?1748556657
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/xsmall.png?1748556657
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/001/943/24435aa6207c452e7bc15cc74b42c7bb/xxsmall.png?1748556657
UMBC News & Magazine
0
0
false
Tue, 24 May 2016 13:36:43 -0400
We Hosted an Event About Masculinity and Sexual Assault and Nobody Came
 A blog post and reflection by staff member Daniel Willey
A blog post and reflection by staff member Daniel Willey
The following post contains mentions of rape and sexual assault. Hyperlinks marked with * indicate that the article contains detailed accounts of assault in some form.
This past April during Sexual Assault Awareness Month, the Women’s Center hosted an program called “What About the Men?” The event was held on during Monday free hour, and it was billed as “a multimedia discussion on masculinity, sexual assault, and male survivors.*”
I wanted to talk about how societal ideas about masculinity (like sexual prowess, social dominance, financial stability, risk-taking, and the “Man Card”) create an environment that encourages — or is at least passively complicit in — sexual violence against women, and isolates and invalidates male survivors of sexual violence.
And nobody came.
Okay, not nobody. Jess and Megan and Shira were there, and four community members stopped in to see what was happening. We actually had a really great discussion and I’m glad those people were there to have that important conversation. But I want to talk about the people that weren’t there. I want to talk about showing up and speaking out for male survivors. I want to talk about accountability, masculinity, and how sexual assault is everyone’s problem.
So, let’s go back a bit and talk about masculinity.
The Man Box is an activity we do in Rebuilding Manhood to get everyone thinking about hegemonic masculinity. Hegemonic masculinity is basically society’s idea of what a man ‘should’ be and do. It’s an idea we all agree to and go along with, whether we agree with it or completely conform to it or not. Inside the Man Box, participants write words or phrases that fit within this dominant idea of masculinity, including: trucks, steak, beer, sports, outdoors, strong, confident, protector, power, leader, man up, boys don’t cry, don’t show emotion, wears the pants, provide for your family, sex with women, good at sex, and good at math and science.
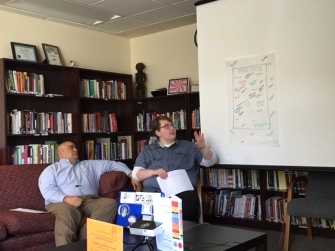
Mito and Dan go over the Man Box
On the outside of the box are words and phrases used for men who step outside the limitations of the Man Box. When we do this activity, everyone is hesitant to write the words on the outside. Once a brave soul (or sometimes the facilitator) writes the first swear word, we see “bitch” “pussy” “gay” “fag” “pansy” “whipped” appear around the outside of the Man Box. The words outside the Man Box keep men trapped within the box. They are the consequences of not living up to the expectations set forth by all of us.
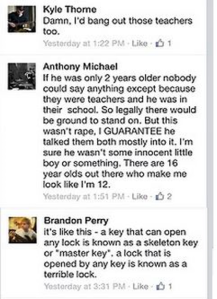
I talk about the Man Box because when it comes to conversations about men’s violence against women, the most common response is, “Not all men are like that.” To quote Tony Porter*, “There’s not a lot of men [perpetrating violence], but there is a lot of violence. So what is it that allows these men to do what they do in the presence of all these good men?” The answer is the Man Box.
It’s up to men to help other men get out of the man box and to discourage violent behavior. To not speak up and actively work to support women and a healthier concept of masculinity is to be complicit in the violence. It can be hard because laughing at rape joke or giving your friend the thumbs up and a condom as he guides a drunk person upstairs is part of the fee for staying in the man box. But if you’re not willing to pay the price of losing your man card to prevent rape or assault, you are part of the problem. When you say “Not All Men,” you’re giving all men a pass to say “that’s not my problem.” It is your problem.
When very few people showed interest in the What About The Men event, not only did it show how many people think sexual violence is not their problem, but it also became an example of a problem I hoped to address in the event: People don’t support male survivors in the same way as other survivors because we have a false image who and what a survivor is.
Now, let’s be real and admit survivors aren’t really supported at all. Even the “perfect victim” (i.e. a straight woman who wasn’t drunk, was dressed conservatively, didn’t know the person, didn’t consent to something else, etc etc) won’t get the support they deserve. But to society, a sexual assault survivor represents vulnerability and violation — something hegemonic masculinity just isn’t — and therefore it is totally unfathomable that a man could be survivor. At most, we can maybe comprehend boys being victimized at a young age, but not adult men. When I was doing research for the event, I found that most of the resources (like support groups and even interviews with psychologists specializing in the field) were targeted for male survivors of childhood sexual assault. None of them addressed sexual assault as an adult, and often they focused on the young age at which the assault occurred in to reassure survivors that they could still be men.

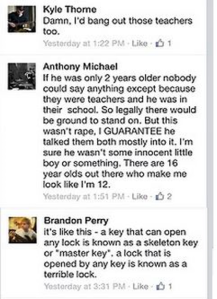

So, what? Men who experience sexual assault as an adult are no longer men? Were they never men to begin with? Are they gay now? Does sexual assault just not happen to men? No, of course not. But because we see men as always wanting sex, as powerful and strong and dominant, we can’t imagine men as survivors unless it was during childhood. We also can’t imagine that sexual assault can be perpetrated by women, but in a recent study 46% of male survivors reported a female perpetrator. Maybe we can wrap our heads around a male perpetrator, but a woman*? No way. He’s supposed to like it*.
Toxic ideas like this leave male survivors feeling isolated. Many feel like they can’t talk about it. Many don’t know they can claim words like “assault” “victim” “survivor” or “rape” to describe their experience. And if men can’t talk about rape, male survivors have nobody to speak up and say “Hey. It happened to me, too.”
We called this event “What About The Men” (if you click on just one link from this whole blog, it should be this one) because every time we or anyone else does anything about sexual assault, someone goes “Hey, men get raped too!” They’re totally right, but usually these people are using male survivors as a way to derail conversations about men as perpetrators. They’re not focusing on how toxic masculinity ignores and reprimands male survivors. They just want to absolve toxic masculinity of its responsibility for sexual violence against all genders. I wanted to use that time and space to really address that question: What About the Men?
We all need to show up more for male survivors. As much as I am upset with our community for not stepping up to be accountable for sexual assault and support male survivors, we at the Women’s Center need to be accountable too. This is the first event we’ve hosted with the focus of male survivors in the last five years, and possibly the only one ever. This is a feminist issue because the power structures of patriarchy and rape culture will continue to put men in positions of power and dominance, whether they use it against others or have it used against them. We all need to do better.
If you’re interested in more issues related to masculinity or are in search of a safe space to talk about masculinity, keep an eye out for Rebuilding Manhood and other Women’s Center programming. If you need to talk one-on-one with someone who can provide a safe and affirming environment, schedule a meeting with Jess or Megan or stop by the Women’s Center, or contact the Voices Against Violence coordinator.
More online resources:
For Gay or Bisexual Men
Commonly Asked Questions
]]>
A blog post and reflection by staff member Daniel Willey The following post contains mentions of rape and sexual assault. Hyperlinks marked with * indicate that the article contains detailed...
https://womenscenteratumbc.wordpress.com/2016/05/24/we-hosted-an-event-about-masculinity-and-sexual-assault-and-nobody-came/
https://dev.my.umbc.edu/api/v0/pixel/news/60354/guest@my.umbc.edu/2ebc9534a96ef0dc2bb2208611f3157f/api/pixel
issues
masculinity
programs
sexual-assault
sexual-assault-awareness-month
uncategorized
Women's, Gender, & Equity Center
https://dev.my.umbc.edu/groups/womenscenter
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xsmall.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/original.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xxlarge.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xlarge.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/large.png?1750974263
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/medium.png?1750974263
https://assets1-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/small.png?1750974263
https://assets2-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xsmall.png?1750974263
https://assets3-dev.my.umbc.edu/system/shared/avatars/groups/000/000/125/78272a4842689b30dbf74672182b78f8/xxsmall.png?1750974263
Women's Center
111
0
false
Tue, 24 May 2016 12:15:00 -0400
Tue, 24 May 2016 12:15:00 -0400



 A blog post and reflection by staff member Daniel Willey
A blog post and reflection by staff member Daniel Willey